Costa Rica’s national health service was hacked sometime earlier this morning by a Russian ransomware group known as Hive. The intrusion comes just weeks after Costa Rican President Rodrigo Chaves declared a state of emergency in response to a data ransom attack from a different Russian ransomware gang — Conti. Ransomware experts say there is good reason to believe the same cybercriminals are behind both attacks, and that Hive has been helping Conti rebrand and evade international sanctions targeting extortion payouts to cybercriminals operating in Russia.
The Costa Rican publication CRprensa.com reports that affected systems at the Costa Rican Social Security Fund (CCSS) were taken offline on the morning of May 31, but that the extent of the breach was still unclear. The CCSS is responsible for Costa Rica’s public health sector, and worker and employer contributions are mandated by law.
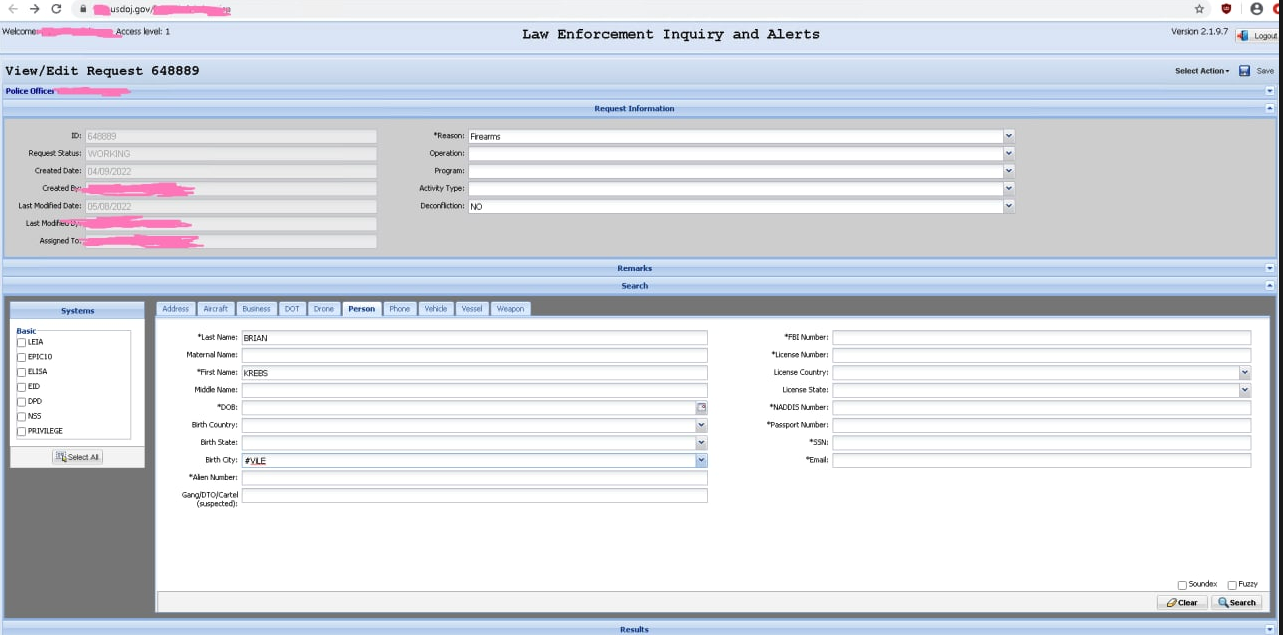
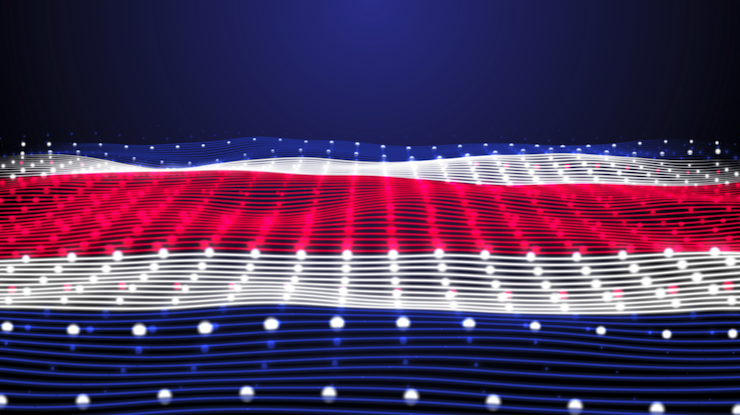
A hand-written sign posted outside a public health center in Costa Rica today explained that all systems are down until further notice (thanks to @Xyb3rb3nd3r for sharing this photo).

