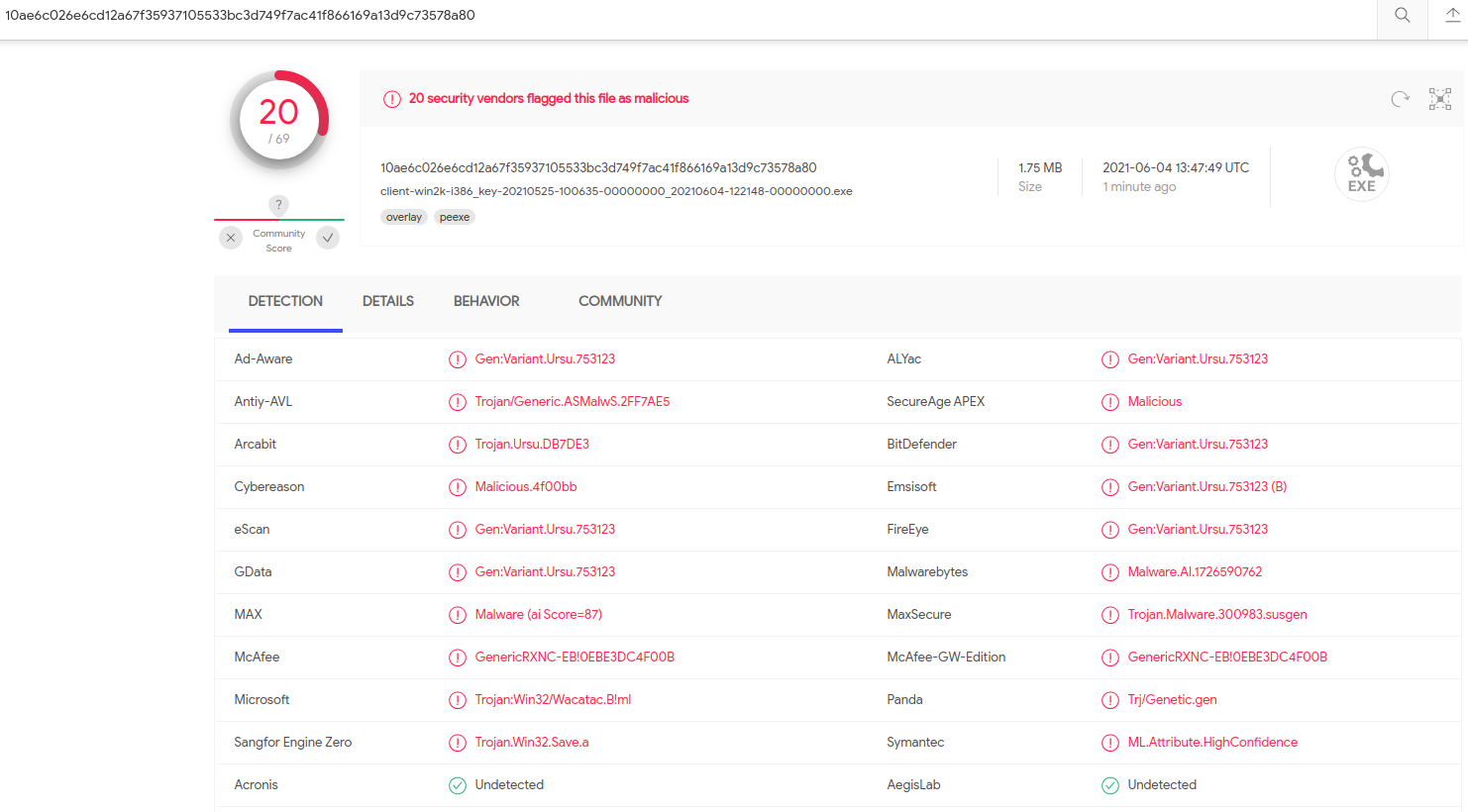
KrebsOnSecurity recently had occasion to contact the Russian Federal Security Service (FSB), the Russian equivalent of the U.S. Federal Bureau of Investigation (FBI). In the process of doing so, I encountered a small snag: The FSB’s website said in order to communicate with them securely, I needed to download and install an encryption and virtual private networking (VPN) appliance that is flagged by at least 20 antivirus products as malware.

