A network intrusion at the International Committee for the Red Cross (ICRC) in January led to the theft of personal information on more than 500,000 people receiving assistance from the group. KrebsOnSecurity has learned that the email address used by a cybercriminal actor who offered to sell the stolen ICRC data also was used to register multiple domain names the FBI says are tied to a sprawling media influence operation originating from Iran.
On Jan. 19, the ICRC disclosed the compromise of servers hosting the personal information of more than 500,000 people receiving services from the Red Cross and Red Crescent Movement. The ICRC said the hacked servers contained data relating to the organization’s Restoring Family Links services, which works to reconnect people separated by war, violence, migration and other causes.
The same day the ICRC went public with its breach, someone using the nickname “Sheriff” on the English-language cybercrime forum RaidForums advertised the sale of data from the Red Cross and Red Crescent Movement. Sheriff’s sales thread suggests the ICRC was asked to pay a ransom to guarantee the data wouldn’t be leaked or sold online.
“Mr. Mardini, your words have been heard,” Sheriff wrote, posting a link to the Twitter profile of ICRC General Director Robert Mardini and urging forum members to tell him to check his email. “Check your email and send a figure you can pay.”
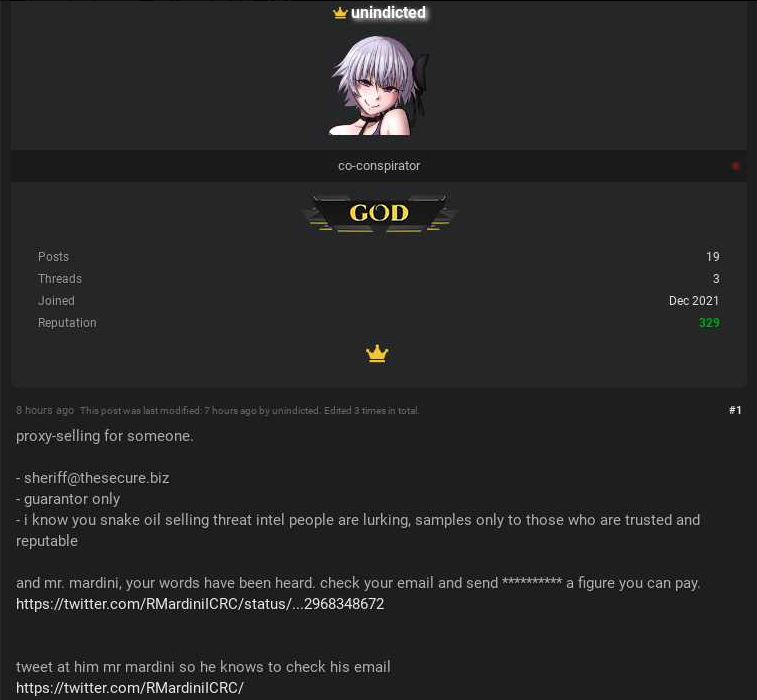
RaidForums member “unindicted” aka Sheriff selling access to the International Red Cross and Red Crescent Movement data. Image: Ke-la.com
In their online statement about the hack (updated on Feb. 7) the ICRC said it had not had any contact with the hackers, and no ransom demand had been made.
“In line with our standing practice to engage with any actor who can facilitate or impede our humanitarian work, we are willing to communicate directly and confidentially with whoever may be responsible for this operation to impress upon them the need to respect our humanitarian action,” the ICRC statement reads.
Asked to comment on Sheriff’s claims, the ICRC issued the following statement:
“Right now, we do not have any conclusive evidence that this information from the data breach has been published or is being traded. Our cybersecurity team has looked into any reported allegation of data being available on the dark web.”
Update, 2:00 p.m., ET: The ICRC just published an update to its FAQ on the breach. The ICRC now says the hackers broke in on Nov. 9, 2021, using an unpatched critical vulnerability (CVE-2021-40539). “This vulnerability allows malicious cyber actors to place web shells and conduct post-exploitation activities such as compromising administrator credentials, conducting lateral movement, and exfiltrating registry hives and Active Directory files. Once inside our network, the hackers were able to deploy offensive security tools which allowed them to disguise themselves as legitimate users or administrators. This in turn allowed them to access the data, despite this data being encrypted.”
Original story:
The email address that Sheriff used to register at RaidForums — kelvinmiddelkoop@hotmail.com — appears in an affidavit for a search warrant filed by the FBI roughly a year ago. That FBI warrant came on the heels of an investigation published by security firm FireEye, which examined an Iranian-based network of inauthentic news sites and social media accounts aimed at the United States., U.K. and other western audiences.
“This operation is leveraging a network of inauthentic news sites and clusters of associated accounts across multiple social media platforms to promote political narratives in line with Iranian interests,” FireEye researchers wrote. “These narratives include anti-Saudi, anti-Israeli, and pro-Palestinian themes, as well as support for specific U.S. policies favorable to Iran.”
The FBI says the domains registered by the email address tied to Sheriff’s RaidForums account were used in service of the Liberty Front Press, a network of phony news sites thought to originate from Iran.