A hand-written notice posted outside a public health clinic today in Costa Rica warned of system outages due to a cyberattack on the nation’s healthcare systems. The message reads: “Dear Users: We would like to inform you that due a problem related to the information systems of the institution, we are unable to expend any medicine prescriptions today until further notice. Thank you for your understanding- The pharmacy.”
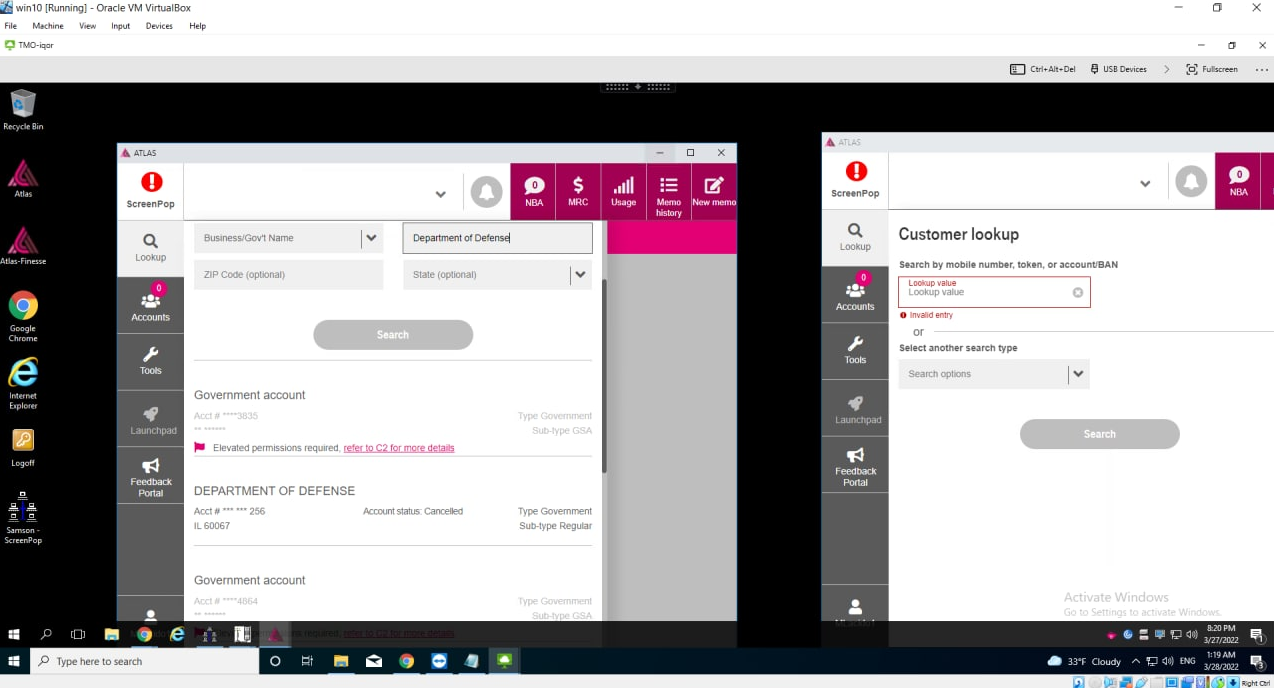
Esteban Jimenez, founder of the Costa Rican cybersecurity consultancy ATTI Cyber, told KrebsOnSecurity the CCSS suffered a cyber attack that compromised the Unique Digital Medical File (EDUS) and the National Prescriptions System for the public pharmacies, and as a result medical centers have turned to paper forms and manual contingencies.
“Many smaller health centers located in rural areas have been forced to close due to not having the required equipment or communication with their respective central health areas and the National Retirement Fund (IVM) was completely blocked,” Jimenez said. “Taking into account that salaries of around fifty thousand employees and deposits for retired citizens were due today, so now the payments are in danger.”
