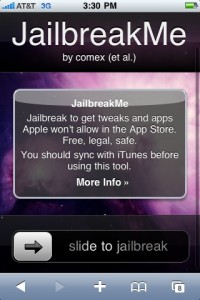
 One of the more interesting developments over the past week has been the debut of jailbreakme.com, a Web site that allows Apple customers to jailbreak their devices merely by visiting the site with their iPhone, iPad or iTouch. Researchers soon learned that the page leverages two previously unknown security vulnerabilities in the PDF reader functionality built into Apple’s iOS4.
One of the more interesting developments over the past week has been the debut of jailbreakme.com, a Web site that allows Apple customers to jailbreak their devices merely by visiting the site with their iPhone, iPad or iTouch. Researchers soon learned that the page leverages two previously unknown security vulnerabilities in the PDF reader functionality built into Apple’s iOS4.
Adobe was quick to issue a statement saying that the flaws were in Apple’s software and did not exist in its products. Interestingly, though, this same attack does appear to affect Foxit Reader, a free PDF reader that I often recommend as an alternative to Adobe.
According to an advisory Foxit issued last week, Foxit Reader version 4.1.1.0805 “fixes the crash issue caused by the new iPhone/iPad jailbreak program which can be exploited to inject arbitrary code into a system and execute it there.” If you use Foxit, you grab the update from within the application (“Help,” then “Check for Updates Now”) or from this link.
Obviously, from a security perspective the intriguing aspect of a drive-by type jailbreak is that such an attack could easily be used for more nefarious purposes, such as seeding your iPhone with unwanted software. To be clear, nobody has yet seen any attacks like this, but it’s certainly an area to watch closely. F-Secure has a nice Q&A about the pair of PDF reader flaws that allow this attack, and what they might mean going forward. Apple says it plans to release an update to quash the bugs.
I’m left wondering what to call these sorts of vulnerabilities that quite obviously give users the freedom that jailbreaking their device(s) allows (the ability to run applications that are not approved and vetted by Apple) but that necessarily direct the attention of attackers to very potent vulnerabilities that can be used to target jailbreakers and regular users alike. It’s not quite a “featureability,” which describes an intentional software component that opens up customers to attack even as the vendor insists the feature is a useful, by-design ability rather than a liability.
I came up with a few ideas.
– “Apptack”
– “Jailbait” (I know, I know, but it’s catchy)
– “Freedoom”
Maybe KrebsOnSecurity readers can devise a better term? Sound off in the comments below if you come up with any good ones.
Finally, I should note that while Adobe’s products may not be affected by the above-mentioned flaws, the company said last week that it expects to ship an emergency update on Tuesday to fix at least one critical security hole present in the latest version of Adobe Reader for Windows, Mac and Linux systems.
Adobe said the update will fix a flaw that researcher Charlie Miller revealed (PDF!) at last month’s Black Hat security conference in Las Vegas, but it hinted that the update may also include fixes for other flaws. I’ll have more on those updates when they’re released, which should coincide with one of the largest Microsoft Patch Tuesdays ever: Redmond said last week that it expects to issue at least 14 updates on Tuesday. Update, Aug. 10, 5:06 p.m. ET:Adobe won’t be releasing the Reader update until the week of Aug. 16.




how about jailbreak.
AppleJack.
To install the latest version of Foxit reader it was necessary to uninstall version 3.3.1… that I had and download version 4.1…, which was not big deal. It encouraging to note that Adobe seems to be taking security more seriously by enabling ASLR and DEP in their reader and the out of band update.
“In its ongoing commitment of providing safer, faster and more stable PDF software tools, Foxit is taking a proactive measure in securing its 100 million PDF Reader users against the iPhone/iPad Jailbreaking application that utilizes malicious PDFs to hack the systems of unsuspecting users. Hackers are now trying to use these malicious PDF’s to access sensitive data on desktops. Foxit welcomes all PDF Reader users to download the latest version of the Foxit Reader 4.1.1 which addresses and resolves the issues related to the jailbreak hack.
To protect iPhone/iPad users from the jailbreak program that is being used to exploit iPhones in the way they handle PDFs, Foxit is preannouncing its soon to be submitted PDF Reader App for iPhone. Foxit believes that the upcoming release of its Foxit Reader for iPhone will provide a secure PDF reader for the iPhone. Foxit will be submitting this App within two weeks and it will have full PDF viewing capability. Just as with the Windows Reader, Foxit PDF Reader for iPhone will protect users against malicious PDFs.”
Vulnerabilities.
Regardless of how they are used, these bugs are vulnerabilities in the intended security model that allow the person using them to bypass software restrictions. Just because a large number of users consider them beneficial doesn’t change what they are.
