The crooks responsible for launching phishing campaigns that netted dozens of employees and more than 100 computer systems last month at Wipro, India’s third-largest IT outsourcing firm, also appear to have targeted a number of other competing providers, including Infosys and Cognizant, new evidence suggests. The clues so far suggest the work of a fairly experienced crime group that is focused on perpetrating gift card fraud.
On Monday, KrebsOnSecurity broke the news that multiple sources were reporting a cybersecurity breach at Wipro, a major trusted vendor of IT outsourcing for U.S. companies. The story cited reports from multiple anonymous sources who said Wipro’s trusted networks and systems were being used to launch cyberattacks against the company’s customers.
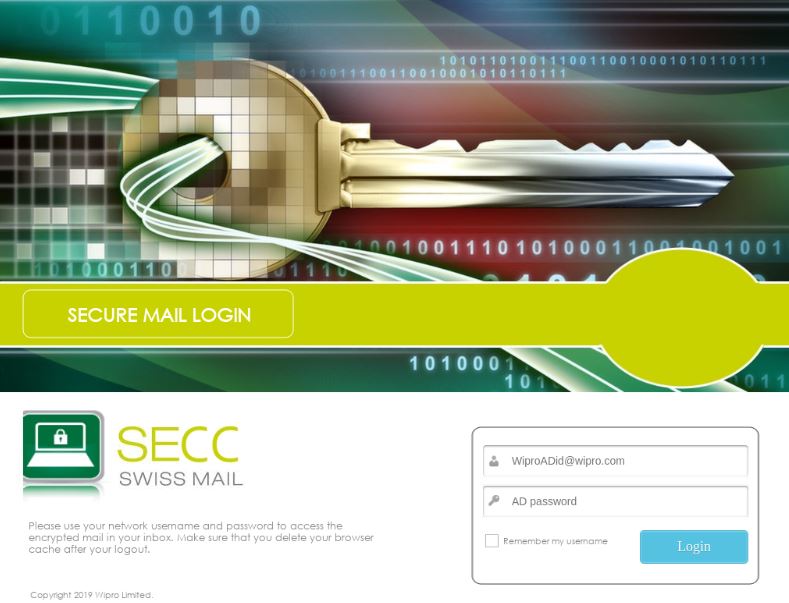
A screen shot of the Wipro phishing site securemail.wipro.com.internal-message[.]app. Image: urlscan.io
If one examines the subdomains tied to just one of the malicious domains mentioned in the IoCs list (internal-message[.]app), one very interesting Internet address is connected to all of them — 185.159.83[.]24. This address is owned by King Servers, a well-known bulletproof hosting company based in Russia.
According to records maintained by Farsight Security, that address is home to a number of other likely phishing domains:
securemail.pcm.com.internal-message[.]app
secure.wipro.com.internal-message[.]app
securemail.wipro.com.internal-message[.]app
secure.elavon.com.internal-message[.]app
securemail.slalom.com.internal-message[.]app
securemail.avanade.com.internal-message[.]app
securemail.infosys.com.internal-message[.]app
securemail.searshc.com.internal-message[.]app
securemail.capgemini.com.internal-message[.]app
securemail.cognizant.com.internal-message[.]app
secure.rackspace.com.internal-message[.]app
securemail.virginpulse.com.internal-message[.]app
secure.expediagroup.com.internal-message[.]app
securemail.greendotcorp.com.internal-message[.]app
secure.bridge2solutions.com.internal-message[.]app
ns1.internal-message[.]app
ns2.internal-message[.]app
mail.internal-message[.]app
ns3.microsoftonline-secure-login[.]com
ns4.microsoftonline-secure-login[.]com
tashabsolutions[.]xyz
www.tashabsolutions[.]xyz
The subdomains listed above suggest the attackers may also have targeted American retailer Sears; Green Dot, the world’s largest prepaid card vendor; payment processing firm Elavon; hosting firm Rackspace; business consulting firm Avanade; IT provider PCM; and French consulting firm Capgemini, among others. KrebsOnSecurity has reached out to all of these companies for comment, and will update this story in the event any of them respond with relevant information.
