The U.S. Department of Justice (DOJ) last week announced the arrest of a 55-year-old Latvian woman who’s alleged to have worked as a programmer for Trickbot, a malware-as-a-service platform responsible for infecting millions of computers and seeding many of those systems with ransomware.
Just how did a self-employed web site designer and mother of two come to work for one of the world’s most rapacious cybercriminal groups and then leave such an obvious trail of clues indicating her involvement with the gang? This post explores answers to those questions, as well as some of the ways Trickbot and other organized cybercrime gangs gradually recruit, groom and trust new programmers.

Alla Witte’s personal website — allawitte[.]nl — circa October 2018.
The indictment released by the DOJ (PDF) is heavily redacted, and only one of the defendants is named: Alla “Max” Witte, a 55-year-old Latvian national who was arrested Feb. 6 in Miami, Fla.
The DOJ alleges Witte was responsible for “overseeing the creation of code related to the monitoring and tracking of authorized users of the Trickbot malware, the control and deployment of ransomware, obtaining payments from ransomware victims, and developing tools and protocols for the storage of credentials stolen and exfiltrated from victims infected by Trickbot.”
The indictment also says Witte provided code to the Trickbot Group for a web panel used to access victim data stored in a database. According to the government, that database contained a large number of credit card numbers and stolen credentials from the Trickbot botnet, as well as information about infected machines available as bots.
“Witte provided code to this repository that showed an infected computer or ‘bot’ status in different colors based on the colors of a traffic light and allowed other Trickbot Group members to know when their co-conspirators were working on a particular infected machine,” the indictment alleges.
While any law enforcement action against a crime group that has targeted hospitals, schools, public utilities and governments is good news, Witte’s indictment and arrest were probably inevitable: It is hard to think of an accused cybercriminal who has made more stunningly poor and rookie operational security mistakes than this Latvian senior citizen.
For starters, it appears at one point in 2020 Witte actually hosted Trickbot malware on a vanity website registered in her name — allawitte[.]nl.
While it is generally a bad idea for cybercriminals to mix their personal life with work, Witte’s social media accounts mention a close family member (perhaps her son or husband) had the first name “Max,” which allegedly was her hacker handle.
Unlike many accused cybercriminals who hail from Russia or former Soviet countries, Witte did not feel obligated to avoid traveling to areas where she might be within reach of U.S. law enforcement agencies. According to her indictment, Witte was living in the South American nation of Suriname and she was arrested in Miami while flying from Suriname. It is not clear where her intended destination was.
A Google-translated post Witte made to her Vkontakte page, five years before allegedly joining the Trickbot group.
Alex Holden, founder of the cybersecurity intelligence firm Hold Security, said Witte’s greatest lapse in judgment came around Christmas time in 2019, when she infected one of her own computers with the Trickbot malware — allowing it to steal and log her data within the botnet interface.
“On top of the password re-use, the data shows a great insight into her professional and personal Internet usage,” Holden wrote in a blog post on Witte’s arrest.
“Many in the gang not only knew her gender but her name too,” Holden wrote. “Several group members had AllaWitte folders with data. They refer to Alla almost like they would address their mothers.”
So how did this hacker mom with apparently zero sense of self-preservation come to work for one of the world’s most predatory cybercriminal gangs?
The government’s indictment dedicates several pages to describing the hiring processes of the Trickbot group, which continuously scoured fee-based Russian and Belarussian-based job websites for resumes of programmers looking for work. Those who responded were asked to create various programs designed to test the applicant’s problem-solving and coding skills.
Here’s a snippet of translated instant message text between two of the unnamed Trickbot defendants, in which they discuss an applicant who understood immediately that he was being hired to help with cybercrime activity.
