The recent mass-theft of authentication tokens from Salesloft, whose AI chatbot is used by a broad swath of corporate America to convert customer interaction into Salesforce leads, has left many companies racing to invalidate the stolen credentials before hackers can exploit them. Now Google warns the breach goes far beyond access to Salesforce data, noting the hackers responsible also stole valid authentication tokens for hundreds of online services that customers can integrate with Salesloft, including Slack, Google Workspace, Amazon S3, Microsoft Azure, and OpenAI.
Salesloft says its products are trusted by 5,000+ customers. Some of the bigger names are visible on the company’s homepage.
Salesloft disclosed on August 20 that, “Today, we detected a security issue in the Drift application,” referring to the technology that powers an AI chatbot used by so many corporate websites. The alert urged customers to re-authenticate the connection between the Drift and Salesforce apps to invalidate their existing authentication tokens, but it said nothing then to indicate those tokens had already been stolen.
On August 26, the Google Threat Intelligence Group (GTIG) warned that unidentified hackers tracked as UNC6395 used the access tokens stolen from Salesloft to siphon large amounts of data from numerous corporate Salesforce instances. Google said the data theft began as early as Aug. 8, 2025 and lasted through at least Aug. 18, 2025, and that the incident did not involve any vulnerability in the Salesforce platform.
Google said the attackers have been sifting through the massive data haul for credential materials such as AWS keys, VPN credentials, and credentials to the cloud storage provider Snowflake.
“If successful, the right credentials could allow them to further compromise victim and client environments, as well as pivot to the victim’s clients or partner environments,” the GTIG report stated.
The GTIG updated its advisory on August 28 to acknowledge the attackers used the stolen tokens to access email from “a very small number of Google Workstation accounts” that were specially configured to integrate with Salesloft. More importantly, it warned organizations to immediately invalidate all tokens stored in or connected to their Salesloft integrations — regardless of the third-party service in question.
“Given GTIG’s observations of data exfiltration associated with the campaign, organizations using Salesloft Drift to integrate with third-party platforms (including but not limited to Salesforce) should consider their data compromised and are urged to take immediate remediation steps,” Google advised.
On August 28, Salesforce blocked Drift from integrating with its platform, and with its productivity platforms Slack and Pardot.
The Salesloft incident comes on the heels of a broad social engineering campaign that used voice phishing to trick targets into connecting a malicious app to their organization’s Salesforce portal. That campaign led to data breaches and extortion attacks affecting a number of companies including Adidas, Allianz Life and Qantas.
On August 5, Google disclosed that one of its corporate Salesforce instances was compromised by the attackers, which the GTIG has dubbed UNC6040 (“UNC” is Google’s shorthand for “uncategorized threat group”). Google said the extortionists consistently claimed to be the threat group ShinyHunters, and that the group appeared to be preparing to escalate its extortion attacks by launching a data leak site.
ShinyHunters is an amorphous threat group known for using social engineering to break into cloud platforms and third-party IT providers, and for posting dozens of stolen databases to cybercrime communities like the now-defunct Breachforums.
The ShinyHunters brand dates back to 2020, and the group has been credited with or taken responsibility for dozens of data leaks that exposed hundreds of millions of breached records. The group’s member roster is thought to be somewhat fluid, drawing mainly from active denizens of the Com, a mostly English-language cybercrime community scattered across an ocean of Telegram and Discord servers.
Recorded Future’s Alan Liska told Bleeping Computer that the overlap in the “tools, techniques and procedures” used by ShinyHunters and the Scattered Spider extortion group likely indicate some crossover between the two groups.
To muddy the waters even further, on August 28 a Telegram channel that now has nearly 40,000 subscribers was launched under the intentionally confusing banner “Scattered LAPSUS$ Hunters 4.0,” wherein participants have repeatedly claimed responsibility for the Salesloft hack without actually sharing any details to prove their claims.
The Telegram group has been trying to attract media attention by threatening security researchers at Google and other firms. It also is using the channel’s sudden popularity to promote a new cybercrime forum called “Breachstars,” which they claim will soon host data stolen from victim companies who refuse to negotiate a ransom payment.