Jimenez said the head of the CCSS has addressed the local media, confirming that the Hive ransomware was deployed on at least 30 out of 1,500 government servers, and that any estimation of time to recovery remains unknown. He added that many printers within the government agency this morning began churning out copies of the Hive ransom note.
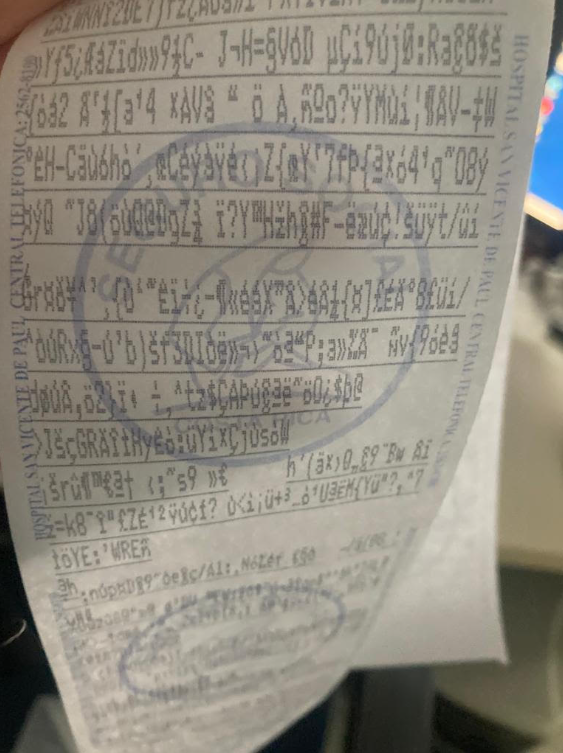
Printers at the Costa Rican government health ministry went crazy this morning after the Hive ransomware group attacked. Image: Esteban Jimenez.
“HIVE has not yet released their ransom fee but attacks are expected to follow, other organizations are trying to get a hold on