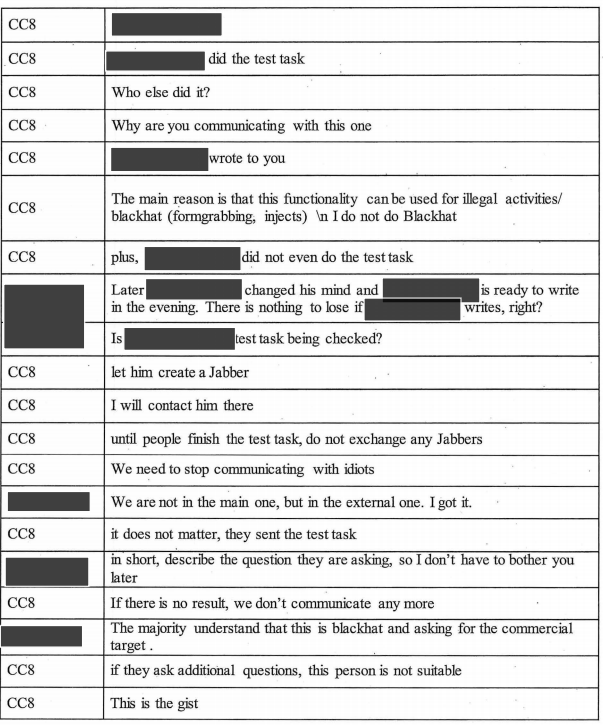
A conversation between two Trickbot group members concerning a potential new hire. Image: DOJ.
The following conversation, on or about June 1, 2016, concerned a potential new Trickbot hire who successfully completed a test task that involved altering a Firefox Web browser.
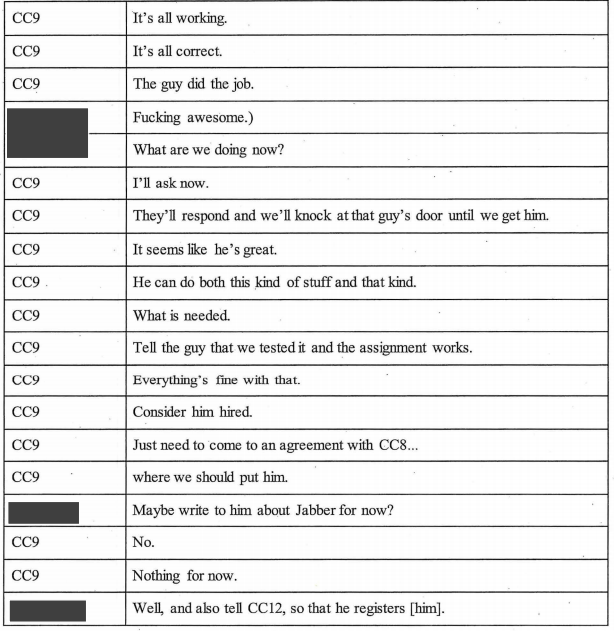
Other conversation snippets in the indictment suggest most new recruits understand that the projects and test tasks they are being asked to tackle are related to cybercrime activity.
“The majority understand that this is blackhat and asking for the commercial target,” wrote the defendant identified only as Co-Conspirator 8 (CC8).
But what about new hires that aren’t hip to exactly how the programs they’re being asked to create get used? Another source in the threat intelligence industry who has had access to the inner workings of Trickbot provided some additional context on how developers are onboarded into the group.
“There’s a two-step hiring process where at first you may not understand who you’re working for,” said the source. “But that timeframe is typically pretty short, like less than a year.”
After that, if the candidate is talented and industrious enough, someone in the Trickbot group will “read in” the new recruit — i.e. explain in plain terms how their work is being used.
“If you’re good, at some point they’re going to read you in and you’ll know, but if you’re not good or you’re not okay with that, they will triage that pretty quickly and your services will no longer be required,” the source said. “But if you make it past that first year, the chances that you still don’t know what you’re doing are very slim.”
According to the DOJ, Witte had access to Trickbot for roughly two years between 2018 and 2020.