The FSB headquarters at Lubyanka Square, Moscow. Image: Wikipedia.
The reason I contacted the FSB — one of the successor agencies to the Russian KGB — ironically enough had to do with security concerns raised by an infamous Russian hacker about the FSB’s own preferred method of being contacted.
KrebsOnSecurity was seeking comment from the FSB about a blog post published by Vladislav “BadB” Horohorin, a former international stolen credit card trafficker who served seven years in U.S. federal prison for his role in the theft of $9 million from RBS WorldPay in 2009. Horohorin, a citizen of Russia, Israel and Ukraine, is now back where he grew up in Ukraine, running a cybersecurity consulting business.
Horohorin’s BadB carding store, badb[.]biz, circa 2007. Image: Archive.org.
Visit the FSB’s website and you might notice its web address starts with http:// instead of https://, meaning the site is not using an encryption certificate. In practical terms, any information shared between the visitor and the website is sent in plain text and will be visible to anyone who has access to that traffic.
This appears to be the case regardless of which Russian government site you visit. According to Russian search giant Yandex, the laws of the Russian Federation demand that encrypted connections be installed according to the Russian GOST cryptographic algorithm.
That means those who have a reason to send encrypted communications to a Russian government organization — including ordinary things like making a payment for a government license or fine, or filing legal documents — need to first install CryptoPro, a Windows-only application that loads the GOST encryption libraries on a user’s computer.
But if you want to talk directly to the FSB over an encrypted connection, you can just install their own client, which bundles the CryptoPro code. Visit the FSB’s site and select the option to “transfer meaningful information to operational units,” and you’ll see a prompt to install a “random number generation” application that is needed before a specific contact form on the FSB’s website will load properly.
Mind you, I’m not suggesting anyone go do that: Horohorin pointed out that this random number generator was flagged by 20 different antivirus and security products as malicious.
“Think well before contacting the FSB for any questions or dealing with them, and if you nevertheless decide to do this, it is better to use a virtual machine,” Horohorin wrote. “And a spacesuit. And, preferably, while in another country.”
It’s probably worth mentioning that the FSB is the same agency that’s been sanctioned for malicious cyber activity by the U.S. government on multiple occasions over the past five years. According to the most recent sanctions by the U.S. Treasury Department, the FSB is known for recruiting criminal hackers from underground forums and offering them legal cover for their actions.
“To bolster its malicious cyber operations, the FSB cultivates and co-opts criminal hackers, including the previously designated Evil Corp., enabling them to engage in disruptive ransomware attacks and phishing campaigns,” reads a Treasury assessment from April 2021.
While Horohorin seems convinced the FSB is disseminating malware, it is not unusual for a large number of security tools used by VirusTotal or other similar malware “sandbox” services to incorrectly flag safe files as bad or suspicious — an all-too-common condition known as a “false positive.”
Late last year I warned my followers on Twitter to put off installing updates for their Dell products until the company could explain why a bunch of its software drivers were being detected as malware by two dozen antivirus tools. Those all turned out to be false positives.
To really figure out what this FSB software was doing, I turned to Lance James, the founder of Unit221B, a New York City based cybersecurity firm. James said each download request generates a new executable program. That is because the uniqueness of the file itself is part of what makes the one-to-one encrypted connection possible.
“Essentially it is like a temporary, one-time-use VPN, using a separate key for each download” James said. “The executable is the handshake with you to exchange keys, as it stores the key for that session in the exe. It’s a terrible approach. But it’s what it is.”
James said the FSB’s program does not appear to be malware, at least in terms of the actions it takes on a user’s computer.
“There’s no sign of actual trojan activity here except the fact it self deletes,” James said. “It uses GOST encryption, and [the antivirus products] may be thinking that those properties look like ransomware.”
