The ransomware group LockBit told officials with Fulton County, Ga. they could expect to see their internal documents published online this morning unless the county paid a ransom demand. LockBit removed Fulton County’s listing from its victim shaming website this morning, claiming the county had paid. But county officials said they did not pay, nor did anyone make payment on their behalf. Security experts say LockBit was likely bluffing and probably lost most of the data when the gang’s servers were seized this month by U.S. and U.K. law enforcement.
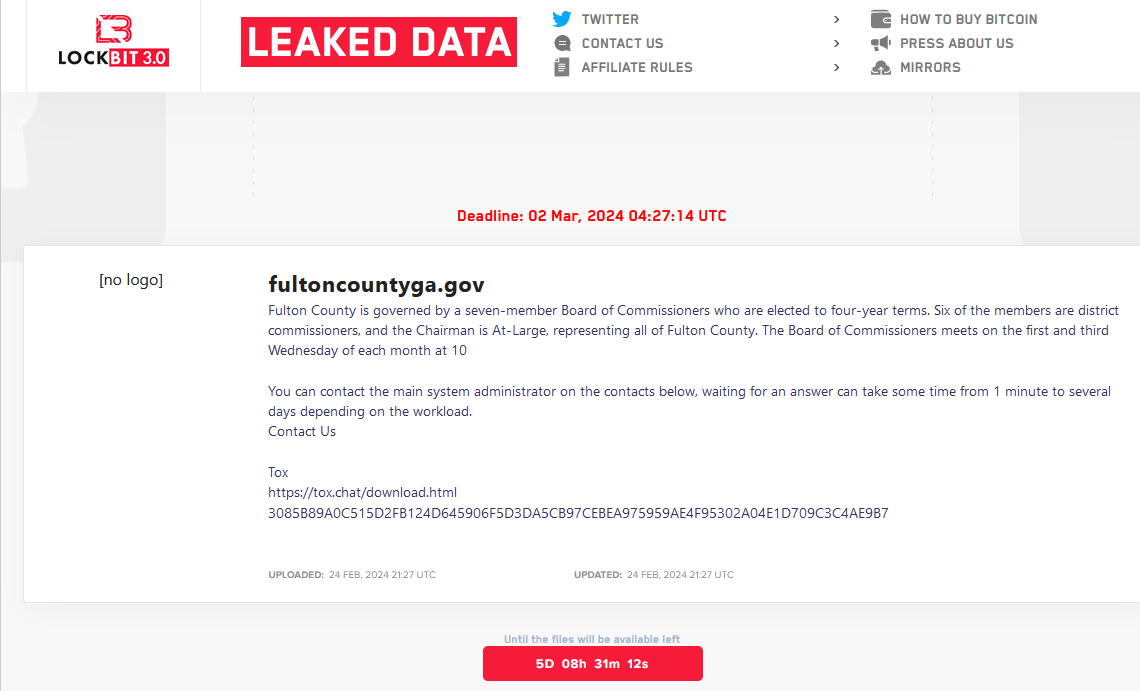
The LockBit website included a countdown timer until the promised release of data stolen from Fulton County, Ga. LockBit would later move this deadline up to Feb. 29, 2024.
LockBit listed Fulton County as a victim on Feb. 13, saying that unless it was paid a ransom the group would publish files stolen in a breach at the county last month. That attack disrupted county phones, Internet access and even their court system. LockBit leaked a small number of the county’s files as a teaser, which appeared to include sensitive and sealed court records in current and past criminal trials.
On Feb. 16, Fulton County’s entry — along with a countdown timer until the data would be published — was removed from the LockBit website without explanation. The leader of LockBit told KrebsOnSecurity this was because Fulton County officials had engaged in last-minute negotiations with the group.
But on Feb. 19, investigators with the FBI and the U.K.’s National Crime Agency (NCA) took over LockBit’s online infrastructure, replacing the group’s homepage with a seizure notice and links to LockBit ransomware decryption tools.
In a press briefing on Feb. 20, Fulton County Commission Chairman Robb Pitts told reporters the county did not pay a ransom demand, noting that the board “could not in good conscience use Fulton County taxpayer funds to make a payment.”
Three days later, LockBit reemerged with new domains on the dark web, and with Fulton County listed among a half-dozen other victims whose data was about to be leaked if they refused to pay. As it does with all victims, LockBit assigned Fulton County a countdown timer, saying officials had until late in the evening on March 1 until their data was published.