WHAT ARE THEY AFTER?
It appears the attackers in this case are targeting companies that in one form or another have access to either a ton of third-party company resources, and/or companies that can be abused to conduct gift card fraud.
Wednesday’s follow-up on the Wipro breach quoted an anonymous source close to the investigation saying the criminals responsible for breaching Wipro appear to be after anything they can turn into cash fairly quickly. That source, who works for a large U.S. retailer, said the crooks who broke into Wipro used their access to perpetrate gift card fraud at the retailer’s stores.
Another source said the investigation into the Wipro breach by a third party company has determined so far the intruders compromised more than 100 Wipro systems and installed on each of them ScreenConnect, a legitimate remote access tool. Investigators believe the intruders were using the ScreenConnect software on the hacked Wipro systems to connect remotely to Wipro client systems, which were then used to leverage further access into Wipro customer networks.
This is remarkably similar to activity that was directed against a U.S. based company in 2016 and 2017. In May 2018, Maritz Holdings Inc., a Missouri-based firm that handles customer loyalty and gift card programs for third-parties, sued Cognizant (PDF), saying a forensic investigation determined that hackers used Cognizant’s resources in an attack on Maritz’s loyalty program that netted the attackers more than $11 million in fraudulent eGift cards.
That investigation determined the attackers also used ScreenConnect to access computers belonging to Maritz employees. “This was the same tool that was used to effectuate the cyber-attack in Spring 2016. Intersec [the forensic investigator] also determined that the attackers had run searches on the Maritz system for certain words and phrases connected to the Spring 2016 attack.”
According to the lawsuit by Maritz Holdings, investigators also determined that the “attackers were accessing the Maritz system using accounts registered to Cognizant. For example, in April 2017, someone using a Cognizant account utilized the “fiddler” hacking program to circumvent cyber protections that Maritz had installed several weeks earlier.”
Maritz said its forensic investigator found the attackers had run searches on the Maritz system for certain words and phrases connected to the Spring 2016 eGift card cashout. Likewise, my retailer source in the Wipro attack told KrebsOnSecurity that the attackers who defrauded them also searched their systems for specific phrases related to gift cards, and for clues about security systems the retailer was using.
It’s unclear if the work of these criminal hackers is tied to a specific, known threat group. But it seems likely that the crooks who hit Wipro have been targeting similar companies for some time now, and with a fair degree of success in translating their access to cash given the statements by my sources in the Wipro breach and this lawsuit against Cognizant.
What’s remarkable is how many antivirus companies still aren’t flagging as malicious many of the Internet addresses and domains listed in the IoCs, as evidenced by a search at virustotal.com.
Update, April 19, 11:25 a.m. ET: I heard back from some of the other targets. Avanade shared the following statement:
“Avanade was a target of the multi-company security incident, involving 34 of our people in February. Through our cyber incident response efforts and technologies, we swiftly contained and remediated the situation. As a result, there was no impact to our client portfolio or sensitive company data. Our review has concluded this was isolated incident. Our security defenses have continued to protect against any potential threat related to this matter. And, we continue take our responsibility to safeguard our clients’ data with the utmost seriousness.”
Cognizant replied:
“We are aware of reports that our company was among many other service providers and businesses whose email systems were targeted in an apparent criminal hacking scheme related to gift card fraud. Since the criminal activity first surfaced earlier this week and following reports that another service provider’s email system was allegedly compromised, Cognizant’s security experts took immediate and appropriate actions including initiating a review.”
“While our review remains ongoing, we have seen no indication to date that any client data was compromised. It is not unusual for a large company like Cognizant to be the target of spear phishing attempts such as this. The integrity of our systems and our clients’ systems is of paramount importance to Cognizant. We continuously monitor, update and strengthen our systems against unauthorized access and have put additional protocols in place related to this specific industry-wide incident.”
Infosys said it has not observed any breach of its network based on its monitoring and threat intelligence. “This has been ascertained through a thorough analysis of the indicators of compromise that we received from our threat intelligence partners,” the company said in a statement.
Rackspace said it has no evidence to indicate that there has been impact to the Rackspace environment: “Rackspace Security Operations continuously monitors our environment for threats and takes appropriate action should an issue be identified.”
