Microsoft Corp. has executed a coordinated legal sneak attack in a bid to disrupt the malware-as-a-service botnet Trickbot, a global menace that has infected millions of computers and is used to spread ransomware. A court in Virginia granted Microsoft control over many Internet servers Trickbot uses to plunder infected systems, based on novel claims that the crime machine abused the software giant’s trademarks. However, it appears the operation has not completely disabled the botnet.
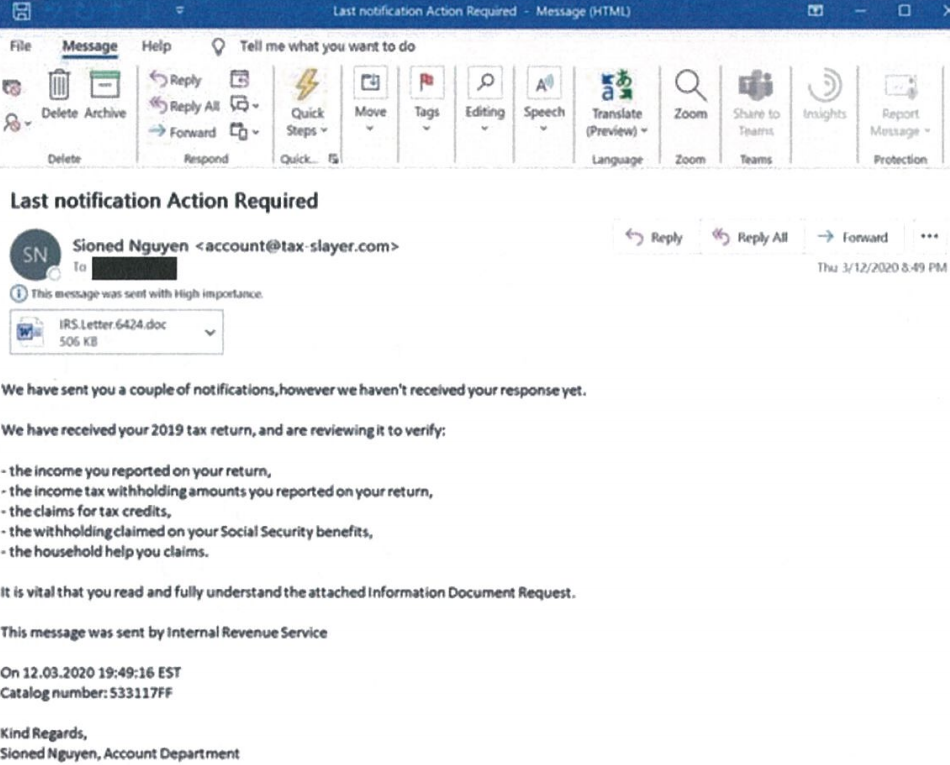
A spam email containing a Trickbot-infected attachment that was sent earlier this year. Image: Microsoft.
“We disrupted Trickbot through a court order we obtained as well as technical action we executed in partnership with telecommunications providers around the world,” wrote Tom Burt, corporate vice president of customer security and trust at Microsoft, in a blog post this morning about the legal maneuver. “We have now cut off key infrastructure so those operating Trickbot will no longer be able to initiate new infections or activate ransomware already dropped into computer systems.”
Microsoft’s action comes just days after the U.S. military’s Cyber Command carried out its own attack that sent all infected Trickbot systems a command telling them to disconnect themselves from the Internet servers the Trickbot overlords used to control them. The roughly 10-day operation by Cyber Command also stuffed millions of bogus records about new victims into the Trickbot database in a bid to confuse the botnet’s operators.
In legal filings, Microsoft argued that Trickbot irreparably harms the company “by damaging its reputation, brands, and customer goodwill. Defendants physically alter and corrupt Microsoft products such as the Microsoft Windows products. Once infected, altered and controlled by Trickbot, the Windows operating system ceases to operate normally and becomes tools for Defendants to conduct their theft.”