Adding a new buzz word just confuses the topic. Whether people like Apple’s iPhone security model or not, it is what it is, and bypassing it using one of these vulnerabilities makes them less secure.
If a similar application came out publicly that leveraged one of these vulnerabilities to elevate privileges in Windows & allowed enterprise users to install $NonApprovedApp, we certainly wouldn’t be as excited about it.
(yes my iPhone is jailbroken.)
When I tried to upgrade Foxit to its newest version following Brian’s instructions, Panda Cloud Antivirus blocked the installation. Explanation… “Dangerous operation detected: Rule 5012. ”
So what’s Rule 5012?
http://blog.cloudantivirus.com/2010/06/03/behavioral-blocking-rules/
“Rules 5012 & 5017: During normal behaviour PDF readers shouldn’t need to create executable files in the system. So if you receive an alert, some kind of vulnerability is being exploited.”
Great! So it appears that what Panda is saying is that a PDF reader that downloads and runs executable security updates (in order to protect against PDF exploits) is in fact an exploit in itself. And so many here wonder why small business owners can’t secure their computers well enough to avoid uhhhh…PDF exploits. You gotta love computers. 🙂
Hello TJ,
I work for Panda Security as incident analyst.
Reported incident while upgrading FoxIt Reader is fixed in our last published version (1.1.2). Could you please download and install it?
If you keep having problems with Foxit upgrade you can reach me at davidDOTsanjose CIRCLEA pandasecurityDOTcom or you can post your problem in our support forums (http://www.cloudantivirus.com/forum/index.jspa)
Regards,
David
David,
Thanks you very much for the reply. I’ll search for the update and install it right away.
Adobait
After installing FoxIt 4.0, I got the sense that even the famously “lightweight” FoxIt is becoming a bit bloated. I’ve always hated the advertisements in the upper right-hand corner of FoxIt.
Currently I’m using Tracker Software’s PDF XChange free viewer. It has an advertisement too.
I’ve also heard about Nitro PDF’s new free reader at nitroreader.com. And of course for those who want truly lightweight, minimal functionality PDF reader there’s Sumatra.
Any opinions? I don’t want to hijack this thread. Vote me down if you want.
SourApples?
WhineSaps?
CrabApples?
Hmm a name well my third thought has already been taken…
Obviously as it’s “Apples fault” not “Adobie et al” then it will have to contain “apple” or something related to them…
My first thought was due to thinking how your average Apple “fashionista” would feel (ie somewhat bitter and twisted up or just plain crabby or at the very least having it leave a nasty taste in the mouth) hence,
crabapple
Moving on from that other geeks might conclude this is proof that Apple products are how should one put it delicately “organic fertilizer of herbivore” etc thus regard them as one would,
Horse Apples
Or as it’s not in the “Apple spirit”,
Calverdross
Once the patches are in place, it will only affected the unpatched, so it could be the Green Apple Jailbreaker. (Sounds like a Batman Villain whose gimmick is using candy-like devices.)
Seriously, though, this kind of exploit is exactly why placing faith in new platforms to protect your customers is only a band-aid for security. Just because malware isn’t known for these platforms yet doesn’t mean they don’t exist or won’t exist in the near future.
The increasing dependence on Mobile platforms by customers should be downright frightening by Financial Institutions who offer extensive services on the platform, because users don’t believe there is any kind of risk of infection or problems with their phone yet.
You are 100% right. Financial institutions are going crazy pushing the mobile platforms, with almost no additional security education. A large volume of applications for mobile phones too only require a single form of authentication. One program I’ve seen requires a 6 digit all numeric password, and doesn’t allow for anything more complex. Clearly the lessons learned in the PC world aren’t being ported over. It won’t take something nearly as good as Zeus to cause some major problems for mobile users…
Heck, I refuse to use my non-smart phone Razr for accessing even my e-mail accounts as I don’t fully trust a: the phone platform itself, and b: the cellular network. I may feel differently if there were good tools (such as those for computers and their associated networks) we could use to verify the integrity of the phone itself and test the security of the celluar network from point to point.
The topic of smart phone security is just now being brought up for discussion! 🙁
Thoughts on Malware for Mobile Devices
https://isc.sans.edu/diary.html?storyid=9046
Thoughts on Malware for Mobile Devices – Part 2
http://isc.sans.edu/diary.html?storyid=9160
Perhaps we ought to view these jailbreakers the same way we view the proverbial canaries in the mine: as early-warning systems designed to alert the rest of us to vulnerabilities needing to be corrected.
If the jailbreakers can find vulnerabilities before the cybercriminals have found and exploited them, then the community benefits from their efforts.