Researchers are tracking a number of open-source “protestware” projects on GitHub that have recently altered their code to display “Stand with Ukraine” messages for users, or basic facts about the carnage in Ukraine. The group also is tracking several code packages that were recently modified to erase files on computers that appear to be coming from Russian or Belarusian Internet addresses.

The upstart tracking effort is being crowdsourced via Telegram, but the output of the Russian research group is centralized in a Google Spreadsheet that is open to the public. Most of the GitHub code repositories tracked by this group include relatively harmless components that will either display a simple message in support of Ukraine, or show statistics about the war in Ukraine — such as casualty numbers — and links to more information on the Deep Web.
For example, the popular library ES5-ext hadn’t updated its code in nearly two years. But on March 7, the code project added a component “postinstall.js,” which checks to see if the user’s computer is tied to a Russian Internet address. If so, the code broadcasts a “Call for peace:”
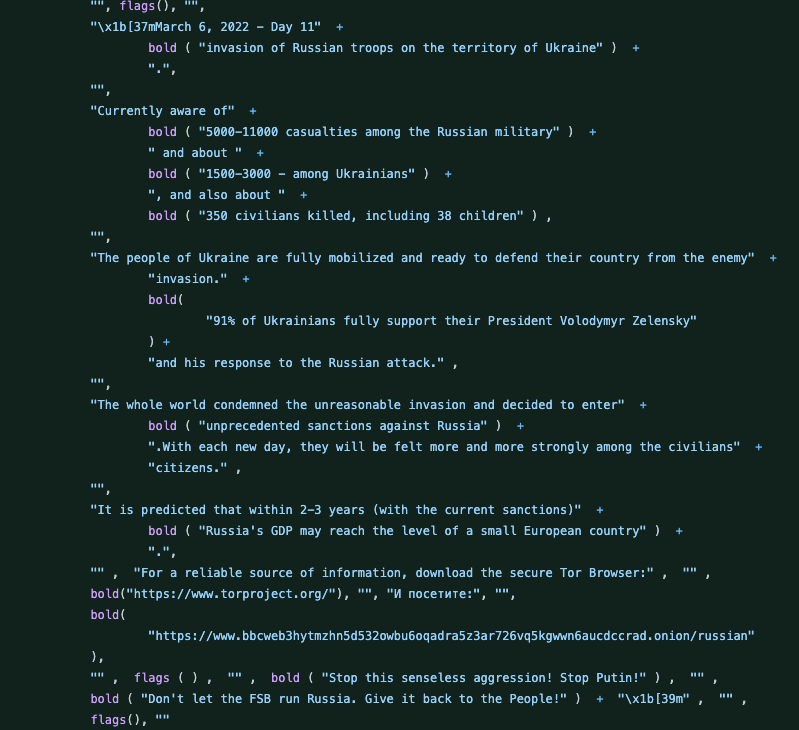
A message that appears for Russian users of the popular es5-ext code library on GitHub. The message has been Google-Translated from Russian to English.
A more concerning example can be found at the GitHub page for “vue-cli,” a popular Javascript framework for building web-based user interfaces. On March 15, users discovered a new component had been added that was designed to wipe all files from any systems visiting from a Russian or Belarusian Internet address (the malicious code has since been removed):
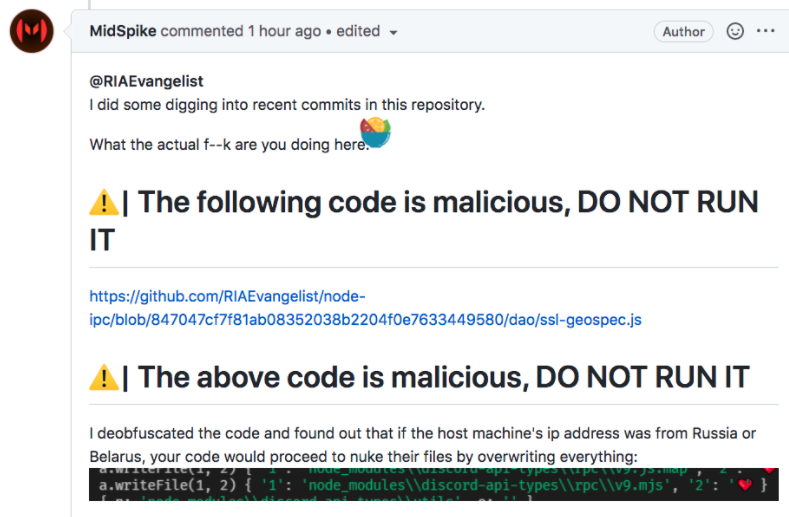
Readers complaining that an update to the popular Vue-Cli package sought to wipe files if the user was coming from a Russian IP address.
“Man, I love politics in my APIs,” GitHub user “MSchleckser” commented wryly on Mar. 15.
The crowdsourced effort also blacklisted a code library called “PeaceNotWar” maintained by GitHub user RIAEvangelist.
