Hard drive giant Western Digital is urging users of its MyBook Live brand of network storage drives to disconnect them from the Internet, warning that malicious hackers are remotely wiping the drives using a critical flaw that can be triggered by anyone who knows the Internet address of an affected device.
One of many similar complaints on Western Digital’s user forum.
Earlier this week, Bleeping Computer and Ars Technica pointed to a heated discussion thread on Western Digital’s user forum where many customers complained of finding their MyBook Live and MyBook Live Duo devices completely wiped of their data.
“Western Digital has determined that some My Book Live and My Book Live Duo devices are being compromised through exploitation of a remote command execution vulnerability,” the company said in a statement June 24. “In some cases, this compromise has led to a factory reset that appears to erase all data on the device. The My Book Live and My Book Live Duo devices received its final firmware update in 2015. We understand that our customers’ data is very important. We are actively investigating the issue and will provide an updated advisory when we have more information.”
Western Digital’s brief advisory includes a link to an entry in the National Vulnerability Database for CVE-2018-18472. The NVD writeup says Western Digital WD My Book Live and WD My Book Live Duo (all versions) have a root Remote Command Execution bug.
“It can be triggered by anyone who knows the IP address of the affected device, as exploited in the wild in June 2021 for factory reset commands,” NVD wrote.
Examine the CVE attached to this flaw and you’ll notice it was issued in 2018. The NVD’s advisory credits VPN reviewer Wizcase.com with reporting the bug to Western Digital three years ago, back in June 2018.
In some ways, it’s remarkable that it took this long for vulnerable MyBook devices to be attacked: The 2018 Wizcase writeup on the flaw includes proof-of-concept code that lets anyone run commands on the devices as the all-powerful “root” user.
Western Digital’s response at the time was that the affected devices were no longer supported and that customers should avoid connecting them to the Internet. That response also suggested this bug has been present in its devices for at least a decade.
“The vulnerability report CVE-2018-18472 affects My Book Live devices originally introduced to the market between 2010 and 2012,” reads a reply from Western Digital that Wizcase posted to its blog. “These products have been discontinued since 2014 and are no longer covered under our device software support lifecycle. We encourage users who wish to continue operating these legacy products to configure their firewall to prevent remote access to these devices, and to take measures to ensure that only trusted devices on the local network have access to the device.”
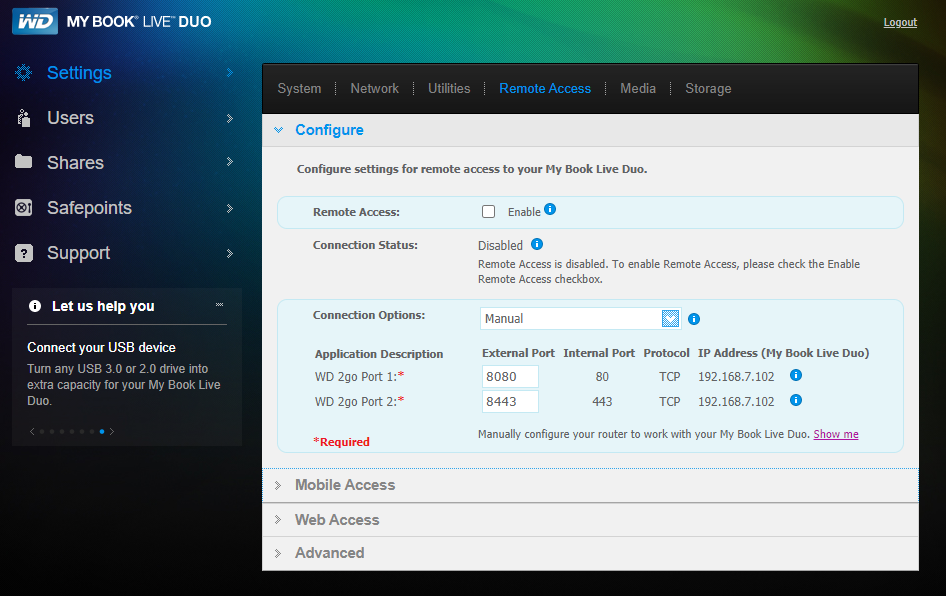
A local administration page for the MyBook Live Duo.