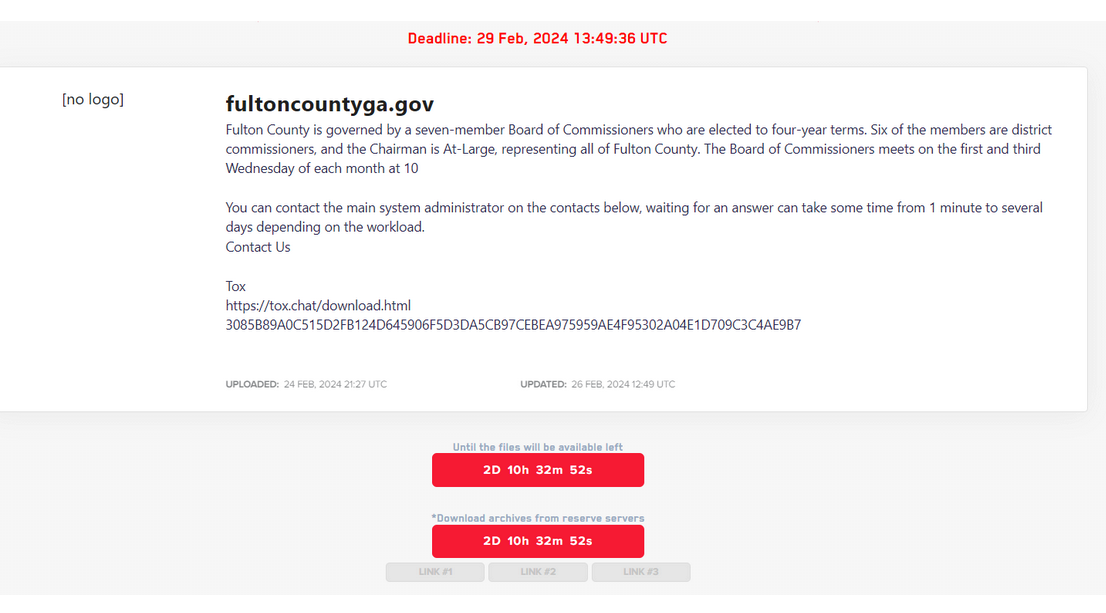
LockBit revised its deadline for Fulton County to Feb. 29.
LockBit soon moved up the deadline to the morning of Feb. 29. As Fulton County’s LockBit timer was counting down to zero this morning, its listing disappeared from LockBit’s site. LockBit’s leader and spokesperson, who goes by the handle “LockBitSupp,” told KrebsOnSecurity today that Fulton County’s data disappeared from their site because county officials paid a ransom.
“Fulton paid,” LockBitSupp said. When asked for evidence of payment, LockBitSupp claimed. “The proof is that we deleted their data and did not publish it.”
But at a press conference today, Fulton County Chairman Robb Pitts said the county does not know why its data was removed from LockBit’s site.
“As I stand here at 4:08 p.m., we are not aware of any data being released today so far,” Pitts said. “That does not mean the threat is over. They could release whatever data they have at any time. We have no control over that. We have not paid any ransom. Nor has any ransom been paid on our behalf.”
Brett Callow, a threat analyst with the security firm Emsisoft, said LockBit likely lost all of the victim data it stole before the FBI/NCA seizure, and that it has been trying madly since then to save face within the cybercrime community.
“I think it was a case of them trying to convince their affiliates that they were still in good shape,” Callow said of LockBit’s recent activities. “I strongly suspect this will be the end of the LockBit brand.”
Others have come to a similar conclusion. The security firm RedSense posted an analysis to Twitter/X that after the takedown, LockBit published several “new” victim profiles for companies that it had listed weeks earlier on its victim shaming site. Those victim firms — a healthcare provider and major securities lending platform — also were unceremoniously removed from LockBit’s new shaming website, despite LockBit claiming their data would be leaked.
“We are 99% sure the rest of their ‘new victims’ are also fake claims (old data for new breaches),” RedSense posted. “So the best thing for them to do would be to delete all other entries from their blog and stop defrauding honest people.”
Callow said there certainly have been plenty of cases in the past where ransomware gangs exaggerated their plunder from a victim organization. But this time feels different, he said.
“It is a bit unusual,” Callow said. “This is about trying to still affiliates’ nerves, and saying, ‘All is well, we weren’t as badly compromised as law enforcement suggested.’ But I think you’d have to be a fool to work with an organization that has been so thoroughly hacked as LockBit has.”




So.. not to give away any secrets or anything.. but nobody had a flash drive or external drive on them?
One of the reasons LockBit persisted for so long, was they have up until now implemented reasonably good Operational Security. This fell apart when US and UK authorities exploited a php function on LockBits systems and gained access and control of their stolen data.
When a bad actor penetrates and exfiltrates data, they perform this obviously from a remote location, routing it round the world repeatedly to destination/s they control ie; cloud, data centre or bulletproof servers, but which they rarely have local access to. They never route it back to themselves at their home location as that leaves a trail and dramatically increases their chances of being caught and convicted with evidence in their possession.
I’d safely assume they do not have a local copy of said data and their gig is over.
Good riddance. Last thing we need is another nothing-burger interrupting Trump prosecutions.
Inb4 all the MAGAts cry “DEEP STATE” on this one, too.
Wow…
TDS much bro? You sound like a 5 year old ranting about popsicles. This article has nothing to do with Trump or Biden so let it go
Scammer admitted he was pro-drump. Trump denial syndrome.