“This code serves as a non-destructive example of why controlling your node modules is important,” RIAEvangelist wrote. “It also serves as a non-violent protest against Russia’s aggression that threatens the world right now. This module will add a message of peace on your users’ desktops, and it will only do it if it does not already exist just to be polite. To include this module in your code, just run npm i peacenotwar in your code’s directory or module root.”
Alex Holden is a native Ukrainian who runs the Milwaukee-based cyber intelligence firm Hold Security. Holden said the real trouble starts when protestware is included in code packages that get automatically fetched by a myriad of third-party software products. Holden said some of the code projects tracked by the Russian research group are maintained by Ukrainian software developers.
“Ukrainian and non-Ukrainian developers are modifying their public software to trigger malware or pro-Ukraine ads when deployed on Russian computers,” Holden said. “And we see this effort, which is the Russians trying to defend against that.”
Commenting on the malicious code added to the “Vue-cli” application, GitHub user “nm17” said a continued expansion of protestware would erode public trust in open-source software.
“The Pandora’s box is now opened, and from this point on, people who use opensource will experience xenophobia more than ever before, EVERYONE included,” NM17 wrote. “The trust factor of open source, which was based on good will of the developers is now practically gone, and now, more and more people are realizing that one day, their library/application can possibly be exploited to do/say whatever some random dev on the internet thought ‘was the right thing they to do.’ Not a single good came out of this ‘protest.'”




Perhaps “trust” should be eroded a bit.
I love open-source, and use it nearly everywhere. We hear so much about the generic concept of zero-trust, but applying it in practice is really difficult.
We cannot expect to audit all code repositories that we use, so we must “trust” the developers. We also “trust” they will never sell their product, retire and let some anon take over. We also “trust” they will stay up to date with patches.
We need a new paradigm for open source. Donations and stable revenue for developers, please. And tie that revenue to certain obligations.
This kinda thing will continue to happen with open source, regardless of how many projects/enterprises are dependent on them. Since the devs are not getting paid to keep their code secure, clean and apolitical, they don’t have an obligation to their users beyond a pinky promise to not be evil.
You package it into your project and you’re responsible for your project.
“We cannot expect to audit all code repositories that we use” = Nonsense.
If you feel like being lazy and trusting unsecured sources, that’s your choice,
not a flaw of OSS. If this highlights that there are some lazy devs out there,
everybody knows that already. That’s what happens, that’s not on everybody,
that’s on the person responsbile for the project in question. Pay is unrelated.
If you’re sloppy because you aren’t being paid not to be, we don’t want your js.
By we, I mean non-developers.
Non-developers make up the vast majority of open source software users. We, the user base, are not paying for the software development. And we have to “trust” the developers that manage those projects to not be lazy and audit upstream code from dependencies.
Trust in this context is a chain (or web), where the user can’t be expected to audit code. So the users trust the package maintainer, who in turn trusts the project team of devs, who should then trust but verify the code originating from those libraries and/or other dependencies.
Any one of them can inject something malicious, or bugs, or politics.
If you can’t read code, you aren’t responsible for code. You are blindly trusting everything.
From that vantage you have little recourse and this isn’t really about you or your issue
as you decide what you install and who you trust. Reputations exist for these reasons.
Similar problems (different, but similar) can and do happen with proprietary projects.
This isn’t a flaw in OSS just because you misplaced your trust in unsecured repos/devs.
If you are installing without verifying you have circumvented your own trust model and
basically aren’t in a position to complain because it’s always been that way in all code.
It’s not an “OSS problem” that some devs are sloppy and some repos are too permissive.
If you demand total security you do your own homework and maintain your own repos.
Use what you choose and by your own criteria you’re insecure by own choice.
There is no such chain of trust if you’re oblivious to the code and the systems relaying it,
you’re basically trusting anything at all based on crowdsourced popularity contests.
That too is your choice.
I use Ubuntu on my home system since last year. Are you saying I shouldn’t?
Trusting Ubuntu is a choice. What’s it based on? Start right there.
If Ubuntu were majorly undermined internally would you continue?
You can’t have it both ways with regard to security vs blind trust.
Ubuntu has a lot of eyeballs on it compared to tiny js code snips.
That’s a plus, but it’s not a guarantee nor does OSS make them.
I don’t think I’m alone in saying that I have to blindly trust the software I use. I cannot afford to hire a hacker to look at this stuff. It does not seem fair that you suggest that everyone should learn coding.
You admit it, that’s certainly a good start. I’m saying your blind trust is basically not even a half step above random chance unless you have some underlying criteria for doing so. It’s rewarding popularity via crowdsourcing and marketing more than anything. Do you read Ubuntu forums, do you dive into the bug lists and see who is fixing what, do you read critical reviews from trusted sources, and do you reevaluate in the light of an repo attack that goes undiscovered for major version rollouts consecutively? If not, you might as well be on Windows FWIW in terms of blind trust. It’s not at all an OSS exclusive problem is my point nor can OSS be expected to be entirely secure in aggregate. It’s like saying “I should be able to trust all software” essentially. Really? Some do I guess!
