The U.S. Justice Department this week indicted seven Chinese nationals for a decade-long hacking spree that targeted more than 100 high-tech and online gaming companies. The government alleges the men used malware-laced phishing emails and “supply chain” attacks to steal data from companies and their customers. One of the alleged hackers was first profiled here in 2012 as the owner of a Chinese antivirus firm.
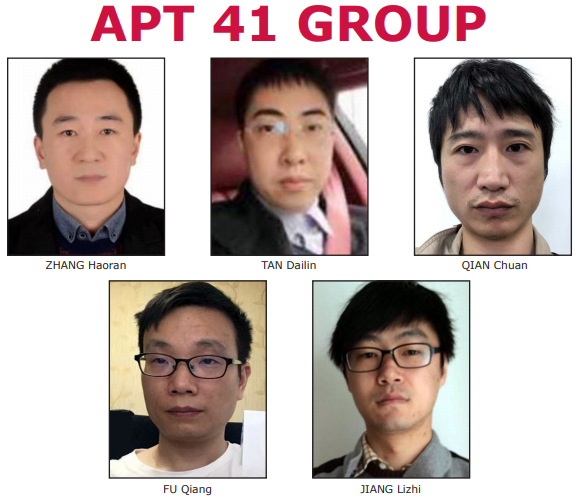
Image: FBI
Charging documents say the seven men are part of a hacking group known variously as “APT41,” “Barium,” “Winnti,” “Wicked Panda,” and “Wicked Spider.” Once inside of a target organization, the hackers stole source code, software code signing certificates, customer account data and other information they could use or resell.
APT41’s activities span from the mid-2000s to the present day. Earlier this year, for example, the group was tied to a particularly aggressive malware campaign that exploited recent vulnerabilities in widely-used networking products, including flaws in Cisco and D-Link routers, as well as Citrix and Pulse VPN appliances. Security firm FireEye dubbed that hacking blitz “one of the broadest campaigns by a Chinese cyber espionage actor we have observed in recent years.”
The government alleges the group monetized its illicit access by deploying ransomware and “cryptojacking” tools (using compromised systems to mine cryptocurrencies like Bitcoin). In addition, the gang targeted video game companies and their customers in a bid to steal digital items of value that could be resold, such as points, powers and other items that could be used to enhance the game-playing experience.
APT41 was known to hide its malware inside fake resumes that were sent to targets. It also deployed more complex supply chain attacks, in which they would hack a software company and modify the code with malware.
“The victim software firm — unaware of the changes to its product, would subsequently distribute the modified software to its third-party customers, who were thereby defrauded into installing malicious software code on their own computers,” the indictments explain.
While the various charging documents released in this case do not mention it per se, it is clear that members of this group also favored another form of supply chain attacks — hiding their malware inside commercial tools they created and advertised as legitimate security software and PC utilities.
One of the men indicted as part of APT41 — now 35-year-old Tan DaiLin — was the subject of a 2012 KrebsOnSecurity story that sought to shed light on a Chinese antivirus product marketed as Anvisoft. At the time, the product had been “whitelisted” or marked as safe by competing, more established antivirus vendors, although the company seemed unresponsive to user complaints and to questions about its leadership and origins.
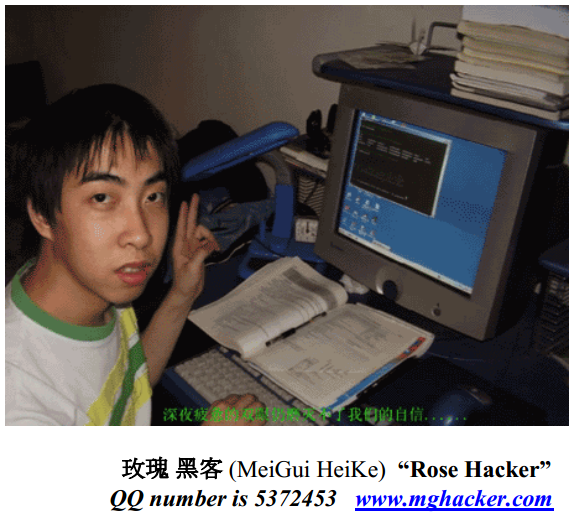
Tan DaiLin, a.k.a. “Wicked Rose,” in his younger years. Image: iDefense
Anvisoft claimed to be based in California and Canada, but a search on the company’s brand name turned up trademark registration records that put Anvisoft in the high-tech zone of Chengdu in the Sichuan Province of China.
A review of Anvisoft’s website registration records showed the company’s domain originally was created by Tan DaiLin, an infamous Chinese hacker who went by the aliases “Wicked Rose” and “Withered Rose.” At the time of story, DaiLin was 28 years old.
That story cited a 2007 report (PDF) from iDefense, which detailed DaiLin’s role as the leader of a state-sponsored, four-man hacking team called NCPH (short for Network Crack Program Hacker). According to iDefense, in 2006 the group was responsible for crafting a rootkit that took advantage of a zero-day vulnerability in Microsoft Word, and was used in attacks on “a large DoD entity” within the USA.