James says he suspects the antivirus false-positives were triggered by certain behaviors which could be construed as malware-like. The screenshot below — from VirusTotal — says some of the file’s contents align with detection rules made to find instances of ransomware.
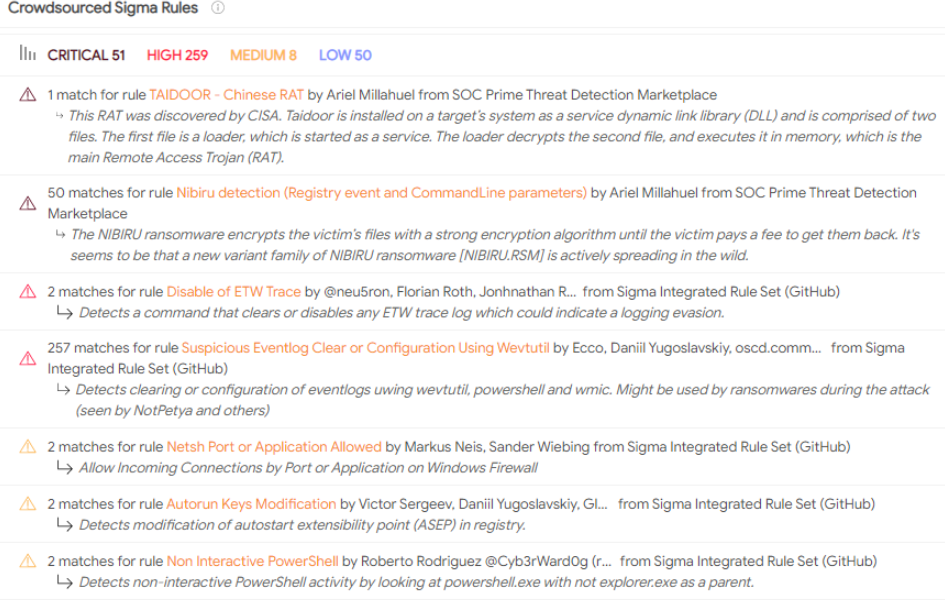
Some of the malware detection rules triggered by the FSB’s software. Source: VirusTotal.
Other detection rules tripped by this file include program routines that erase event logs from the user’s system — a behavior often seen in malware that is trying to hide its tracks.
On a hunch that just including the GOST encryption routine in a test program might be enough to trigger false positives in VirusTotal, James wrote and compiled a short program in C++ that invoked the GOST cipher but otherwise had no networking components. He then uploaded the file for scanning at VirusTotal.
Even though James’ test program did nothing untoward or malicious, it was flagged by six antivirus engines as potentially hostile. Symantec’s machine learning engine seemed particularly certain that James’ file might be bad, awarding it the threat name “ML.Attribute.HighConfidence” — the same designation it assigned to the FSB’s program.
KrebsOnSecurity installed the FSB’s software on a test computer using a separate VPN, and straight away it connected to an Internet address currently assigned to the FSB (213.24.76.xxx).
The program prompted me to click on various parts of the screen to generate randomness for an encryption key, and when that was done it left a small window which explained in Russian that the connection was established and that I should visit a specific link on the FSB’s site.
