A company that rents out access to more than 10 million Web browsers so that clients can hide their true Internet addresses has built its network by paying browser extension makers to quietly include its code in their creations. This story examines the lopsided economics of extension development, and why installing an extension can be such a risky proposition.

Singapore-based Infatica[.]io is part of a growing industry of shadowy firms trying to woo developers who maintain popular browser extensions — desktop and mobile device software add-ons available for download from Apple, Google, Microsoft and Mozilla designed to add functionality or customization to one’s browsing experience.
Some of these extensions have garnered hundreds of thousands or even millions of users. But here’s the rub: As an extension’s user base grows, maintaining them with software updates and responding to user support requests tends to take up an inordinate amount of the author’s time. Yet extension authors have few options for earning financial compensation for their work.
So when a company comes along and offers to buy the extension — or pay the author to silently include some extra code — that proposal is frequently too good to pass up.
For its part, Infatica seeks out authors with extensions that have at least 50,000 users. An extension maker who agrees to incorporate Infatica’s computer code can earn anywhere from $15 to $45 each month for every 1,000 active users.
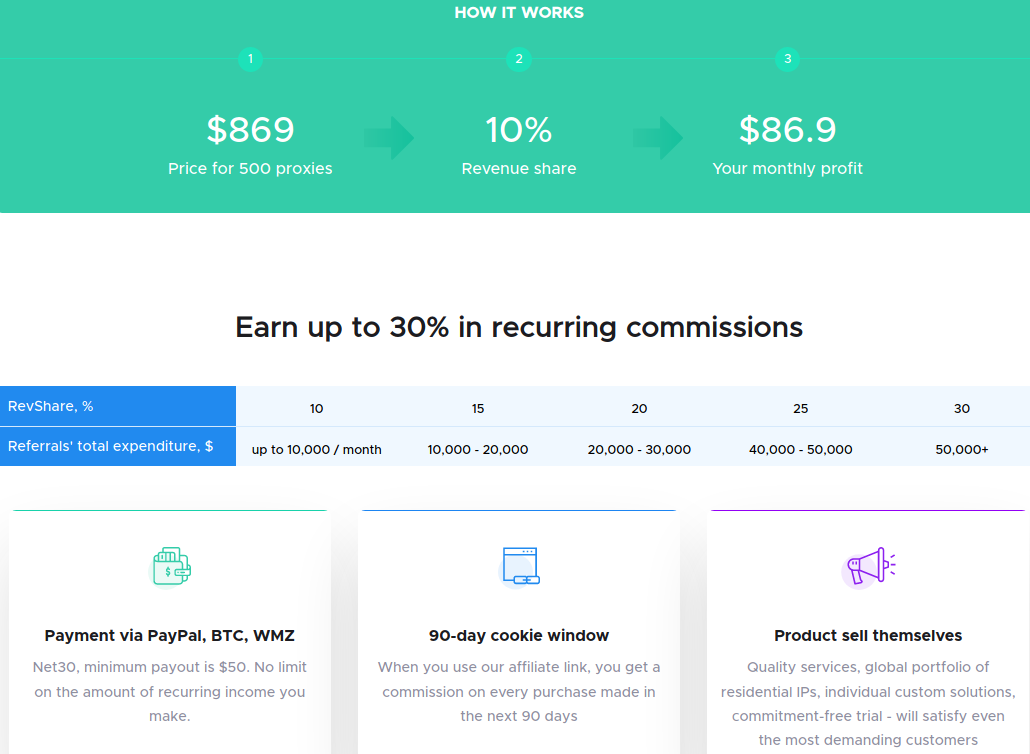
An Infatica graphic explaining the potential benefits for extension owners.
Infatica’s code then uses the browser of anyone who has that extension installed to route Web traffic for the company’s customers, including marketers or anyone able to afford its hefty monthly subscription charges.
The end result is when Infatica customers browse to a web site, that site thinks the traffic is coming from the Internet address tied to the extension user, not the customer’s.
