Earlier this week, a Ukrainian security researcher leaked almost two years’ worth of internal chat logs from Conti, one of the more rapacious and ruthless ransomware gangs in operation today. Tuesday’s story examined how Conti dealt with its own internal breaches and attacks from private security firms and governments. In Part II of this series we’ll explore what it’s like to work for Conti, as described by the Conti employees themselves.

The Conti group’s chats reveal a great deal about its internal structure and hierarchy. Conti maintains many of the same business units as a legitimate, small- to medium-sized enterprise, including a Human Resources department that is in charge of constantly interviewing potential new hires.
Other Conti departments with their own distinct budgets, staff schedules, and senior leadership include:
–Coders: Programmers hired to write malicious code, integrate disparate technologies
–Testers: Workers in charge of testing Conti malware against security tools and obfuscating it
–Administrators: Workers tasked with setting up, tearing down servers, other attack infrastructure
–Reverse Engineers: Those who can disassemble computer code, study it, find vulnerabilities or weaknesses
–Penetration Testers/Hackers: Those on the front lines battling against corporate security teams to steal data, and plant ransomware.
Conti appears to have contracted out much of its spamming operations, or at least there was no mention of “Spammers” as direct employees. Conti’s leaders seem to have set strict budgets for each of its organizational units, although it occasionally borrowed funds allocated for one department to address the pressing cashflow needs of another.
A great many of the more revealing chats concerning Conti’s structure are between “Mango” — a mid-level Conti manager to whom many other Conti employees report each day — and “Stern,” a sort of cantankerous taskmaster who can be seen constantly needling the staff for reports on their work.
In July 2021, Mango told Stern that the group was placing ads on several Russian-language cybercrime forums to hire more workers. “The salary is $2k in the announcement, but there are a lot of comments that we are recruiting galley slaves,” Mango wrote. “Of course, we dispute that and say those who work and bring results can earn more, but there are examples of coders who work normally and earn $5-$10k salary.”
The Conti chats show the gang primarily kept tabs on the victim bots infected with their malware via both the Trickbot and Emotet crimeware-as-a-service platforms, and that it employed dozens of people to continuously test, maintain and expand this infrastructure 24 hours a day, 7 days a week.
Conti members referred to Emotet as “Booz” or “Buza,” and it is evident from reading these chat logs that Buza had its own stable of more than 50 coders, and likely much of the same organizational structure as Conti.
According to Mango, as of July 18, 2021 the Conti gang employed 62 people, mostly low-level malware coders and software testers. However, Conti’s employee roster appears to have fluctuated wildly from one month to the next. For example, on multiple occasions the organization was forced to fire many employees as a security precaution in the wake of its own internal security breaches.
In May 2021, Stern told Mango he wanted his underlings to hire 100 more “encoders” to work with the group’s malware before the bulk of the gang returns from their summer vacations in Crimea. Most of these new hires, Stern says, will join the penetration testing/hacking teams headed by Conti leaders “Hof” and “Reverse.” Both Hof and Reverse appear to have direct access to the Emotet crimeware platform.
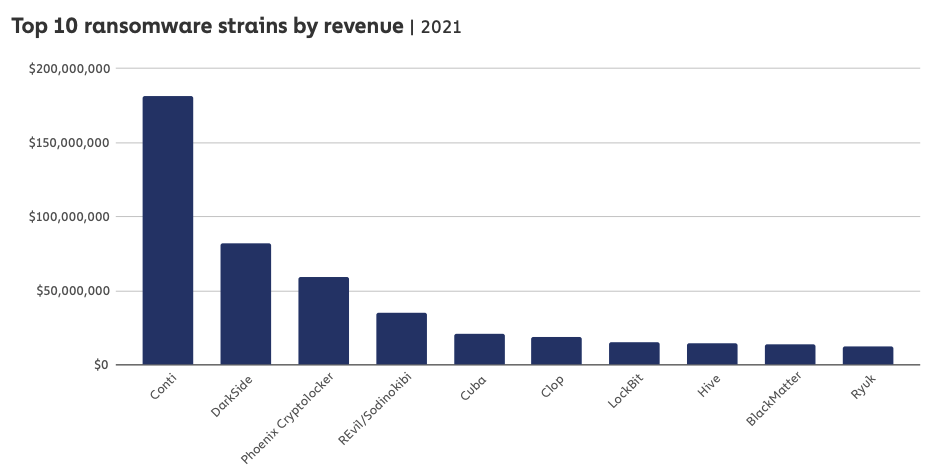
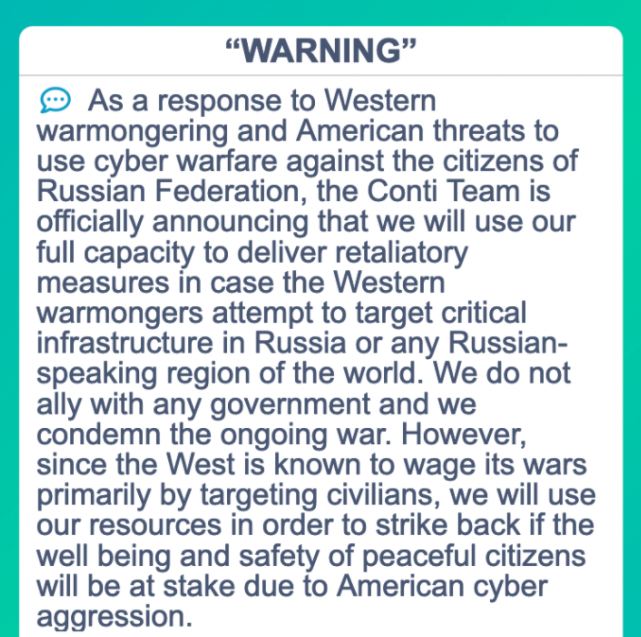
On July 30, 2021, Mango tells stern the payroll has increased to 87 salaried employees, with more hires on the way. But trying to accurately gauge the size of the Conti organization is problematic, in part because cybersecurity experts have long held that Conti is merely a rebrand of another ransomware strain and affiliate program known as Ryuk.
