A leading Russian politician has accused a prominent Moscow businessman of running an international spam and online pharmacy operation while serving as an anti-spam adviser to the Russian government. Russian investigators now say they plan to create a special task force to look into the allegations.
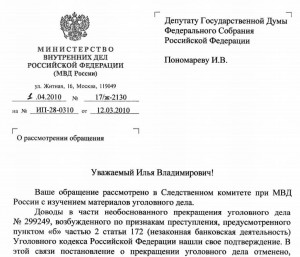 In an open letter to investigators at the Ministry of Internal Affairs (MVD) of the Russian Federation, Ilya V. Ponomarev, a deputy of the Russian State Duma’s Hi-Tech Development Subcommittee, in March called for a criminal inquiry into the activities of one Pavel Vrublevsky, an individual I interviewed last year in an investigative report on rogue security software (a translated PDF version of Ponomarev’s letter is here).
In an open letter to investigators at the Ministry of Internal Affairs (MVD) of the Russian Federation, Ilya V. Ponomarev, a deputy of the Russian State Duma’s Hi-Tech Development Subcommittee, in March called for a criminal inquiry into the activities of one Pavel Vrublevsky, an individual I interviewed last year in an investigative report on rogue security software (a translated PDF version of Ponomarev’s letter is here).
Vrublevsky is founder and general director of ChronoPay, an online payment processor widely accepted in Russia to handle a number of domestic transactions, including payment for Russian airline and lottery tickets. ChronoPay also specializes in handling “high risk” online merchants, such as pharmacy, adult and Internet gaming sites. Last year, The Washington Post published a story I wrote that showed Chronopay was processing payments for a large number of sites pushing rogue anti-virus products, or “scareware.”
According to Ponomarev, Vrublevsky also is known online as “Redeye,” and is the creator of Crutop.nu, a large adult Webmaster forum that the U.S. Federal Trade Commission last year said was a place “where criminals share techniques and strategies with one another,” and a Russian language Web site “that features a variety of discussion forums that focus on making money from spam.”
In his letter to A.V. Anichin, the deputy minister and chief of the Russian MVD Investigations Committee, Ponomarev said the primary analysis of Vrublevsky’s activities shows the extent of the problem which escapes attention of law-enforcement bodies.
“They include trade in pornography on the Internet that contains scenes of cruel violence, real rape, zoophilia, etc. (etu-cash.com, cash.pornocruto.es), unlawful banking business focused on laundering of money generated by a range of criminal activities in order to escape taxes using fethard.biz and acceptance of payments for illegal sale of music files mp3 which violates author’s rights of performers and illegal trade in drug-containing and controlled prescribed drastic preparations via on-line chemistry networks (rx-promotion.com, spampromo.com), and illegal mass spam distribution all over the world, as well as sale of malicious software under the guise of anti-virus software.”
Ponomarev notes that Vrublevsky is a key member of the anti-spam working group of the Ministry of Telecom and Mass Communication. Ponomarev also said that the MVD had instituted a criminal investigation into Vrublevsky in 2007, only to abandon the case when the chief investigator quit and reportedly went to work for Vrublevsky.
“We have here a merger between a criminal element and the government power which is unacceptable and inadmissible in any civilized society,” Ponomarev wrote.