From the civil complaint Microsoft filed on October 6 with the U.S. District Court for the Eastern District of Virginia:
“However, they still bear the Microsoft and Windows trademarks. This is obviously meant to and does mislead Microsoft’s customers, and it causes extreme damage to Microsoft’s brands and trademarks.”
“Users subject to the negative effects of these malicious applications incorrectly believe that Microsoft and Windows are the source of their computing device problems. There is great risk that users may attribute this problem to Microsoft and associate these problems with Microsoft’s Windows products, thereby diluting and tarnishing the value of the Microsoft and Windows trademarks and brands.”
Microsoft said it will leverage the seized Trickbot servers to identify and assist Windows users impacted by the Trickbot malware in cleaning the malware off of their systems.
Trickbot has been used to steal passwords from millions of infected computers, and reportedly to hijack access to well more than 250 million email accounts from which new copies of the malware are sent to the victim’s contacts.
Trickbot’s malware-as-a-service feature has made it a reliable vehicle for deploying various strains of ransomware, locking up infected systems on a corporate network unless and until the company agrees to make an extortion payment.
A particularly destructive ransomware strain that is closely associated with Trickbot — known as “Ryuk” or “Conti” — has been responsible for costly attacks on countless organizations over the past year, including healthcare providers, medical research centers and hospitals.
One recent Ryuk victim is Universal Health Services (UHS), a Fortune 500 hospital and healthcare services provider that operates more than 400 facilities in the U.S. and U.K.
On Sunday, Sept. 27, UHS shut down its computer systems at healthcare facilities across the United States in a bid to stop the spread of the malware. The disruption caused some of the affected hospitals to redirect ambulances and relocate patients in need of surgery to other nearby hospitals.
Microsoft said it did not expect its action to permanently disrupt Trickbot, noting that the crooks behind the botnet will likely make efforts to revive their operations. But so far it’s not clear whether Microsoft succeeded in commandeering all of Trickbot’s control servers, or when exactly the coordinated seizure of those servers occurred.
As the company noted in its legal filings, the set of Internet address used as Trickbot controllers is dynamic, making attempts to disable the botnet more challenging.
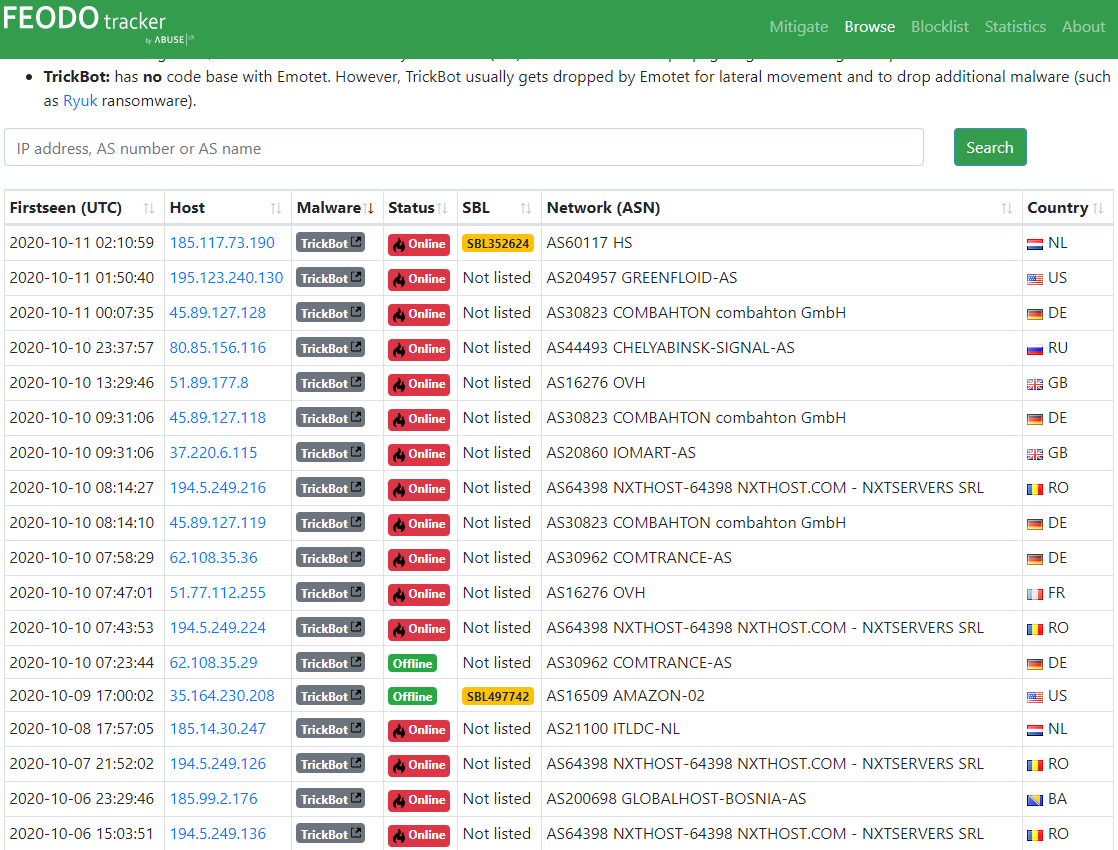
Indeed, according to real-time information posted by Feodo Tracker, a Swiss security site that tracks Internet servers used as controllers for Trickbot and other botnets, nearly two dozen Trickbot control servers — some of which first went active at beginning of this month — are still live and responding to requests at the time of this publication.