the emergency declaration to obtain additional funds to purchase new pieces of infrastructure, improve their backup structure amongst others,” Jimenez said.
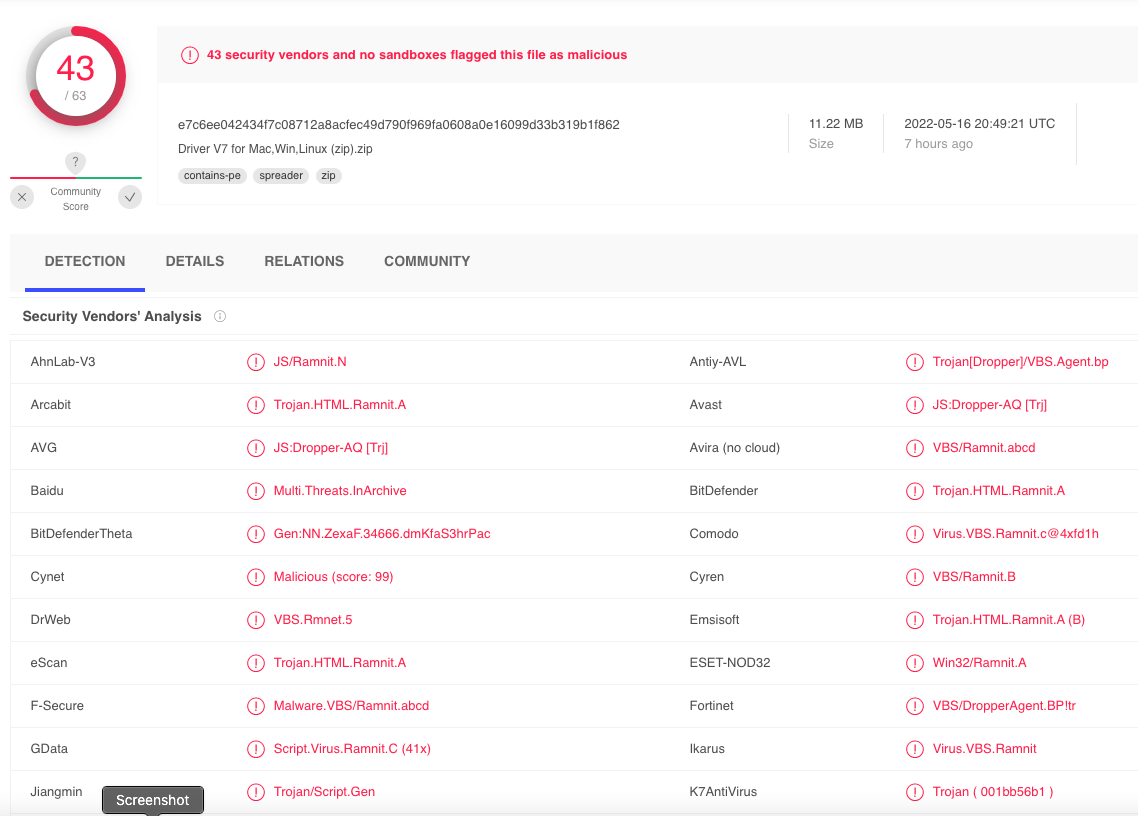
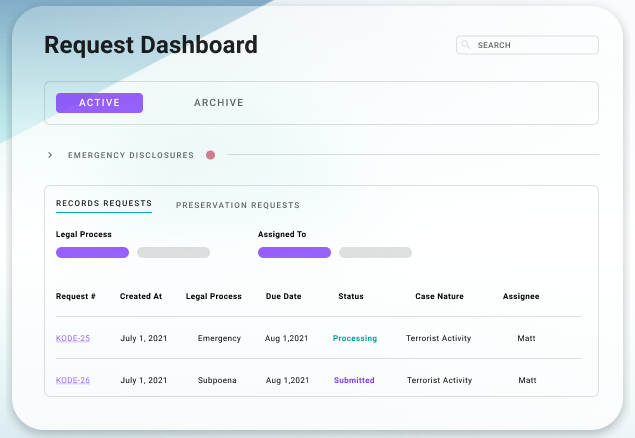
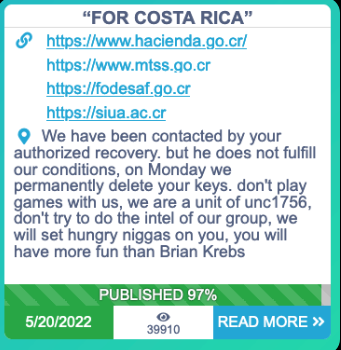
A copy of the ransom note left behind by the intruders and subsequently uploaded to Virustotal.com indicates the CCSS intrusion was the work of Hive, which typically demands payment for a digital key needed to unlock files and servers compromised by the group’s ransomware.
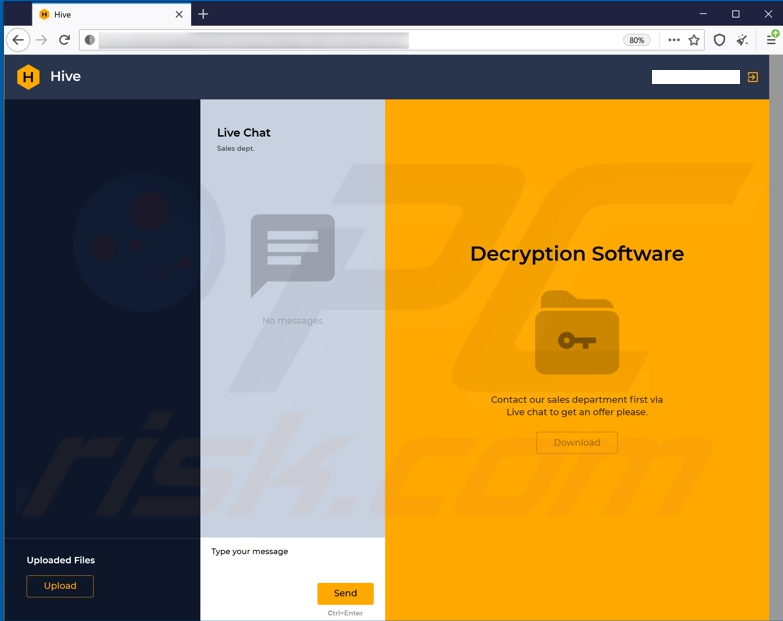
A HIVE ransomware chat page for a specific victim (redacted).