Investigators say prior to launching Trickbot, some members of the conspiracy previously were responsible for disseminating Dyre, a particularly stealthy password stealer that looked for passwords used at various banks. The government says Trickbot members — including Witte — routinely used bank account passwords stolen by their malware to drain victim bank accounts and send the money to networks of money mules.
The hiring model adopted by Trickbot allows the gang to recruit a steady stream of talented developers cheaply and covertly. But it also introduces the very real risk that new recruits may offer investigators a way to infiltrate the group’s operations, and possibly even identify co-conspirators.
Ransomware attacks are nearly all perpetrated these days by ransomware affiliate groups which constantly recruit new members to account for attrition, competition from other ransomware groups, and for the odd affiliate who gets busted by law enforcement.
Under the ransomware affiliate model, a cybercriminal can earn up to 85 percent of the total ransom paid by a victim company he or she is responsible for compromising and bringing to the group. But from time to time, poor operational security by an affiliate exposes the gang’s entire operation.
On June 7, the DOJ announced it had clawed back $2.3 million worth of Bitcoin that Colonial Pipeline paid to ransomware extortionists last month. The funds had been sent to DarkSide, a ransomware-as-a-service syndicate that disbanded after a May 14 farewell message to affiliates saying its Internet servers and cryptocurrency stash were seized by unknown law enforcement entities.
“The proceeds of the victim’s ransom payment…had been transferred to a specific address, for which the FBI has the ‘private key,’ or the rough equivalent of a password needed to access assets accessible from the specific Bitcoin address,” the DOJ explained, somewhat cryptically.
Multiple security experts quickly zeroed in on how investigators were able to retrieve the funds, which did not represent the total amount Colonial paid (~$4.4 million): The amount seized was roughly what a top DarkSide affiliate would have earned for scoring the initial malware infection that precipitated the ransomware incident.




This story could be the premise for Breaking Bad II, this time with female leads. Is there a Jessica Pinkman sidekick character?
Or is Breaking Bot a more apt series title.
“I am the one who Port Knocks!!”
Breaking Baud
This proves the effectiveness of indictments against foreign hackers. Even when it seems impossible to enforce, because the indicted persons are in Russia or someplace seemingly untouchable.
There are 7 defendants in this indictment and over a dozen co-conspirators. Most are probably never going to be caught, but SOME may slip up and get caught crossing into a friendly country that is willing to extradite.
Indictments also allow US Law Enforcement to draft a complete picture of a criminal conspiracy.
Another little-known, but major benefit, is the monetary proceeds from a criminal enterprise can be confiscated MUCH easier when there is an indictment. We may only hear about the big arrests, but indictments play a huge role in punishing these criminals, even when they aren’t caught in such spectacular fashion.
Alla Witte, needs to learn better cyber-security practices , with those coding skills
More like OPSec skills
Why do you feel the need to mention she is a mom several times or even once? Do you mention a male subject is a dad or call him “hacker dad” if he has children?
If that hacker dad used his son’s first name as his handle, yeah I’d mention that he was both a hacker dad and that he practiced terrible opsec. And yes, as much as it seems to make a lot of people uncomfortable whenever gender is even mentioned, in this context it also matters because it’s somewhat unusual for a female programmer to be named in a cybercrime indictment.
Give me a break! Stop virtue signaling. It’s common knowledge that this woman doesn’t fit the typical cybercriminal mold and that Brian was simply pointing it out because he found it interesting. Generalizations exist for a reason.
Could you write a post now on how does a really old mom who likes to code get hired for a _legit_ job?
It’s telling that legit tech jobs are harder for females to get.
Age not gender. Men who raised children at home like I did, who are my age, have exactly the same problem as me. The first thing I noticed about her photo was her apparent approximate age. I think jobs for her just dried up along with her skin. Even with her experience, she had to take whatever job would pay the rent. A better title for the OP is “Who else but gangs hire old coders?” When anyone over 55 gets a true entry-level job in tech, it’s front page news.