Wizcase said the flaw it found in MyBook devices also may be present in certain models of WD MyCloud network attached storage (NAS) devices, although Western Digital’s advisory makes no mention of its MyCloud line being affected.
The vulnerable MyBook devices are popular among home users and small businesses because they’re relatively feature-rich and inexpensive, and can be upgraded with additional storage quite easily. But these products also make it simple for users to access their files remotely over the Internet using a mobile app.
I’m guessing it is primarily users who’ve configured their MyBooks to be remotely accessible who are experiencing these unfortunate drive wipes. Regardless, it’s probably safest to observe Western Digital’s advice and disconnect any MyBooks you have from ethernet access.
If you’d still like to keep your MyBook connected to your local network (at least until you can find a suitable backup for your backups), please make double sure remote access is not enabled in your device settings (see screenshot above).




Reprehensible behaviour on WD’s part.
“No longer supported” shouldn’t mean “Say goodbye to your data!’
Excellent way to turn customers into ex-customers.
There will always be a limit on how long manufacturers support their products. The more you pay the more support you can (or should) expect, but sooner or later it will end. And these customers can jump to any cheap as chips product from another manufacturer, yet the rules will be the same. Sorry for life being so hard on you.
These were defective from shipment, so ‘never supported’ as opposed to ‘support stopped’.
The exploit was determined post-shipment. Like 4-6 years post shipment.
“Never supported” is quite the exaggeration.
-ASB
Kinda like when I went to the Apple store for a replacement battery for my iPad Mini I. Although they had the battery in-stock and weren’t busy and could otherwise complete the replacement within an hour or two, they had no choice but to refuse because their system told them that the product is no longer supported by Apple….
These drives haven’t been manufactured or sold in seven years. People using them are probably not going to be repeat WD customers, anyway.
No, it’s not reprehensible behavior.
The devices were shipped between 2010 and 2012.
They were no longer under support in 2014.
They received their last security update in 2015.
This vulnerability was discovered in 2018, and at that time, WD issued a stance on its support status and a workaround for customers.
It is now 2021. This is outside the realm of “reprehensible” for the vendor.
If this were 2014, and all they did was shrug, that would be one thing, but this is 7 years after support has ended, and the guidance given 3 years ago hasn’t been followed either.
-ASB
It’s a lack of ethics and bad for the environment to ship a product in 2012 that is no longer supported in 2014. Some may have become brainwashed that new and shiny is always needed and better, but the reality remains that this ridiculous commercialization is unhealthy in every way. A simple storage device should last longer than a few years. Do you seriously think it’s unreasonable for a simple storage device to last 7 years? Just wait until this wanton manipulation is happening with your refrigerator, your stove, your washer & dryer, your dental work, furniture, cars, roof, etc. It’s a lack of ethics. PERIOD.
Not to mention that they knew about this security flaw years ago yet took zero action and did not warn customers. Unethical.
They did warn customers. They posted a blog / security advisory.
They even made recommendations on how to protect the device.
The real problem is the double edge sword of communications/privacy.
How many people sign up for notification emails and stay subscribed for a decade?
For devices that don’t use a cloud service, but are standalone systems… do you subscribe to newsletters for every device in your house? The vast majority of people do not. And they certainly don’t subscribe to news regarding security advisories. There are hundreds every day and a person would have to filter through a lot to just see devices they own.
People don’t want to be bothered, and don’t register their email with the manufacturer of every device they buy. They don’t sign up for product warranties if available, and certainly don’t want companies to keep their email in a database for a decade after they bought a hard drive.
There is plenty of blame on WD here. But the consumers have to pay attention and subscribe to security advisories, especially when they have connected devices that are old and outdated.
Same if you own a car that is out of warranty. The car owner still has to periodically check for recall notices. They should not expect to be notified by magic years after.
