A little over a year ago, the FBI and law enforcement partners overseas seized WeLeakInfo[.]com, a wildly popular service that sold access to more than 12 billion usernames and passwords stolen from thousands of hacked websites. In an ironic turn of events, a lapsed domain registration tied to WeLeakInfo let someone plunder and publish account data on 24,000 customers who paid to access the service with a credit card.

For several years, WeLeakInfo was the largest of several services selling access to hacked passwords. Prosecutors said it had indexed, searchable information from more than 10,000 data breaches containing over 12 billion indexed records — including names, email addresses, usernames, phone numbers, and passwords for online accounts.
For a small fee, you could enter an email address and see every password ever associated with that address in a previous breach. Or the reverse — show me all the email accounts that ever used a specific password (see screenshot above). It was a fantastic tool for launching targeted attacks against people, and that’s exactly how the service was viewed by many of its customers.
Now, nearly 24,000 WeLeakInfo’s customers are finding that the personal and payment data they shared with WeLeakInfo over its five-year-run has been leaked online.
In a post on the database leaking forum Raidforums, a regular contributor using the handle “pompompurin” said he stole the WeLeakInfo payment logs and other data after noticing the domain wli[.]design was no longer listed as registered.
“Long story short: FBI let one of weleakinfo’s domains expire that they used for the emails/payments,” pompompurin wrote. “I registered that domain, & was able to [password] reset the stripe.com account & get all the Data. [It’s] only from people that used stripe.com to checkout. If you used paypal or [bitcoin] ur all good.”
Cyber threat intelligence firm Flashpoint obtained a copy of the data leaked by pompompurin, and said it includes partial credit card data, email addresses, full names, IP addresses, browser user agent string data, physical addresses, phone numbers, and amount paid. One forum member commented that they found their own payment data in the logs.
According to DomainTools [an advertiser on this site] Wli[.]design was registered on Aug. 24, 2016 with Dynadot, the domain registrar which also was used to register WeLeakInfo.com. On March 12, wli[.]design was moved to another registrar — Namecheap.
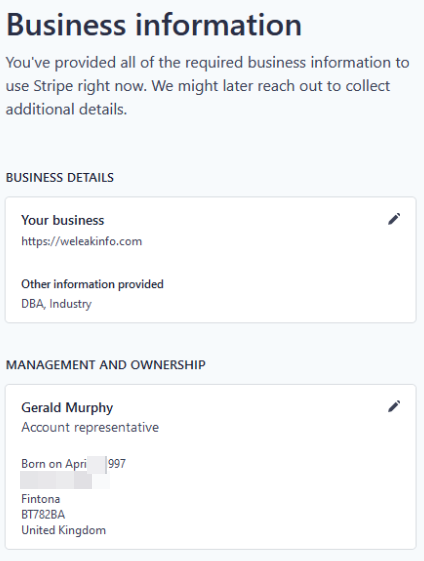
Pompompurin released several screenshots of himself logged in to the WeLeakInfo account at stripe.com, an online payment processor. Under “management and ownership” was listed a Gerald Murphy from Fintona, U.K.
Shortly after WeLeakInfo’s domain was seized by authorities in Jan. 2020, the U.K.’s National Crime Agency (NCA) arrested two individuals in connection with the service, including a 22-year-old from Fintona.
PLENTY OF TIME FOR OPSEC MISTAKES
It’s been a tough few months for denizens of various hacking forums, which are finding themselves on the defensive end of a great many attacks testing the security of their aliases and operational security lately. Over the past few weeks three of the longest running and most venerated Russian-language online forums serving thousands of experienced cybercriminals have been hacked.
In two of the intrusions (against the Russian hacking forums “Mazafaka” and “Verified”) — the attackers made off with the forums’ user databases, including email and Internet addresses and hashed passwords.
“Members of all three forums are worried the incidents could serve as a virtual Rosetta Stone for connecting the real-life identities of the same users across multiple crime forums,” a recent story here explained.
An exposure of 15 years worth of user data from a forum like Mazafaka is a big risk for registrants because investigators often can use common registration details to connect specific individuals who might have used multiple hacker handles over the years.
Many of the domains from the email addresses listed in the Maza dump date to the early 2000s, back when budding cybercriminals typically took fewer precautions to obfuscate or separate the myriad connections to their real-life identities online.