“In 1965, in Soviet Union city Rostov-on-Don, which is now a part of Russia, Alla Klimova (Алла Климова) was born. Before the fall of the Soviet Union, in 1983 she moved to Riga, Latvia to study Applied Mathematics at the University of Latvia where she remained for a number of years after Latvia became a separate country.
She held several interesting jobs such as a sales manager and a teacher, but her passion throughout her life was programming. In numerous posts on the various Russian-language forums, Alla Klimova admits that her interests in technology started later in life. In 2004, she got a job with a Dutch AOSH EU and in 2007, after getting married, now Alla Witte, moved to Amsterdam.”
Looks like a late start in IT… but always smart and good at math.
The economics of the labor market is complicated and different throughout the world. There are lots of factors, but yeah, age and gender are often discriminated against due to stereotypes.
But I still fall short of sympathy for criminals even if the legitimate jobs are harder to get. It’s no excuse to go blackhat.
I agree about the sympathy for cybercriminals but I can understand the pull to go dark. A friend of mine has three doctorates and was in early with Microsoft. They have lived all over the world as they were formerly in the Navy and the US State Dept as an embassy atache before coming up in the tech sector.
They now live in an RV in an RV park about two hours outside Seattle, Washington. She is trans and never got the nods to go up the management ladder anywhere she worked.
Coaster, I’m afraid to tell you but your statement is wrong. Look at any big tech company and you will find that they are more likely to hire a woman compared to an equally qualified man.
hahah. love it.
All jobs are legitimate. Some are more dangerous than others.
The FBI may have used her private key and taken her Bitcoin that most likely came from the proceeds. Also they may have gotten private key off trickbot servers they got into.
The FBI, private keys, bitcoins… are all part of the Darkside story, not the main story about Trickbot and Alla Witte.
The last 3 paragraphs of this article, are just a reference to a previous story.
Yet another good blog, mate. Beer, sometime.
What was the nature of this “lapse of judgment” that caused her to infect herself with the Trickbot malware? Does this mean she did it deliberately or accidentally? I don’t know which would be worse, but neither looks good for her at all. The article seems perfectly ambiguous on this, as her intent (or lack thereof) can be interpreted variously.
The blog indicates that this was done for testing purposes.
If she’s developing the front end for the ransomware admins, she might want to test load the ransomware on a fresh machine to see if it registers in the system when it calls back to the C2 server.
Obviously her opsec is crap because she didn’t use a disposable VM that is sanitized of all identifying information.
But I think she did intend to install it.
Now, as an older over xx age. I would say her older security was not crap. According to old reports, vm’s were trashed back in Obama’s time by college kids. Yah, ms supposedly fixed it and issued “updates” to fix the problems. She just did not correctly estimate the intensity of the opposition. When some people loose money, they tend to get excited and fly off the handle, others get icey and go to war. Somebody picked on a wrong person, and somebody one step up from mules got caught. Finally.
Interesting article Brian. Keep it up.
I am not convinced she was central to the criminal “hacking/cracking” part. Sounds more like she was the website manager/front woman. That is much more in line with all the errors and bad opsec she displayed, e.g., booking a flight by way of Miami.
In my view, they arrested the receptionist and are pumping this up to make it look like a blow to the malware gang.
I did not get the impression of ‘pumping this up’, by either Krebs or the DOJ.
I don’t think anyone is thinking she wrote the actual ransomware, or that the gang is somehow diminished from losing her.
A bit more than a “receptionist”, but certainly not “central”. She’s a programmer, she wrote code for the front end.
This distinction is not about her importance to the criminal enterprise, but rather about a potential legal defense.
A “receptionist” for a laundromat that is a front for the mafia, MAY try a defense that she didn’t know of any illegal activity. Plausible deniability.