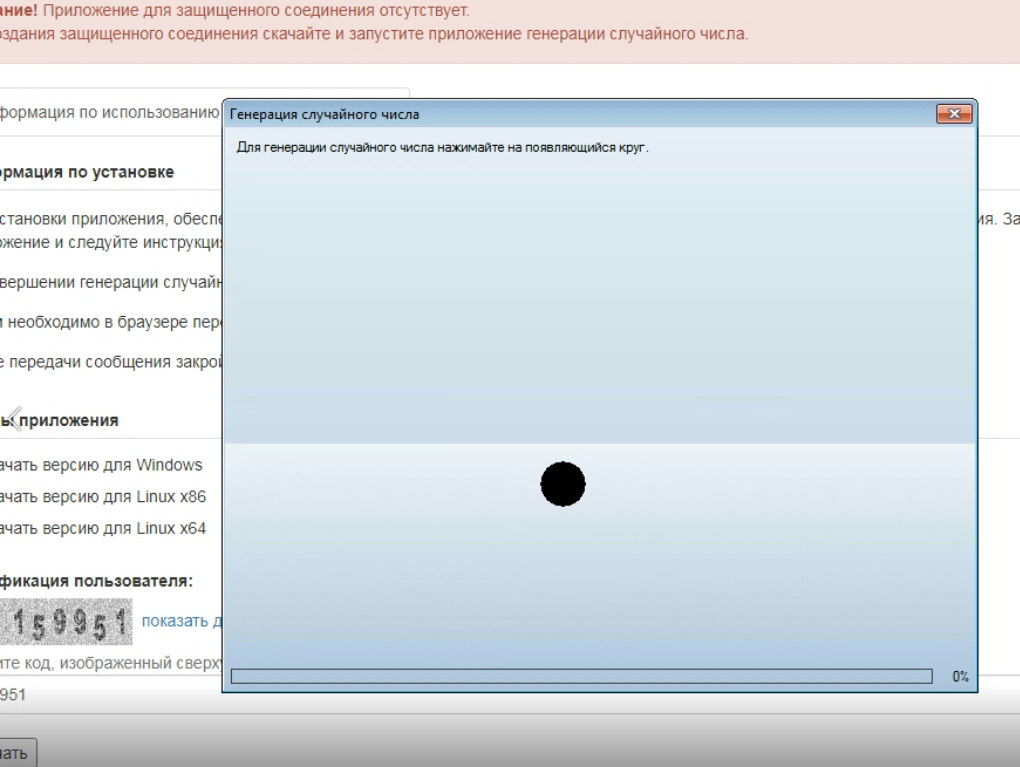
The FSB’s random number generator in action.
Doing so opened up a page where I could leave a message for the FSB. I asked them if they had any response to their program being broadly flagged as malware.
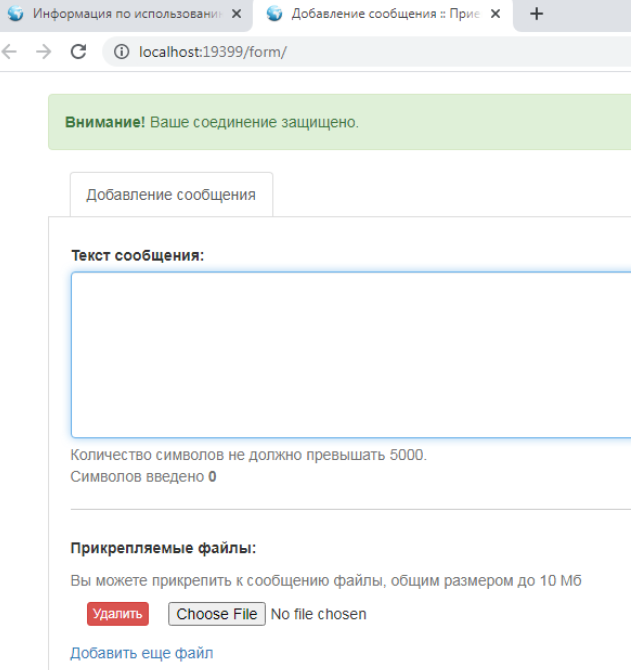
The contact form that ultimately appeared after installing the FSB’s software and clicking a specific link at fsb[.]ru.
After all the effort, I’m disappointed to report that I have not yet received a reply. Nor did I hear back from S-Terra CSP, the company that makes the VPN software offered by the FSB.
James said that given their position, he could see why many antivirus products might think it’s malware.
“Since they won’t use our crypto and we won’t use theirs,” James said. “It’s a great explanation on political weirdness with crypto.”
Still, James said, a number of things just don’t make sense about the way the FSB has chosen to deploy its one-time VPN software.
