AMLBot, a service that helps businesses avoid transacting with cryptocurrency wallets that have been sanctioned for cybercrime activity, said an investigation published by KrebsOnSecurity last year helped it shut down three dark web services that secretly resold its technology to help cybercrooks avoid detection by anti-money laundering systems.
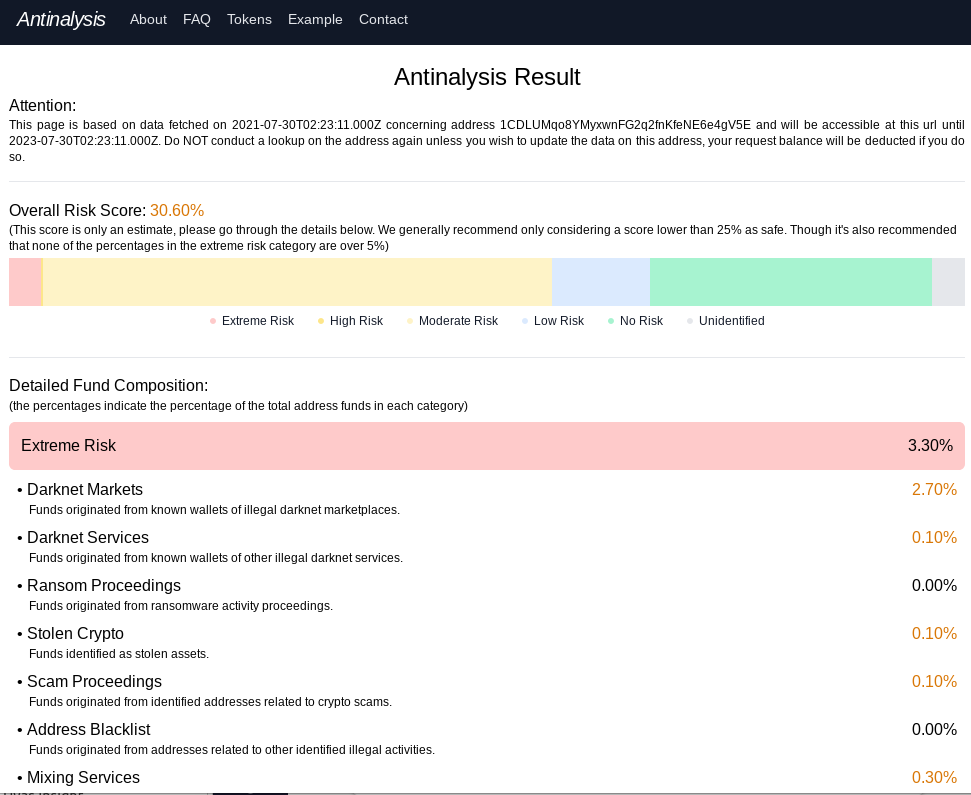
Antinalysis, as it existed in 2021.
In August 2021, KrebsOnSecurity published “New Anti Anti-Money Laundering Services for Crooks,” which examined Antinalysis, a service marketed on cybercrime forums that purported to offer a glimpse of how one’s payment activity might be flagged by law enforcement agencies and private companies that track and trace cryptocurrency transactions.
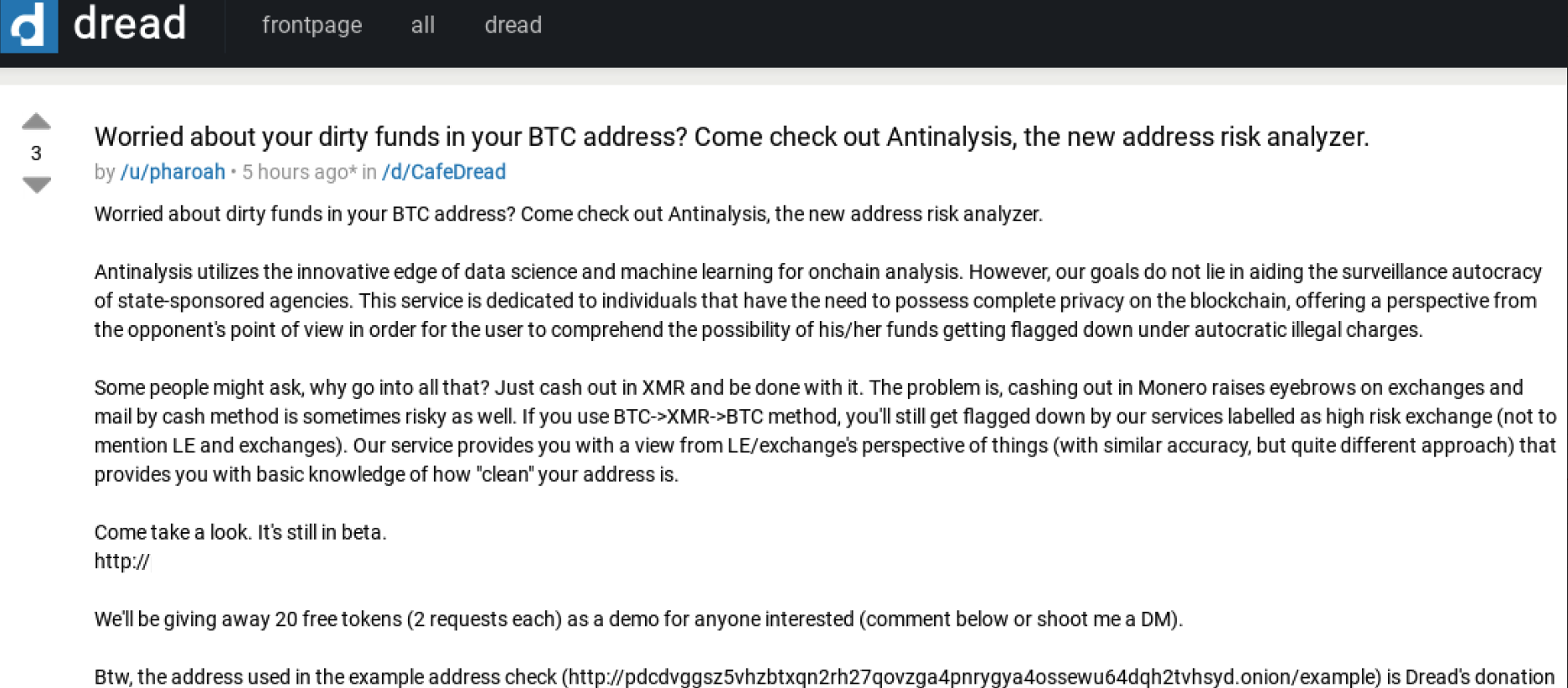
“Worried about dirty funds in your BTC address? Come check out Antinalysis, the new address risk analyzer,” read the service’s opening announcement. “This service is dedicated to individuals that have the need to possess complete privacy on the blockchain, offering a perspective from the opponent’s point of view in order for the user to comprehend the possibility of his/her funds getting flagged down under autocratic illegal charges.”
Antinalysis allows free lookups, but anyone wishing to conduct bulk look-ups has to pay at least USD $3, with a minimum $30 purchase. Other plans go for as high as $6,000 for 5,000 requests. Nick Bax, a security researcher who specializes in tracing cryptocurrency transactions, told KrebsOnSecurity at the time that Antinalysis was likely a clone of AMLBot because the two services generated near-identical results.
AMLBot shut down Antinalysis’s access just hours after last year’s story went live. However, Antinalysis[.]org remains online and accepting requests, as does the service’s Tor-based domain, and it is unclear how those services are sourcing their information.
AMLBot spokesperson Polina Smoliar said the company undertook a thorough review after that discovery, and in the process found two other services similar to Antinalysis that were reselling their application programming interface (API) access to cybercrooks.
Smoliar said that following the revelations about Antinalysis, AMLBot audited its entire client base, and implemented the ability to provide APIs only after a contract is signed and the client has been fully audited. AMLBot said it also instituted 24/7 monitoring of all client transactions.
“As a result of these actions, two more services with the name AML (the same as AMLBot has) were found to be involved in fraudulent schemes,” Smoliar said. “Information about the fraudsters was also sent to key market participants, and their transaction data was added to the tracking database to better combat money laundering.”
