Many fake antivirus businesses that paid hackers to foist junk security software on PC users have closed up shop in recent weeks. The wave of closures comes amid heightened scrutiny by the industry from security experts and a host of international law enforcement officials. But it’s probably too soon to break out the bubbly: The inordinate profits that drive fake AV peddlers guarantee the market will soon rebound.
During the past few weeks, some top fake AV promotion programs either disappeared or complained of difficulty in processing credit card transactions for would-be scareware victims: Fake AV brands such as Gagarincash, Gizmo, Nailcash, Best AV, Blacksoftware and Sevantivir.com either ceased operating or alerted affiliates that they may not be paid for current and future installations.
On July 2, BestAV, one of the larger fake AV distribution networks, told affiliates that unforeseen circumstances had conspired to ruin the moneymaking program for everyone.
“Dear advertisers: Last week was quite complicated. Well-known force majeure circumstances have led to significant sums of money hanging in the banks, or in processing, making it impossible to pay advertisers on time and in full.”
The disruption appears to be partially due to an international law enforcement push against the fake AV industry. In one recent operation, authorities seized computers and servers in the United States and seven other countries in an ongoing investigation of a hacking gang that stole $72 million by tricking people into buying fake AV.
There may be another reason for the disruption: On June 23, Russian police arrested Pavel Vrublevsky, the co-founder of Russian online payment giant ChronoPay and a major player in the fake AV market.
Black Market Breakdown
Vrublevsky was arrested for allegedly hiring a hacker to launch denial of service attacks against ChronoPay’s rivals in the payments processing business. His role as a pioneer in the fake AV industry has been well-documented on this blog and elsewhere.
In May, I wrote about evidence showing that ChronoPay employees were involved in pushing MacDefender — fake AV software targeting Mac users. ChronoPay later issued a statement denying it had any involvement in the MacDefender scourge.
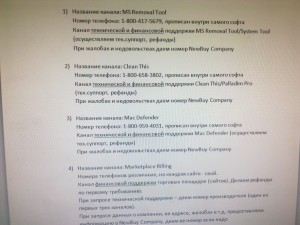
But last week, Russian cops who raided ChronoPay’s offices in Moscow found otherwise. According to a source who was involved in the raid, police found mountains of evidence that ChronoPay employees were running technical and customer support for a variety of fake AV programs, including MacDefender. The photograph below was taken by police on the scene who discovered Website support credentials and the call records of 1-800 numbers used to operate the support centers.
Russian investigators also found that ChronoPay computers support the infrastructure of Rx-Promotion, a rogue online pharmacy program that paid spammers millions of dollars to promote Web sites that were pushing knockoff prescription drugs, including addictive painkillers like Vicodin and oxycodone (Rx-Promotion also appears to have closed up shop following Vrublevsky’s arrest).
Group-IB, a Russian computer-forensics firm that has been assisting the police in their investigation of Vrublevsky, said that his arrest and subsequent searches of ChronoPay’s office symbolize the possible interest of Russian law enforcement agencies in stopping the laundering of money earned in selling counterfeit medicines and fake AV.
“If allegations against ChronoPay are true then we should expect significant decrease of revenues received by cyber criminals in the appropriate segments of black market in the near future,” said Maxim Suhanov, a computer-forensics specialist at Group-IB.
Ridiculously Profitable
Given fake AV’s status as a reliable cash cow, the industry is likely to bounce back rapidly. Fake AV is extremely profitable, in large part because it is easily franchised.
Individual affiliates can quickly make a lot of money. Fake AV distribution networks pay affiliates between $25 and $35 each time a victim provides a credit card to pay for the junk software.
More importantly, fake AV affiliates can outsource the majority of their work. Damon McCoy, a researcher at the University of California, Santa Diego, has been studying the fake AV industry. He found that fake AV can be massively profitable when installed via pay-per-install (PPI) programs. PPI networks contract out the deployment of the malware to affiliates who get paid per one thousand installs (the payment rate varies with the geographic locations of the victim PCs).
McCoy said fake AV affiliates can purchase 10,000 installs of their scareware programs very cheaply. “For 10,000 installs, [the PPI networks] will charge you normally about $900, but if you squeeze them a bit they will go down to $750,” McCoy said.
