An Estonian man was sentenced today to more than five years in a U.S. prison for his role in at least 13 ransomware attacks that caused losses of approximately $53 million. Prosecutors say the accused also enjoyed a lengthy career of “cashing out” access to hacked bank accounts worldwide.

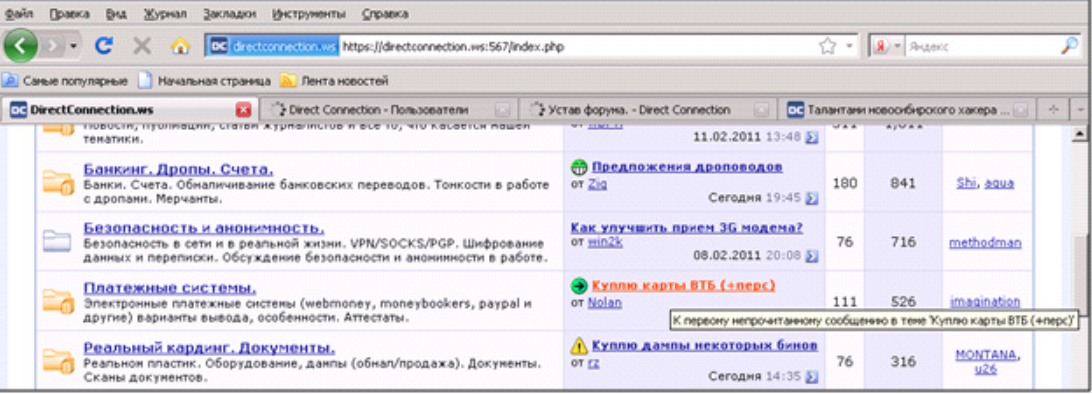
Maksim Berezan, 37, is an Estonian national who was arrested nearly two years ago in Latvia. U.S. authorities alleged Berezan was a longtime member of DirectConnection, a closely-guarded Russian cybercriminal forum that existed until 2015. Berezan’s indictment (PDF) says he used his status at DirectConnection to secure cashout jobs from other vetted crooks on the exclusive crime forum.
Berezan specialized in cashouts and “drops.” Cashouts refer to using stolen payment card data to make fraudulent purchases or to withdraw money from bank accounts without authorization. A drop is a location or individual able to securely receive and forward funds or goods obtained through cashouts or other types of fraud. Drops typically are used to make it harder for law enforcement to trace fraudulent transactions and to circumvent fraud detection measures used by banks and credit card companies.
Acting on information from U.S. authorities, in November 2020 Latvian police searched Berezan’s residence there and found a red Porsche Carrera 911, a black Porsche Cayenne, a Ducati motorcycle, and an assortment of jewelry. They also seized $200,000 in currency, and $1.7 million in bitcoin.
After Berezan was extradited to the United States in December 2020, investigators searching his electronic devices said they found “significant evidence of his involvement in ransomware activity.”
“The post-extradition investigation determined that Berezan had participated in at least 13 ransomware attacks, 7 of which were against U.S. victims, and that approximately $11 million in ransom payments flowed into cryptocurrency wallets that he controlled,” reads a statement from the U.S. Department of Justice.
Berezan pleaded guilty in April 2021 to conspiracy to commit wire fraud.
For many years on DirectConnection and other crime forums, Berezan went by the hacker alias “Albanec.” Investigators close to the case told KrebsOnSecurity that Albanec was involved in multiple so-called “unlimited” cashouts, a highly choreographed, global fraud scheme in which crooks hack a bank or payment card processor and used cloned payment cards at cash machines around the world to fraudulently withdraw millions of dollars in just a few hours.
Berezan joins a growing list of top cybercriminals from DirectConnection who’ve been arrested and convicted of cybercrimes since the forum disappeared years ago. One of Albanec’s business partners on the forum was Sergey “Flycracker” Vovnenko, a Ukrainian man who once ran his own cybercrime forum and who in 2013 executed a plot to have heroin delivered to our home in a bid to get Yours Truly arrested for drug possession. Vovnenko was later arrested, extradited to the United States, pleaded guilty and spent more than three years in prison on botnet-related charges (Vovnenko is now back in Ukraine, trying to fight the Russian invasion with his hacking abilities).
Perhaps the most famous DirectConnection member was its administrator Aleksei Burkov, a Russian hacker thought to be so connected to the Russian cybercriminal scene that he was described as an “asset of extreme importance to Moscow.” Burkov was arrested in Israel in 2015, and the Kremlin arrested an Israeli woman on trumped-up drug charges to force a prisoner swap.
