Many online services allow users to reset their passwords by clicking a link sent via SMS, and this unfortunately widespread practice has turned mobile phone numbers into de facto identity documents. Which means losing control over one thanks to a divorce, job termination or financial crisis can be devastating.
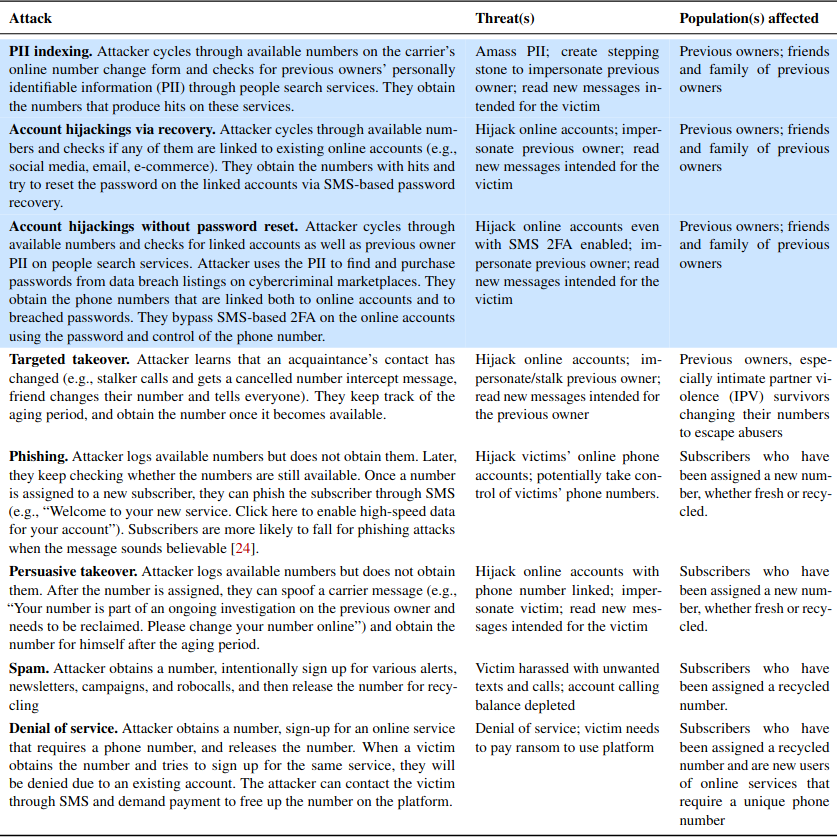
Even so, plenty of people willingly abandon a mobile number without considering the potential fallout to their digital identities when those digits invariably get reassigned to someone else. New research shows how fraudsters can abuse wireless provider websites to identify available, recycled mobile numbers that allow password resets at a range of email providers and financial services online.

Researchers in the computer science department at Princeton University say they sampled 259 phone numbers at two major wireless carriers, and found 171 of them were tied to existing accounts at popular websites, potentially allowing those accounts to be hijacked.
The Princeton team further found 100 of those 259 numbers were linked to leaked login credentials on the web, which could enable account hijackings that defeat SMS-based multi-factor authentication.
“Our key finding is that attackers can feasibly leverage number recycling to target previous owners and their accounts,” the researchers wrote. “The moderate to high hit rates of our testing methods indicate that most recycled numbers are vulnerable to these attacks. Furthermore, by focusing on blocks of Likely recycled numbers, an attacker can easily discover available recycled numbers, each of which then becomes a potential target.”
The researchers located newly-recycled mobile numbers by browsing numbers made available to customers interested in signing up for a prepaid account at T-Mobile or Verizon (apparently AT&T doesn’t provide a similar interface). They said they were able to identify and ignore large blocks of new, unused numbers, as these blocks tend to be made available consecutively — much like newly printed money is consecutively numbered in stacks.
The Princeton team has a number of recommendations for T-Mobile and Verizon, noting that both carriers allow unlimited inquiries on their prepaid customer platforms online — meaning there is nothing to stop attackers from automating this type of number reconnaissance.