It has EVERYTHING to do with politics so get off your high horse. No one made you ruler of anything.
LOL that is so contradictory I had to laugh out loud. Saying if they released data/corruption evidence it would be Nothing, while saying it would Interrupt a prosecution about political corruption, then crying that there is no corruption. OMG pick a lane.
awe, you’re admitting that none of you “wokesters” have the skills for something like this? guess not when you major in crap like gender studies, basket weaving, how to establish safe places, etc.
This is another case of a public entity not having enough of a priority for security, not enough priority for that work force, not enough of a budget for that function, not enough testing of its security protocols, software and expertise. In the corporate realm, if the top computer security official is not reporting directly to the CEO, the organization has not adequately prioritized that issue. Courts get no passes. Their legislative funders should be paying a lot of attention to this.
I think it is possible that someone has paid the highest ransom and has more precious documents that could incriminate them.
This is plausible but more likely, the LockBit team likely was nation state sanctioned and gave copies of their data haul to their patron.
They likely were bluffing to make a last score and failed. But I don’t doubt a copy of their data is still in the hands of a malicious enemy.
Whether it will be released depends on if they can do more harm by going public or first providing it to a valued member of their transnational criminal organization desperately trying to cheat to beat the justice system in GA.
Interesting…yeah, the local government may not have much to loose either way. But the high profile people that may be implicated? That’s another story. Hypothetically also why proof of payment couldn’t be furnished like normal too.
I wish they WOULD publish what they have. I’m curious to know which trial documents have been sealed! How many MORE innocent people fell victim to Fani Willis’s crooked BS?
Why not just leave your message in Russian?
Feds got your tongue? Or just your vertical business?
You are a brainwashed magat idiot. Trump magats are the dumbest creatures ever to walk this planet.
Who brainwashed you?
It has EVERYTHING to do with politics so get off your high horse. No one made you ruler of anything.
That you would believe anything other than what you want to calls into question any credibility one might assume you pocess by your presence responding to this report.
Trump paid it. He doesn’t want the public to know his secret lies. He paid with election money and pillow guy idiot paid some too out of his business funds.
all you gang/party members are nuts. Political gangs should be banned in the US as organized crime. and make people run on their own merits. I so sick of the two gangs keeping the country stuck in stupid drama to keep themselves in the wealth.
TDS stronger than ever.. I wasn’t expecting to see raving lunatics here but I guess they have become inescapable. It’s like going back in time to my terms and reading posts on forums me and my fellow children would make lol.
Lockbit may be dead as lockbit but assuming the couple of people who “worked” there that actually had any skills are still roaming free they will just reform under a new name and continue on until caught. There is lots of money in selling tools, sure not necessarily as much as there is in bribing companies to pay ransom but also not an insignificant amount.
Id really like to see how lockbits day to day went and the structure they operated under. I didn’t pay much attention to them and what they did but I knew of them and how big they were… Did they mess with this County then get their lunch eaten by the FBI (and others of course) or was there other US Govt entities attacked by them beforehand? Be more funny if it was 1 then done. And on that day chubs mcgee knew he has dun goofed.
Now I’m going to fat some random cat forum and enjoy more lunatic ranting while I have my coffee.
most of the gangs – are a couple idiot (all greedy leaches on society) leaders and everyone else is a contractor – if they can keep their identity hidden. One coder can be a dozen or one person in multiple groups. Could even be an FBI/FSB/CCP commander running the top positions to guide international behaviors. Although I think its 99% greedy idiots that lack respect for anyone, trying to get enough money for hookers and drugs, since they are unlikable as a person – they have to pay for people to pretend to like them. Then we all fall down dead. meh.
wikipedia.org/wiki/Lockbit – “LockBit was the world’s most prolific ransomware in 2022. It was estimated in early 2023 to be responsible for 44% of all ransomware incidents globally.”
Cry about someone mentioning Trump by… mentioning Trump again, bravo that.
I’m sure the opine was “otherwise” well researched and sourced though. /s
since when has anyone paid bribes to a party they’re extorting? might be high time to down scale the micro dosing and nootropez, cuhd?
I I got the SanDisk cruze 4 GB
Fulton County Commission Chairman Robb Pitts told reporters the county did not pay a ransom demand, noting that the board “could not in good conscience use Fulton County taxpayer funds to make a payment.”
-It may be nothing but note specific verbage, “the county did not pay” + “could not use taxpayer funds.”
That doesn’t say “nobody paid” last minute in direct service of those interests w/ other funds.
Wonder if we’ll ever know.
You all do know lockbit 3.0 is up an running right… If they released the info they would lose the credibility of businesses they attack in the future. For a succesful buisness model, when the “customer” or in this case victim pays, they get what they pay for. When they don’t it is released.
Lockbit has stated that they will be going after .gov infrastructure. It’s gonna get spicy.
You realize that the victim is insisting that they didn’t pay, right? That puts lockbit into doubt.
…and you actually believe that a criminal’s statement about what they will or will not do is worth anything in this context?