According to the FBI affidavit, the address kelvinmiddelkoop@hotmail.com was used to register at least three different domains for phony news sites, including awdnews[.]com, sachtimes[.]com, and whatsupic[.]com. A reverse WHOIS search on that email address at DomainTools.com (an advertiser on this site) shows it was used to register 17 domains between 2012 and 2021, including moslimyouthmedia[.]com, moslempress[.]com, and realneinovosti[.]net.
A review of Sheriff’s postings to RaidForum reveals he has used two other nicknames since registering on the forum in December 2021: “Unindicted,” and “threat_actor.” In several posts, Sheriff taunts one FireEye employee by name.
In a Jan. 3, 2022 post, Sheriff says their “team” is seeking licenses for the Cobalt Strike penetration testing tool, and that they’re prepared to pay $3,000 – $4,000 per license. Cobalt Strike is a legitimate security product that is sold only to vetted partners, but compromised or ill-gotten Cobalt Strike licenses frequently are used in the run-up to ransomware attacks.
“We will buy constantly, make contact,” Sheriff advised. “Do not ask if we still need)) the team is interested in licenses indefinitely.”
On Jan. 4, 2022, Sheriff tells RaidForums that their team is in need of access to a specific data broker platform, and offers to pay as much as $35,000 for that access. Sheriff says they will only accept offers that are guaranteed through the forum’s escrow account.
The demand for escrow in a sales thread is almost universally a sign that someone means business and they are ready to transact on whatever was advertised or requested. That’s because escrow transactions necessarily force the buyer to make a deposit with the forum’s administrators before proceeding on any transaction.
Sheriff appears to have been part of a group on RaidForums that offered to buy access to organizations that could be extorted with ransomware or threatened with the publication of stolen data (PDF screenshot from threat intelligence firm KELA). In a “scam report” filed against Sheriff by another RaidForums member on Dec. 31, 2021, the claimant says Sheriff bought access from them and agreed to pay 70 percent of any ransom paid by the victim organization.
Instead, the claimant maintains, Sheriff only paid them roughly 25 percent. “The company pay $1.35 million ransom and only payment was made of $350k to me, so i ask for $600k to fix this dispute,” the affiliate wrote.
In another post on RaidForums, a user aptly named “FBI Agent” advised other denizens to steer clear of Sheriff’s ransomware affiliate program, noting that transacting with this person could run afoul of sanctions from the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) that restrict commerce with people residing in Iran.
“To make it clear, we don’t work with individuals under the OFAC sanctions list, which @Sheriff is under,” the ransomware affiliate program administrator wrote in reply.
RaidForums says Sheriff was referred to the forum by Pompompurin, the same hacker who used a security hole in the FBI’s website last year to blast a phony alert about a cybercrime investigation to state and local authorities. Pompompurin has been quite active on RaidForums for the past few years, frequently posting databases from newly-hacked organizations, and selling access to stolen information.
Reach via Twitter, Pompompurin said they had no idea who might have offered money and information on Sheriff, and that they would never “snitch” on Sheriff.
“I know who he is but I’m not saying anything,” Pompompurin replied.
The information about Sheriff was brought to my attention by an anonymous person who initially contacted KrebsOnSecurity saying they wanted to make a donation to the publication. When the person offering the gift asked if it was okay that the money came from a ransomware transaction, I naturally declined the offer.
That person then proceeded to share the information about the connection between Sheriff’s email address and the FBI search warrant, as well as the account’s credentials.
The same identity approached several other security researchers and journalists, one of whom was able to validate that the kelvinmiddelkoop@hotmail.com address actually belonged to Sheriff’s account. Those researchers were likewise offered tainted donations, except the individual offering the donation seemed to use a different story with each person about who they were or why they were offering money. Others contacted by the same anonymous user said they also received unsolicited details about Sheriff.
It seems clear that whoever offered that money and information has their own agenda, which may also involve attempts to make members of the news media appear untrustworthy for agreeing to accept stolen funds. However, the information they shared checks out, and since there is precious little public reporting on the source of the ICRC intrusion, the potential connection to hacker groups based in Iran seems worth noting.




Really the Red Cross… you animals.
Red Cross , like other ”worldly” organizations have been proxies for spy agencies and money laundering for operations thru-out history.
“Better the devil you know than the devil you don’t.”
or
“Listen, child—if you’re at a party with a hundred people and one of them is the devil, he’ll be the last one you’d suspect.”
― Dean Koontz, Deeply Odd
and
“… the devil doesn’t come dressed in a red cape and pointy horns. He comes as everything you’ve ever wished for …”
― Tucker Max, Assholes Finish First
Following up broad-brush, dramatic, unverified claims with pithy verifiable quotes is a very good diversionary tactic.
You have incontrovertible evidence for your absurd claim about the Red Cross, of course…
Sergi -SIC Tolstoy does not make mistakes.
That “anonymous person” was trying to buy your silence in further investigative online journalism on the subject matter.
I know I’ve seen the profile picture that “unindicted” is using before. Can someone please remind me what his other aliases are?
