Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code.
Microsoft said in a blog post today it identified more than 200 organizations and 5,000 consumer devices that were caught up in a stealthy but remarkably simple spying network built by a Russia-backed threat actor known as “Forest Blizzard.”

How targeted DNS requests were redirected at the router. Image: Black Lotus Labs.
Also known as APT28 and Fancy Bear, Forest Blizzard is attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). APT 28 famously compromised the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016 in an attempt to interfere with the U.S. presidential election.
Researchers at Black Lotus Labs, a security division of the Internet backbone provider Lumen, found that at the peak of its activity in December 2025, Forest Blizzard’s surveillance dragnet ensnared more than 18,000 Internet routers that were mostly unsupported, end-of-life routers, or else far behind on security updates. A new report from Lumen says the hackers primarily targeted government agencies—including ministries of foreign affairs, law enforcement, and third-party email providers.
Black Lotus Security Engineer Ryan English said the GRU hackers did not need to install malware on the targeted routers, which were mainly older Mikrotik and TP-Link devices marketed to the Small Office/Home Office (SOHO) market. Instead, they used known vulnerabilities to modify the Domain Name System (DNS) settings of the routers to include DNS servers controlled by the hackers.
As the U.K.’s National Cyber Security Centre (NCSC) notes in a new advisory detailing how Russian cyber actors have been compromising routers, DNS is what allows individuals to reach websites by typing familiar addresses, instead of associated IP addresses. In a DNS hijacking attack, bad actors interfere with this process to covertly send users to malicious websites designed to steal login details or other sensitive information.
English said the routers attacked by Forest Blizzard were reconfigured to use DNS servers that pointed to a handful of virtual private servers controlled by the attackers. Importantly, the attackers could then propagate their malicious DNS settings to all users on the local network, and from that point forward intercept any OAuth authentication tokens transmitted by those users.
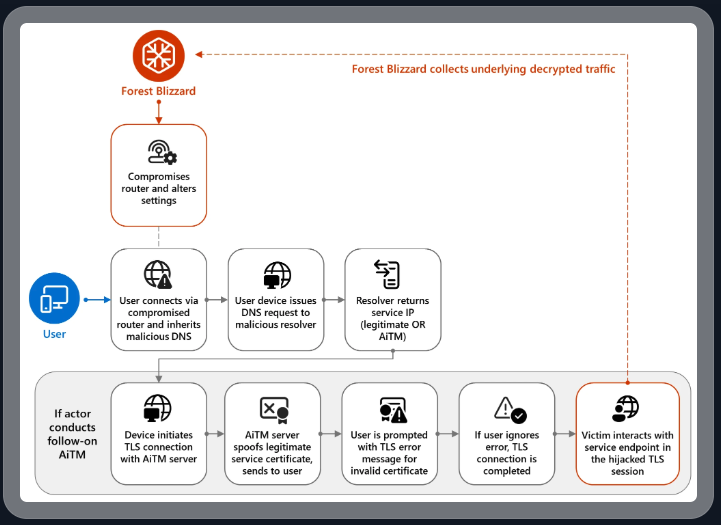
DNS hijacking through router compromise. Image: Microsoft.
Because those tokens are typically transmitted only after the user has successfully logged in and gone through multi-factor authentication, the attackers could gain direct access to victim accounts without ever having to phish each user’s credentials and/or one-time codes.
“Everyone is looking for some sophisticated malware to drop something on your mobile devices or something,” English said. “These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done.”
Microsoft refers to the Forest Blizzard activity as using DNS hijacking “to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains.” The software giant said while targeting SOHO devices isn’t a new tactic, this is the first time Microsoft has seen Forest Blizzard using “DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices.”
Black Lotus Labs engineer Danny Adamitis said it will be interesting to see how Forest Blizzard reacts to today’s flurry of attention to their espionage operation, noting that the group immediately switched up its tactics in response to a similar NCSC report (PDF) in August 2025. At the time, Forest Blizzard was using malware to control a far more targeted and smaller group of compromised routers. But Adamitis said the day after the NCSC report, the group quickly ditched the malware approach in favor of mass-altering the DNS settings on thousands of vulnerable routers.
“Before the last NCSC report came out they used this capability in very limited instances,” Adamitis told KrebsOnSecurity. “After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable.”
