Media attention to crimes involving ATM skimmers may make consumers more likely to identify compromised cash machines, which involve cleverly disguised theft devices that sometimes appear off-color or out-of-place. Yet, many of today’s skimmer scams can swipe your card details and personal identification number while leaving the ATM itself completely untouched, making them far more difficult to spot.
The most common of these off-ATM skimmers can be found near cash machines that are located in the antechamber of a bank or building lobby, where access is controlled by a key card lock that is activated when the customer swipes his or her ATM card. In these scams, the thieves remove the card swipe device attached to the outside door, add a skimmer, and then reattach the device to the door. The attackers then place a hidden camera just above or beside the ATM, so that the camera is angled to record unsuspecting customers entering their PINs.
The crooks usually return later in the evening to remove the theft devices. Armed with skimmed card data and victim PINs, skimmer thieves are able to encode the information onto counterfeit cards and withdraw money from compromised accounts at ATMs across the country.
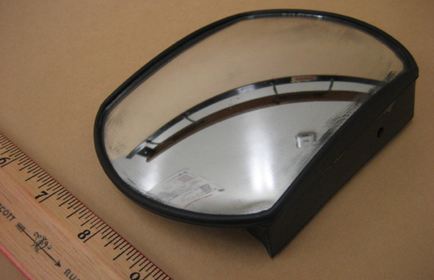
On July 24, 2009, California police officers responded to a report that a customer had uncovered a camera hidden behind a mirror that was stuck to the wall above an ATM at a bank in Sherman Oaks, Calif. There were two ATMs in the lobby where the camera was found, and officers discovered that the thieves had placed an “Out of Order” sign on the ATM that did not have the camera pointed at its PIN pad. The sign was a simple ruse designed to trick all customers into using the cash machine that was compromised.
Bank security cameras at the scene of the crime show the fake mirror installed over the ATM on the right.
Here’s a front view of the hidden camera, which probably would appear to most ATM users as nothing more than a parabolic mirror designed to give customers a view of anyone standing behind them.
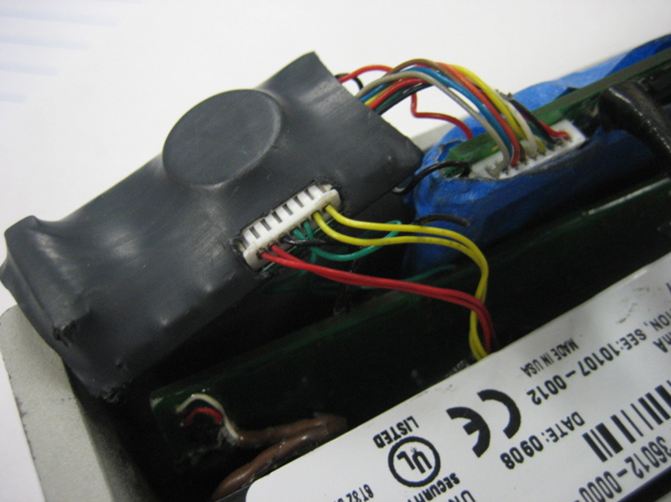
Behind the glass, however, was a battery-operated hidden camera. A tiny hole was cut out of the bottom of the mirror housing to enable the camera to record PIN entries.
Below are several images showing the key card door lock that was compromised in this attack. The top left image shows the device as it would appear attached to the door securing access to the ATM lobby. The other two pictures show the skimmer device with the electronic components added by the thieves.
 The attackers hitting this ATM were either very persistent, or varied: A source familiar with the July 24 incident said this particular door lock would be stolen and modified a total of nine times in 2009.
The attackers hitting this ATM were either very persistent, or varied: A source familiar with the July 24 incident said this particular door lock would be stolen and modified a total of nine times in 2009.