From the story:
A review of Sheriff’s postings to RaidForum reveals he has used two other nicknames since registering on the forum in December 2021: “Unindicted,” and “threat_actor.” In several posts, Sheriff taunts one FireEye employee by name.
He’s been around longer than that. He’s the one who did this: https://krebsonsecurity.com/2021/04/are-you-one-of-the-533m-people-who-got-facebooked/
I just can’t remember the name
I found another of his aliases, “pshmm”. Maybe that’s what I’m thinking of. I could’ve swore sheriff was a different person entirely.
LONG LIVE THREAT ACTOR POM POM PURIN – RIPTIDE
Following up broad-brush, dramatic, unverified claims with pithy verifiable quotes is a very good diversionary tactic.
“attempts to make members of the news media appear untrustworthy for agreeing to accept stolen funds”
This right here should not be overlooked. The info may check out, but dangling a bit real bait might be worth it for someone.
Krebs investigates hundreds of cybercrime groups and individual cyber criminals. One of those actors could be trying to taint the journalistic integrity of the top investigators.
“[T]the FBI says are tied to a sprawling media influence operation originating from Iran.”
Yep – every hacker worth his salt originates his hacks right from his own home country! And this brought to us by the same government that warned the world so helpfully about Iraq’s WMD’s and imminent nuclear attack capabilities! Colin Powell even did his powerpoint presentation to the UN!!
I don’t automatically assume that our government lies to us. Neither will I automatically trust it. If other intelligence agencies — outside of the Five Eyes — will corroborate on this, I’ll believe it more.
Cry more cuck.
This proves only one thing. Pompompurin is a real n****,
I love trolling the media lel, thx brian for believing my bs. Dis why no 1 trust da americans they r cappers
Donald this isn’t going to keep you out of jail, give it up.
This just shows how mentally ill some of these people are, they really need help, $1 worth of lead would do for this one.
I’ve spent many hours over the years in the cold ringing the bell. My personal reward is seeing parents teach children sharing with others and compassion. Something these scum known nothing of. A small child is smarter than these leaches on society.
Like many of these breaches although the once inside a network the cyber-attach has been very sophisticated, the original entry point was very preventable with minimum technology and cost. The vulnerability in question (CVE-2021-40539) was to the Zoho ManageEngine ADSelfService Plus version 6113 and prior which was “vulnerable to REST API authentication bypass with resultant remote code execution.”
The availability of a security update for this vulnerability was in a CISA Current Activity Notification on 9/7/2021. On 9/16/2021 the CISA Alert AA21-259A (https://www.cisa.gov/uscert/ncas/alerts/aa21-259a ) Notification sent about a joint advisory from the FBI, CGCYER, and CISA disclosing active exploitation of this vulnerability. This was almost two months before ICRC was breached, more then an enough time to patch such a critical piece of software. And if your organization cannot do that, then that is the problem to solve not getting a new piece of software using AI.
On 11/3/2021 the CISA Current Activity Notification titled CISA Issues BOD 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities (https://www.cisa.gov/uscert/ncas/current-activity/2021/11/03/cisa-issues-bod-22-01-reducing-significant-risk-known-exploited ) announcing the “Catalog of Known Exploited Vulnerabilities” (https://www.cisa.gov/known-exploited-vulnerabilities).
CVE-2021-40539 was in the original catalog entries, tied for 16th for the earliest Due Date to patch of 11/17/2021.
If you are not familiar with the CISA National Cyber Awareness System notifications, please educate yourself. Many trade rag articles are written the next day after one of these notifications, save yourself 24 hours and signup. Then instill a procedure to look at them once or twice a day (takes less than 5 minutes most days), and then when the information is relevant to your organization execute.
It would be helpful if there were a central database of organized fake news and other similar influence operations available.
Perhaps I’m unaware of the existence of such a resource.
Surely you have heard of Fox News.
I would not call Fox News fake news, because they are pretty much not news anymore, just opinion and analysis… Have you ever seen Tucker Carlson, he may be right, he might be wrong, but at least is trying to be logical and analytical, not reading mindlessly a script as most media do, just one single example of thousands of “safe and effective” propaganda: https://tube.cadence.moe/watch?v=hWLjYJ4BzvI
“Hitler may be right, Hitler may be wrong, but at least the trains try to run on time.”
Fox is the largest of “the media” and Tucker is a conspiracy golden goose.
Henry Kissinger basically outlined it way back in the golden age of deception.
I’m not interested in clicking links so much, but do us both a solid instead :
Search yourself – “How Roger Ailes Built the Fox News Fear Factory”
We understand the popularity of the Rogan method of Journalism.
He’s just asking questions, who knows if racial slurs are legitimate?
I don’t know any phlebotomists do you? I check my own DNA bro.
Tucker alone can fix it unless it’s a toilet full of classified memos.
Research doesn’t require peer review if you’re entirely peerless.
Prove it didn’t happen and if you can’t it’s just more proof it did.
It’s 3am, do you know where your belief system is? Whose it is?
Place your bets please. Always double down.
Mediabiasfactcheck.com