Infatica prices its service based on the volume of web traffic a customer is seeking to anonymize, from $360 a month for 40 gigabytes all the way to $20,000 a month for 10,000 gigabytes of data traffic pushed through millions of residential computers.
THE ECONOMICS OF EXTENSIONS
Hao Nguyen is the developer behind ModHeader, an extension used by more than 400,000 people to test the functionality of websites by making it easier for users to modify the data shared with those sites. When Nguyen found himself spending increasing amounts of his time and money supporting the extension, he tried including ads in the program to help offset costs.
ModHeader users protested loudly against the change, and Nguyen removed the ads — which he said weren’t making him much money anyway.
“I had spent at least 10 years building this thing and had no luck monetizing it,” he told KrebsOnSecurity.
Nguyen said he ignored multiple requests from different companies offering to pay him to insert their code, mainly because the code gave those firms the ability to inject whatever they wanted into his program (and onto his users’ devices) at any time.
Then came Infatica, whose code was fairly straightforward by comparison, he said. It restricted the company to routing web requests through his users’ browsers, and did not try to access more sensitive components of the user’s browser experience, such as stored passwords and cookies, or viewing the user’s screen.
More importantly, the deal would net him at least $1,500 a month, and possibly quite a bit more.
“I gave Infatica a try but within a few days I got a lot of negative user reviews,” he said. “They didn’t like that the extension might be using their browser as a proxy for going to not so good places like porn sites.”
Again he relented, and removed the Infatica code.
A TARGET-RICH ENVIRONMENT
These days, Nguyen is focusing more of his time on chrome-stats.com, which provides detailed information on more than 150,000 extensions. The service is free for limited use, but subscribers who pay a monthly fee can get access to more resources, such as older extension versions and details about their code components.
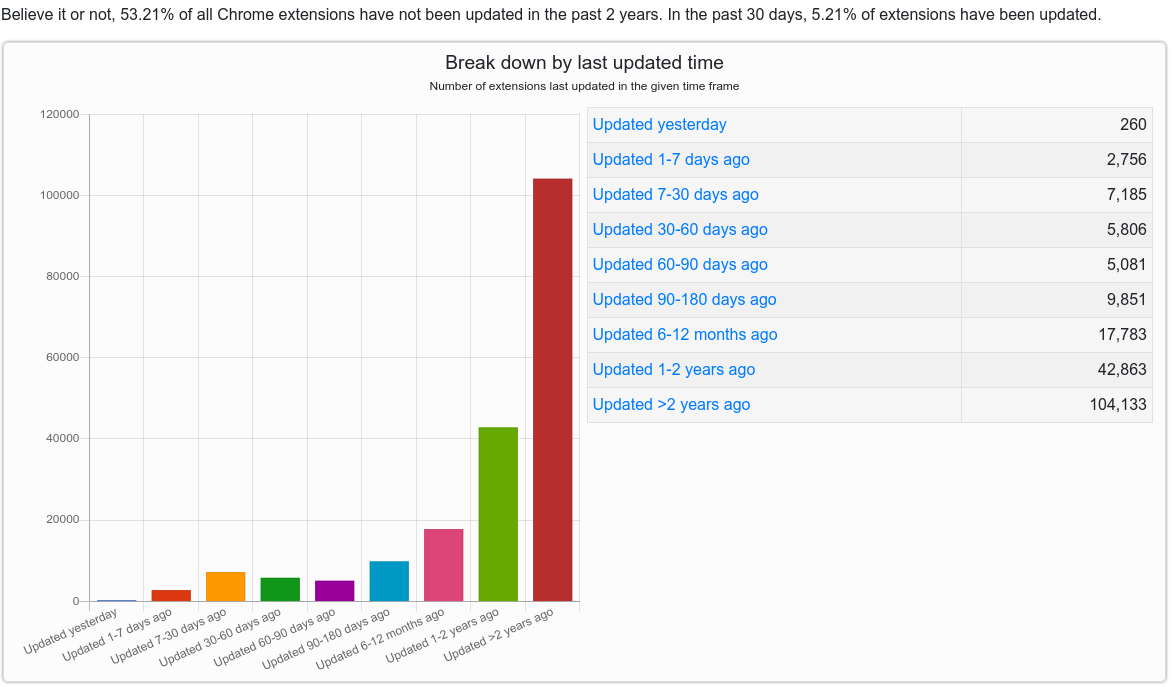
According to chrome-stats.com, the majority of extensions — more than 100,000 of them — are effectively abandoned by their authors, or haven’t been updated in more than two years. In other words, there a great many developers who are likely to be open to someone else buying up their creation and their user base.