“The way they have set this up to suddenly trust a dynamically changing exe is still very concerning. Also, why would you send me a 256 random number generator seed in an exe when the computer has a perfectly valid and tested random number generator built in? You’re sending an exe to me with a key you decide over a non-secure environment. Why the fuck if you’re a top intelligence agency would you do that?”
Why indeed. I wonder how many people would share information about federal crimes with the FBI if the agency required everyone to install an executable file first — to say nothing of one that looks a lot like ransomware to antivirus firms?
After doing this research, I learned the FSB recently launched a website that is only reachable via Tor, software that protects users’ anonymity by bouncing their traffic between different servers and encrypting the traffic at every step of the way. Unlike the FSB’s clear web site, the agency’s Tor site does not ask visitors to download some dodgy software before contacting them.
“The application is running for a limited time to ensure your safety,” the instructions for the FSB’s random number generator assure, with just a gentle nudge of urgency. “Do not forget to close the application when finished.”
Yes, don’t forget that. Also, do not forget to incinerate your computer when finished.




Think you tagged C# when you meant C++
WordPress must have done that. I definitely tagged C++.
Yep. Just tested it on a draft. If you add “C++” as a tag in WordPress, it shows up as it should in the WordPress editor, but then when published it converts it to “C#”. Not sure if that’s a bug or what, but kind of seems like it. Maybe it is some script filtering or something. But thanks for pointing that out.
If the FSB is like this……well….I can’t imagine what goes on with the FBI either…..
I wonder this all the time, as we know, the FSB will not announce they’re hacked.
“I wonder how many people would share information about federal crimes with the FBI if the agency required everyone to install an executable file first …” This is a Social Engineering feature not a bug. It pops up in many registry contexts. First, while (big bad) Law Enforcement can collect evidence in plain sight they can come back for an incidental explanation and further questions. The FBI “Tip Page” asks tipsters for reference factoids which can be integrated and investigated at their leisure. Second, nobody in tech ever went broke jumping to conclusions. That neither the FSB nor the FBI would take kindly to manipulation is a finding not a conclusion, but it was always a choice.
Because they are a government agency and are required to meet specific government encryption standards which aren’t supported in a random browser, so the lowest bidder who made the site shrugged and did the sloppiest job they could get away with, not giving a fuck about whether actual whistleblowers will trust this? Sometimes a black cat is just a black cat. Sometimes bureaucracy takes over malicious machinations of the godless nefarious KGB successor.
>why would you send me a 256 random number generator seed in an exe when the computer has a perfectly valid and tested random number generator built in?
Well, for starters, your random number source is likely made by Intel, AMD, Microsoft, or any other company which can’t be held accountable or be relied upon if a vulnerability is found. It’s a very obvious supply chain security issue.
Alternatively it could be a channel to selectively target individuals. Nobody has demonstrated that the exe files are always benign non-trojans, just that the one (or few) examined here didn’t have those features in those few instances. What if a known-to-FSB asset/suspect/interest from a pre-designated IP/machine/phone/fingerprint went to download the exe, would they get the same package or not? OLYMPUSFIRE / FOXACID type of selection perhaps for the extra sauce.
I’m just speculating there’s some additional unconsidered benefit to doing it this way from their perspective.
Otherwise why would they bother going out of their way.
More likely they don’t know jack about what is or isn’t secure. I wouldn’t put too much faith in their ability to protect their networks.
Thank you, Brian — as always, great reporting!
My thoughts:
(1) “Why the fuck if you’re a top intelligence agency would you do that?” — Maybe they aren’t ‘a top intelligence agency’ any more? Cronyism and nepotism hurt organisations in the long run. And it’s been already over 20 years since their former head Putin took the helm of the whole country.
(2) “the FSB recently launched a website that is only reachable via Tor” — Oh, the irony, i.e. the FSB using something originally promoted by their nemesis and arch-enemy NSA in in support of human rights and against authoritarian governments!