Right on Anna. Writing this comment on Firefox. Its Open Source right? I cannot verify its code. I assume someone is verifying its code. But I don’t know any of those people. The good (I assume) folks at mozilla can decide to put protestware in Firefox and there is nothing I can do to stop them.
It’s so arrogant and stupid to say that I need to either learn to read all the source code or just stop using it.
“I don’t know any of those people.
I trust cnet reviews and stuff.”
Or? What is your criteria, OSS = secure? There are other OSS browsers. No trust? Big name wins? If Firefox is organizationally stupid enough to allow malicious code to go out as a final product you would be outraged and switch. Wouldn’t you. It’s “so arrogant and stupid” to lump all OSS together as if these custody and verification problems only (or equally) affect all of it and on that basis you’re making decisions either way? You have but the reputation alone as your criteria unless you’re going to a further extent to verify security, was the point. The expectation of 100% secure and quality code in each and every local repository of “Open Source Software” is just the dumbest thing I’ve ever heard of since Kenny Thompson explained trust’s relativity the first time.
Having trust in OSS “because OSS” is just insane underthink. When you put organizational reputation ahead of the verification you’re asking for it either way, even assuming the popular reputation is accurate is a massive stretch these days. You blindly trust and are defensive about the practice, that’s entirely understandable. It’s not the concept of OSS as intended.
“It does not seem fair that you suggest that everyone should learn coding.”
Life isn’t fair, nor is it expected secure to trust 3rd parties blindly.
The expectation of trusting things “because OSS” 1:1 is the fail.
It’s not an OSS exclusive issue, if anything OSS mitigates it.
I think I understand. Sounds like its probably for the best that I erode my trust in open-source software. That much I do agree with the original post.
I’ve never seen such a flame war from people that fundamentally agree.
Because all OSS is equivalent?!
(& as opposed to closed source?)
Blind trust is truly blind then.
Just install debsecan package, security analysis automation tool with CVE reportings
You are right. But there’s another thing. I have clients who order JS coding, some of them are Russian. I never had to test what happens when a person with Russian IP uses our code, I was pleased with the results my staff had. It’s not an issue to add a few extra tests like this but damnit, now I should. Hence Russian clients will pay more money for the same work and my (Ukrainian btw) coders will get less. So some of the Russian clients would probably choose Russian developers instead of me. I’ll survive, but my Ukrainian coders will get less money. Is it what this was about?
You absolutely should be verifying your final product as much as is possible before delivering it to clients if you value those relationships. As that costs extra money, just consider the money you “saved” by being lucky enough not to have been burned to date while not doing verification in depth already. It’s also obviously not smart to lump coder talent or trust/expectations of quality by nationality alone as of course you can be burned by locals just as easily, or anyone else in the chain.
What you just described is closed-source software.
Well, somewhere in between. Open-Souce doesn’t have to be “free” open source. And even software that pays well for its developer doesn’t necessarily need be a “paid” app either.
Right now, its hard to find good secure and well maintained code without paying for it. Donations isn’t really sustainable long term.
Closed source has its problems too. Zero-days can last a long time since not many people are looking at closed source code, and you have to wait until a white hat finds it and reports it. It can be months or years if only the black hats know about vulnerabilities.
Whether you’re paying money for software directly or using a free license, you are trusting the motivations of the developers. I’d prefer to trust their self-interest in collecting consistent revenue, but with much of the Free Open Source community, you are just trusting the “good will” of the devs. If that good will turns sour, or politics become important to them, then that will be their primary interest. Most of the time, they just stop maintaining the code.. but in the case of protestware, they want to increase awareness.
Development “advice” from non-developer who doesn’t read code.
It’s not advice for developers. It’s advice for people who use software. If you think only developers use software, then you’re in your own little bubble.
I can read and write code just fine. But it’s not developed code for consumer use. Most of my writing is at higher level interpreted languages. But I need to be able to read lower level code so I can understand how malware functions or maybe write an exploit.
I sometimes work with devsecops but it’s very frustrating because so many developers don’t know crap about security.
Developers are generally not respected in the IT field. The labor market for developers is saturated by anybody who says they can code. I’m reminded of that Rick and Morty episode where that alien is asking everybody to develop an his app. Sounded like a commentary that even Jerry can be a developer.
Anyway, my point is that I don’t want to be a developer. It’s a crap job. Under appreciated and underpaid. Most people don’t want to be and will never be a developer, and should not have to learn how to read their code in order to trust them.
It’s not actually advice at all.
Writing this comment on Firefox. Its Open Source right? I cannot verify its code. I assume someone is verifying its code. But I don’t know any of those people. The good (I assume) folks at mozilla can decide to put protestware in Firefox and there is nothing I can do to stop them.
It’s so arrogant and stupid to say that I need to either learn to read all the source code or just stop using it.
It’s also extremely arrogant to suggest that not being a developer is somehow a negative. If anything, this story shows that developers can be whiny, greedy, and emotional to the point that they betray their users.
Speaking of whiny (cough!) no less, you either work with code or you don’t.