On May 8, President Chaves used his first day in office to declare a national state of emergency after the Conti ransomware group threatened to publish gigabytes of sensitive data stolen from Costa Rica’s Ministry of Finance and other government agencies. Conti initially demanded $10 million, and later doubled the amount when Costa Rica refused to pay. On May 20, Conti leaked more than 670 gigabytes of data taken from Costa Rican government servers.
As CyberScoop reported on May 17, Chaves told local media he believed that collaborators within Costa Rica were helping Conti extort the government. Chaves offered no information to support this claim, but the timeline of Conti’s descent on Costa Rica is worth examining.
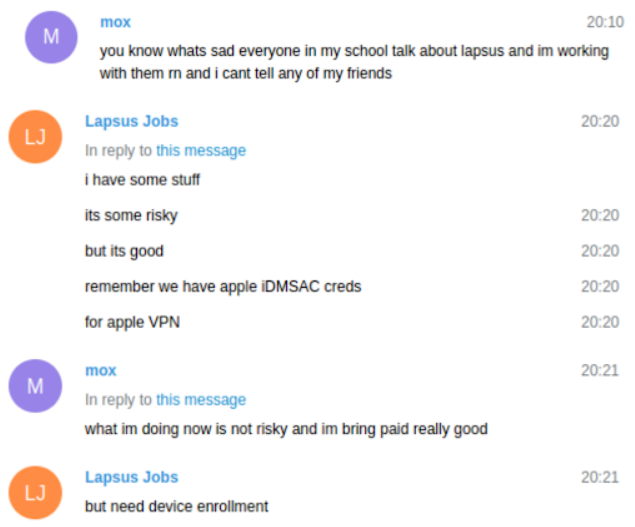
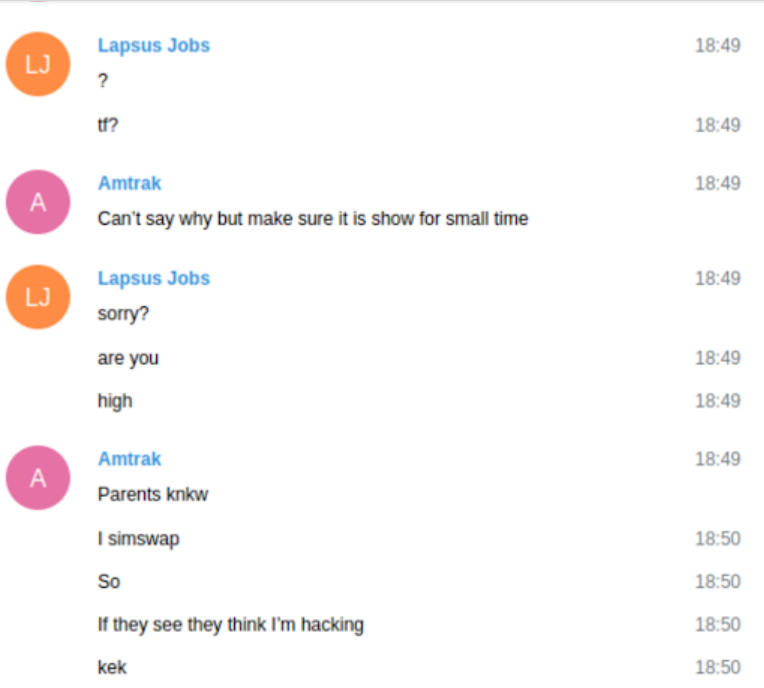
Most of Conti’s public communications about the Costa Rica attack have very clearly assigned credit for the intrusion to an individual or group calling itself “unc1756.” In March 2022, a new user by the same name registered on the Russian language crime forum Exploit.
A message Conti posted to its dark web blog on May 20.
On the evening of April 18, Costa Rica’s Ministry of Finance disclosed the Conti intrusion via Twitter. Earlier that same day, the user unc1756 posted a help wanted ad on Exploit saying they were looking to buy access to “special networks” in Costa Rica.
“By special networks I mean something like Haciendas,” unc1756 wrote on Exploit. Costa Rica’s Ministry of Finance is known in Spanish as the “Ministerio Hacienda de Costa Rica.” Unc1756 said they would pay $USD 500 or more for such access, and would work only with Russian-speaking people. Continue reading