Top hints: “default password ‘admin,’ ” followed by “final firmware update in 2015,” and “CVE-2018…” It’s almost as though individuals are copying the cybersecurity practices of corporations!
Another reason to have multiple backups and one of them better be air-gapped.
Yup…then distribute then to different geographic areas, one of which is in a basement at a Zoo behind a door marked “Beware The Leopard.”
I’m not so sure…WD did state that the device should not be connected to the Internet (but probably not in anything sent to people they knew had bought the device). The vulnerability was identified 3 years after they stopped producing it, and at this point it has been 6 years since the last one was produced.
I’m with Brian…the surprising thing is that it took three years after the vulnerability with POC was exploited (at least on any scale).
There will always be a limit on how long manufacturers support their products. The more you pay the more support you can (or should) expect, but sooner or later it will end. And these customers can jump to any cheap as chips product from another manufacturer, yet the rules will be the same. Sorry for life being so hard on you.
Not victim shaming, but what the heck are you doing exposing a personal hard drive to the web in the first place?
Ever since smartphones were invented, the consumer trend has been clear. People do want to access their resources from anywhere.
Whether it’s security cameras, baby monitors, home automation, or storage for files. Internet connectivity and remote access is a feature that people want.
That’s true. I’ve turned these down before because I know better than to put something like that on the internet. But most people aren’t software engineers.
Odds are WD even advertised these devices as being secure enough for the internet. Now WD says the devices are insecure because they are old. The reality is they were never any more secure in the past. WD just got lucky by dropping support before it was their problem.
With respect to JamminJ’s comment, the same goes for smartphones. That is also a personal hard drive, with personal data, and it is insecure. I have disabled all internet and wifi on my smartphone. It is not an inconvenience. I can still call and text from anywhere, and make notes about what to look up when I return to my firewallled burrow.
I’m a tech from way back and I also have external hard drives plugged up to my computer, two of them WD brand, but I never made use of the online cloud service provided by WD. In the world before cloud computing was available, I copied everything to two separate hard drives and then handed one to my father and another one to my grandmother and they stored them in the back of some closets in their own homes for years. My logic at the time was this: if there’s ever a fire or some other kind of disaster, at least my data is safe in two different backup locations.
I used to do the same – just with bank safe deposit box rather than offsite relatives. Even then, updating backup by swapping external drives every month or so was a chore. Since 2015, I’ve been using Mega for my offsite backup. So much more convenient, plus worldwide access (in case of need). Mega claims client-side encryption (I also encrypt my private files before syncing/uploading), and I further protect the account with 2FA.
At home, full sets of data reside in my working drive plus two external drives (one air gapped when not backing up). Additional protection where I specifically give my “standard user” self only read access to the two external drives. Writing/deleting require elevation to password-protected Admin (which I supply with my fingerprint). Easy for me, hard for malware (hopefully).
The first paragraph’s use of “previously unknown” is either confusing (there’s a 3-year old CVE and POC) or tautological (everything we know is “previously unknown”). Admittedly a nit, but one an article skimmer might think excuses WD somewhat.
You’re right. That was a holdover from before I finished reporting the story that shouldn’t have been in the lede. Thanks.
> Regardless, it’s probably safest to observe Western Digital’s advice and disconnect any MyBooks you have from **ethernet** access.
Was this supposed to be **internet** access? Not nitpicking here, just wouldn’t want anyone to think “oh it’s ok mine’s on WiFi not Ethernet”
Or USB? Fine question.
No, he means Ethernet.
Ethernet is a wired networking technology. It uses cables with plugs that resemble the classic telephone plugs you may remember seeing when you plugged a phone into a wall. (They’re wider than the phone plugs.)
The MyBooks in question have both USB and Ethernet connectivity.
If you plug them in via USB, then a single computer (the host of the USB topology) controls the device.
If you use Ethernet instead, then any computer on your local network can try to connect to the device via TCP/IP (the basis for http on the internet). And if your router has UPnP enabled (or certain other configurations), then it’s possible for someone on the internet to connect to your device.
It’s in this Ethernet configuration that the devices are vulnerable to the described attacks.