Being a user of (an) open source isn’t some open ticket to complain about it.
You demand everything sight unseen, you deserve absoluetly nothing at all.
“If anything, this story shows that developers can be whiny, greedy, and emotional to the point that they betray their users.”
Not that you’d know. A world of surprises awaits, proprietary trolls.
> you either work with code or you don’t.
What the hell? What dogmatic, cultish nonsense is this?
If you’re a developer, you give the rest of us a bad name.
There are thousands of coding languages with hundreds in popular use today. I often have to develop in one language for clients who only know markup languages. I wouldn’t expect them to know how to read my source code. Don’t act so high and mighty just because you know some languages, you don’t know them all.
The developer in question does not claim to develop any code or practice any actual best practices. That’s kind of key even to someone pretending to beo outraged in a duplicate nom de guerre. No one claims to know all languages, but some claim even by knowing none they can give advice about all of them. “Veteran Developer” is not a realistic nom de guerre either.
Way too obvious JposerJ
Everyone who isn’t me is JamminJ poser. I know because only I use mealy, SMH and Criticality here.
Like Space Exploration, we should leave politics out of open source libraries.
Oh.
I just emailed you asking you to look into it. Refreshed the page and there it was… haha. Great work!
Holden is I believe Milwaukee, WI based not Minneapolis, MN. Thanks always for your great work Brian.
I’d sure love to see what the chat records for the Conti ransomware group are saying these days!
There’s also https://nvd.nist.gov/vuln/detail/CVE-2022-23812 referring to the node.js node-ipc package.
Overall this seems to be a really bad, bad thing. Aside from anything else, as we ThreatSTOP have noted on our blog, geolocation is a really inaccurate thing in many cases, so the chances are high that there will be false positives and quite likely those will be in Ukraine and thus be precisely the people the hactivists want to support.
Plus there’s the way this does significant damage to trust in open source as nm17 noted. Now to some degree that’s good. Excessive trust in open source libraries and dependencies lets all sorts of supply chain hacks take place, but there’s a significant danger that we end up throwing the baby out with the bathwater on this
Anyone using packages they don’t control in their project should be vetting that code, but they don’t. Too many automatically pull it in which is the entire issue. This is a laziness issue disguised as trust. Can’t the 3rd parties maintain their own node repository for their own projects and keep them secure? Of course they could, they just don’t, and this is the bathwater practice that is dirty by design. If you’re responsible for the baby, test the bathwater first. It only sounds completely basic and common sense because it actually is, but I don’t think it per se undermines OSS, just this one particular aspect or practice of it. I don’t see a reason why this isn’t entirely avoidable going forward, if wanted.
“Anyone using packages they don’t control in their project should be vetting that code” assumes its “their project”. Not everyone is a developer. Code gets used by end users who are not developers. Those users are not vetting that code, so who is?
Its not just the open source libraries and dependencies that need trust, but the project teams that are supposed to be vetting all their dependent code. In the case of protestware it is the project devs that are injecting into the codebase. They might be the last devs in the chain before it reaches a consumer.
JamminJ you are not Criticality.
^ JamminJ’s argument, posing as criticality.
JCriticalityJ, you should use, instead of someone else’s name to make the JamminJ argument.
If you were honest.
So if I use OpenSSL library in my project I should be vetting the full OpenSSL codebase or else I am just lazy?!?
Do you have any idea how stupid your argument is?
Not even longtime OpenSSL developers were able to spot Heartbleed bug for more than 5 years, what chance someone not familiar with the codebase and cryptography has to audit the OpenSSL code before including it in their project?
Libraries exist so that developers do not have to be experts in all fields because that is literally impossible given the complexity.
If you had to audit all 3rd party code you use it would not only defeat the purpose of using libraries and modular programming, but you would also need to audit your compiler, OS, and BIOS as well as firmware and drivers of every hardware device you use.
Software is a complex web of dependencies and verifying them all would not only require insane amount of time and expertise, but would also cause development costs skyrocket to the point of nobody but the biggest companies being able to afford to write and purchase software.
So next time try not to make an idiot out of yourself by giving uninformed opinions on a subject you are obviously not familiar with and by insulting a whole class of hard-working people working on thankless jobs.
There’s also similar behavior (my comment with the link went in the spam bucket) in the node.js node-ipc package.
Overall this seems to be a really bad, bad thing. Aside from anything else, as we ThreatSTOP have noted on our blog, geolocation is a really inaccurate thing in many cases, so the chances are high that there will be false positives and quite likely those will be in Ukraine and thus be precisely the people the hactivists want to support.
Plus there’s the way this does significant damage to trust in open source as nm17 noted. Now to some degree that’s good. Excessive trust in open source libraries and dependencies lets all sorts of supply chain hacks take place, but there’s a significant danger that we end up throwing the baby out with the bathwater on this
“Now to some degree that’s good. Excessive trust in open source libraries and dependencies lets all sorts of supply chain hacks take place, but there’s a significant danger that we end up throwing the baby out with the bathwater on this”
I agree completely. We need a better way. Having this false dichotomy of either “verified trust” by auditing every line of code yourself, or “blind trust” where you have no excuses and deserve what you get… is just wrong. I think Open Source developers need to get paid more than just the inconsistent and meager donation system of today. I don’t know how it might look, but if you pay them well, they would be willing to sign contracts that stipulate their efforts to be secure, timely and free of protestware.