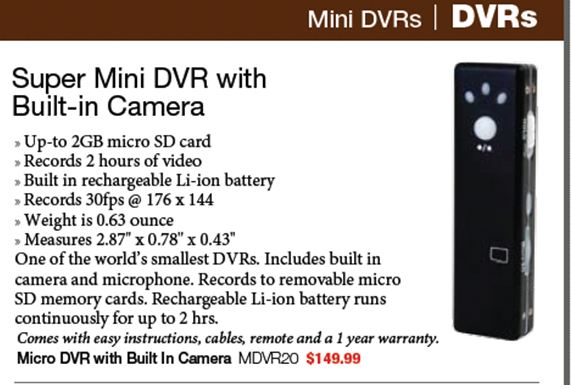
The camera used in this attack retails for about $150, can record up to 2 GB (about two hours worth) of video, and runs on a rechargeable lithium ion battery.
[EPSB]
Have you seen:
Having a Ball With ATM Skimmers…On February 8, 2009, a customer at an ATM at a Bank of America branch in Sun Valley, Calif., spotted something that didn’t look quite right about the machine: A silver, plexiglass device had been attached to the ATM’s card acceptance slot, in a bid to steal card data from unsuspecting ATM users. But the customer and the bank’s employees initially overlooked a secondary fraud device that the unknown thief had left at the scene: A sophisticated, battery operated and motion activated camera designed to record victims entering their personal identification numbers at the ATM.
[/EPSB]







I always wondered why the banks in my city leave the door unlocked to the ATMs (no need to swipe). Now I know why.
This skimming method can be easily defeated if you swipe one card to get access into the lobby (I guess even one expired might work, probably not authenticated online) and another card into the ATM machines and provided that you have on the 2 cards different pin codes. This method of controlling access in the lobby is not used very often in Europe, here banks have 1-2 ATM’s inside, which can be used during banking hours and one ATM and one CHIP machine (a device which allows transferring founds from your account to the chip of your card, which can subsequently be used for transactions which are not authenticated online) outside which can be used 24×7.
The outside devices are targeted by skimmers, but I don’t consider placing the ATM’s in a lobby and controlling access with a card swipe to be a good protection against skimmers, robbers, vandals, thieves, etc. They can easily get inside by tailgating, using a false or stolen card, forcing the door, etc, and then they can go on with their “business” undisturbed by passers-by. (as it looks the bank cameras are not watched 24×7 and can be easily knocked out anyway.
In fact it struck me in the article that Police was alerted by an observant customer who noticed the camera pinhole and not by bank security personnel.
Not only can you use a different card to gain access to the lobby, many of the lobbies only require *a* card with a magnetic bar. I’ve opened some with my capital one card!
It always scares me .. things like this .. and even though it doesn’t happen very much in my city I wonder how would anyone know and would the bank even catch it?
Banks are required to avoid NEGLIGENCE in their operations, which would require DAILY inspection for irregularities in and around ATM machines.
Lawyers just love CLASS ACTIONS in TORT and negligence4 is a tort. Tort actions also allow for punitive damages, where contract actions do not.
So, in my opinion, regardless of what you have contractually agreed to with the bank, the remedy of tort for either negligence or gross negligence remains available.
Banks indeed inspect ATMs every day. However, thieves tend to be in and out very quickly, within a few hours. If you are a victim of unauthorized transactions, you are protected by Regulation E. Class action suits for negligence would never be entertained by the courts since there are adequate protections already.
how can it be adequate if people are stealing money under your nose??? does not even make sense!
It makes sense if you pay attention. As I’ve said before, thieves work much faster and in greater numbers than banks. You seem to want to stop the thieves in the first place; fair enough. But not practical. Can’t be done.
By adequate protections, I’m referring to Regulation E, which requires the bank cover any theft of your money at ATMs. Therefore, no class action suits since there are no losses for the customer.
Of course it can be done! Just do away with magstripe cards already, like the rest of the world has. Smartcard bank passes can’t be skimmed.
You can get mini cameras from china very cheap via ebay under two weeks delivery to the uk it cost me just £6.80 post free a few months ago. amazing tech just needed a spare 4gig micro sd card i had, playback quality on windows media player was stunning, sound as well.
http://cgi.ebay.co.uk/SPY-CAR-KEYRING-KEY-FOB-CAMERA-KINGSTON-2GB-MICRO-SD-UK-/290484533769
Why is Tommy down voted? He is exactly right. microSD card mini ‘spy cameras’ can be had for less than 10% of the price Brian noted.