Capgemini said its internal Security Operation Center (SOC) detected and monitored suspicious activity that showed similar patterns to the attack faced by WIPRO. “This occurred between March 4 and March 19. The activity concentrated on a very limited number of laptops and servers. Immediate remedial action took place. There has been no impact on us, nor on our clients to date.”
Slalom, another company listed above, said it can “confirm that phishing attack activity was detected and prevented between March 4 and March 19, which correlates to the information that you have published on the Wipro event. A combination of 24×7 Security Operations Center advanced security monitoring, security awareness training and threat intelligence automation enabled us to detect, alert, and prevent an event, sourcing from the phishing attacks. We have verified this through internal forensics and with the support of our threat intelligence partners.”




I think these sites would have been marked as malicious had Wipro actually come out and shared IOC’s. I’m sure they’re cutting edge technology is blocking it now though.
Wipro’s sales team made commissions by selling this holey service to many companies/organizations that had a misguided sense of trust.
The corporate brass and salespeople should all have their salaries/bonuses/worthless-stock clawed back.
The companies and organizations that utilize such a shoddy vendor should have their management penalized also.
Without significant penalties this type of malfeasance/criminality will continue.
I wouldn’t call them shoddy. Careless perhaps. Problem is in this day and age anyone can be a victim. No one is immune. If you think you are, you’re probably already compromised. Companies have to be right every single time. The bad guy only once.
ChrisSuperPogi and Anon404, you do not need multiple AV programs to have multiple AV engines. There are AV products that use a number of AV engines. Yes, it’s really inexcusable that many AV engines have yet to add most of these domains.
Mike, while I get your point, at this level of enterprise don’t you think careless = shoddy, for the most part? I agee not all carelessness would equal shoddy, but c’mon—these guys have other companies security in their trust. There can be no “carelessness”.
Did you read the article that Brian posted on twitter about their CISO who said that cybersecurity shouldn’t interfere with business and that multi-factor authentication is not needed for most employees? I think that is a shoddy attitude, if nothing else. MFA could have prevented this mess.
Indeed, any executive who makes the claim that MFA is not necessary protection in 2019 is in for some harsh realities.
“What’s remarkable is how many antivirus companies still aren’t flagging as malicious many of the Internet addresses and domains listed in the IoCs, as evidenced by a search at virustotal.com.”
It was proven – 2014 Black Hat Conference, I think – that a single intelligence feed would not be enough to cover all of the threats out there.
This lead me to install multiple anti-virus protection to increase my depth (in defense).
My kind word, folks!
Defense in Depth is not having multiple anti-virus programs. Multiple AV’s will likely step on each others toes, although some are known to place nice together. However, an actual defense in depth strategy involves having multiple layers of defense. AV is one layer, IDS/IPS(Snort) is another. A next gen firewall with ACL’s and traffic inspection would be another layer, packet capture and analysis(tcpdump/Wireshark) would be another, a PAM solution is another layer. Log collection and analysis is yet another(SIEM solution) as well as advanced logging beyond the standard Windows logs(Sysmon). Simply having more then one AV is NOT defense in depth.
Yep, well said Anon404,
Depth of Defense starts at your edge network devices right down to the AV engine…
If you’ve been affected because you haven’t patched right up to compliance then there are far bigger issues to deal with first…
Whilst it is very important the reality is that there are SCADA environments out there that will always run up to a year behind in patching because they have to be 100% tested against critical path equipment by their manufacturers etc…
Those environments need to be air gapped whenever possible…
“What’s remarkable is how many antivirus companies still aren’t flagging as malicious many of the Internet addresses and domains listed in the IoCs, as evidenced by a search at virustotal.com.”
It was proven before – 2014 Black Hat Conference, I think – that a single intelligence feed would NOT be enough to catch all of the threats out there.
I had since deployed multiple anti-virus protection…
Be safe folks!
OpSec fail in user name.
/trombone/
Interesting that they used .app domains given Google backed those as a “more secure” domain that enforces HTTPS only.
