
Some of Western Digital’s MyCloud-based data storage devices. Image: WD.
Countless Western Digital customers saw their MyBook Live network storage drives remotely wiped in the past month thanks to a bug in a product line the company stopped supporting in 2015, as well as a previously unknown zero-day flaw. But there is a similarly serious zero-day flaw present in a much broader range of newer Western Digital MyCloud network storage devices that will remain unfixed for many customers who can’t or won’t upgrade to the latest operating system.
At issue is a remote code execution flaw residing in all Western Digital network attached storage (NAS) devices running MyCloud OS 3, an operating system the company only recently stopped supporting.
Researchers Radek Domanski and Pedro Ribeiro originally planned to present their findings at the Pwn2Own hacking competition in Tokyo last year. But just days before the event Western Digital released MyCloud OS 5, which eliminated the bug they found. That update effectively nullified their chances at competing in Pwn2Own, which requires exploits to work against the latest firmware or software supported by the targeted device.
Nevertheless, in February 2021, the duo published this detailed YouTube video, which documents how they discovered a chain of weaknesses that allows an attacker to remotely update a vulnerable device’s firmware with a malicious backdoor — using a low-privileged user account that has a blank password.
The researchers said Western Digital never responded to their reports. In a statement provided to KrebsOnSecurity, Western Digital said it received their report after Pwn2Own Tokyo 2020, but that at the time the vulnerability they reported had already been fixed by the release of My Cloud OS 5.
“The communication that came our way confirmed the research team involved planned to release details of the vulnerability and asked us to contact them with any questions,” Western Digital said. “We didn’t have any questions so we didn’t respond. Since then, we have updated our process and respond to every report in order to avoid any miscommunication like this again. We take reports from the security research community very seriously and conduct investigations as soon as we receive them.”
Western Digital ignored questions about whether the flaw found by Domanski and Ribeiro was ever addressed in OS 3. A statement published on its support site March 12, 2021 says the company will no longer provide further security updates to the MyCloud OS 3 firmware.
“We strongly encourage moving to the My Cloud OS5 firmware,” the statement reads. “If your device is not eligible for upgrade to My Cloud OS 5, we recommend that you upgrade to one of our other My Cloud offerings that support My Cloud OS 5. More information can be found here.” A list of MyCloud devices that can support OS 5 is here.
But according to Domanski, OS 5 is a complete rewrite of Western Digital’s core operating system, and as a result some of the more popular features and functionality built into OS3 are missing.
“It broke a lot of functionality,” Domanski said of OS 5. “So some users might not decide to migrate to OS 5.”
In recognition of this, the researchers have developed and released their own patch that fixes the vulnerabilities they found in OS 3 (the patch needs to be reapplied each time the device is rebooted). Western Digital said it is aware of third parties offering security patches for My Cloud OS 3.
“We have not evaluated any such patches and we are unable to provide any support for such patches,” the company stated.
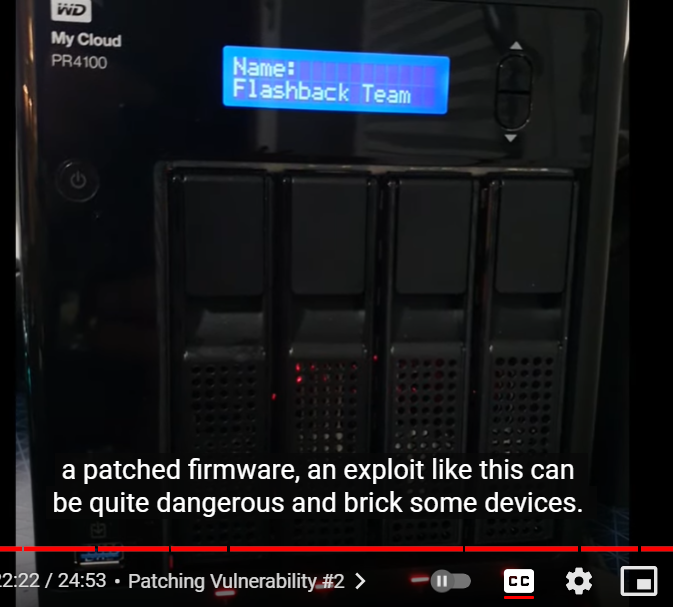
A snippet from the video showing the researchers uploading their malicious firmware via a remote zero-day flaw in MyCloud OS 3.
Domanski said MyCloud users on OS 3 can virtually eliminate the threat from this attack by simply ensuring that the devices are not set up to be reachable remotely over the Internet. MyCloud devices make it super easy for customers to access their data remotely, but doing so also exposes them to attacks like last month’s that led to the mass-wipe of MyBook Live devices.