JamminJoke non-dev give more advice, then pretends to be SMH.
SMH has been one of my names on here. I claim it.
Being a non-dev is supposed to be an insult. Only developers are allowed to have an opinion about developers.
List of other protestware repositories https://github.com/open-source-peace/protestware-list
This is childish and very harmful. People have learned the power of canceling supposed bad actors on twitter. Now everyone thinks that canceling an entire country makes sense. Breaking trust in open source will have implications far and wide, with lots of collateral damage.
Looks like postinstall.js is a lot cruder than checking whether a computer is tied to a Russian internet address. It only checks time zones.
Where did they get the line about Russian IP’s then? Did they invent that or different node package?
Sadly the genie is out of the bottle, and it isn’t benevolent at all. I would add to this concern the possibility of distribution corruption, now that so many distributions are using snaps and you need non-distribution software providers, the same process applying and a plethora of library CVEs. Relying on an IPv4 address to definitively identify a computer as being in a given locale is prone to give false results, as IP addresses are easily spoofed or anonymized, not even getting into the discussion of IPv6 with it’s phenomenal addressing potential. Another object lesson in the road to hell being paved with good intentions, IMHO…
If your developers aren’t vetting the code that goes into your company’s products or external presence the company deserves what it gets (and customers would be right to abandon the products). This whole load everything plus four kitchen sinks because some lazy or incompetent programmer doesn’t want to write a few lines of code needs to end.
Humans are inherently opinionated individuals. Those opinions will eventually make it into the way products are built, distributed, and used. Just assuming no one will mess with code at some point in the future because it would be ‘bad’ is like sticking a Windows XP computer on the Internet and expecting no one to exploit it. At least with FOSS the source code is auditable if you’re skilled enough or have enough eyes on it these things can be found – assuming those gating in these projects aren’t lazy. It’s impossible to do the same with proprietary products.
This doesn’t erode any trust in FOSS that shouldn’t have already in “trust but verify” mode, which is the ENTIRE POINT of FOSS to begin with.
What happens if you’re an end-user, not a developer, or your company uses software but doesn’t have a team of developers? Do you just never use open source?
JamminJ if your company doesn’t have developers you shouldn’t be developing.
They are not developing. Open Source software is in use all over the world, by companies and individuals. who don’t develop their own software.
JamminJ using other people’s nicks (again) here is not a great idea, Brian will know.
Like last time.
mealy posts using all sorts of nicks, is JamminJ also mealy
JamminJ historically has posed as multiple people (not random new names but actual nicks of people in the dicussion) to discredit them for disagreeing.
He really can’t accept when people simply disagree. Look at the history of the clap-backs where it’s basically a settled issue or resigned to an opinion, always escalated to the final word. When he thinks nobody will notice he’ll historically impersonate them because the forum architecture doesn’t forbid it – our esteemed Mr. Krebson is obviously not running a day care but he is aware of the issue. C’est la vie, I just find it churlish and call it out for what it is. He designs to run this forum via frequency and volume of opine.
We see this every few months on this forum. Both mealy and his aliases and JamminJ and his aliases are both trolls with low self esteem. Both need to get the last word in. Both have attitudes and accuse the other.
It’s not okay to use aliases even though its allowed. Just stick with one so people can know. At this point I don’t care about who is whom, I just read the content.
JamminReader now? Get a life dude.
Impressive trolling! My (actual) esteem is for interesting and verifiable information – and I don’t impersonate anyone or troll people just because we disagree on some concept or minor point.
That is the difference between myself and an impersonator who wants to be seen explaining things and talking down to people as if pontificating from on high, despite the obvious problem of not actually being omniscient.
Please direct all armchair psychoanalysis into the mirror where it can be usefully interpreted by potentially knowledgeable parties. I don’t mind disagreement. I also won’t pretend to be JamminJ or yourself should we find ourselves intellectually opposed. Only Brian will know based on email pattern matching, or more likely, nobody will care and JamminJ will continue to impersonate people they disagree with in the absence of a hard control on that, unfortunately not forthcoming.
That last JJ comment is a tacit admission.
Read it carefully for what it is.
Now JamminJ is impersonating SMH.
Period.
Brian can verify this, no one else.
This is the real mealy. Not the other guy.
Brian why won’t you defend me and my identity?
Brian is talented in figuring out who is lying but this is such low-lying fruit, it’s not even worth the stoop. Unfortunately.
It’s entirely distinct to use an alias vs impersonating an existing (or multiple existing) aliases of people you do not agree with to undermine their argument because the limitation of the platform allows for that. Personally I would verify at an intimate level and let our masqued phantom break himself on the rocks of reality, but it’s not worth the effort on Brian’s part. C’est la J vie.