Internet users should be using “Synology” for their NAS drive needs, not that crap.
yeh, at least with Synology you know up front they have backdoors and other various other reconnaissance and remote-execution capabilities built right into their firmware….and they are not even trying to hide it, it’s written right into their EULA that you have to agree too when first setting up the NAS.
quote: “Section 7. Audit. […]You agree to grant Synology a right to access to your facilities, equipment, books, records and documents and to otherwise reasonably cooperate with Synology in order to facilitate any such audit by Synology or its agent authorized by Synology.” /quote
Where “agent authorized by Synology” = the NAS firmware itself.
It can still be firewalled. EULA blurb doesn’t actually say anything about “data harvesting” OOB beyond the backup itself. You need to accept their EULA or homebrew your own way of doing that in a way you’re more comfortable with. If anyone can openly telnet at any unsuspecting devices on your network, let’s just say Synology “backdoors” or firmware holes aren’t what you need to be worried about first. Shut the front door (firewall), update firmware regularly, and if you absolutely must remote access you absolutely must VPN. If the NAS is somehow surreptitiously evading a FW to phone data home, that’s a real gripe. See : M$ Windows since forever. That they have a slightly-azz-covering EULA with some jargon you don’t fully appreciate the deeper meaning of ought to be a clue not of a backdoor, but of a EULA.
How do you know that disabling “Remote access” solves the issue? As far as I know, the vulnerable REST API can be called in any case, or am I wrong?
Maybe from a separate attack on your network, the api could be called locally, I suppose, SO WHAT.
I own one of these devices and I remember they were specifically advertised as being suitable for remote access to your important files. That feature was central to the marketing. I never used it that way–it’s just a LAN-only media library for me at this point. I this set up with external traffic blocked at the router level.
To me, this ought to be similar to a safety recall with a car. Sure, they can say the car is out of warranty for things like regular wear and tear, but out of warranty or not, car companies are still on the hook if the airbags spontaneously explode.
Imagine if Toyota knew their airbags didn’t work and just decided not to bother with a fix. I haven’t suffered any loss, but I’ll be happy to join a class action over this. The lawyers will get fees and I probably wouldn’t get any money, but I’d do it just to teach WD a lesson. Without lawsuits, companies won’t bother even with doing the minimum.
It’s worth noting specifically that this seems to apply to MyBook *Live* devices. There are a lot of MyBook brand drives that don’t have Ethernet connectivity
I purchased a brand new MyBook Live in 2017. No one told me it left the factory years ago and was already a “legacy device” that would not receive support or updates. Thankfully, the law (in Norway) says the manufacturer is liable for manufacturing defects for 5 years from the time of purchase, the law does not care about manufacturing date.
Same here, I bought a brand new WD MyBook Live Duo in the UK in 2018. I configured it as RAID 1 for data protection. In the logs I can see that the hackers were downloading malicious files from a server in Russia. For example, they modified the login page to capture the admin password. What I can’t tell is whether they stole any of my files from the hard drive.
There should be a class action suit against WD. New devices were already “unsupported” at the time of sale. The FTC should be involved.
Just for the record, I received an email from Western Digital on 2021-06-26. It is a notification about the My Book Live and My Book Live Duo security issue.
The text reads:
Our records indicate that you registered a My Book Live or My Book Live Duo device. To protect your data on the device from ongoing attacks, we recommend you disconnect your My Book Live and My Book Live Duo from the Internet and access your data locally by following these instructions on our Knowledge Base.
Western Digital has determined that some My Book Live and My Book Live Duo devices are being compromised through exploitation of a remote command execution vulnerability. In some cases, the attackers have triggered a factory reset that appears to erase all data on the device.
Our investigation of this incident has not uncovered any evidence that Western Digital cloud services, firmware update servers, or customer credentials were compromised. As the My Book Live devices can be directly exposed to the internet through port forwarding, the attackers may be able to discover vulnerable devices through port scanning.
We understand your data is very important. Some customers have reported that data recovery tools may be able to recover data from affected devices, and we are currently investigating the effectiveness of these tools.