“Luckily for many users they don’t expose the interface to the Internet,” he said. “But looking at the number of posts on Western Digital’s support page related to OS3, I can assume the userbase is still considerable. It almost feels like Western Digital without any notice jumped to OS5, leaving all the users without support.”
Dan Goodin at Ars Technica has a fascinating deep dive on the other zero-day flaw that led to the mass attack last month on MyBook Live devices that Western Digital stopped supporting in 2015. In response to Goodin’s report, Western Digital acknowledged that the flaw was enabled by a Western Digital developer who removed code that required a valid user password before allowing factory resets to proceed.
Facing a backlash of angry customers, Western Digital also pledged to provide data recovery services to affected customers starting this month. “MyBook Live customers will also be eligible for a trade-in program so they can upgrade to MyCloud devices,” Goodin wrote. “A spokeswoman said the data recovery service will be free of charge.”
If attackers get around to exploiting this OS 3 bug, Western Digital might soon be paying for data recovery services and trade-ins for a whole lot more customers.




This affects only the WD MyBook product line? If you have a WD MyPassport (ultra or other) it’s not affected, because that product is not set up to be reachable remotely over the Internet, correct?
This only affects WD devices that can connect directly to a network (i.e. NAS devices). USB-connected devices like the ones you mentioned are not affected by these bugs.
Correct. My book live and my book cloud.
Honestly.. Western Digital has a track record of atrocious software on their network attached devices. I remember getting a box of old tech with a WD NAS in it, and after a quick google, I turfed it into ewaste (after pulling out the drives) as it was a steaming pile of remotely compromisable cruft.
They clearly want to have some network attached solutions to appeal to folks who want more than just device attached storage, but their heart clearly isn’t in it… just increasing the breadth of the product portfolio.
The hyperlink for the list of MyCloud devices that support OS5 does not work.
Yes the link doesn’t work. We would really like this link to be corrected and published.
I assume this is a list of the devices that are eligible for upgrade will support WD OS5:
https://www.westerndigital.com/support/productsecurity/wdc-21004-recommended-upgrade-to-mycloud-os-5
Anybody that nowadays makes all their backup or whatever data accessible from the Internet simply through a half baked bundled OEM application is bound to be looking for trouble just like this. When will people finally realize that today’s Internet is the “Danger Zone”. For sure it ain’t Kansas anymore…
How many people know or even care if they do know?
I think the question we need to ask is do we expect all users to STOP USING the HW when the product EOL hits after a mere 4(!) years? That’s the proposition described, the security support ends with feature support. That should be decoupled IMO. Not all devices need to run the new 5 version, but the old ones should still have a rudimentary patch (it wouldn’t really cost that much, but it has a cost) to address the big flopping 0 days as discovered. If it’s something that can’t be overcome by a minor update maybe they’re off the hook, but this isn’t that. This is fixable. And I acknowledge they can’t support products forever – that’s not what I’m describing, just a priority shift towards a base-level secure state and separation of responsibility vis a vis major holes that are easily filled in 4-5 year old products, rather than artificially “deciding” that the only way to address it is landfill. Yes I’m calling for a higher legal standard than extant.
I ordered 2 Mybook drives in January that were DOA and they didn’t have any stock left to replace them. There is nothing to worry about with standard usb wd drives? I have 4 of the mypassport ones.
I find it interesting that WD will help with data recovery but ONLY if you buy (with trade-in) a new device from them. Translation: “We’re sorry you lost your precious family photos. We’ll be happy to get them back for you unless you decide you don’t want to (or are financially unable to) keep using our products.
And what’s wrong with that. WD will help with data recovery on the understanding that you won’t just stick the recovered data right back onto the vulnerable devices and go through the same thing again. Because like it or not, there would be some users stupid enough to do just that. Translation: We’ll help you recover your data but only on the understanding that you will not be using your unsupported, obsolete WD NAS system to store that data so that you don’t (and we don’t) have to go through this again.
Upon further investigation I cannot find where Western Digital is requiring people to buy a new WD NAS device in order to qualify for data recovery services. All I can find is the following statement(s):
“Data Recovery and Product Trade-In Programs: To help customers who have lost data as a result of these attacks, Western Digital will provide data recovery services, which will be available beginning in July. My Book Live customers will also be offered a trade-in program to upgrade to a supported My Cloud device.”
