The same miscreants responsible for breaking into the networks of America’s top consumer and business data brokers appear to have also infiltrated and stolen huge amounts of data from the National White Collar Crime Center (NW3C), a congressionally-funded non-profit organization that provides training, investigative support and research to agencies and entities involved in the prevention, investigation and prosecution of cybercrime.
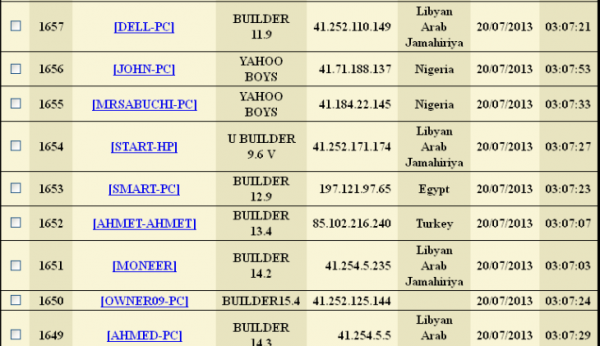
Last week, KrebsOnSecurity reported that entrepreneurs behind the underground criminal identity theft service ssndob[dot]ms also were responsible for operating a small but powerful collection of hacked computers exclusively at top data brokers, including LexisNexis, Dun & Bradstreet and HireRight/Kroll. A closer analysis of the Web server used to control that collection of hacked PCs shows that the attackers also had at least one infected system for several months this summer inside of the NW3c.
Core to the NW3C’s mission is its Investigative Support division, which according to the organization’s site “provides timely, relevant and effective services to member agencies involved in the prevention, investigation and prosecution of economic and high-tech crimes. The section has no investigative authority but can provide analytical assistance and perform public database searches.”
The NW3C said its analysts are frequently called upon to assist in establishing financial transaction patterns, developing possible links between criminal targets and associated criminal activity and providing link charts, timelines and graphs for court presentations. “Information obtained through public database searches can assist investigations by locating suspects, establishing property ownership and finding hidden assets, just to name a few of the benefits,” the organization’s Web site explains.
The NW3C also works with the Federal Bureau of Investigation (FBI) to run the Internet Crime Complaint Center (IC3), which accepts online Internet crime complaints from victims of cybercrime.
Neither the NW3C nor the IC3 responded to requests for comment on this story. FBI Spokeswoman Lindsay Godwin would say only that the FBI was “looking into it,” but declined to elaborate further, citing the ongoing nature of the investigation.
THE CRIME MACHINE
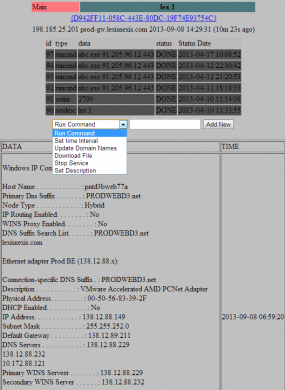
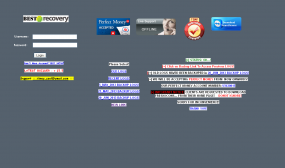
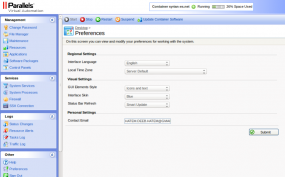
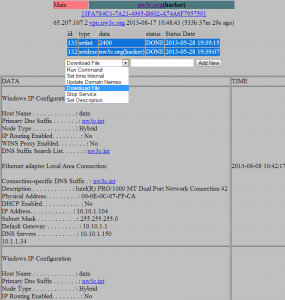
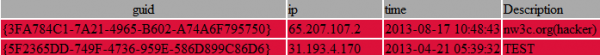
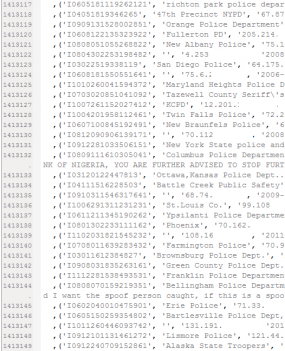
A number of indicators suggest that the attackers first gained access to the NW3C’s internal network on or around May 28, 2013. According to records in the online communications panel that the miscreants used to control their network of hacked systems, the affected NW3C server was taken offline on or around Aug. 17, 2013, indicating that the organization’s networks were compromised for approximately 11 weeks this summer. It’s not clear at this point why the miscreants marked this organization’s listing with a “(hacker)” designation, as shown in the snapshot of their botnet control panel below.
The attackers appear to have compromised a public-facing server at NW3C that was designed to handle incoming virtual private network (VPN) communications. Organizations frequently set up VPNs so that their remote employees can create an encrypted communications tunnel back to an otherwise closed network, and these setups are an integral component of most modern business applications.
Alarmingly, the machine name of the compromised NW3C system was “data.” On May 28, 2013, the attackers uploaded a file — nbc.exe — designed to open up an encrypted tunnel of communications from the hacked VPN server to their botnet controller on the public Internet. This appears to be the same nbc.exe file that was found on the two hacked servers at LexisNexis.