How many times will you spam this forum?
You sound like you’ve gone off the paranoid deep end. Now you’re accusing me, and who knows how many others of being fake. I don’t take it personally though.
I’ve told you before to stop feeding the trolls lest you become one. You don’t need to have the final word. You’re trying to justify your use of aliases as if it was different. Just be you. If you’re posting as different names, then you don’t get to be outraged when someone uses that against you.
Instead, you let another troll get under your skin. You’ve now commented way more than JamminJ. You repeatedly say, c’est la vie, as if you aren’t bothered, but it has you angry and obsessed. Trolls will go away when you ignore them. JamminJ is no different.
Readership1, I’m actually not trolling here. Neither of us use real names and neither of us have trademarked names here. People are free to be anonymous here (despite his pleading with Brian to doxx people). I’m glad for you that you choose a single name and stick with it, but that’s not required and that’s not for everyone. If mealy uses other handles that’s just some random word, it’s not impersonation for others to use it because it’s not a real person’s identity. Just showing the absurdity of trying to claim an anonymous identity just for oneself.
Mealy started this first. It was pretty obvious that Criticality was mealy because he’s too cowardly to respond directly to my comment under his original name. Responding again with the same anonymous name shows that you should indeed just read the content and don’t worry so much about who is who.
I totally agree with you that If he changes his handle all the time, he gets what he deserves and gets responses from the same name. It would be better if nobody had names on here and we could let the content speak for itself.
I am actually very amused that he is now spamming and raging. I actually sat back and stopped commenting. And just laughing that he’s now accusing everyone of being me. I guess I’m living rent free in his mind right now.
He desperately is trying to come off as being indifferent, but his words show the reality, he is very triggered by all this. And yes, very paranoid that everybody here is me. I resolved to let him think whatever he wants, and not deny anything even when he’s wrong.
Ever seen an egomaniac troll admit that’s what they are doing, admit to impersonating people to discredit them?
Of course you haven’t. They don’t come clean, that’s anathema.
It’s been quiet on that front lately but the history of doing this for months and months is all there. Brian will have to step in unfortunately if this is going to end because J-insertnamehere-J is not going to suddenly grow up and stop trolling people who even slightly disagree via impersonation.
Mealy, spamming is a much worse offense than impersonation. Maybe that is why Mr. Krebs isn’t doing what you want. He has enough work keeping scammers, hate speech, and spammers off his site. He doesn’t need people complaining that someone stole an alias that never even belonged to you.
You seem to be under the false impression that anybody cares what alias someone is using. Looks like Mr. Krebs has already made a conscience decision to allow anonymous aliases here. So why are you wasting your energy staying up late at night and repeating the same thing for someone who is obvious getting kicks watching you suffer? Don’t bother trying to win a hollow victor of some admission of guilt. You don’t own any of your many aliases and have nothing to defend.
JamminJ, although it’s not against any specific rule here, it’s still a jerk move and abuses the intent of this public forum. I get that you are doing it out of spite for mealy’s supposed similar transgressions. But it still comes across as petty. “he started it” may be true but is a childish defense.
The actual content of your posts suggest you are better than this. Mealy, if you just use one name when responding to JamminJ, and JamminJ if you stop muddling the thread, you can go back to being productive contributors.
“Mealy, spamming is a much worse offense than impersonation.” Wrong, but he does both anyway.
Get well soon “reader” assuming you actually do that.
Narcissist versus a troll.
A troll knows he’s offensive and makes comments deliberately to get a reaction out of the other person.
A narcissist is self-absorbed with their own identity and takes offense at being impersonated.
Mealy, your vanity is exactly the reason you are attracting a troll. NOBODY CARES ABOUT YOUR ANONYMOUS IDENTITY HERE. This forum was not designed for people to have a persistent reputation to feed their ego.
Multiple user impersonation is a step more insidious in a security forum while also far less obvious to spot and deal with compared to any definition of actual spamming.
It’s not your job reader, let Brian do his.
There is no such thing as impersonating an anonymous post.
There is no login, there is no user account, no terms of service, mealy isn’t your real name, and anyone can use any name they want here.
You seem to think it’s a crime, a violation that Brian should care about, or somehow that you’ve got names trademarked here.
Brian deletes spam and scams here. But he values the freedom of speech that comes with anonymous comments. So again, NOBODY CARES ABOUT YOUR CLAIMS.
“Criticality” says what JJ was saying initially above, “mealy” repeats it.
Once each. It’s JJ’s argument and 180 degress from what I said here.
Userland can’t see the emails he supplied, but Krebs certainly can.
He’s forfeiting the goodwill and trust he purports to seek in the world.
If you think “use” == “develop”… then you are too deep in the weeds and don’t understand the topic.
You use what you choose. If you’re not qualified to judge whether your trust is misplaced in an unsecured project or repo, then you’re blindly trusting everything. That’s not a tenet of OSS.
Re-debunked, JamminJ.
Writing this comment on Firefox. Its Open Source right? I cannot verify its code. I assume someone is verifying its code. But I don’t know any of those people.