The vast majority of extensions are free, although a handful that have attracted a large and loyal enough following have been able to charge for their creations or for subscription services tied to the extension. But last year, Google announced it was shutting down paid Chrome extensions offered on its Chrome Web Store.
Nguyen said this will only exacerbate the problem of frustrated developers turning to offers from dodgy marketing firms.
“It’s a really tough marketplace for extension developers to be able to monetize and get reward for maintaining their extensions,” he said. “There are tons of small developers who haven’t been able to do anything with their extensions. That’s why some of them will go into shady integration or sell the extension for some money and just be done with it.”

A solicitation sent by Infatica to the developer of the SponsorBlock extension. Image: sponsor.ajay.app
WHO IS INFATICA?
It is unclear how many extensions currently incorporate Infatica’s code. KrebsOnSecurity searched for extensions that invoke several domains tied to Infatica’s Web proxy service (e.g., extendbalanc[.]org, ipv4v6[.]info). This research was conducted using Nguyen’s site and crxcavator.io, a similar extension research site owned by networking giant Cisco Systems.
Those searches revealed that Infatica’s code has been associated with at least three dozen extensions over the past few years, including several that had more than 100,000 users. One of those is Video Downloader Plus, which at one point claimed nearly 1.4 million active users.
The founder and director of Infatica — a resident of Biysk, Russia named Vladimir Fomenko — did not respond to multiple requests for comment.

Infatica founder Vladimir M. Fomenko.
Fomenko is the sole director of the iNinja VPN, another service that obfuscates the true Internet address of its more than 400,000 users. It stands to reason that iNinja VPN also is not only offering its customers a way to obfuscate their Internet address, but is actively using those same systems to route traffic for other customers: A Chrome browser plugin and ad blocker by the same name whose code includes Infatica’s “extenbalanc” domain has 400,000 users.
That would put Infatica in line with the activities of another major controversial VPN/proxy provider: Luminati, a.k.a. “HolaVPN.” In 2015, security researchers discovered that users of the HolaVPN browser extension were being used to funnel Web traffic for other people. Indeed, in the screenshot above, Infatica’s marketing team can be seen comparing its business model to that of HolaVPN.
Fomenko has appeared in two previous KrebsOnSecurity stories; both concerned King Servers (a.k.a. “Hosting Solution Ltd.“), a hosting company he has operated for years which caters mostly to adult websites.
In 2016, hackers suspected of working for Russian state security services compromised databases for election systems in Arizona and Illinois. Six of the eight Internet addresses identified by the FBI as sources of the attack traced back to King Servers. In an interview with The New York Times several months later, Fomenko flatly denied having any ties to the hacking.
According to the Russian daily Novaya Gazeta, revelations about the 2016 hacking incident’s ties to King Servers led to treason charges against Sergey Mikhaylov, the former deputy chief of Russia’s top anti-cybercrime unit.
Russian authorities charged that Mikhaylov had tipped off the FBI to information about Fomenko and King Servers. In 2019, Mikhaylov was convicted and sentenced to 22 years in a penal colony.
