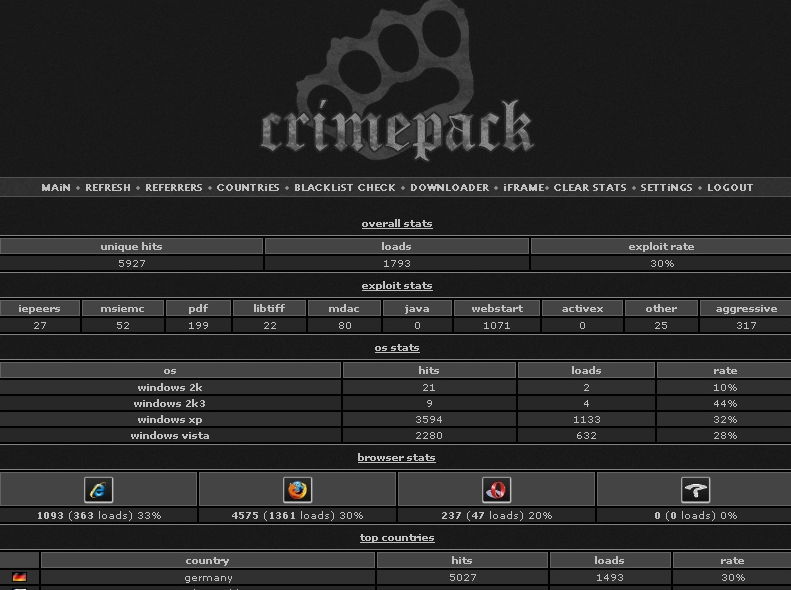
 McAfee just published the sixth edition of its Security Journal, which includes a lengthy piece I wrote about the pros and cons of taking down Internet service providers and botnets that facilitate cyber criminal activity. The analysis focuses on several historical examples of what I call “shuns” and “stuns,” or taking out rogue networks either by ostracizing them, or by kneecapping their infrastructure in a coordinated surprise attack, respectively.
McAfee just published the sixth edition of its Security Journal, which includes a lengthy piece I wrote about the pros and cons of taking down Internet service providers and botnets that facilitate cyber criminal activity. The analysis focuses on several historical examples of what I call “shuns” and “stuns,” or taking out rogue networks either by ostracizing them, or by kneecapping their infrastructure in a coordinated surprise attack, respectively.
The theme of this edition of the journal is finding ways to take security on the offense, and it includes articles from noted security researchers Joe Stewart and Felix “FX” Lindner.
Here’s the lead-in from my contribution:
The security technologies most of us rely on every day — from anti-virus software to firewalls and intrusion detection devices — are reactive. That is, they are effective usually only after a new threat has been identified and classified. The trouble is that, meanwhile, an indeterminate number of individuals and corporations become victims of these unidentified stalkers.
Until quite recently, this “bag ’em and tag ’em” approach to dealing with malicious activity online had become so ingrained in the security community that most of the thought leaders on security were content merely to catalog the Internet’s worst offenders and abide the most hostile networks. Exponential increases in the volume and sophistication of new threats unleashed during the past few years — coupled with a pervasive attitude that fighting criminal activity online is the principal job of law enforcement — have helped to reinforce this bunker mentality.
Then, in the fall of 2007, something remarkable happened that seemed to shake the security industry out of its torpor: a series of investigative stories in the mainstream and technology press about concentrations of cybercrime activity at a Web hosting conglomerate in St. Petersburg known as the Russian Business Network (RBN) caused the ISPs serving the infamous provider to pull the plug. The RBN, which had been a vortex of malicious activity for years, was forced to close up shop and, subsequently, scattered its operations.
This was the first of many examples that would demonstrate the strategic (and, arguably, cathartic) value of identifying and isolating significant, consistent sources of hostile — if not criminal — activity online. I will focus on two popular methods of taking the fight to the enemy and will offer a few thoughts on the long-term viability of these approaches.
Copies of the journal are available from this link.