Cyber intelligence firm Intel 471 says fully taking down Trickbot would require an unprecedented level of collaboration among parties and countries that most likely would not cooperate anyway. That’s partly because Trickbot’s primary command and control mechanism supports communication over The Onion Router (TOR) — a distributed anonymity service that is wholly separate from the regular Internet.
“As a result, it is highly likely a takedown of the Trickbot infrastructure would have little medium- to long-term impact on the operation of Trickbot,” Intel 471 wrote in an analysis of Microsoft’s action.
What’s more, Trickbot has a fallback communications method that uses a decentralized domain name system called EmerDNS, which allows people to create and use domains that cannot be altered, revoked or suspended by any authority. The highly popular cybercrime store Joker’s Stash — which sells millions of stolen credit cards — also uses this setup.
From the Intel 471 report [malicious links and IP address defanged with brackets]:
“In the event all Trickbot infrastructure is taken down, the cybercriminals behind Trickbot will need to rebuild their servers and change their EmerDNS domain to point at their new servers. Compromised systems then should be able to connect to the new Trickbot infrastructure. Trickbot’s EmerDNS fall-back domain safetrust[.]bazar recently resolved to the IP address 195.123.237[.]156. Not coincidentally, this network neighborhood also hosts Bazar malware control servers.”
“Researchers previously attributed the development of the Bazar malware family to the same group behind Trickbot, due to code similarities with the Anchor malware family and its methods of operation, such as shared infrastructure between Anchor and Bazar. On Oct. 12, 2020 the fall-back domain resolved to the IP address 23.92.93[.]233, which was confirmed by Intel 471 Malware Intelligence systems to be a Trickbot controller URL in May 2019. This suggests the fall-back domain is still controlled by the Trickbot operators at the time of this report.”
Intel 471 concluded that the Microsoft action has so far has done little to disrupt the botnet’s activity.
“At the time of this report, Intel 471 has not seen any significant impact on Trickbot’s infrastructure and ability to communicate with Trickbot-infected systems,” the company wrote.
The legal filings from Microsoft are available here.
Update, 9:51 a.m. ET: Feodo Tracker now lists just six Trickbot controllers as responding. All six were first seen online in the past 48 hours. Also added perspective from Intel 471.




Copyright is not at all the same thing as trademark. You should get your story and your headline in sync.
That was an oversight that was corrected less than a minute after this story was published. Unfortunately, the URL that gets populated included the mistake, as did the newsletter.
To err is human.