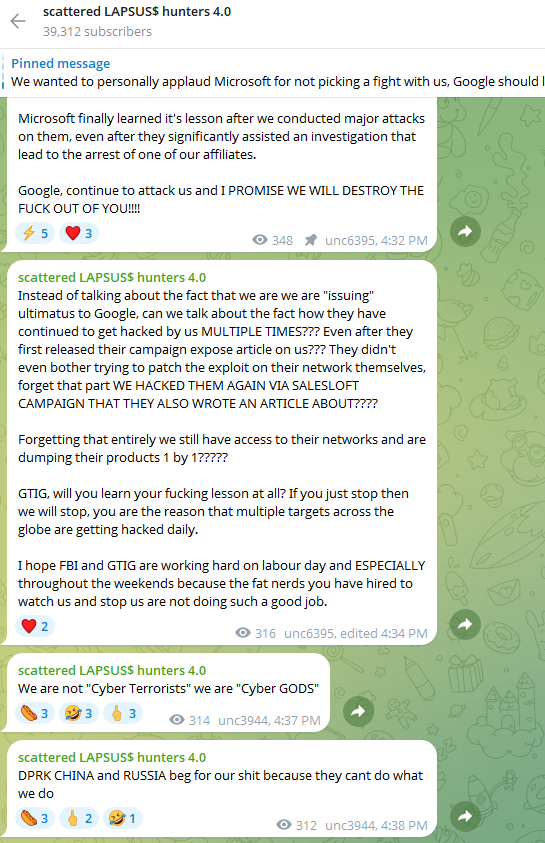
The “Scattered Lapsus$ Hunters 4.0” channel on Telegram now has roughly 40,000 subscribers.
But Austin Larsen, a principal threat analyst at Google’s threat intelligence group, said there is no compelling evidence to attribute the Salesloft activity to ShinyHunters or to other known groups at this time.
“Their understanding of the incident seems to come from public reporting alone,” Larsen told KrebsOnSecurity, referring to the most active participants in the Scattered LAPSUS$ Hunters 4.0 Telegram channel.
Joshua Wright, a senior technical director at Counter Hack, is credited with coining the term “authorization sprawl” to describe one key reason that social engineering attacks from groups like Scattered Spider and ShinyHunters so often succeed: They abuse legitimate user access tokens to move seamlessly between on-premises and cloud systems.
Wright said this type of attack chain often goes undetected because the attacker sticks to the resources and access already allocated to the user.
“Instead of the conventional chain of initial access, privilege escalation and endpoint bypass, these threat actors are using centralized identity platforms that offer single sign-on (SSO) and integrated authentication and authorization schemes,” Wright wrote in a June 2025 column. “Rather than creating custom malware, attackers use the resources already available to them as authorized users.”
It remains unclear exactly how the attackers gained access to all Salesloft Drift authentication tokens. Salesloft announced on August 27 that it hired Mandiant, Google Cloud’s incident response division, to investigate the root cause(s).
“We are working with Salesloft Drift to investigate the root cause of what occurred and then it’ll be up to them to publish that,” Mandiant Consulting CTO Charles Carmakal told Cyberscoop. “There will be a lot more tomorrow, and the next day, and the next day.”




“Scattered-typhoon sandworm shiny-fancy-cozy oceanlotus sidewinder-Lazeru$$$”
We are legion, fear our chatbots!
ooouuuu daddy shinyhunters
shiny was apart of the insecurity discord with all the other guys targeting MSP via bec he goes by “Timothy” idk how the FBI hasnt arrested him already dude is doxed asf
heyyy im waifus ex gf :3, i just wanted to drop by and comment on here that my daddy shinyhunters is #RIU and #INVINCIBLE
he is not dumb like my dumb ex bf waifu!!! allison nixon can do what ever she wants but she IS NOT GETTING MY MANZZZZZ!!
#shinyhunters #theshadowbrokers
:3 >w<
ShinyHunters is MLT now its so obvious lmao
So I will explain the ShinyHunters brand group
it all started on skype, with yukari AKA theshadowbrokers who hacked the NSA and leaked a bunch of NSA exploits.
shinyhunters used to be known as shad0w in TSB, then moved onto become gnosticplayers and thedarkoverlord, after that era it formed shinyhunters group, ever since then it has incorporated and inherited multiple groups such as lapsus$ and scattered spider, h4ckth3pl4n3t, ac1db1tch3z, and etc
everyone is just ignoring the fact that the same or similar group of people since earliy/mid 2010s have been doing this till now.
shinyhunters past alias:
FMX nvcman kuroish yukari w0ne kms MLT LS vinnytroia vincenzotroia etc
The “supergroup” known as SCATTERED LAPSUS$ HUNTERS consists of Scattered Spider, LAPSUS$, and ShinyHunters.
This all began with LAPSUS$ and it will end with LAPSUS$. The legacy continues on from Snowflake. We saw mostly everyone in Snowflake campaign get arrested EXCEPT ShinyHunters. That is very odd in my opinion.
How come this indiviual or group or what ever always seems to survive multiple FBI field days? Since the beginning of this Salesforce campaign coverage, a lot of journalists and researchers have vouched for the identity of ShinyHunters, saying it’s the same person they spoke to last year as well. It’s very odd that the government(s) seem to always arrest the wrong individual who they accuse of being the ring leader of ShinyHunters.
It happens because Shiny has Epstein Files as leverage on feds.
No wonder they’re all quitting in protest of something!
Dee Deedee…….
unc3944 stop edging chanel please