That effort failed. Burkov was extradited to the U.S. in 2019, soon pleaded guilty, and was sentenced to nine years. However, he was recently deported back to Russia prior to serving his full sentence, which has prompted Republican leaders in the House to question why.
Other notable cybercrooks from DirectConnection who’ve been arrested, extradited to the U.S. and sentenced to prison include convicted credit card fraudsters Vladislav “Badb” Horohorin and Sergey “zo0mer” Kozerev, as well as the infamous spammer and botnet master Peter “Severa” Levashov.
At his sentencing today, Berezan was sentenced to 66 months in prison and ordered to pay $36 million in restitution to his victims.




Another one bites the dust!
Is 66 months a fair sentence?
If they got the $$53MM squired away, looks like crime pays well. Who knows, while in prison, they may be able to do more hacking. And if someone gets 66 months in the USA, they may halve the sentence for good behavior. That is impressive they got the $1.7MM bitcoin. I thought it was safer than a Swiss bank account.
Exactly, very light sentence.
In the US, federal prison time cannot be halved for good behavior. At most, you can get is 2-3 weeks a year iirc.
So if he’s serving 5.5 years, he might be able to shave off 2-3 months off his total time if he’s good.
That being said, I do believe 66 months is a fair sentence.
In addition to the 54 days/yr for good time federal inmates who successfully participate in recidivism-reduction programs will qualify for early release from prison under new rules unveile by the U.S. Justice Department.Jan 2022.
There is some disconnect if you believe 53 million in loss is worth less than 52 months prison time. I’m sure that sentence will provide retribution, deterrence, incapacitation, rehabilitation and restoration as are the goals of the criminal justice system.
Anon(1) said 66 was fair to them, not that 52 was unfair.
“and ordered to pay $36 million in restitution to his victims.”
+ the cooperative informing + the prison time. He gave it up.
The deal is you give up everything you know, not a little bit.
He didn’t obtain $53 million, reads that he caused that amount in losses for businesses as a result of his attacks. Perhaps earned $11million in ransom payments according to the article. Likely has the lifetime assets to cover the restitution.
An_n – what? What was described realistically the Albanec looking at 52 months with system available. So 66 = 52 would be fair to Anonymous. the losses are what police can prove. Like any crime, commit 10 caught for one. Much more losses by actor. Yes what you can prove and with that I understand agree “eto legkiy prigovor” Nikulin made company loss 550.000 and 88 big month in prison.
He did not kill someone it was numbers and digits wich banks add zeros or taking a zeros…nowdays money is not real thing its just digits.
Second point is our streets are much more safer if there is ways to earn money like this otherwise knife crimes or other robberies will be starting
But nowdays criminal activity is for educated and well connected people uneducated and without connections can maximum steal vodka from shop lol… nowdays you need to be rich to make money and organised crime no different only wealthy people can do crimes like this for sure he had all ready money poor people dont do crimes its impossible
But this men is not estnonian its not estonian name btw so why say its estonian ??
He didn’t attack someone violently, but what if someone dies because ransomware locked a hospital’s system so they couldn’t get treatment? Or a company had to close because of ransomware, what about the impact to staff, the stress to owners of small business etc? Has anyone ever committed suicide or self-harm after an attack like that affected systems they were responsible for securing?
I agree his crimes were not the same as someone who attacks their victims physically, but I have a lot of issue with the idea of “victimless crimes” – you might say a crime against a big bank or corporation was “victimless”, do you really think the corporations just wear the loss rather than pass it on to all of us?
A similar type of attack was used to hijack the domain dark(DOT)fail around a year ago. Someone produced a document that resembled a German court-order, sent it to the registrar Tucows (which was registrar of domain and had some business in Germany) and then their compliance team transferred the domain to Tucows account belonging to attacker who then attempted to complicate ownership of the domain by transferring to another ICANN registrar. This was further complicated by the fact the court-order had a false ‘gag order’ and as far as I am aware, neither the Tucows reseller or the registrant were aware anything was amiss until the domain was ‘stolen’ and replaced with a phishing site.
This article is really amazing. Thanks for the sharing.
To be really very very honest I am always amazed when I actually look at you that despite being yourself so very knowledgeable how come you just keep benefitting others as well as helping others with it. Thanksgivings for the very knowledge sharing that you actually do for others.
To be really very very honest to you I actually thought that you would just be arrogant as well as like those highbrows as you are so very knowledgeable but in reality, you are so very humble and the real manner in which you just keep sharing your very knowledge to all, it actually deserves my commendation.