“To forgive is divine “
While to forgive is devine, it’s not our company’s policy.
To really screw things up, you need a computer.
can you put in a redirect to force the URL to be better?
That Feodo Tracker website is a good source of information !
Curious if there is an easy way to detect if you have Trickbot infected systems?
Trickbot is memory resident, doesn’t leave files behind, and is used for lateral movement. Generally it latches onto existing services if memory serves. You have to find and eliminate the compromised bastion host(s) after plugging the holes that let them in and competent attackers have multiple toolkits to gain persistence with and will “walk you up the value chain” from the easy stuff to the more difficult stuff when you respond. A good way to handle this is to have a SIEM that is aggregating shell commands to a central spot, and a well curated firewall with traffic segregated into multiple policies and zones, and to analyze traffic on a per-policy basis. You reboot everyone at the same time and that will often reveal the bastion host.
Any idea what operating system makes up the majority of these infected machines? Wondering if they are old Windows 7 and XP devices?
“Any idea what operating system makes up the majority of these infected machines? Wondering if they are old Windows 7 and XP devices?”
——————-
You are asking the wrong question
Are these systems under the operation of Windows Security Experts (Like Myself), or mere Windows Professionals, as they like to call themselves
I have been running Windows XP-SP2 online since before the wannacry attack and have NEVER been a victim of ransomware of any type, regardless of the shady malware sites I research
My XP box has ZERO Microsoft security updates installed and is running under a Full Admin Account ONLINE!
The NSA, CIA, Israeli Military, N. Korea, Chinese Military and Russia cannot wreck this XP installation, now or ever and it will remain malware free for many years to come
A mere Professional on the other hand……
OMG
Thanks! That was the dumbest thing I’ve read all day…and this is 2020!
LoL
Security Noobs
> “I have been running Windows XP-SP2 online since before the wannacry attack and have NEVER been a victim of ransomware of any type, regardless of the shady malware sites I research”
Obvious bait is obvious. Thanks for the laugh.
IP address or you’re lying.
I’m reminded of a friend of mine who thought he was clever and bragged online that his Windows 98SE machine could never be commandeered because it didn’t have enough of an attack surface for someone to hijack. He didn’t use those words but that’s the basic thought behind it. This is when 98SE was still getting patches, so it’s not quite like XP guy here.
Of course he was a jackass online to all the wrong kinds of people and wasn’t smart enough not to download executables from the wrong corners of the internet, so within a couple days he ended up bringing his system to me because “his mouse started moving on its own.” Ended up building him a whole new system on a different OS (I think it was XP) and a hardware firewall.
He ran with that setup for a couple more years until he had another incident caused by downloading executables… thankfully he stopped taunting people about his computer’s invincibility.
WOW….Just….WOW!
I seriously doubt that YOU could be trusted to tell the truth if I give you my I.P. address
Just ask Brian Krebs if I was viewing this post using Windows XP-SP2 @ 10:10P.M. Central Time
on October 12, 2020
He wouldn’t LIE would he?
Unbelievable
Anyone can forge a browser signature.
It doesn’t appear you know anything about cybersecurity, or else you would not hold up a browser useragent string as proof.
If your bold (nonsense) claim were true, then you would not need to “trust” Michael at all. You could give him your IP address and let your superior hardening skills speak for itself.
Go ahead, post your public IP.
> “Are these systems under the operation of Windows Security Experts (Like Myself), or mere Windows Professionals, as they like to call themselves”
Come on everybody, this is such an obvious troll that he might as well be waving at you from under a bridge.
I don’t think it is wise to brawl who you are and what you research while sitting online with admin acc. People leave digital traces everytime they are getting an account somewhere. Don’t you think someone wouldn’t be sniffing traffic to look for the data being sent? Or that some crooks may, in theory, hack this website to look for your email, and thus trace you? Man, this is ridiculously risky. Still what you stated at least for Windows 7 is mostly true, there’s no fully trusted environments, and if you add external security you can get a resemblance of trusted system, even when the OS no longer supported.