“Wicked Rose and the NCPH hacking group are implicated in multiple Office based attacks over a two year period,” the iDefense report stated.
When I first scanned Anvisoft at Virustotal.com back in 2012, none of the antivirus products detected it as suspicious or malicious. But in the days that followed, several antivirus products began flagging it for bundling at least two trojan horse programs designed to steal passwords from various online gaming platforms.
Security analysts and U.S. prosecutors say APT41 operated out of a Chinese enterprise called Chengdu 404 that purported to be a network technology company but which served a legal front for the hacking group’s illegal activities, and that Chengdu 404 used its global network of compromised systems as a kind of dragnet for information that might be useful to the Chinese Communist Party.

Chengdu404’s offices in China. Image: DOJ.
“CHENGDU 404 developed a ‘big data’ product named ‘SonarX,’ which was described…as an ‘Information Risk Assessment System,'” the government’s indictment reads. “SonarX served as an easily searchable repository for social media data that previously had been obtained by CHENGDU 404.”
The group allegedly used SonarX to search for individuals linked to various Hong Kong democracy and independence movements, and snoop on a U.S.-backed media outlet that ran stories examining the Chinese government’s treatment of Uyghur people living in its Xinjian region.
As noted by TechCrunch, after the indictments were filed prosecutors said they obtained warrants to seize websites, domains and servers associated with the group’s operations, effectively shutting them down and hindering their operations.
“The alleged hackers are still believed to be in China, but the allegations serve as a ‘name and shame’ effort employed by the Justice Department in recent years against state-backed cyber attackers,” wrote TechCrunch’s Zack Whittaker.




Another great article , keep them coming !
scammmmers
I’m glad Brian is kicking these dust mice out in the open for all the public to see. With no extradition agreement, this is all we can do. The public needs to know.
It’s time to stop buying Chinese products or doing any business with that kleptocratic farcical ethnostate. As a world bloc.
How do we stop buying stuff made in China? Everything is made there or made of parts made there. Almost all electronic components are made in China. I repair equipment for a German company and nearly all components bar microcontrollers are manufactured in China.
Simple AF. Pay more per part. You stop paying for slave labor,
you build up an emerging market even if it costs slightly more,
in the short term. They have you by the short-term balls.
There is literally NOTHING made in China that cannot be made elsewhere. If you’re talking about certain parts for automobile makers that “aren’t” made anywhere else, that’s because they only sought a single vendor to make them. That’s their fault.
Yes it will take time and have a cost to move away from slave labor. Do so, or you end up in their situation soon enough.
China is happy to let you believe nobody else can make a BAR microcontroller in the world, believe me, they love lazy folks.
The most profitable market doesn’t even look for a 2nd source.
If your argument is that it’s easier to march into bondage, sure.
The same mindset just pays the ransomware a-holes. Easier.
But it’s a chicken-and-egg thing. Right now, everyone buys components from China. Suppose I need component X for my product. And suppose I’m willing to pay a premium and buy from a non-Chinese company. Problem is, there’s no market: it’s not worthwhile for someone to manufacture component X outside of China. I just need a few thousand pieces, I can’t set up my own X factory. So I go ahead and buy from China, because there’s no alternative.
They have a large % of the rare earth mineral deposits right?
As does Australia; the trouble is, we can dig it up, but we have have to send it to China to turn it into batteries.
Unless and until we invest in our own manufacturing, at subsidized cost, like China did to cheat the system the first place…
A major part of the price for letting our thousands of American factories and millions of American jobs go to China was the loss of not so easy to re-create assembly lines, supply chains and related manufacturing skills. Moving electronics and other supply chains back to the US will take a major effort.
I agree the best we can do is expose them and their tactics. Hacker scum took my life away so I’ve made it a point to focus on bringing as many of them to justice as I can. Great story.
Another great spotlight, Brian. My laptop has just blocked attempted fraud emails from akatuki@bz03.plala.or.jp claiming to be from Nucleus Financial Group PLC.
Is there any way that I can trace that he/she is part of the APT people?
Also, is there any way that I can establish if my email address/other details are for sale on the dark web? My bank account was hacked last year and my bank still has no idea how the hacker by-passed the two-stage log-in security. They replaced my bank account but I’m still getting these annoying fake emails.
Regarding your second question, this might help:
haveibeenpwned.com
Once again a great article keep em commin !
hxxps://answers.microsoft.com/en-us/windows/forum/all/anvi-folder-lockers-security/d68773e2-70e4-4eef-b469-7adf71f14143
From: Raymond Ave
Microsoft Agent | Moderator
“Just to answer your question, Anvisoft collects some personal data from you while using their products or services. Anvisot is such a reputable company…” September 6, 2018
#GeeThanksMicrosoft
Anvisoft or any other Chinese security soft are really OK but personally I wouldn’t use them. Why gambling? No way you can find them or b4ing them to justice so there is no incetive for them being loyal to customers in “imperialistic” countries.
what a faces lol:D funny 😀
> With no extradition agreement, this is all we can do
Well obviously cleaning up the vulnerabilities Silicon Valley keeps churning out is also possible but yeah, I used to think so. But I am beginning to change my mind. The problem is that this public attribution strategy combines catastrophically badly with a deterrence strategy.