“On postpaid interfaces, Verizon already has safeguards and T-Mobile does not even support changing numbers online,” the researchers wrote. “However, the number pool is shared between postpaid and prepaid, rendering all subscribers vulnerable to attacks.”
They also recommend the carriers teach their support employees to remind customers about the risks of relinquishing a mobile number without first disconnecting it from other identities and sites online, advice they generally did not find was offered when interacting with customer support regarding number changes.
In addition, the carriers could offer their own “number parking” service for customers who know they will not require phone service for an extended period of time, or for those who just aren’t sure what they want to do with a number. Such services are already offered by companies like NumberBarn and Park My Phone, and they generally cost between $2-5 per month.
The Princeton study recommends consumers who are considering a number change instead either store the digits at an existing number parking service, or “port” the number to something like Google Voice. For a one-time $20 fee, Google Voice will let you port the number, and then you can continue to receive texts and calls to that number via Google Voice, or you can forward them to another number.
Porting seems like less of a hassle and potentially safer considering the average user has something like 150 accounts online, and a significant number of those accounts are going to be tied to one’s mobile number.
While you’re at it, consider removing your phone number as a primary or secondary authentication mechanism wherever possible. Many online services require you to provide a phone number upon registering an account, but in many cases that number can be removed from your profile afterwards.
It’s also important for people to use something other than text messages for two-factor authentication on their email accounts when stronger authentication options are available. Consider instead using a mobile app like Authy, Duo, or Google Authenticator to generate the one-time code. Or better yet, a physical security key if that’s an option.
The full Princeton study is available here (PDF).




Unfortunately, logins for many websites, including some financial institutions, still don’t allow a second factor other than a mobile phone SMS.
Maybe it will take a breach at some big bank with loss of depositors’ money. Has there not been any such yet?
Would that it were many. For the websites I deal with, it’s most.
Would be useful for Password programs to provide ability to see at glance the sites that are storing your cell, especially when its used for 2FV.
I know I can create a separate entry in each record and search for records based on that content but I’ll have to come up with something unique, be consistent with the content but it still won’t be as easy as a pre-made filter.
Basically wireless carriers for security reasons, should take old and unused numbers by customers out service permanently to avoid these situations.
Sunshine State, you are short a clue. Any clue. If Bellcore (that’s “they”) took all old numbers out of service, you’re looking at a 15 or 20-digit phone #.
It *used* to be required that a number not be recycled for a minimum of 18 months (I’ve worked for telecoms), but that went away – not sure what it is, now.
Then there’s the other issue: why would *anyone* not want to keep their number? Are they trying to get away from everyone they know, including their parents?
I, and my kids, have had our same phone #s for 15 years and more. Our friends and family know out numbers. Just moving to a new number, also, will *not* cut the robocalls.
So basically you are saying for example, that big companies like Google recycle gmail(.)com email addresses after 18 months of non use, because then it would make it harder to recreate new ones for users That’s the analogy that you are giving me here . Abuse is abuse, and you have to make radical changes to stop it
You can’t compare email addresses, as they are variable length and characters as well as digits, and therefore significantly more available addresses, no need to recycle.
The reason you need to recycle phone numbers is because there is a limited supply!
@SSS
It’s a math problem. There are are an infinite number of phone numbers available given the current numbering system, at least for North America. More area codes could be created to help with that issue, but that still would not be enough with all the phone numbers used in one’s lifetime. Remember pagers, landline modems and fax machines? Should all those numbers have been removed already?
Many phone numbers are reserved for special use, so are not available to the public.
Read more here: https://en.wikipedia.org/wiki/North_American_Numbering_Plan
The total number of possible email addresses is only limited by what can be transmitted over the internet.
https://stackoverflow.com/questions/386294/what-is-the-maximum-length-of-a-valid-email-address
Should have read “are *not* an infinite number….”