First spotted in 2018, Ryuk was just as ruthless and mercenary as Conti, and the FBI says that in the first year of its operation Ryuk earned more than $61 million in ransom payouts.
“Conti is a Targeted version of Ryuk, which comes from Trickbot and Emotet which we’ve been monitoring for some time,” researchers at Palo Alto Networks wrote about Ryuk last year. “A heavy focus was put on hospital systems, likely due to the necessity for uptime, as these systems were overwhelmed with handling the ongoing COVID-19 pandemic. We observed initial Ryuk ransom requests ranging from US$600,000 to $10 million across multiple industries.”
On May 14, 2021, Ireland’s Health Service Executive (HSE) suffered a major ransomware attack at the hands of Conti. The attack would disrupt services at several Irish hospitals, and resulted in the near complete shutdown of the HSE’s national and local networks, forcing the cancellation of many outpatient clinics and healthcare services. It took the HSE until Sept. 21, 2021 to fully restore all of its systems from the attack, at an estimated cost of more than $600 million.
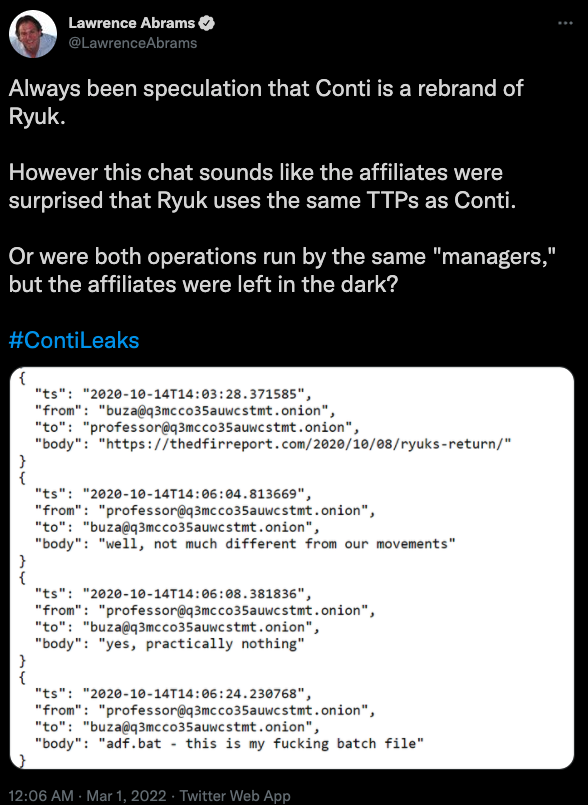
It remains unclear from reading these chats how many of Conti’s staff understood how much of the organization’s operations overlapped with that of Ryuk. Lawrence Abrams at Bleeping Computer pointed to an October 2020 Conti chat in which the Emotet representative “Buza” posts a link to a security firm’s analysis of Ryuk’s return.
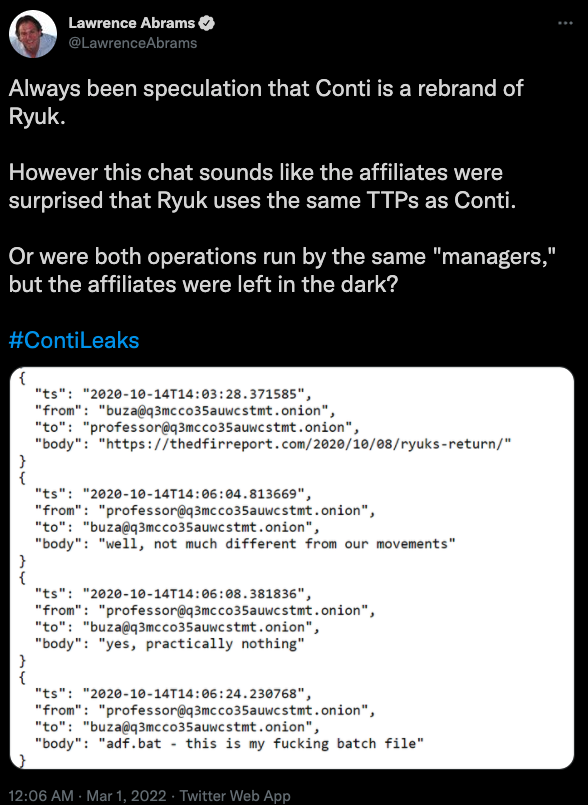
“Professor,” the nickname chosen by one of Conti’s most senior generals, replies that indeed Ryuk’s tools, techniques and procedures are nearly identical to Conti’s.
“adf.bat — this is my fucking batch file,” Professor writes, evidently surprised at having read the analysis and spotting his own code being re-used in high-profile ransomware attacks by Ryuk.
“Feels like [the] same managers were running both Ryuk and Conti, with a slow migration to Conti in June 2020,” Abrams wrote on Twitter. “However, based on chats, some affiliates didn’t know that Ryuk and Conti were run by the same people.” Continue reading →