This just makes me wonder why we still have that magnetic stripe on credit cards. It wouldn’t work with a pure chip-based solution.
There are portable receivers that can be easily carried in a handbag or a briefcase that collects data from chip cards. Someone can get into an elevator with you or pass you on the street and have all of your chip card data. Much easier than skimming devices. I wouldn’t own a chip card.
Actually, that’s not exactly the case. With RFID “chip cards”, yes, it’s entirely possible and easy to do exactly what you just said unless the victim has some sort of Faraday cage around their cards (aluminum foil wallet, for example). However, what is more often employed are SMART cards. These tricky little devils actually have a fully functioning IC inside that house a private encryption key (basically a PGP key) that is very difficult to extract even if you physically dismantle the card. When you use one of these cards, the reader activates the circuit and sends a message. The card “signs” that message with the secret key and transmits it back, and the reader verifies the signature with the stored public key that corresponds to that card’s private key. Even if a thief stole your wallet, it is unfathomable for the average thief to have the means to get the data off your card, and even if he did, you should have had it canceled by then.
Google around for smart cards, PGP/GPG encryption, etc. if you want more info about this technology. I personally don’t like it because SMART cards are orders of magnitude more expensive to create, and have technical limitations such as comparatively small MTBF ratings and a general physical weakness, especially in an environment as adverse for electronics as a wallet.
Anything with a magnetic strip works in the outside door. I use a supermarket “discount card” and never had issue. Since anyone can use an atm (i.e. Bank of America card holders can withdraw from a Citizens ATM, etc), banks don’t care what card gets swiped in the door. The door security is just one of those false sense of security mechanisms used by the banks.
Hmm.. I never thought about it that way. I have to try this next time.
@Dave
Too right. I’ve used my driver’s license, a gas (discount/shopping) card, a pool pass card and a few other things. False sense of security is right. anything with a mag stripe will let you in.
I’d be careful what I tried to use for indiscriminate swiping. Some cards may have just as much sensitive info on that magnetic stripe as your bank card would.
@EJ, good point! I’m always surprised many don’t think of NOT swiping anything at all and instead find a different ATM. While there is always a convenience versus security factor, it’s amazing to me how many people consistently go for convenience without ever thinking about any possible consequence. To me it comes down to laziness of thought. People don’t want to think about it. It’s like we’ve been conditioned to be this way with all these modern day conveniences. I see this type of behavior in various facets of life. I admit I struggle with it from time to time, but make a conscious effort to be vigilant and not fall into the lazy thought trap. The old axiom “An ounce of prevention is worth a pound of cure” is a good one to live by. 🙂
Wow I did not know that! My bank you have to swipe outside to get in and use the machine but it is all glass and well lit. Still .. it is after hours and this side of town not a lot of cops so .. I think I will stick to day time hours.. now.
Actually some banks in my country disabled that since some homeless people used some discount cards to get into the “protected” zone to sleep at night. Altought this was a while back, don’t know if they keep doing it!
Firstly, cool trick. I never thought about how the outside door was authenticating the mag strip. I guess those old hotel keys will be useful after all.
Secondly, since the bad guys seem to be getting card info from the outside door, I wonder if anyone has ever thought of using an overt camera pointed into the anti-chamber to get the PIN info. You could make the camera look legitimate and as if it belonged in the area. A PTZ hood could even conceal the direction the camera was pointed. If positioned correctly and with the right lense, the bad guy would never have to enter the premises.
Has anyone ever heard of someone using a legitimate looking security camera to steal PINs?
This reminds me, last year we had someone try to 3D print an ATM skimmer with us: http://i.materialise.com/blog/entry/attention-atm-skimming-device
3D print crime FTW.
Wow glad your company was on the ball! Now I see how the criminals get their hands on such stuff in the first place!