Too bad no one told the bad actors they too couldn’t use HTTPS and obtain certificates for next to nothing, actually nothing according to namecheap.com.
“You can register a .App domain name for only $14.98 and get a free PositiveSSL certificate for one year.”
Searching Cert Transparency logs for that root domain returns some interesting additional domains…..
https://transparencyreport.google.com/https/certificates?hl=en&cert_search_auth=&cert_search_cert=&cert_search=include_expired:true;include_subdomains:true;domain:internal-message.app&lu=cert_search
businesscenter.valuelink.biz.internal-message.app
secure.firstdata.com.internal-message.app
secure.expediagroup.com.internal-message.app
secure.episerver.com.internal-message.app
securemail.pcm.com.internal-message.app
Also just looking at the issuance dates, it looks like wipro was not the first target.
Awesome followup article
Screenconnect is not normally used by MSSP’s I hope? It’s an product from the 2000’s that i would sincerely hope no MSSP would normally use… even surprised the bad guys would use it… it should stand out like a sore thumb in any enterprise.
ScreenConnect is the default remote-control product in the ConnectWise management suite. It’s been re-branded as ConnectWise Control, but it’s used daily by many MSPs.
Dear Wipro Customers:
Remember that time you decided American IT support was way too expensive? You put up a bunch of job postings requiring a Masters Degree and 5 years of experience for an entry level IT job, then told the government that no American was qualified to do the work to get tax breaks? You got what you paid for.
Sincerely,
The educated IT guy you turned down.
Thank you for your continued coverage of this debacle, Brian.
That sounds familiar!! I’m probably too old now.
You are my new favorite person.
Schadenfreude:
Schadenfreude is the experience of pleasure, joy, or self-satisfaction that comes from learning of or witnessing the troubles, failures, or humiliation of another.
Let me add my +1 to the others’.
I haven’t checked, but if these guys are number 3, who are numbers 1 and 2? Is the naming rights sponsor of the nyc marathon 1 or 2? I wonder how much money the nyrr folks are paying to ensure the joggers’ information stays private.
If nothing, this incident has brought out the hatred that a part of the security community harvests for Indian MSSP’s and other outsourcing firms. People somehow think shoddy practices and lack of skillset is behind the breach, when in reality it’s a combination of oversight by individuals and multiple levels of technology failure that are now being investigated. Didn’t RSA face a massive breach years ago? Were they also suffering at the hands of MSSP’s?
This has just given people affected by the outsourcing wave a chance to come and air their grievances publicly. They say things like “you get what you pay for” without knowing much about what actually transpired.
I couldn’t agree more whole-heartedly! I’ve had the same sentiment going back to the late 90s when all of this out-sourcing started. Companies were just looking for a profit!
Why no one is ready to point to M$ here… Most of the MSPs are using O365 when this happened..
Love that statement… So true, but sadly, cheap is all that counts nowadays.
“someone using a Cognizant account utilized the “fiddler” hacking program to circumvent cyber protections that Maritz had installed several weeks earlier.”
That’s some crappy “cyber protections” they have 🙂
Looks like their amazing internal solution didn’t work.
https://www.mesalliance.org/wp-content/uploads/2017/04/3-Cognitive-Cyber-Defense-Wipro-Murali-Rao.pdf
ha! “fiddler hacking tool”. that means “we added javascript security and they worked around it by sending the requests without a browser that run our dumb javascript”
They probably lost all their accounts on the phishing hacks, and then a “security consultant” saw that cognizant used some test account in a internal test and flagged that as compromised, while it had nothing to do on how the attackers got the credentials anyway (which was the phishing a year before)
You get what you pay for! There is no quality in any of Wipro services.
USA companies are risking all of their employees and clients identities by partnering by Wipro.
You get what you get pay for!
USA companies are risking their clients identities by partnering with off-shore companies.
https://www.theverge.com/2019/4/15/18311112/microsoft-outlook-web-email-hack-response-comment
Oh look! Another breach that doesn’t involve an Indian MSSP. And it’s a company that provides email solutions to the entire globe. Whoops, looks like people who are salty about outsourcing cannot blame other companies for not having a job!