(3) On top of (2), the FSB — knowingly or unknowingly — contravenes against Russian law by not using GOST-compliant encryption for their TOR site. Who would have thought that a government agency would act against the law? Colour me surprised. 😉
1. vast majority of Russian people don’t care about changing exe. In Russia you can download iso image or buy dvd easily with all sort of programs – Like Photoshop, Microsoft Office, Windows OS, etc along with “crackers, key generators. etc”, ignoring screams from cracked antivirus when trying to install it.
2. That is rather a concern. I would think there are plenty of Tor nodes controlled by FSB, so they have visibility to traffic.
3. I would say FSB is not government agency, it is rather government itself. Russian government, is in fact agency of FSB. So, whatever FSB decides to do – they just go for it, and sometimes if they find it suitable, they may formalize things as a law through their peers in parliament.
I wonder what would happen if you were using a real machine and or in Russia. I work for a company that has to use that crypto to generate documents for the Russian government. No sooner do we put the crypto on the machines then our AV flags something trying to attach to about every process running on the machine.
So I whole heartedly agree that you should use a completely separate system and a space suit if you need to use this stuff. It looks to me like the hackers are testing technics using their citizens as beta testers. Can we be blamed for not using their crypto?
nsa regularly asks companies to compromise their own products in subtle ways such as making ms rng be slightly less random or leak keys somehow. russians arent idiots. if fsb is using its own rng it has a reason.
nsa broke https ssl and aes in early 2000s ( and if they didnt break it via sheer force maths then they just went around it by sitting on the pipes of att yahoo msn goog et al)
Iron Felix is alive, well and as efficient as ever!! Dzerzhinsky may be absent from the square front of the building, but no matter whether working for Putin, Lenin or Stalin, the activities at the Lubyanka remain the same.
Brian, did UNIT221B or anyone fully Reverse Engineer the downloaded exe? Since it’s unique for every download, each one will need to be disassembled. It is very likely that there are some checks that happen, that ensure only real targets are downloading the trojanized executables. Maybe by IP, or other fingerprinting. Once the malicious executable is downloaded, it probably does additional checks before it allows the malicious code to run. So your protective actions (VM and/or additional VPN) may have resulted in the defanged/non-malicious exe.
A reverse engineer would have to set up a sandbox that doesn’t look like a sandbox, and looks like they are coming from a target. I would suggest they actually set up a new relay in the Ukraine or even domestic Russia, and modify the TTL too. Then run on bare metal. I would hope UNIT221B would do all that, but if the FSB is being very careful, then it’ll be difficult to get the real malicious file.
It is clever to have a unique exe each time. Very hard for anyone to flag a moving target if based on signature. And if they do flag based on heuristics, it happens too often… effectively devaluing virustotal to the point where people just expect it to be flagged. They could even blame it on politics (oh, western AV engines just don’t trust us).
This sounds like kleptocracy 101.
Corrupt governments frequently allow organized crime direct access to informants. This method of “securing” the FSB messaging seems like a trap for snitches to get them stitches.
If you ever have suspicions about software, create a virtual machine and install it there. If anything goes bad, destroy the VM.
Granted, it’s not 100% proof against something getting out as we have proof of concept code of VMWare hypervisors getting compromised, but it’s pretty darn good.
Hmmm, this may be why no Cloud Data Centers from MSFT/Amazon exist in RU/CN.
They have their own cloud platforms.
Way more than concept code, VM escape bugs are hot right now. VMs are no silver bullet, only defence in depth can save you. In this case, I’d treat the computer I did this with as disposable.
Very interesting read. If I ever have the time and money, I’d love to set up a totally separate system to check out things like this, but sure wouldn’t trust a VM alone to protect me. From what I understand, Russia is run by organized crime, and lots of shady stuff goes on and is just accepted as normal. At least that’s the impression I’ve gotten from someone I know who’s Russian and moved to the US.
I found this quote to be hilarious: “Why the fuck if you’re a top intelligence agency would you do that?” So thanks for the much needed laugh!