“All open source is the same candy crush I hear, therefore by picking any sing open source project’s implementation I can compare it to another open source project.” – Goddam troglodyte with Adobe Acrobat open.
Exactly right. I’d add there’s nothing stopping people from having their own trusted repos. Dupe all day, verify at night, but don’t wake up complaining that you “trusted the internet” because you grabbed something without looking expecting it to be perfectly sanitary, that’s insane. If anything this is a wakeup call to the big repos and loose orgs that use them loosely as they’re the ones who are going to have their reputations burned in laziness. There are existing ways to prevent all of this at each and every step. One misadministrated policy mishap != “OSS is flawed”
I think the problem is not open-source per se, but the large number of dependencies used by some open source projects. If you use 100% proprietary software, the developer of that software could introduce wiper code in an update, but at least you’re only trusting that one developer. Whereas if you are using software developed with Node.js, the standard library is small, which means that projects of any real complexity will have many, many dependencies. I think this is why we keep seeing these issues with Node.js and NPM packages, instead of with Python-developed code (Python has a large standard library, presumably with a solid code-review process). So between the extremes of proprietary and Node.js projects are projects developed with a small number of dependencies (e.g., web apps developed in Python using Django). Calling this a problem with “open source” in general seems reductionist – there are certain software ecosystems in which these problems are more prevalent.
“Now to some degree that’s good. Excessive trust in open source libraries and dependencies lets all sorts of supply chain hacks take place, but there’s a significant danger that we end up throwing the baby out with the bathwater on this”
I agree completely. We need a better way. Having this false dichotomy of either “verified trust” by auditing every line of code yourself, or “blind trust” where you have no excuses and deserve what you get… is just wrong. I think Open Source developers need to get paid more than just the inconsistent and meager donation system of today. I don’t know how it might look, but if you pay them well, they would be willing to sign contracts that stipulate their efforts to be secure, timely and free of protestware.
A better way exists already and you’re oblivious to that. Stop impersonating, get well soon.
What’s your better way?
Impersonating people and mansplaining instead of actual development / verification.
I call it the JamminJ method.
Stop impersonating and we’ll discuss it, otherwise you’ll be treated as a pure troll. Period.
Google it per the specificity of your masquerade, J the non-dev.
Selective focus, omitting any denial.
Hey Ethan looks like we share the same hacker, they did a really good job for me too, helping me gain access to my partner’s phone without physical contact
That’s wonderful, they were able to help me increase my credit score and you can’t imagine how happy I was
advisories banners related with war Russia / Ukraine in many web pages simply block with browser plugins blacklist.
Gee, libertarians not understanding the concept of societal or communal trust and being so willing to erode it? What a surprise! Imagine if your people began developing food that could somehow tried to poison you based on your nationality. Imagine if your car tries to detect if it considers you an enemy and explodes. Imagine if this technology was developed by careless, sloppy, and overpaid manchildren with no restraint.
The problem is that they’re underpaid, or not being paid at all. These are developers working hat in hand for donations. Ever tried talking to an open source dev about a complaint. They get uppity. Rightly so, they aren’t getting paid for this. They are often developing in their free time.
A far as many of them are concerned, it’s their creative works. Their art. And if they want to decide that politics are important to them, they’ll do want they want.
So who trusted them to do otherwise and why individually so?
What relies on what and why?
Hilariously or not, the lack of positive comment attribution on this site undermines a faithful discussion of larger open source vulnerability to imposter attacks at any misconfigured link in the distribution chain.
Shout out to “researcher” (although NOT developer?) J2thaJ for the “discovery” and oft-repeated POC, but really you need to stop pretending to be other people just because it’s so dang trivial. Your style is E N T I R E L Y distinct and your argument diametrically opposed from those you are impersonating, it’s rather silly. We could discuss hypothetical vulns inherent in open source share libraries here instead of the obvious one you repeatedly exploit to avoid risking all that e-narcisism. It’s no more worth our time than Brians but I’d expect we’re wasting it in equal micro-measure by being forced to investigate your misbehavior when people disagree with your posits of varying to dubious quality. Some of what you say is absolutely correct and concise. It’s the rest we need to be concerned about, and I don’t claim to demarcate that line myself. Nor will I impersonate you, I think your own ideas being represented by yourself makes all the sense in the world instead of trying to superimpose my name on yours, or vice versa. Let’s stop being small dogs and be small people, eh?
”
How many times will you spam this forum?
You sound like you’ve gone off the paranoid deep end. Now you’re accusing me, and who knows how many others of being fake. I don’t take it personally though.
I’ve told you before to stop feeding the trolls lest you become one. You don’t need to have the final word. You’re trying to justify your use of aliases as if it was different. Just be you. If you’re posting as different names, then you don’t get to be outraged when someone uses that against you.
Instead, you let another troll get under your skin. You’ve now commented way more than JamminJ. You repeatedly say, c’est la vie, as if you aren’t bothered, but it has you angry and obsessed. Trolls will go away when you ignore them. JamminJ is no different.