BE SPARING IN TRUSTING EXTENSIONS
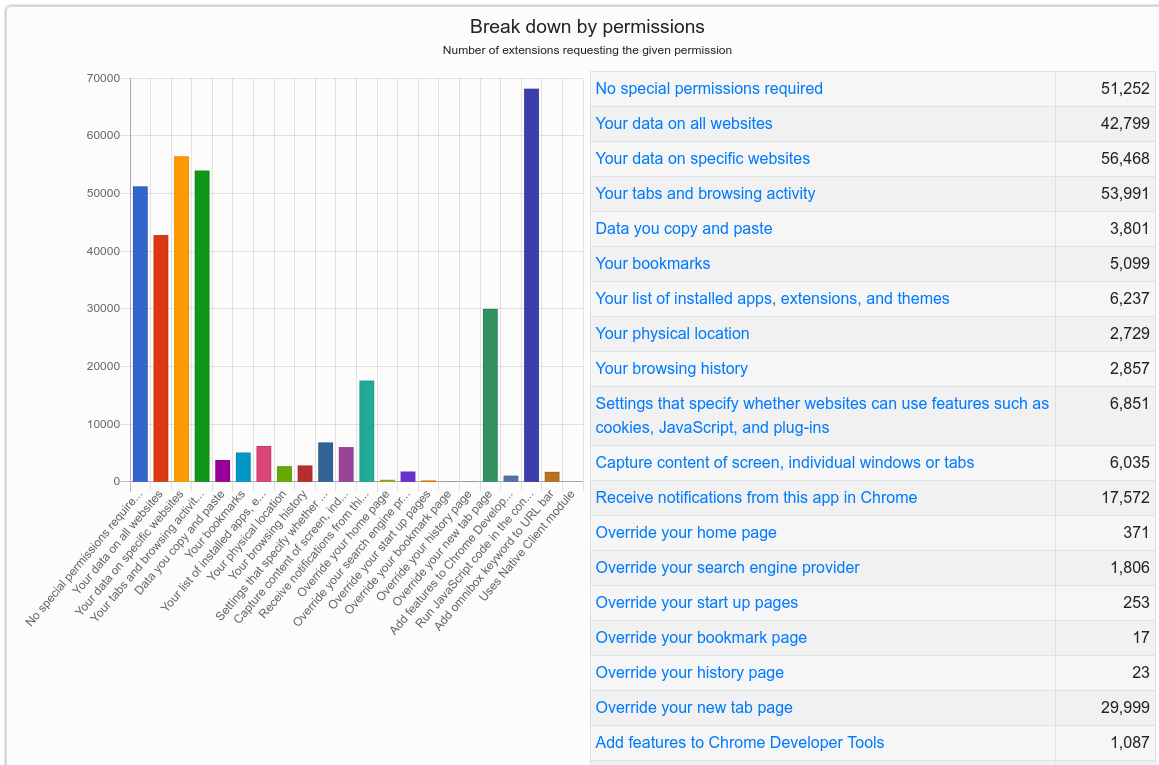
Browser extensions — however useful or fun they may seem when you install them — typically have a great deal of power and can effectively read and/or write all data in your browsing sessions. The powers granted to each extension are roughly spelled out in its “manifest,” basically a description of what it will be able to access once you incorporate it into your browser.
According to Nguyen’s chrome-stats.com, about a third of all extensions for Chrome — by far the most widely-used Web browser — require no special permissions. But the remainder require the user to place a good deal of trust in the extension’s author. For example, approximately 30 percent can view all of your data on all or specific websites, or index your open tabs and browsing activity.
More than 68,000 Chrome extensions allow the execution of arbitrary code in the context of webpages, effectively allowing the extension to alter the appearance and functionality of specific sites.
I hope it’s obvious by this point, but readers should be extremely cautious about installing extensions — sticking mainly to those that are actively supported and respond to user concerns.
Personally, I do not make much use of browser extensions. In almost every case I’ve considered installing one I’ve been sufficiently spooked by the permissions requested that I ultimately decided it wasn’t worth the risk, given that any extension can go rogue at the whims of its author.