This is one reason I only use drive up ATM’s after hours or use an inside one only during business hours, and in either case preferably ONLY at my local bank branch. I’ve never liked those inside ones that required swiping a card to enter. Beyond the risk of the door reader being compromised and skimming your card info, once inside, you’re a sitting duck for a bad guy to corner you and demand your money or threaten you with violence. It also provides them cover to install these skimming devices. In comparison, a good outside drive up ATM, you’re in your car and can use it to make a fast break if you feel threatened in any way. That’s also why I leave plenty of space between my car and the one in front and constantly scan around for anything out of the ordinary (security starts with awareness, right?). Also, a good drive up ATM is typically very well lit and easily visible from the street where passersby and/or law enforcement can more easily spot something amiss. The only other time I’ll use an inside ATM after hours is at work where our buildings are secured 24/7 by company security staff. Even then, I’m checking out the ATM and surrounding area for anything amiss.
Gee, you sound mighty paranoid. I’m glad I’m not living where you are. It doesn’t sound like a very nice neighborhood!
A healthy cynicism is more like it as well as a product of my ISTP personality type. 🙂
http://en.wikipedia.org/wiki/ISTP_(personality_type)#Cognitive_functions
Btw, I live/work in a middle to upper class suburb, nothing considered bad security wise.
To add more fuel to the ‘skimmer fire’.. this article from the Washington Post..
ATM skimmer investigated in Md.
http://voices.washingtonpost.com/crime-scene/baltimore/atm-skimmer-investigated.html
Wait until the crooks figure out how to do the PayPass proximity thing from 100ft away… Can already hear the card companies going “Oh, how should we have known that you DIDN’T buy ice cream for 49.99$ in Kirovograd today?”
All you have to do is report the unauthorized transaction. YOu are protected by Regulation E.
If you need money, write a check payable to ‘CASH’ and use the drive-thru window (where available), thus avoiding the ATM completely. Of course, this is only good when the bank is open.
My bank doesn’t have that and even another bank that does have “drive-thru” there is no window but an ATM there..
I’d say to prevent them skimming your card with the access door to use something else instead of your debit card. But then .. at the same time they could still be compromising the inner ATM …
And to think my family would rather use the ATM instead of doing online banking…
I have to admit it is a clever bit of sideways thinking, the second I read what they were doing I laughed as I thought “Why did I not think of that…”
My excuse is I’ve never used one and only seen a few, so never realy thought about it 8)
Now the next obvious question is one of “social engineering”. That is,
Could you actually fritz the door lock and put up a keypad with some little note saying “Due to recent vandalisum… … type in valid PIN” or some such and actually get people to type their PINs into it…
As far as I’m concerned, the banks are responsible all losses in these sorts of cases. There’s no reason we don’t have strong crypto cards that don’t reveal their secret, but instead do a handshake that can only be used once. We have the technology, the banks are just refusing to use it.
Banks refuse to use it because the technology is largely theoretical. If there is no infrastructure to support those types of transactions, they simply can’t be used. Further, customers would resist it. If you’re as old as I am, you’ll remember that the check card took decades to get buy-in from the general public.
And yes, banks are responsible for these types of losses, provided customers report them. We literally pay out millions on these types of counterfeit transactions every month. Keep in mind,however, that there are more theives than there are bankers and they are way ahead of us all the time.
[quote]Banks refuse to use it because the technology is largely theoretical. If there is no infrastructure to support those types of transactions, they simply can’t be used. Further, customers would resist it.[/quote]
That is not true. All over Europe chip cards providing exactly that functionality is wide-spread. I think the only reason the magnetic stripe is still in use is due to compatibility with countries that are not chip-based, yet. Strangely one of these countries is the US.
Yeah in my area it seems more and more things are getting chips in it. Some refuse to go that route (worried about what information is being kept on the chip as apposed to the strip as the chip can hold more and worried where this will lead in the future of no privacy .. that is what I have read are people’s worries about chips) but in my city there are at every store now new debit card readers that all support the ATM cards with chips in them. You stick them in the bottom instead of swiping the card on the side. It seems the future means all cards will be chipped and no magnetic strip.