Bad troll is bad
A quick check of the Feodo Tracker site at 9:45 EST shows that only 6 trickbot servers listed in the graphic above remain online.
Bravo, Microsoft!
One huge clue is the bad grammar used in that email shown at the bottom of your article. Nobody from the IRS is going to communicate with us in that sloppy of an email.
That defense only works for people who know grammar. 😉
While the grammer was okay, I got an official email from Washington State (a tax reminder) that looked very much like spam: few/no graphics, lots of colored text, several short paragraphs. I had to go and look up the phone numbers and websites listed, and didn’t click any links.
Ultimately, I was able to determine it was authentic, but I sent them a note that they needed to work on their formatting a bit.
That’s actually the point. They’re trying to infect less educated people’s computers, who are less likely to notice their computer is acting funny, less likely to have 2-factor on their accounts, and won’t have alerts set at their bank.
A very similar effect is used on spam-based scams, when they make it obvious it’s a scam to select only the most gullible victims.
You obviously aren’t very familiar with a lot of people 🙂
Never ceases to amaze me when we know where the systems are running but no one shuts them down? OVH. Always has a little something brewing in their infrastructure. You can do an abuse report but they don’t really try and help. Must be needing the server rental money. It’s like trying to hold onto jello, just squeeze and it goes somewhere else.
Between the thousands of poorly maintained WordPress sites and “first month free” VPS hosting that you can register for using a yandex email, its a hackers paradise. What’s not to love?
Of course OVH is one of the ISP’s. I would have been shocked if they were not there. A cesspool of contamination.
Has Microsoft provided any details about how, exactly, they will “assist Windows users impacted by the Trickbot malware in cleaning the malware off of their systems”? I sincerely hope that they’re not going to cold call people and announce that “This is a call from Microsoft. We’ve detected and infection on your computer.” It’s been hard enough getting my friends and family to stop responding to calls and emails like that! I’ve always told anyone who will listen that Microsoft will never call you out of the blue to offer you technical support, and I sincerely hope they’re not going to start now.
It stands to reason that if they now control a large number of Trickbot controllers, they could easily see the IP addresses and perhaps other info related to infected systems. If they have any telemetry from that, it may be useful for pushing specific updates to those systems. However, I should say I have no insight into what they may or may not do or be able to do in this regard.
@BrianKrebs – yes, I was wondering if that was what you were suggesting (pushing targeted updates to specific users). That would be kind of interesting if they can actually do that, but I’d also be surprised if they had that capability because it seems like it would be difficult and expensive to implement that level of “personalized” attention. Plus it would open them up to potential privacy concerns and all that comes with them. I’m not sure how I would feel about it if I knew that they were sending targeted updates specifically to me because of information they have about my system that I may not even be aware of. But, then again, I suppose that’s exactly what happens every time we install updates … perhaps it wouldn’t really be that different.
Historically speaking, the clean up efforts from Microsoft have been a combination of outreach to ISPs and CERTs worldwide providing information on infected IP addresses within that IP space and adding the family of malware to the MSRT (which runs monthly on 1B+ computers each month- I would expect that to happen tomorrow if they still follow the schedule of second Tuesday release).
Once you have the C2 Servers, it is generally trivial to reverse engineer the codebase and generate a patch and incorporate that patch into monthly security updates. Trickbot itself, if memory serves, is not file resident, however. You knock out Trickbot’s C2’s, and once the remote systems reboot you’re clean.
The biggest issue with the Emotet group and malware is is they are selling access to 3rd parties as part of the monetization chain. Their monetization chain goes something like, and Brian you should do an Expose’ on this at some point (or maybe you have? I don’t read daily tbh), they infect the targeted infrastructure, gain persistence and auction access.
If at a certain point nobody, such as a national government, buys access, they then proceed to deploy automated toolkits to gather data off of end user stations including things like domain admin passwords that are poorly kempt. Good way to tell if access has been sold is if they are manually customizing e-mails to your org or if you just have a few IP’s off of Cryptolameus’s or Abuse.ch’s websites then the trail ends on your firewall logs.