I have read a book about how Putin came to power – He’s been in cahoots with organised crime since his days in the St Petersburg KGB…
https://www.amazon.co.uk/Putins-People-Took-Russia-Turned/dp/0007578814/
Posting the obligatory “In Russia VPN uses you…”
But happy to see the apparent lack of tradecraft in this. One would have expected a bit more stealth.
FWIW there are people who believe that random number generation on Intel/Windows is backdoored somehow, so if you’re especially paranoid that might be why you’d use a custom RNG rather than the built in generator. In general the FSB probably doesn’t trust any US-made software/hardware to not be backdoored, so from that perspective their approach makes somewhat more sense.
The problem with antivirus programs is that lots of them use/license a scanning/detection engine/virus signatures from another AV because they do not have the expertise to develop a good antivirus. Bitdefender is used by a lot of them. I noticed that 5 of the engines detected “Razy”, which is what Bitdefender calls the “malware.”
If it is Razy it is malware, no quotes. Bitdefender is actually good AV. Still it’s not immune to false-P’s.
Curious if these measures, a 3rd part RNG, non-standard crypto, are more geared towards allowing their assets in the field to evade US/state actor detection if they need to phone home.
If the Russians don’t trust traditional ssl, maybe they believe that it can be easily decoded.
Incredible !
No one mentioned that all this implies trust in runing a exe that was downloaded from http
It is therefore extremely easy for an FSB adversary or any actor that would be interested in
eavesdropping that sort of messages to on fly replace the exe by a man-in-the-middle attack!
Greetings, Brian. You write:
“This appears to be the case regardless of which Russian government site you visit. According to Russian search giant Yandex, the laws of the Russian Federation demand that encrypted connections be installed according to the Russian GOST cryptographic algorithm.
That means those who have a reason to send encrypted communications to a Russian government organization — including ordinary things like making a payment for a government license or fine, or filing legal documents — need to first install CryptoPro, a Windows-only application that loads the GOST encryption libraries on a user’s computer.”
This is a false statement – you can access web pages, and send encrypted communication, without installing any creepy software packages. The largest Russian website handling government services, gosuslugi.ru, is freely available with any browser and has an RSA TLS-certificate.
Is that a 3rd party?
Gosuslugi.ru? It is not.
meduza.io/en/news/2021/06/04/russian-government-confirms-hacking-of-state-services-accounts-during-ruling-party-primaries
Interestingly enough.
To expand on that, Russian law around computer technology is nuts, Russian law around state security is bonkers, and Russian law about computer security of the state just bears no relationship to reality—except maybe for the tentacle of the government that drafted that particular part.
So websites of Russian government services don’t use GOST crypto, and a lot of document exchange can be accomplished without ever touching it… Except for things that would normally require your physical signature like tax returns, where you can either ferry the signed slip from the web service to the requisite office, or use the homegrown GOST-based PKI. The latter is a minefield of cumbersome incompatibility like all government PKIs and is expensive to boot, so individuals normally don’t bother with it.
Is that what the law requires? Standard TLS suites for getting your medical test results, but GOST for signatures? But somehow the FSB is special? No idea, wouldn’t be surprised either way. Russian laws are the epitome of arbitrary enforcement, there’s even a saying about that (roughly, “the strictness of Russian law is only counterbalanced by its optional nature”).
I wonder if Windows Sandbox would be used for such installation because it deletes the program when exiting out of it.
And totally in character to want “security” for people who are only contacting FSB to ask a question which they intend to publish to the world along with any answer.
No, you don’t have to install anything GOST to pay fines and stuff like that. You just use your browser to go to sites like gosuslugi.ru (in my browser, it’s ye olde TLS 1.2, RSA, and AES_256_CBC with HMAC-SHA1 and a cert issued by Sectigo) or mos.ru (a better TLS 1.2, ECDHE_RSA with P-256, and AES_128_GCM, GlobalSign) and do your business there. No plugins or anything like that required.
If it is Razy it is malware, no quotes. Bitdefender is actually good AV. Still it’s not immune to false-P’s.
I would def be using a ras-pi bought second hand from a swap meet using cash that would then go in the acid bath.