If you’re the type of person who uses multiple extensions, it may be wise to adopt a risk-based approach going forward. Given the high stakes that typically come with installing an extension, consider carefully whether having the extension is truly worth it. This applies equally to plug-ins designed for Web site content management systems like WordPress and Joomla.
Do not agree to update an extension if it suddenly requests more permissions than a previous version. This should be a giant red flag that something is not right. If this happens with an extension you trust, you’d be well advised to remove it entirely.
Also, never download and install an extension just because some Web site says you need it to view some type of content. Doing so is almost always a high-risk proposition. Here, Rule #1 from KrebsOnSecurity’s Three Rules of Online Safety comes into play: “If you didn’t go looking for it, don’t install it.” Finally, in the event you do wish to install something, make sure you’re getting it directly from the entity that produced the software.
Google Chrome users can see any extensions they have installed by clicking the three dots to the right of the address bar, selecting “More tools” in the resulting drop-down menu, then “Extensions.” In Firefox, click the three horizontal bars next to the address bar and select “Add-ons,” then click the “Extensions” link on the resulting page to view any installed extensions.




What are your thoughts on NoScript for Firefox?
Noscript is not used as much as Https Everywhere, b/c it breaks too many websites for me.
My Extension List
AD Block adblock.com
Download Chrome Extension opera.com
Google Analytics Opt Out google.com
Https Everywhere eff.org
Privacy Badger eff.org
Modify Header Value HTTP mybrowseraddon.com
User-Agent Switcher mybrowseraddon.com
WebRTC Control mybrowseraddon.com
Trafficlight bitdefender.com
WebRTC Leak Prev github
AnonTab anon.com
DecentralEyes decentraleyes.org/test
NoScript Suite Lite mybrowseraddon.com
Change Timezone mybrowseraddon.com
Country flag website’sr mybrowseraddon.com/flag-pl
thanks!
I’ve started to use uBlock Origin ever since I heard about AdBlock getting paid to keep specific ads going.
I like uBlock Origin for the zapper feature, but for fine control I prefer uMatrix, since it allows per component blocking (script, XHR, frame, media, etc.) blocking rather than just domain. I use them together.
> AD Block adblock.com
There is no reputed content blockers which match this name and site. I advise you look again into your choice of content blocker.
Works OK for me, but as the OP noted I do have to provide exceptions so take it on a case-by-case basis. I also use an adblocker (and some sites hate it, so I ignore them and move on).
I’ve been using Chrome w/ site default of not allowing scripts and not loading images for years.
Giorgio Maone is a good guy. And he long ago found a way to make money w/o going down this dark path.
I can’t find a current list of the Mozilla Security Group members (bit-rot is so much fun).
That said, the point of Brian’s article is that just because an extension author is well behaved today doesn’t mean the extension will be well behaved tomorrow.
An incident of this type with a very popular Chrome add-on called The Great Suspender happened a few weeks ago. Took months for Google to remove the add-on from the store:
https://github.com/greatsuspender/thegreatsuspender/issues/1263
Yes, see also
https://www.ghacks.net/2021/01/09/we-no-longer-recommend-the-chrome-extension-the-great-suspender-here-is-why/
See also https://lwn.net/Articles/846272/
NoScript is tagged with “Recommended” that means Mozilla verifies any code updates.
If you are using Firefox extensions, Mozilla and “Recommended” are safe to use.
https://support.mozilla.org/en-US/kb/add-on-badges?utm_source=addons.mozilla.org&utm_medium=referral&utm_content=promoted-addon-badge
This is reassuring, but doesn’t help in cases where something nasty has been added in a new release of an extension you already have installed. In some cases that would at least trigger FF to ask you to permit additional permissions, but not always…
The recommended program does involve verification of updates, AFAIK. Its certainly better than the Chrome situation
Which permissions would you consider safe for an extension to have? the only permissions my extensions have are “read browser data”
That means it can see everything your doing. That is not quite as dangerous as full permission but in the same vein it is not nothing. Essentially you could be giving up your privacy.