Chips have their own security concerns. The chips can be read from a distance – no swiping necessary. Further, chips can be conterfeited as can anything else. The magnetic strip only contains limited information anyway. It’s the card number, plus authentication processes that provide the security and accountability.
Keep in mind also that chip-driven devices are widely used in Europe largely because they use many more stored-value cards. Checking accounts are pervasive in America, but much less common elsewhere in the world, thus apples and oranges.
In terms of infrastructure, a single bank can’t adopt a new tech without near-universal availability to vendors. We simply don’t have that infrastructure to support chips. We also lack an incentive to do so.
There is also the small matter of weighing costs and benefits. This post might possibly exaggerate the losses to customers when in fact fraud rarely harms the customer. By law, the banks carry most of the responsibility for any abuse suffered by their customers. See Regulation E.
> The chips can be read from a distance – no swiping necessary.
No true. Only if a radio interface is implemented. And that is not the case for current chip based credit cards. (It is for new passports, though).
> Further, chips can be conterfeited as can anything else.
No. They are small computers, and the security is based on the chip holding a secret key only known by the credit card and the server at Visa/Master Card /etc. Then encryption is used to verify that the card is genuine. There is no mechanism to get that key out of the credit card. Similar techniques have been used for GSM SIM cards for decades.
You’re not well informed about the situation in Europe. The chip based authentication being rolled out at the moment is not for stored-value cards. Those cards never really caught on. It’s the joint American Express, JCB, MasterCard and Visa system known as EMV. It’s usually implemented as a part of SEPA, the Single European Payments Area.
The use of the word “checking account” itself is an anachronism, as many European countries do not use cheques anymore, relying on electronic means of payment.
Contactless payments aren’t being implemented as a part of SEPA, and they don’t seem to be catching on.
Meanwhile, I’ve been using the chip on my bank card for my shopping on holiday in Brazil. Somehow European and South American countries do manage to implement chip based EFT; in fact, EMV is used in 80 countries.
Your statement that the “card number, plus authentication processes [..] provide the security and accountability” is nonsense; a number does nothing. Only a chip based solution can provide cryptographic protection. If anything, EMV uses crypto that is not strong enough and not open (audited) enough. And especially if contactless payments were to catch on, strong crypto is key. You never get that with a magstripe.
Banks should still eat losses for substandard security, sure, SEPA has regulations like Reg E. too. But a chip is also mandated.
Hello Brian!
Can you send me an email (Vladimir.p.a@gmail.com) and tell me where I can buy those skimmers & Cameras for educational purposes?
Rudely enough no one has responded. To purchase one you must find your local retailer of these fine products. How do you find one? Simple, they all look like this: https://2.bp.blogspot.com/_MDK4-ZCd6y8/TQ0kPMV-8-I/AAAAAAAAA8U/F17Xz3j1VGE/s1600/boris.jpg
Brian has spent a lot of time outlining the threats posed by ATM skimming. But, I do not recall any information ever posted regarding the prosecution of individuals who engage in this activity.
Brian–do you know of any significant prosecutions of individuals who perform these skimming activities?
Just do some google and twitter searches on atm skimmer arrest and you should have no problem finding reports of arrests. that should also give you some measure of how common these are.
The answer is that there are plenty of arrests, although I’m not sure how many of them would rise to the “significant” level. My sense is, mostly those arrested are the guys lower on the totem pole of larger fraud operations. Whether they get them to flip on their higher-ups after being arrested is another story.
How come I never see postings on banks warning about this type of thing? Are they more worried that people would feel that only their’s was compromised and would stay away from their banks if they did this? Most people are not even aware that skimming goes on unless they search for this info online or are on top of reading about the latest scams.
You make it sound like a conspiracy of silence! lol. There is plenty of publicity about many scams, but banks simply have no interest in announcing their losses, particularly when they always make good any unauthorized transactions. As I said previously, there are many more thieves than there are bankers. There are also more crooks than cops and more worry-warts than there are reporters to publicize their paranoid fantasies.