If someone has credit card numbers stored in chrome, they’ll nab for example with IcedID. At that point they assess the system for a coinminer or host. If you plug and chug IP’s off of cryptolaemus group’s or abuse.ch websites into shodan.io you’ll find almost every host they are using has a vulnerability and they rotate places like a roving gang between warehouses. They’ll sit at a place for 2 weeks, move on, sit another place 4 weeks, then move back and so forth.
At that point the final step in the monetization chain, which can be as little as a week or as long as 2-3 months, is Ryuk. Which, BTW, they messed up in December 2019 so all it did was trash data.
If you’ve been targeted by a group and access has been sold, and you start responding, they may walk you up the value chain. You’ll get e-mails from linkedin contacts or e-mails with links to wordpress websites that have been compromised and use zero day exploits for the browser, and so on and so forth.
They have a specific business model and a tremendous amount of automation and it’d be interesting, Brian, for you look into them and maybe get someone who knows their tools and can talk about the evolution of that business model. Because they have been known to service national governments, they have favors to pull in like any mobster and I don’t think the public knows much about them. I think what you’re looking at there is the future of cybercrime, the first real mobsters.
Anyway. Good to see the us military and MS are doing something about these jagoffs. A lot of the reason probably has to do with zerologon….
@Steve –
Well there is always the “Microsoft Malicious Software Removal Tool”, that is often accompanying updates, but I’m sure trickbot probably can defeat that using file camouflage, and also perhaps simply turning off or disabling updates, and WSUS servers.
it’s interesting that they can just “shut down” these servers. but in a non-election year let them run rampant? Why not just shut them down ALL THE TIME. I know anti-ransomware, next gen AV,etc are HUGE businesses that rely on the fear of an infection, but this was a little obvious; hey we can shut this stuff down whenever we want, we just normally don’t want to?? someone correct me, because I can’t be right.
Everything is a tradeoff between taking down servers and putting up more servers, and on both ends the motivation is money. For the bad guys, the more servers they can deploy, the more money they can potentially make. Unfortunately, on the other side of the equation, you’ll need to hire teams of people with fat salaries, 401Ks, and dental insurance and have that as their sole job around the clock.
Unless that dynamic changes, the good guys will always be swimming upstream and it’s like putting out a wildfire with a garden hose.
I wonder if someone could explain something to a lay person.
“A court in Virginia granted Microsoft control over many Internet servers”
“Microsoft said it will leverage the seized Trickbot servers”
In the context of these two statements, what exactly is meant by “control” and “seized”? This is not physical control is it? If MS is now “controlling” these servers remotely, presumably through some feature of the OS, can’t the perps just physcially turn them off or shut off the VM they are running on?
The court in Virginia is a US Federal Court, not a state court. So its jurisdiction covers the US and its court orders are often adhered to by our friends outside of the US.
Microsoft: “There is great risk that users may attribute this problem to Microsoft.”
If the shoe fits. Macros need to die, die, die. They were always just a gimmick. It should take a ridiculous and extreme amount of effort for a Word document macro to execute. Instead, it’s just one wrong click, and the systems is toast.
Does this at all help them catch the operators? IMO these guys should get a minimum of 10 years in prison. Causing loss of millions. And, why is this site not mobile friendly?
Said “… Guys should get a minimum of 10 years in prison.”
How in the hell are you going to put them in prison when the felon has been convicted but the foreign government won’t cooperate or extradite the SOB?
“Catch me if you can!” SMH.
Maybe put a bitcoin bounty on his head? Prolly won’t work.
If the other countries won’t cooperate to take down these thieves then the CIA should be given a “dead or alive” license to hunt and kill them worldwide. The damage they do is massive, even to organizations not directly infected– Even small organizations have to hire IT guys just to keep this nasty ransomware out.
And if it’s a 14 year old kid?
They’ll probably have to aim a little lower.
I didn’t get any OTP so please send me in flipkart