I’ve been using one tab eetension,I hope it’s safe,otherwise the user doesn’t have the choice but to create itself the extension he/she wants
The WP/Joomla example is a poignant one. A few years ago, there was a scandal in the online marketing world when it was discovered a company had been purchasing well-installed plugins, changing the code, then using it as a means to inject backlinks to game Google. I can’t remember all the details, but I believe it still goes on.
Use Brave browser – I feel like pages download much quicker but some financial sites do not allow me to login.
Good browser. But also made the news recently regarding a tor feature that was leaking private information.
Also not too long ago they got caught inserting their own affiliate link into a crypto currency web page.
They also recently got busted inserting their own affiliate link into a crypto currency website.
they fixed it.
So do they deserve kudos for removing it or continuing suspicion for thinking inserting was a good idea in the first place? I know which I choose.
“sticking mainly to those that are actively supported” I agree with this statement
Well, except if the supporter(s) have bought-into getting paid to add bad code… They wouldn’t tell you.
I use 4 –
uBlock Origin
HTTPS Everywhere
Roboform Password Manager
Sort Bookmarks (Firefox)
Neater Bookmarks replaces Sort Bookmarks for Edge.
No issues.
You wouldn’t know of an issue, until months after.
Maybe a year. Long after it’s too late.
We try to stay away from password managers as browser extension.
Best to have its own app. Better still, it’s own sandbox or VM.
It was a bit ironic and funny reading this article and seeing you take a quote about how hard it is to monetize these types of programs, and make it into a pull-quote **using a WordPress plugin that I developed** (“Graceful Pull-Quotes”).
That plugin has (at minimum) thousands of users, and I rarely see a dime for my trouble.
Which, honestly, is fine. I made it because it was something I wanted to exist, and decided to share it with other users. Yes, a donation once in a while would be nice, but I’m not surprised that I don’t see them. Perhaps my attitude would change if the plugin required a lot of ongoing upkeep.
I do once in a rare while get a come-on to put links on my site in exchange for payment. Haven’t said “yes” yet.
Great article Brain. But Internet criminals do not primarily buy proxies to hide their IP. TOR I2P is used for these purposes. The proxy serves as the final output for cyber criminals because many servers have TOR exitnodes blacklisted, such as financial institutions such as banks, some social networks, local price comparators, local bazaar portals, crypto exchanges, local hosting providers, etc. These servers usually allow access to the site but do not allow registration or login if they detect tor exit nod, so the Internet fraudster needs to use a local residental proxy. . Imagine a Polish or Hungarian price comparator and a fraudster wants to add 1000 fake positive reviews to criminals fraudulent eshop on this local price comparator. For this purpose, a criminal needs a large number of residental(polish) IP addresses to create fake accounts … The same is true if you do bank fraud or, for example, need to hire money mule on a social network and need a fake account. Proxy is also used for phishing accounts (fraudster needs to log in through the proxy so that the account is not blocked), etc. Every professional cyber criminal (fraudster) who operates on clierwebe uses TOR / I2P and resident proxies. security features of web servers can detect and blacklist tor exit nodes, but all residental proxy servers no one will ever be able to blacklist.I’m an Ex cyber fraudster so I know what I’m talking about.
^— this
Working in the general “traffic proxy” industry has made one thing overwhelmingly clear. Any business who can provide IP addresses and decent bandwidth that reliably classifies as being residential… is guaranteed shady. Especially if they don’t care what kind of traffic you’re wanting to pass.
Small typo, missing the verb in “there a great many developers”.
Keep up the great work! 🙂
https:// is just the way things are going now…
you can still sandbox your browser or run it off a usb and isolate it doesnt take much to test the extention
also check the back end of the xpi
about:config see whats good….