Actually, Kas, I have seen warnings some newer ATMs. I can’t recall, I think it was Wells Fargo, but the machine actually had a placard on the side that showed a picture of the ATM, and said basically “hey, this is what the ATM is supposed to look like. if it looks different from this picture, don’t use it, and call 800-..”
Brian,
I wonder how long it will take the card skimmers to make a poster just like the legitimate wells fargo one, except it has a picture of how the ATM looks with the card reader etc attached and the skimmers just stick it on top of the real one…
The thing is that unless the bank do the physical and information “security” properly (which they usually don’t) then people will continue to get hurt.
The card skimmers are atleast as intelligent as the security people the banks employ (and in many cases a lot smarter) also the skimmers respond to change in days not the months and years the banks take.
Although most of your readers have the smarts to take precautions at ATMs many people don’t for various reasons. The banks don’t help by effectivly pushing people towards ATMs as they cost considerably less than bank staff.
What kind commenting system do you use on this site? Thanks for the info.
Also, the article was informative.
I paid in some cheques into an ATM in my local branch which actually gives you a copy of all the faces of the cheques that are submitted.
Wonderful you might think.
However one batch of cheques I submitted didn’t credit my account. Looking at the receipt I noticed it had a different Branch Address on it to the one which I had visited.
This highlights how sloppy the banks can be with regard to security procedures. BTW my money did get credited after I pointed out the error, but I now refuse any invitations by bank staff to use the machines.
It seems that the low-tech defense is the most effective: cover your hand with your other hand when keying in your PIN, so it won’t get picked up on camera.
MicroSD gumcams/stickcams are significantly less expensive than noted here. They can be found on Amazon for less than $20 and on eBay for under $15. Even more insidious are the ‘808’ keychain cameras that are nearly as inexpensive and look like a Toyota or VW keyfob remote.
2 questions:
1. Any reports of ATM shimming in the US yet?
2. Any reports on RFID skimming in conjunction with PIN cameras?
I have read the article and the comments with great interest. Like many of you, I am an SVP of Ops and a Chief Risk Officer in banking. I spend a great deal of time every day assessing these types of events and attempt to draw lessons learned. In any of these cases, several items really need to be addressed. They are not exclusive of one another and the problem cannot be solved in any “one” way.
First, daily inspection of all ATM is essential. That said, many large FI’s were targed over the evening hours in large metro’s and the thieves did quite well even with six hours of card data.
Secondly, the card issuers and the banks must get on the technology bandwagon. We are behind the technology curve. There are multiple technologies that would stop this type of attack (a couple were mentioned above). Customers, we need you to prode your FI and the card issuers to deploy expensive but necessary preventative technology.
Finally, the legal system must be 100% behind finding, arresting, and fully prosecuting those that are involved in these types of rings. The reason this type of crime continues to grow is the ease of use and the lack of fear of being caught and heavily prosecuted. Our legal and law enforcement system have yet to really put teeth into this type of crime.
When these three items happen, we will see a considerable slowing in the crime. And yes, client education is another key. Leaving, losing, and throwing cards around like candy does not help matters. When the consumer stands to lose more than $50 watch how much more guarded they will become in how and where they wheel out their card.
That said, I don’t blame the consumer. Three major areas need to be addressed first!
Using a credit card to open the door is just a really bad idea.
The card is a token for authorizing transactions, not authenticating you to a door.
The door does not require the full details of your credit card track 2 (unless you are using a bank that charges you for the privilege of using their lobby).
I sell ATM SKIMMER, price 1000 dollars. I can show on webcam. my id on yahoo mesenger is: acces.denied
The thing to do is to equip ATMs with electronic weighing equipment, so they can detect the mass of a skimmer attached to the machine. Use at least two: a sensitive one measuring just the front panel around the card slot, and another for the whole machine, which can be less sensitive.
I sell smallest bluetooth atm head reader with bluetooth receiver. If anyone is interested please contact me at: tmsr206@aol.com
PS: I SHOW ON WEBCAM!