The Obama white house first as deterrence against Ukraine style attacks then as retribution for the 2016 election announced it was already in the Russian electrical grid and telecom networks and cybercommand would deploy “cyber weapons” there (aka sabotage) if the US was provoked.
The Trump white house (and the firecrowdeye`s looking to sell to them) have gone very quiet on Russia .. except when Bolton was in charge. Having gotten rid of all the silly softy doctor types on the NSC he doubled down on deterrence with new public proclamations.
Whether is was Russia or someone else is hard to tell but clearly somebody noticed. The dragonfly/nuclear-17/energetic bear actor launches a new wave of discretely implanting themself across NATO critical infrastructure, particularly the energy sector every time the white house uses threatening language like that.
Under Obama they were widely documented. In Trump current Era of “Dont talk about the (Russian Cyber)-war” keeping track of energetic bear has been difficult but if you read between the lines of the executive order, the San Francisco airport announcement, leaked German warning, the ESET, Dragos and cybercommand comments on virustotal, the NSA taking over for DHS/CISA with its own warnings or by signing on to UK ones. .. well together a clear picture emerges. Somebody responds in kind to all US announcements it has implanted others and will sabotage if provoked.
If you talk tough about how if provoked you are totally gonna leave Moscow without electricity then you really end up in a bind when you actually are provoked.. which in the case of cybersecurity is really a daily occurrence.
You can either:
A. Maintain strategic ambiguity, you don’t tip your hand about how much you know about the attackers and about what the threshold is for you to respond. You just quietly keep an eye on them making sure every exploit or tactic gets quietly countered.
B. You say “hey our economy/national security is starting to take serious hits here… time to hit them to pay a similar price.. well then the other side where almost nobody had a clue what was going on till the power goes out has little choice but to escalate with large scale sabotage of your soft critical infrastructure targets using zero days previously stockpiled for quiet espionage against highly defended systems… and in the end North Korea wins the “cyber worldwar” on account of having the least vulnerable IT infrastructure… or any really any IT infrastructure.
C. You fail to make a choice. DOJ confirms publicly you know you were hit and you know in detail how bad it was. Cybercommand champs at the bit with a cyber retaliation plan but the real world jobs offered by trade deals, counter-terrorism, real war zone strategic considerations and the risks of escalating retaliation at a time when your economy isn’t in any shape to take another hit have you decide not to strike back.
Everyone sees this reaction and how you know you are vulnerable, that’s why you came up with all the threatening language but the real repercussions are actually very mild to none.. Maybe some nerds had to buy new laptops after the got wiped and now they can never visit defcon without being arrested but that’s it…
Thats a massive invitation to lots of smaller powers with small risk averse military budgets to see what the now proven zero day market can offer them.
D. You looked at option B. and option C. and decide option A isn’t great but it really is the least bad.
Whatever strategy they choose I really hope the next white house manages to learn from history
A few questions.
1)Are these people state sponsored or independent?
2)If independent will china charge them, or are they like Russia; only prosecute criminals that commit crimes at home?
3)Can you share which AV tools detected their malicious activity? I’d like to know which one’s are smart enough not to trust anyone.
Thank you for the great reporting.
…all activity in PRC is either quasi or directly government sponsored…
…this is 1/2 of 1% of what they do every day, and have for at least two decades…
…read the mandiant report…
Great work as usual! I’m wondering if naming these guys might serve to make them heros in China…but on the good side – they might think twice about that vacation in Disneyland…
It is difficult to find sites with clear, actionable security advice. Brian frequently tells us what we can do, especially with personal privacy and financial security.
When our politicians speak about infrastructure they usually mean building roads and buying votes with government money. Perhaps we need more people helping businesses secure their systems. I think a lot of people depend on the Internet and are in over their heads.
Seems like crime and authoritarianism are mutually reinforcing. Democracy and the rule of law are synergistic. You’re not a sucker if you keep to the straight and narrow.
This article only serves to glorify them. No way to touch them in China. They will keep doing what they are doing.
Articles like this is why GRGBanking ATMs distributed through Cummins Allison scare me. GRG’s parent company is listed as a Chinese state-owned company. But US (and worldwide) banks are happily buying them and installing them on their networks because they are cheaper! All the while are we giving the Chinese access to customer banking data and bank network data.
This are the same guy in sacramento..
You’re so interesting! I do not think I’ve read anything like that before.
So good to find somebody with some unique thoughts on this topic.
Really.. thank you for starting this up. This site is something that is required on the internet,
someone with a bit of originality!