The biggest potential gold mine for de-anonymizing Maza members is the leak of user numbers for ICQ, an instant messaging service formerly owned by AOL that was widely used by cybercrime forum members up until around 2010. That’s about when AOL sold the platform in 2010 to Russian investor DST for $187.5 million.
Back then, people often associated their ICQ numbers to different interests, pursuits and commerce tied to their real life identities. In many cases, these associations are on public, Russian language forums, such as discussion sites on topics like cars, music or programming.
In a common inadvertent exposure, a cybercriminal happens to make an innocuous post 15 years ago to a now-defunct Russian-language automobile forum.
That post, preserved in perpetuity by sites like archive.org, includes an ICQ number and says there’s a guy named Sergey in Vladivostok who’s selling his car. And the profile link on the auto forum leads to another now-defunct but still-archived personal site for Sergey.
Interestingly, services like WeLeakInfo can just as easily be used against cybercriminals as by them. For example, it’s likely that the database for the automobile forum where Sergey posted got compromised at some point and is for sale on sites like WeLeakInfo (there are active competitors).
Ditto for any other forum where Sergey used the same email address or password. When researchers start finding password re-use across multiple email addresses that all follow a pattern, it becomes much easier to tie Sergey from Vladivostok to his cybercriminal and real-life identities.






Pizda Krebs
Sergey? I have a bone to pick with you about this car…
When the Hunters become the Hunted.
Oh, sweet, sweet irony!
lol i am so screwed i was literally 12 when i made a wli account… any advice brian??
Don’t drop the soap man.
That’s all we can say.
cringe
LOL. You were 12. You’d probably only get charged as an ‘add on’ charge down the road, IF you commit more crimes. Keep your nose clean, and I’m pretty sure you’ll be fine.
If not, don’t drop that thing that other person said 🙂
So the hackers are getting hacked? LMAO!!
i got raided for being in this dumb db like a few months ago
nca kinda bad doe 🙂
Why would the “FBI be the one to “let” the domain expire”?
Why would buying an expired domain, instantly give you access to everyone’s name/password that made a purchase on that site, years before? You are only buying the DOMAIN name… not there past database contents?
Why do krebonsecurity articles always cause far more unanswered questions that make 0 sense?
Did you not read the article?
Once a domain expires, you are able to preform password resets on accounts that used the domain for their emails, and weleakinfo used stripe for their payment processing, which included all the details
for example, say you owned coolwebsite.com, and used hello@coolwebsite.com as an email for your accounts, but you let this domain expire and somebody else buys it, now that person is able to impersonate you and use your email address as you. They could reset your passwords, etc.
The FBI “let” it expire, by not paying to renew the domain.
Ever hit “forgot password” on a website? They send you an email. If your email provider let their domain expire, and I bought that domain, I could reset your passwords, because I would own every email address linked to that domain.
If your family bought a domain name, and set up mom@ourdomain.com, dad@ourdomain.com, kid1@ourdomain.com, kid2@ourdomain.com. Then you all used those email addresses to log into websites… With me being the new owner of ourdomain.com, I’d own all those email addresses. In fact, I’d own any and every email address tied to that domain. Please send me a password reset link 🙂
It wasn’t everyone on the site who had their info taken. They used Stripe.com to process debit/credit cards. They just reset the password for the stripe account, by clicking forgot password. Stripe emailed them the password reset link, and boom, they were into the account on Stripe, which got them the history of all the transactions.
The Paypal account was not compromised, now were Bitcoin transactions. This is only the Stripe.com data.
As you learn more about IT, you’ll better understand his articles.
Expecting anything but epic and utter failure from programmers is just down right comical…. failure is their way.
Insecure junk code is the default.
The postcode has been left exposed, that tells you the street and is precise to within a few door numbers of the address in question. If you blur the street name, there is good reason to blur the postcode (zip) too.
Something odd happened with the email notification for this article and the sms one. They both appeared in my inbox a few hours ago on the 18th. One shows up as arriving the 15th and the other the 16th, behind other emails that arrived after those dates.
Another message on fiserv has just turned up and appears as though it arrived the 17th.
This basically comes down to this: Nothing humans do is 100% perfect. They will and do make mistakes at times.
And when cyber-criminals do make mistakes someone else can use these mistakes to their advantage.
good to see this
Who is this and why are you
Help