We are continuing our investigation and will post the latest information about this incident on our Product Security Portal. For further assistance, you can contact our Customer Support team.
Having data wiped is bad, but the question no one seems to be asking is “DID THE HACKERS STEAL ANY FILES FROM THE HARD DRIVES”. Does anyone know the answer to this vital question?
Check with Mr. Pastebin over and over for about 4 years.
A factory reset appears to erase all data on the device. But I seriously doubt that it actually erases all data on the device. Does it just wipe the file allocation table? Could the file allocation table be rebuilt? If there is a factory reset, that means that no new data is overwriting the old data. It’s not be beyond the skill of Western Digital to write an “unerase” program.
File scraping tools can recover most files. Often they won’t contain metadata and file names. But for them most common file types, the magic number / signatures are intact so the file can be recovered.
Not as simple as unerase, but useful.
…technically unless an unerase has written over the unallocated and slack sectors the data is still there and can be recovered with FTK or EnCase or the like…
…and for you conspiracy theorists out there even if it’s a “good” overwrite the data can still be recovered with a scanning electron microscope (tongue firmly in cheek)…
Why “seriously doubt”? What a weird way to live and communicate. Hard to even see the point. There are two options for the devices, once which securely erases the drive – “write zeroes”. Either method can be exploited remotely.
Well I only have bad experience with Western Digital. I bought an HDD 2 years ago. After the german law guarantee of 2 years the HDD stopped working. It was really hard to recover all my data. If you want to order an HDD or device please buy from an trusted company like Sandisk, Samsung and more however not WD.
Sorry to hear you’ve had a problem with a WD HDD. Are you aware of this recovery utility: https://www.grc.com/sr/spinrite.htm ?
Additionally, there are (or at least there used to be) companies which can recover data from faulty drives. Try looking for hard drive recovery services or data recovery services. And, yes, it will be costly but only you know the value of the data you’ve lost.
My experience with WD storage has been extremely good. And it would be worth your time to learn about S. M. A. R. T. data. There are tools and facilities which you can use to find if there are any early warning signs of problems.
FWIW, for my critical permanent storage needs (i.e. my in house backup server) I use WD Enterprise class (Gold) devices. Those have a much higher MTBF and better warranty.
And finally, if my memory serves me, SanDisk is a part of Western Digital.
.
Drivesavers <- best in the biz.
Cyka Bylat!? …So no more storing nudey pics of Babushka on icloud any more!? How about facedump, they are safe place for celebs, no?! Lol._. Decibils
might i suggest saving all your file both personal and private to icloud, they never get hacked.. except if your a celebritay
Aside from loosing your data, you should also wonder if it was downloaded before deletion.
There is a point where a vendor has to let go of a product and declare it unsupported. I have several older NAS products from another vendor that have the capability to be visible on the internet. I toyed with the idea and decided to not enable that feature, as it would be too much exposure of my data for my tastes. With the advent of Azure, Amazon and Google, the need for local storage is somewhat reduced. Although there is the MRC and the risk of those companies getting hacked. One does the best one can I guess. Three copies, two of which are offline. Unique passwords and no direct access from the web. Paranoid? No. Cautious? You bet.
To those beating on WD, WD makes a good product as does STX.
Otherwise they would have been gone a long time ago.
Every one has issues from time to time.
Backup your data, use good passwords. keep your firmware updated, update your hardware from time to time as the world changes and risks increase. Keep your powder dry.
Oh and go outside and ride you bicycle. The last is perspective
sweet, wise advice. thx.
Your blog is very informative.
Backup your data, use good passwords. keep your firmware updated, update your hardware from time to time as the world changes and risks increase. Keep your powder dry. Vclubshops
there is always global rackets, who involve in this curse of cyber crime, global cyber uniform laws should be framed. Yes with quick CERT response system.
I’m glad I opted for a USB connected My book and hooked it up to a Raspberry pi as a NAS.
The title of this article is misleading. Instead of “MyBook Users Urged to Unplug Devices from Internet” the title should be “MyBook Live Users Urged to Unplug Devices from Internet”.
The users of MyBook are not affected.