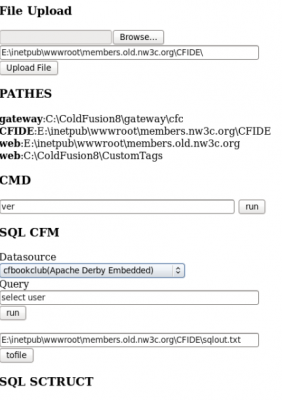
Abundant evidence left behind by the attackers suggests that they broke into the NW3C using a Web-based attack tool that focuses on exploiting recently-patched weaknesses in servers powered by ColdFusion, a Web application platform owned by Adobe Systems. I managed to get hold of the multiple exploits used in the attack server, and shared them with Adobe and with Rob Brooks-Bilson, a ColdFusion expert and author of the O’Reilly books Programming ColdFusion MX and Programming ColdFusion.
Although some of the exploits were listed as “0day” in the attack tool — suggesting they were zero-day, unpatched vulnerabilities in Adobe ColdFusion — Bilson said all of the exploits appear to attack vulnerabilities that are fixed in the most recent versions of ColdFusion. For example, three of the four exploits seems to have involved CVE-2013-0632, a vulnerability that Adobe first patched in January 2013, not long after the flaw was first spotted in actual zero-day online attacks. The remaining exploit in the attack kit targets a bug that Adobe fixed in 2010.
“The big issue with ColdFusion is that so many people install and set it up without following any of Adobe’s hardening guidelines,” Brooks-Bilson said in an email to KrebsOnSecurity. “Most of the exploits that have come out in the recent past have all worked via a similar mechanism that is easily mitigated by following Adobe’s guide. Of course, so many people disregard that advice and end up with servers that are easily compromised.”
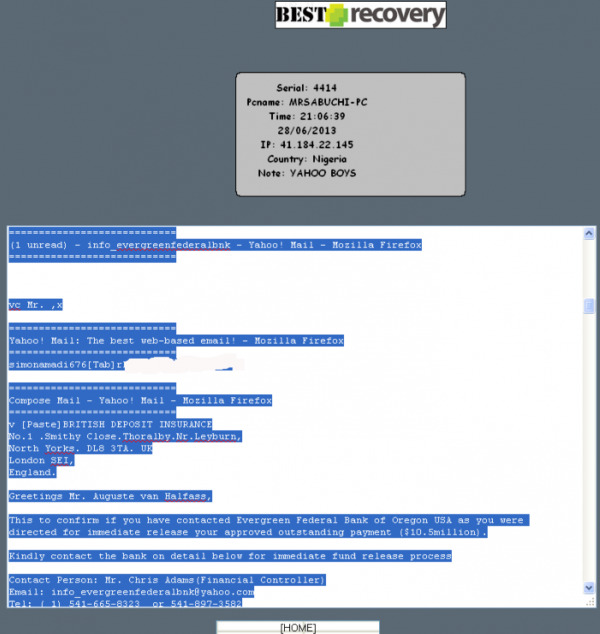
STEALING DATA ON VICTIMS AND FELLOW CROOKS ALIKE
The ColdFusion exploit server contains plenty of records indicating that the attackers in this case plundered many of the databases that they were able to access while inside of NW3C. Part of the reason for the persistence of this evidence has to do with the way that the attackers queried local databases and offloaded stolen data. It appears that once inside the NW3C’s network, the bad guys quickly scanned all of the organization’s systems for security vulnerabilities and database servers. They also uploaded a Web-based “shell” which let them gain remote access to the hacked server via a Web browser.
The attack server and shell also let the attackers execute system commands on the compromised hosts, which appear to be Microsoft IIS servers. Their method also left a detailed (if not complete) log of many of their activities inside the network. One of the first things the attackers did upon compromising the “Data” server on the network was run a query that forced the local database to dump a copy of itself to a file — including a list of the authorized users and passwords — that the attackers could download.
The bad guys in this case also appear to have used their access to the NW3C to steal 10 years’ worth of consumer complaint information from the Internet Crime Complaint Center (IC3), the aforementioned partnership between the NW3C and the FBI that tracks complaints about cybercrime.
Present on the attacker’s server are some 2.659 million records apparently lifted from the IC3. The records range in date from about the time of the IC3’s inception — May 8, 2000 — to Jan. 22, 2013.
It’s not clear if the stolen IC3 data set includes all of the consumer complaints ever filed, but it seems likely that the archive is lacking just the past few months of records. In a report released earlier this year, the IC3 said it was receiving about 24,000 complaints per month, and that consumers had filed 289,874 complaints last year. The IC3’s site doesn’t maintain annual complaint numbers prior to 2003, but according to the site some 2.35 million have been filed with the system since then. To put the year-over-year growth in complaints in perspective, the IC3 said it wasn’t until 2007 — nearly seven years after its birth — that the organization received its millionth complaint.





![The botnet interface used by the miscreants who own and operate ssndob[dot]ms](https://krebsonsecurity.com/wp-content/uploads/2013/09/SSNdobBotC2-600x118.png)