I have a comment on this because I change my number often and port my numbers to voip solutions for a decommission period before releasing them. Its also helpful for accessing forgotten accounts.
We really have to stop using cell phones for everything. I shouldn’t need my cell phone to read a menu at a resturaunt, park my car in the city or authenticate.
Amen Dylan! Do not have a “smart phone”, hope never to have one. The idea of having your life on a device such as that should horrify people.
@mark
Victims of domestic abuse want to change their numbers.
Also, my sister changes her number often, but I think that is more to dodge creditors.
Brian: I looked at Authy and Duo and even after that have no idea how they work, where they work (do they work on a PC?), and on what sites they work (do the sites need to have Authy internally, or is all of this external?). Is explaining this something you would consider writing about.
Wikipedia describes Google Authenticator, and probably other solutions too: https://en.wikipedia.org/wiki/Google_Authenticator
Reply to jon bondy:
I use Authy for my Windows laptop and Android phone:
1. Install Authy on phone. Set up account as prompted.
2. Install Authy on your PC or laptop.
3. Opt in for 2FA via Authy at your particular websites and apps – one after another. There’s usually a QR code which you scan with your phone (or enter whatever code onto your PC/laptop). Synced and done.
Now, when signing in to a particular 2FA website, you open up Authy on your PC/laptop/phone… scroll to the name of that website, copy the 6-digit code (changes every 30 seconds) and paste onto the website page. With your login ID, password, and now the 6-digit code pasted, you should be able to fully log in. Some websites allow your PC/laptop/phone to “remember” so you won’t need to 2FA authenticate for future visits (or until you delete cookies).
Thanks for sharing.I found a lot of interesting information here.
My credit union uses Authy. So I have it on my PC. It seems to work ok. I just can’t copy/paste the code into the website. I have to manually type it in (but that may be the website).
My work uses Duo. What I like about it is that I can have a fob instead of using my phone.
I avoid using phone based authentication whenever possible because I consider it insecure. But it is getting harder as sites are using it more.
1. You can install Authy on Windows, macOS, Linux, Android, and iOS — and you can share a common linked account across multiple devices. n.b. there is some risk in this, as it means whichever of these devices is easiest to attack compromises all linked accounts (this includes a device being lost/stolen). OTOH, if any of these devices is lost/stolen/compromised, you need to deal w/ it.
2. 2FA can be used in many places — https://2fa.directory/
Recycling is an old trick in scamer industry – in general for years.
Lets say a new movie comes out with a wikipedia entry and a link to the movie url is: NewMovie-TheFilm.com After 3months the link is down because no need anymore for commercials, u will immediately find a chinese or indo porn or whatever scam site behind this dns because links from wikipedia makes u important in google.
I use my Google Voice number for apps/website authentication purpose. Whenever there’s a website authentication request, my phone, computer, devices will all receive a text. It’s also trivially easy to turn on or off or even set “outside hours” for any and all device notifications on my Google Account webpage. No need to be ‘forever’ tied to a cell phone number.
BONUS: There’s ZERO human help for anything whatsoever with a free Google Account. So no worries about hackers calling up a Google rep and impersonating as you to hijack your 2FA protection. Who knew that non-existent service can be a ‘feature’ too?
That’s a good idea, ReadandShare, except that many SMS based two factor authentication schemes do not support VOIP numbers (including Google Voice).
It’s dumbfounding how many high value sites either do not implement any 2FA, only provide SMS non-VOIP based 2FA, or bizarrelly — provide a whole slew of 2FA but don’t let you ratchet down to the most secure. The latter option is almost the worst of the bunch — why enable ten different ways to verify your account?
I also use my Google voice number for my second factor authentication instead of my regular mobile phone number. I’ve used it on multiple sites, and so far haven’t run into any that don’t let me use that number. At some point I’m sure I’ll come across one but not yet.