And the following:
“For customers who have lost data as a result of these attacks, Western Digital will provide data recovery services. My Book Live users will also be offered a trade-in program to upgrade to a supported My Cloud device. Both programs will be available beginning in July, and details on how to take advantage of these programs will be made available in a separate announcement.”
Neither of which state that in order to receive the data recovery assistance once must trade in or buy a new WD NAS device. So what is your exact source for your claim that a trade-in or purchase of a new WD NAS device is required.
Source:
https://www.westerndigital.com/support/productsecurity/wdc-21008-recommended-security-measures-wd-mybooklive-wd-mybookliveduo
Right and their answer is to give you 40% off a new product. 40%, really??? WTF! How about 80% off????
I mean, I get the discontent…But could you really even label this as incompetence? With “Nation States” that have enumerable resources dedicated to stealing any/all data…Should any company be held responsible for an exploit on out of warranty equipment especially if it’s 5 years out? If so, what is the time-line for accountability? Millennials always need someone to blame when something goes wrong…Maybe Millennials are what’s wrong…
Millennials would only set up these devices for their Boomer parents who don’t know or care to keep them updated.
The “set it and forget it” mentality of the older generation is simply incompatible with modern threats.
I know more millennials with a “set it and forget it” mentality than “Boomer parents” with that mentality. Remember, it was boomers and GenXers who created the thing. Most of us who have been around since the days when 1200 baud modems were “state of the art” know better.
It is the generation that was raised on iPhones and iThis and iThats that expect things to “just work” without putting in any effort that have led to most of this. All of that “just works” convenience has *ALWAYS* come at a security cost. But people have come to expect that computers will update themselves (because PCs and Macs do that. Even when you explicitly tell them not to; if you block their ability to do so, PCs will start complaining that you are running “unlicensed software”. It really goes hand in hand with the mentality that just accepts that we don’t own the software on our computing devices.
In a world where we don’t own the software on our computing devices, and in particular, we don’t own the software on the computing device (it’s no accident that when you install or upgrade your software, you are presented with a **LICENSING** agreement…), then yeah, I’d say it’s the publisher’s responsibility to maintain their software. If you own a car, you don’t get to stop taking care of the brakes, and still expect it to run. So sure, if I *own* the software, then I should be expected to maintain it, but I am explicitly told I *DO NOT* own the software. So which is it? Do I own the software, or do I license the software?
I doubt it. The “set it and forget it” mentality comes from household appliances that boomers invented for themselves.
Now, they treat computers like appliances. They want all the cloud benefits, but don’t understand that the cloud isn’t magic.
“But people have come to expect that computers will update themselves”
Um… no. We understand when devices prompt to be updated. We don’t call our kids every time a popup says to confirm an update like you guys.
What are you talking about? What’s your definition of “owning”. Rights to the intellectual property? Being allowed to distribute software? Or just buying the rights to operate a single instance of the software? If you write software, and sell it… do you think whoever buys a license to use it, should be entitled to indefinite support?
The car analogy is better one. When a car goes out of warranty… the owner still has to periodically check for recall notices.
I think when WD published software that deliberately disabled even basic protection like a password check… yeah, they’re responsible for that. Obviously, that update was published before they went out of warranty. They should at least be required to fix *that* bit of stupidity.
If the update that disabled password authentication for admin tasks happened to be published in the days leading up to the product going out of warranty… that’s *at least* borderline criminal. It would likely be *really* hard to prove that it was intentional, but that the sort of thing that even if it wasn’t intentional could destroy a company.
Note that I’m not saying that particular things *was* published just before they went out of warranty; I have no way to know when that entered the source code. One could probably look at the modification date in the firmware and make an educated guess, but I don’t have one of these devices (and if I did, I’d have replaced the factory OS as soon as I could figure out how. I don’t even run stock firmware on my WiFi routers if I can help it (and I always purchase units that I can reflash…) )
Given that physical storage companies think of firmware as something that can be deprecated and no longer supported, it seems like we should be relying on the firmware for as little as possible (performant I/O directly through a standard interface). Build the NAS or other solution via software on top, with those solutions presumably have much longer support timelines, and better migration paths when they reach deprecation status?
Thanks for sharing such great information, the post you published have some great information which is quite beneficial for me.
I updated my firmware to 2.41.116 but since I don’t agree with the TOS to use the new browser interface I can’t log in to jump to v5.
I disabled all apps and access to the cloud on original install and put a block rule from my LAN IP in my router so I don’t feel exposed.
I am curious I don’t really see anyone talking about the possibility of shucking these drives and putting them in a new USB 3 enclosure. I am assuming that would mitigate the security vulnerability.