Firefox is still way safer then chrome cause of all the background crap it does with service host….why it needs all the ram….for what should be lower then 30% even if its heavy on usage….https just deal with it, its like adobe flash its just getting phased out
Brave is good even using a emulator and that browser is good enough its not hard to hop proxy and re-direct
There are far too many bugs in software in general – software created by large corporations like Google, Microsoft, etc.
Why would anyone trust that there aren’t major vulnerabilities in extensions created by (in most cases) a single developer?
The reasons a lot of extensions aren’t maintained or well documented is that doing endless bug fixes, docs, and satisfying complaining users is a lot of drudgery. For developers, it’s a lot more fun developing new code and since there isn’t any monetary incentive to grind out documentation and update what they produced, they blow it off. This is why packages in the open source world have crappy documentation and support. There’s also a belief by some that if you don’t know how to fix it and use it then you’re too dumb to be bothered with.
The reason why commercial software has better documentation and support is that the developers are on salary with benefits and there’s a boss over them making them grind through the bug fixes and mind numbing documentation.
This is probably a dumb question, but if you wouldn’t mind: Brian mentions 4KVideo Downloader. I have this program installed as a standalone, not a browser extension. Am I still at risk?
Brian does not mention 4K Video Downloader; he mentions Video Downloader Plus, which is completely unrelated. 4K Video Downloader is safe.
I had no idea of these things.
RE:mr-wendel.
Internet fraudsters prefer to use illegal proxy botnets, because many “legal” proxy providers modify http header (they add information there that it is a proxy server).
and “data center” legal proxy providers usually use minority ISP providers which are also often blacklisted.
Cyber criminals do not need high connection speed or scalability,criminals usually use proxies only for simple tasks such as registering accounts or accessing accounts in web servers where it is not possible to use TOR or VPN.
Very used proxy providers for fraudsters are for example luxsocks(+-25% have financial institusion blaclisted ) or vip72(+-60% blaclisted) and my choice was AWMproxy (10-12% blacklisted) etc.
AWMproxy is so good ilegal proxy botnet..
Legal proxy providers are mostly used for “web-scaping” for marketing purposes or on captcha bypass in spamming bots etc. These are not mostly static but dynamic rotary proxies, but usually they are unsuitable for standard blackhat use (like fraud,theft etc).
I have used Avast for 15 years or more. I have just become aware that Avast has provided botnet protection since July 2020 and am optimistic that it will be good protection for the issues raised in Brian’s article.
“Do not agree to update an extension if it suddenly requests more permissions than a previous version. This should be a giant red flag that something is not right. If this happens with an extension you trust, you’d be well advised to remove it entirely.”
That’s a little too strong of an approach IMO. If something like that happens, that’s not always a giant red flag. Maybe read the change log of the extension and see if they needed to change or add permissions for some reason? I’ve seen it happen for legitimate reasons. Sometimes Firefox or Chrome changes certain things about permissions that extension devs have to respond to.
It’s at least a yellow flag.
If software has changed ownership or directorship, then the change log won’t necessarily be trustworthy.
And 99% of users won’t be able to understand the source code.
A viable income stream is definitely a problem (even Firefox itself is suffering in this category).
As always, a great article that attempts to point out to users the pitfalls of their systems in a manner easily understood and yet giving experts the needed detail.
I admit I have a few extensions that likely need revisiting (shopping) and some including script/tracking that I have no idea if they were updated since 2020.
My recommendation is to do a reset and cleanup, which Chrome offers. I will ‘spring clean’ all my browseirs, removing all extensions and carefully vet what to reinstall.
I keep (had kept?) a VM w/ Brave solely for financial / company link / router & security config.
I’ve a few non-browser vendor sourced extensions, IP Tools, Bookmarks sorter, etc. However I keep them turned off for the most part. Is that safe? Secondly, is there a way to scan a just installed extension with an AV and get a positive hit if it is fishy. Or would an AV not be able to detect it as nefarious?