But Alla Witte wrote code that facilitated criminal activity, saw how payments were made, understood the process of ransomware. The point is, she is an minor part, but a complicit part. Thus, named as a defendant in the indictment.
Her arrest can be helpful though. As the prosecution puts the pressure on her, she may reveal information to further expand the indictments. Often times, it’s just additional detail into the workings of the criminal enterprise. Academic information, such as “how criminals recruit” perhaps. But occasionally, even the low level criminals can provide new co-conspirators previously not on the radar.
The mid-level and upper-level criminals are usually safe in their non-extradited countries. But sometimes they get cocky and don’t realize they’ve been compromised, and venture out to be caught.
A low-level catch, like this, can also reveal to investigators, other low-level criminals. Many times, the money mules are caught this way. This can disrupts criminal operations more so than catching a single front end web developer.
Well, they only named the one suspect they managed to arrest. The rest’s names have been obscured in the indictment, probably because the feds don’t want to blow away any chance of apprehending more of this group.
How much was granny paid for this work?
The Bookeeper nailed Capone. She has the internal code and that code is spread through the DNA of the System……it’s like a Fingerprint.
I’m just Excited to SEE the Feds go after REAL criminals vs Political Criminals! This is Nasty stuff and hope she is treated the way the Vietnamese treated our POW’s. Don’t care how old or who she is……she is GUILTY of helping!
Just like the Nazis, just doing their job..right?
I like the Capone comparison. Criminal racketeering and extortion. But like it or not, these are not violent crimes (maybe if they hit a hospital and someone died).
So you hope she’s treated like a POW? And what did the German people think about all their captured POWs? They deserved it for being criminals?
This kind of extremism is why we have a system of laws and due process.
She will be given a trial, and if found guilty, given a sentence that FITS the crime. We should not ask for any less than justice, but we shouldn’t ask for more either. People need to stop with the extremism.
She is not a “senior” citizen. She is just 55 years old.
I agree. However, if at 55 you can still get senior citizen discount at Ross every Tuesday, and if the Denny’s ‘senior menu’ is available to 55’ers too, then calling her a senior citizen is not entirely wrong. It may also depend on the life expectancy of local (e.g., Latvian) population, but I don’t think that was in scope here.
As a 55 year old women who has over 20 years experience in security I do take offense at the senior citizen comment Brian used in this story. I have never received a senior citizen discount, veterans discounts yes, but not senior. I don’t feel like a senior citizen and neither do my friends of similar age.
Jennifer,
Might you really be a “sexy” senior citizen? Or just a beautiful mature woman? The 55 year old of today’s world has much better health and vitality than those of the same age when you were born…
Whatever way you want to be called! Some of us don’t worship at the altar of youth but in the church of life experiences!
“…Latvian senior citizen”? Cheeky, but also shows ageism is still alive and well in tech.
She is NOT latvian!
FFFUUUUU!!!!
“But what about new hires that aren’t hip to exactly how the programs they’re being asked to create get used? Another source in the threat intelligence industry who has had access to the inner workings of Trickbot provided some additional context on how developers are onboarded into the group.”
In logical theory, one could obtain an inexperienced or new coder and hire with alternative motives get said source and modify to more malicious needs.
Honestly man, it seems forgotten a lot of this is basic social manipulation.
If you lack the skill, find someone else who has it.
Case example:
Why name me as the “MAIN DUDE” for Orcus, when I didnt touch even a single aspect of the code or programming to any of it? 😀
Tis a sad state of affairs when we cant even get accurate information I was educate to be an architect towards and its used for such nonsense now a days.
Everything is very open with a clear description of the issues. It was truly informative. Your website is very helpful. Many thanks for sharing!
Great post! From wanting to read just the first paragraph to reading the entire article, time just flew.
But what are best suitable courses or programs that one should take up to be on the right track to a good cyber security career?
Hope I get a reply 🙂
Thank you
– A newly enrolled student at EC Council University