My bank and broker websites do not provide any user options for 2FA. Instead, they have “automatic” 2FA. Whenever I access my bank or broker websites from an “unknown” computer, they will automatically send a verification email or text to me. I wish I could set up with Authy instead, but it’s whichever email / phone info I provided in my ‘contact preferences’.
For these companies that insist on having your phone number, update the number on their website.
I once got assigned a phone number which had previously belonged to a drug dealer, that was interesting.
An interesting article but I don’t believe for an instant that “the average user has something like 150 accounts online”. I’d love to see how that nice, big, round number was arrived at 🙂
Well, I am in a bit of a state of shock …
I thought 150 accounts was a bit excessive, so I opened my password manager password vault and counted the entries …
671!
Now not all are online passwords – I keep things like router passwords in my password vault as well as things like my NHS number (so I can complete forms with a right click to access the number) – but I think I have “acquired” at least 500 online accounts over my digital life (say from 1996 – 25 years: new meaning to “Silver surfer”?).
Clearly I have a lot of house keeping to do as some of the accounts will be redundant (the service may not even exist any longer – which will make closing the accounts an interesting experience!).
These accounts can build up – particularly if you try to keep to keep different aspects of your life separate and do not just “sign on with facebook”.
Why don’t you believe that? because you don’t? or just don’t realize how many services have online accounts now?
Do you even have an inventory of all your accounts?
The avg user would have the following “online account”
email
social media
banking
medical services
utilities
home services like security, contractors
schools
travel sites
retailers for shopping and rewards
restaurant and hotel rewards
that’s a few examples, you likely have over 100 online accounts and don’t even realize it
news and magazines
hobby forums
Just counted 98 entries in my password manager. But I also have ZERO social media accounts.
Nice heads up Brian. Mobile phone service providers are excessively keen to take back control of numbers so ensure that your spare phone is used to make a call at least once a month.
Modern life is like being prey on African savannah. Lions and ihyenas, i.e. businesses, are always prowling in search of ‘opportunities’.
@samak – not sure about you, but I would guess for the average middle-aged, employed central European Joe:
At work before single-sign on was widely deployed, I believe I had up to 20 online identities only within my company. Now we are down to 2 or 3.
Then work related accounts at third parties – probably 5-10 or so
bank, investment company (2-5)
telecom for landline and mobile (2 or more if you also manage for your household members)
personal email accounts (2-5)
airlines, frequent flyer programs, multi-company rebate programs (5-25)
entertainment, music and video streaming etc (3-5)
then nearly every bleeding webshop that you ever did business with (50+??)
…and I am sure I have forgotten a field or two.
This would bring the range to between 70 and 125. So 150 in the article sounds high, but not completely off. I guess this scales a lot by geography and demographic. 85+% of the world population probably have exactly zero accounts.
Verizon recycles landline numbers as quickly.
Apparently, ATT also reassigned landlines within a few days. I was once told by ATT that they completely dropped the waiting period before reassigning numbers.
When I got Verizon service I was assigned a number that was apparently in use by someone else just a day earlier. I keep getting calls from people, including collection bureaus, demanding payment from the previous holder.
Imagine the havoc one could cause for the previous holder. No one vets the number to ensure it is still assigned to anyone any more. No one at all.
My preferred way to park a phone number is to move it to a cheap VoIP provider. The one I use is $1.95/mo plus 1.5c/min for any call I answer, which is basically none.
Thanks for sharing post on this topic. Yes,I am agerly agrre with the post that people do not have sometimes idea for what they use their mon\bile numbers and when they give their mobile number for authantication purpose OTP,they don’t even know where their number will be used. It is neccesity of the time to aware people about their privacy related to mobile number and email.
aessuccess
Here in México, Telcel recycles your phone number after a few weeks of disuse.
My partner just received a text message, to a phone number she’s had for >20 years, in a state where she hasn’t lived for about 9 years, about a license plate she hasn’t had for 9+ years. Sht’s out there in the wild!
privacy nowadays is a general problem for a common man.They don’t even know where their data is stored and howcompany is using it.People read privacy policy often.
idp.generic