Nothing like a good ol’ fashioned false equivalency
Exactly! We know Microsoft would never outsource to a company based in India! (Certainly not Wipro!)
Right?
https://www.nytimes.com/2004/11/16/business/worldbusiness/microsoft-expands-operations-in-india.html
Consider WIPRO HR team they communicate using personal email account of Employee. They close official ID and send confidential information to employees using gmail.
Even VP Putul Mathur uses people personal email.
They threaten people, over emails. Calls are recorded by Deepti from Compliance team to rise FIR when an employee calls to seek help.
Smitha Vasanth from HR team rejects applied medical leaves and reports to complaince team as Employee is absconding.
These are done in with in wipro.
To save paper, papers which are waste printouts must be put into shredder but one sided scribble pads are prepared.
Once I got account section scribble pad which had some Employees salary account number.
Final settlement of an Employee in lakhs.
Employee data is also exposed
Have you heard about Intruders target IBM? Why? We are in the IOT world, cyber security is very Important now days, so new security concepts technology is required to stop the Intruders. It is necessary and mandatory for every IT Firm!
Ref – Softhunters
Discover Solutions better to questioning the threat!
Hmm… maybe that explains why recently I got a couple of emails from Sears, with whom I have not done business in several years, and whose local brick-and-mortar stores are all now closed. Fortunately they arrived at a Yahoo email address I use only for public-facing correspondence.
Several hundred Sears stores are still open, though many will resize and rebrand as Sears Home and Life.
Their online operations have never stopped.
Even the store locations that closed will remain part of the Sears brand, because they own their property in most locations. Sears will be landlords for other stores or condominiums, as they pop up.
Sears isn’t dead.
Brian, any idea that why did these other organisations, who were targeted as well, did not go public with the information, until your enquiry to them?
I have seen very little demonstration of thought leadership here, just rag like approach to venting anti-outsourcing venom and some petty point scoring.
In all fairness, it does look like day zero . How much investigative zeal, including getting on to investor calls , cross checking versions etc are we going to expend on others. Why not invest that expertise to understand the trend and implications.
This is a very aware and pragmatic comment. Not like the others which are hate speeches from jobless IT admins
I have a few doubts about this. Is this a new way to wind a poor business. Looks like there is a scam behind this. Only Snowden and Julian can reveal the actual truth. This is definitely not just a phising gift fraud case. There is more behind this.
The worst part is that these MSPs outsource cyber security instead of building a strong corporate security team. How can they ensure client’s security.
They are seriously abusing the OPT program for international students to staff information security positions in america with false profiles. If H1B is tough they find other loop holes.
unsure if this is related or not, but there was something published by lastline on jan 11 detailing an APT attack which utilized a phishing domain targeting wipro
https://www.lastline.com/labsblog/threat-actor-cold-river-network-traffic-analysis-and-a-deep-dive-on-agent-drable/
hr-wipro[.]com hosted on 185.161.211[.]79
Virustotal has those as malicious:
http://www.virustotal.com/en/url/e7256f51b6f1c00e2de365bca8b9704531af2c1ea16725bf86b9019ea10eaa16/analysis
http://www.virustotal.com/en/url/b81141cd5a58a65fe0ab790608d660a9e56363961f0504e036040de3f5caa0bd/analysis
http://www.virustotal.com/en/url/77d2d1d3601bd103cec9ce538183d4c7a55f44611ce324f75b3885961e10c645/analysis
http://www.virustotal.com/en/url/81cc98f1769c8fff6fb18e0945950d7ad36e73b0a7c38603c02776a06c5507e5/analysis 5months ago
http://hr-suncor.com on the same IP. Notice the “hr-” same as in “hr-wipro”
“DNS hijacking activity targeting government…”
https://www.google.com/search?hl=en&lr=lang_en&num=100&safe=active&q=%22hr-suncor.com%22
https://krebsonsecurity.com/tag/dnspionage
Both hr-wipro.com and hr-suncor.com mentioned as “fake job websites” in the Talos report linked in the DNSpionage Krebs article.
The worst part is that these MSPs outsource cyber security instead of building a strong corporate security team. How can they ensure client’s security.