TP-Link was among the router makers facing a complete ban in the United States. But on March 23, the U.S. Federal Communications Commission (FCC) took a much broader approach, announcing it would no longer certify consumer-grade Internet routers that are produced outside of the United States.
The FCC warned that foreign-made routers had become an untenable national security threat, and that poorly-secured routers present “a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons.”
Experts have countered that few new consumer-grade routers would be available for purchase under this new FCC policy (besides maybe Musk’s Starlink satellite Internet routers, which are produced in Texas). The FCC says router makers can apply for a special “conditional approval” from the Department of War or Department of Homeland Security, and that the new policy does not affect any previously-purchased consumer-grade routers.




This is helpful information and worth passing on to folks who might be interested.
But… I wish there were clearer information about which routers are at risk.
I’m an individual and have no responsibility outside of my own home.
But if I were to send this to, say, a public official charged with securing their networks, what might I say? I’m “just an outsider” and *not to be trusted.* As is appropriate, given a zero trust environment.
Looking for a flash of brilliance here.
There are several links to other resources in the story, including this advisory from the NCSC, which lists very specifically which models they saw affected and why.
https://www.ncsc.gov.uk/news/apt28-exploit-routers-to-enable-dns-hijacking-operations
Now that I look at the NCSC’s advisory closer, it mainly lists specific TP-Link devices it saw as part of the botnet, as well as domains and IP addresses associated with the DNS botnet. But it doesn’t mention Microtik. Hopefully, someone else can weigh in on that front.
IOC list…
https://www.ncsc.gov.uk/news/apt28-exploit-routers-to-enable-dns-hijacking-operations#ioc
Since the attack relies on an invalid TLS certificate, it also requires that the user ignore warnings about an invalid certificate. Of course 98% of average users would authorize connections anyway.
I’m confused by the original Microsoft post. Shouldn’t Outlook domains be on HSTS preload or at least have HSTS from first visit? Since Microsoft has a whole lot of domains, this could have been an oversight.
For OAuth Authentication Tokens, as I understand it the authentication token part of the OAuth redirect is not transmitted when first creating an https connection. The website of the “Client” in OAuth terms could also use HSTS to defeat it.
Not that I would be fine with my router/DHCP to be compromised. But reliance on DNS in general is what https is supposed to get away from (as well as reliance on IP routing for the http connection itself). DNS server could be hardcoded to, say, 8.8.8.8 and a regular MitM attack could also still work. That is if the user clicks through bad certificate warnings and there is no HSTS.
I still do not understand. Suppose somebody compromised a router or a name server. Then the connection would go to a machine not intended to get that connection. Would not the TLS cert check fail because the server cannot prove to the client that it has the private key? Or is part of the story that the private keys were exfiltrated? Or that they are doing something sneaky such as micros0ft.com or micr0soft.com or microsoft.corn?
You are correct – the attack is relying on unskilled users ignoring the TLS error.
So, was this a case of:
1) Users being fooled by look-a-like websites (the spoofed DNS leads to a website that then redirects).
2) The DNS redirect being to a non-TLS’d site, with browsers not alerting
3) The routers, and user devices, being set up to trust a TLS root on the router, which was compromised.
4) The end points in question being over plain HTTP ?
Basically I’m struggling to understand how the DNS redirection lead to AiTM on TLS.
Ah, never mind, I see the clue is *only in the image*. So, it’s relying on a user bypassing a TLS error/warning.
Entire hack chain requires old, outdated and in fact deprecated SOHO routers in use in 2026.
Some % of people reflexively will click ‘continue’ no matter what the rest says because they don’t understand the warnings, terms/grammar/language/importance any of it, are intimidated or are just set to click-thru inherently – same folks using 10 years defunct SOHO routers who’ve never read the words firmware nor deprecated in their happy lives as disease vectors. Mosquito spawns that ripe shouldn’t be on the internet in 2026.
Vendors should have (mandated!) baked-in FW time bombs to FORCE updates/refurb on a 1-2 year window.
If it dies because it’s not updated in that window, it dies. Send it in get a new one. No unattended zombies!
I am not totally disagreeing with you, mealy, however I think you might be a wee bit heavyhanded with the scorn.
Ok but ‘scorn’ directed at whom? It’s a business artifact built on fail paradigms.