”
— Readership1
Readership1, neither of us use real names and neither of us have trademarked names here. People are free to be anonymous here (despite his pleading with Brian to doxx people). I’m glad for you that you choose a single name and stick with it, but that’s not required and that’s not for everyone. If mealy uses other handles that’s just some random word, it’s not impersonation for others to use it because it’s not a real person’s identity. Just showing the absurdity of trying to claim an anonymous identity just for oneself.
Mealy started this first. It was pretty obvious that Criticality was mealy because he’s too cowardly to respond directly to my comment under his original name. Responding again with the same anonymous name shows that you should indeed just read the content and don’t worry so much about who is who.
I totally agree with you that If he changes his handle all the time, he gets what he deserves and gets responses from the same name. It would be better if nobody had names on here and we could let the content speak for itself.
I am actually very amused that he is now spamming and raging. I actually sat back and stopped commenting. And just laughing that he’s now accusing everyone of being me. I guess I’m living rent free in his mind right now.
He desperately is trying to come off as being indifferent, but his words show the reality, he is very triggered by all this. And yes, very paranoid that everybody here is me. I resolved to let him think whatever he wants, and not deny anything even when he’s wrong.
You need to stop impersonating people if you wish to have discussions with them.
Brian knows the truth if he cares to JJ.
Thanks for using your own nick this time, that’s precious.
I see even bigger problem here – people engaging in clearly CRIMINAL activity not being afraid of LAW prosecution just because social media hypes this as “positive” , or “hacktivism”. I don’t see any authorities stepping in to press charges against this person pushing malicious code in the open with malicious intent.
Define the crime. The code in this case is claimed to be non-destructive. If that’s true, unless there is some really fine grained contract they’re violating (possible, civil law and not criminal at that stage) it’s just a flawed work product and would likely be resolved between the employer and employee. They could sue, depending. CFAA probably isn’t applicable if they were authorized to work on the code and it doesn’t destroy or steal resources. There are actual destructive malware campaigns going on at the same time which would and do get such attention regardless of what social media says.
…I can’t imagine it’s criminal…it’s free software not warranted to be fit for anything and used entirely at the end user’s acknowledgement…
…no ransom demand, no erasing data, etc., etc…
…now the s/w that somehow detects the source of the IP address in Russia and then wipes data…
…but again see my first point…
How did you come up with it not erasing data? that was the explicit purpose of the malicious code, to overwrite data with emojis.
Its criminal to write data wiping malware, and then attempt to push it to thousands of systems via a “trusted” mechanism.
“Not fit for a particular purpose” does not give the write to push malicious code which damages the system.
…if you read the article and my comment I clearly differentiated between protest messages and wiping software…
…the latter is criminal, the former is not…
…as to “not fit for a particular purpose”, that’s a well known concept that I’ll let you find out about…
…and the software is free and includes no warranty…
…in other words, one gets what one pays for, protest message and all…
“…NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION…”
https://opensource.org/licenses/GPL-2.0
Incredible how much the battlefield has changed over the years! Thanks again for another informative well written post.
In the previous few days, a few famous NodeJS libraries had been “weaponized” to wipe the customers documents if the IP-primarily based absolutely geo-area shows the individual is from Russia or Belarus.
The problem is that such geo-vicinity is not normally a hundred% correct, as a result going earlier, particularly the ones living in nearby worldwide places (which might be geo-placed with the useful resource of mistake as in one of the focused countries), have to probably pay greater care to the modern-day dependencies one offers, or updates, to his software software program.
Moreover, given the cutting-edge geo-political landscape, given the war and sanctions, it’s no longer unrealistic to recall that the opportunity thing may additionally begin doing the identical and goal clients from western international places…
How many times does “the problem with x is …” occur in this thread, or any thread.
This reveals two problems:
1. there is never just one problem
2. you likely don’t don’t know what it is.
Bravo! Brian on exposing the Russian crook business!
Thanks for another informative post.
It’s scary how battlefield has changed over this few years. I wonder how it gonna be in next few years with the web 3 and the Blockchain technology.
There are actual destructive malware campaigns going on at the same time which would and do get such attention regardless of what social media says.
This is why it’s important to leadership to know how to deal with such problems in the near future.
I think open source should be renamed to open malware
And closed source software should be renamed “1001 hidden 0-day vulnerabilities”.
I got something new here! This post increase my knowledge.
I wish this war will be stop soon so the people who are suffering from this war get some relaxed.
I’m curious as to why you decided to exclude this guy’s real name, Brandon Nozaki Miller , from the article when its easily available and announced on his GitHub profile.
This guy pushed malware which negatively impacted innocent people, including those who are against the war in Ukraine. All based upon IP geolocation which could easily be inaccurate, or someone who owns infra in a country, or someone using a VPN, etc, not to mention the reputational damage to related projects/open source. Should be covered just like any of the other Ner’Do Well’s that you cover here, especially when he’s publicly professed his information.
This guy destroyed his reputation as a developer in 15 minutes.