The Antinalysis homepage and chatter on the cybercrime forums indicates the service was created by a group of coders known as the Incognito Team. Tom Robinson, co-founder of the blockchain intelligence firm Elliptic, said the creator of Antinalysis is also one of the developers of Incognito Market, a darknet marketplace specializing in the sale of narcotics.
“Incognito was launched in late 2020, and accepts payments in both Bitcoin and Monero, a cryptoasset offering heightened anonymity,” Robinson said. “The launch of Antinalysis likely reflects the difficulties faced by the market and its vendors in cashing out their Bitcoin proceeds.”




And a naughty government (which ours is beginning to resemble) could use the same tool to block crypto transactions by their political opponents or any consumer who is engaging in a business they do not like. For example, donations to WalkAway, and buying a MyPillow.
Rather like the Patriot Act has been misapplied.
AMLbot blocks nothing. Their clients can voluntarily decline to transact with those on the list, in much the same way you have voluntarily declined to read and comprehend the article.
Thanks, Brian!
Just goes to show there is no service that can’t be repurposed to thwart its mission!
APIs will be the interface to the death of us all.
Sell your soul wisely.
It’s very hard to figure out what you’re on about here, Brian. This seems to be about EULA enforcement and not AML enforcement.
You really don’t see how it’s connected here?
Any customer of AMLBot could be a “cybercrook” using it to avoid detection by anti-money laundering systems, and the mention of “cybercrooks” here obfuscates the salient matter – the objectionable activity apparently is reselling API access (or brokering it), rather than the character of the entities making the queries.
Hence the crackdown on the API customer base, right?
The real launderers would be customers of people leveraging the API
(themselves in violation of a EULA++) and hopefully also detectable
after the fact. That last part is a hope, not a fact.
@edward
Ours(U.S.?) is “beginning” to resemble a naughty government? Where have you been?! It’s been naughty for most of its time.
He means US looks more like China every day
That’s retarded to a point and that point is in China.
Ah yes, and this applies to “official” money as well? Any fiat ever involved in any illegal activity is void, correct?
I owe my recently boosted excellent credit to Credit Boost Helpers. I used many popular credit repair shops including credit saints and Lexington Law. CBH were amazing ! They left no stone unturned and sure my credit score rose from 538 to 791 . I’m so grateful for the existence of such great help as CBH.