Internet facing products should be secured, up to date – or no internet access.
(This is going to piss off some Libertarian hardware-is-mine types, rightfully.)
No scorn; people who don’t know what firmware or deprecated mean as terms
should not be put in a position of being responsible for securing their devices.
They are not capable. That responsibility must fall on the mfr of the product
and be enforced one way or another. If it can be fixed it must be fixed.
Things will cost more. Not all products will make the cut. Que sera.
I meant scorn directed against generally uninteresting people somewhat ignorantly using ten year old hardware. Not like there are that many people going around hacking WiFi like decades ago. Their threats are more likely phishing or clicking the wrong link. Shrug. Not that it isn’t done. Not that a darpa employee would have any business doing that. But some random schmo, meh.
One of us is missing the gyst of what the other is saying, or both. I’m not ‘scorning’ the % of people who can’t be bothered nor care to attempt to understand how to basically secure their (personal) internet-touching devices, even though as my tone implies that is not an easily defensible position in the world of 2026 malware campaigns and frauds associated. If they’re not caring and the mfr’s aren’t being forced to care particularly and there’s no deadman’s switch that kicks them off the shared internet and into limp mode when they become deprecated or seriously vulnerable, the result is what we’re talking about – Frauds and campaigns that succeed, that go sideways into other systems and institutions and undermine otherwise-secured systems by association, and ruin people’s lives. Ignorance may be bliss but it shouldn’t be an excused vector. Because we can’t force-educate all internet users (oh, someday) before they get packets routed to them, the least we can do is force manufacturers to make more timely and obvious efforts to offer EXCLUSIVELY secure and up to date products, and be willing to eat some of the profit margin when they are shipping out replacement models to last-decade’s itinerant customer. But even random schmo has a responsibility to TRY not to be an online hygiene failure, just as everyone should look both ways before they cross the street. There’s a limit to the amount of laziness that the universe makes allowances for. Random schmo isn’t off the hook entirely when his files get encrypted and his/her work credentials are in the APT wind. I wish Random schmo well, but if we’re going to secure everything he/she touches, we need to get serious about Random Manufacturers.
‘we need to get serious about Random Manufacturers.’
Been saying exactly this for over a decade now. It’s harder than you’d think.
I realize that but we can’t stop trying to get it accomplished. If we can put tariffs on things for stupid shortsighted bs reasons you’d think we might use that power for useful things once in a while too. Without making it too political, we’re being idiots. What are we waiting for.
Any high security environment should’ve had their endpoint devices configured to prevent users bypassing any certificate warnings. Forced DNSSEC also would’ve helped. As a last resort, appropriate user training & awareness.
A high security environment might expect their users to have a minimum amount of commonsense around things like that (clicking through a big red flashing warning sign). But they SHOULD however be insisting on conditional access with the Oauth token bound to the device it was issued for. …….Anybody??
ANYBODY AT ALL IN A HIGH SECURITY ENVIRONMENT……
Crickets…and blame the user again. In 2026 that’s table stakes not an ‘addutional security feature’ Redmond – you are confusing users who know no better. Shame.
In fairness clicking through a warning about an insecure connection – not great to be sure. But plenty of shame to go round here.
It might get to the point where large corporations and ISPs need to start banning devices that are EOL/EOS. I don’t like it, but they seem to pose such a security risk to everyone else including themselves.
The alternative is to force corporations who make these devices to forever provide security updates, which to me also isnt a great idea.
But so many consumer devices and software use self signed certs, people are so used to simply clicking through.
Perhaps start requiring anything requiring a certificate to be signed using something like certbot with auto rewnew enabled by default when possible?
I meant scorn directed against generally uninteresting people somewhat ignorantly using ten year old hardware. Not like there are that many people going around hacking WiFi like decades ago. Their threats are more likely phishing or clicking the wrong link. Shrug. Not that it isn’t done. Not that a darpa employee would have any business doing that. But some random schmo, meh.
I get what you meant.
The wave of invasions has been increasing a lot lately.
Don’t all modern day browsers force “Secure DNS” through google/cloudflare ?
Seems like a serious wake-up call. Microsoft Office tokens and bypass MFA entirely. It goes to show how overlooked network devices can become powerful espionage tools. Keeping your routers updated is definitely is the move.