In an analysis of the fake AV industry released last month, McCoy and other UCSD researchers discovered that fake AV affiliates can expect that one out of every 50 people who have fake AV installed on their systems will pay for the software.
“If you do the math, it’s almost like you’re printing money,” McCoy said. “You could pay the PPI networks $75 to get 1,000 fake AV installs. And if you had an average conversion rate of one in 50, making between $25-$35 on each install, that works out to about 20 sales — or conservatively $500 per one thousand installs. So, you pay someone $75 and you can expect to make four or five times your investment. The economics of this market are ridiculously profitable, and it’s easy to see why fake AV is the go-to method today for monetizing botnets.






Thank you for the article, Brian.
I was thinking some days ago that were about 30 days since Pavel was arrested and wondering if he was released from custody or further detained / charged.
Great work brian , hopefully they have alot of misfits locked up in the cold bar hotel consuming wish sandwiches . Meaning two pieces of bread and nothing between them . In my opinion monies not going to buy there way out of this one top l.e. Agencys involved here . 🙂
“unforeseen circumstances” . Lol its called the element of surprise and the bad guys got captured . 🙂
Mixed feelings. On the one hand, these people need to be behind bars. On the other hand, Russian jail might torture and kill him.
If only this guy could swap places with the guy from Norway…
i want to buy quick heal antivirus..total pc protection….tell me its prize and would u deliver it to my home….
Great article Brian.
Following the money trail always leads to the criminals. I wonder how difficult it would be to identify and shut down the published support phone numbers for these fake AVs.
My Russian is a little rusty, but I wonder if 1-800-417-5679, 1-800-658-3802, 1-800-959-4031 could easily be tied back to the criminals.
Just as a note the 1:50 conversion rate shouldn’t be attributed to me or UCSD, this is the approximate conversion number from the UCSB paper and what the scammers typically claim in their fakeAV affiliate recruitment advertisements posted to underground forums. We haven’t done any research to validate this conversion rate, and as a caveat it might not be similar for fakeAV installed via a PPI based vector.
I agree with the article’s title: “Fake Antivirus Industry Down, But Not Out”, since I find the arrest of Pavel Vrublevsky to be nothing more than a temporary disruptive event on the Fake AV / Rogue Anti-Malware Industry. In fact, I do not think Mr. Vrublevsky will suffer or do much jail time, since he is a connected at the highest levels of the Russian government.
For example, here is a picture of Pavel Vrublevsky (on the right), co-founder of ChronoPay, the Russia’s largest processor of online payments (currently under arrest) with Russia’s Deputy Prime Minister of the Russian Federation, Sergei Borisovich Ivanov (on the left):
http://f8.ifotki.info/org/56e50da471e51571d910b656c1f88b70c7309391348273.jpg
Even if Mr. Vrublevsky never sees the light of day, too much money was made, and can still be made as of today, so somebody else will pick up where Mr. Vrublevsky left off.
Furthermore, the corrupt affiliate distribution channels are all still there waiting until the “payment processing problem” is resolved, once that is corrected, it will be business as usual for the Fake-AV and Rogue-Anti-Spyware makers, and the cash-print-press begins again $$$$$$$ at the expense of innocent people who are be extorted to pay the ransom to the Fake AV poping on their screens across the internet.
Remember, Mr. Vrublevsky was not arrested for processing payments for Fake AV makers, or aiding or abiding them. He was only arrested for attacking his competitor with a DDoS attack to block the Aeroflot airline deal. The Bottom-line is: “The Russian authorities do care about the millions of victims in the US and the EU that were hijacked by these Fake AV makers and their army of affiliates. They are completely indifferent on the nameless people who these criminals defrauded and forcefully invaded their PCs, thus is only a matter of time before the new “King-of-Fake-AVs” will rise, and he will come!”
As long as money can be made, and the Russian Federation’s government does not arrest these people for this business practice, this will never stop, which is good news for the legit AV makers who make a living analyzing, detecting, and removing these threats from individual internet user’s.
спасибо всем!
Hey dial all 3 numbers in the pic Brian posted its all ways busy , at least I have tried . Anyone else have tried calling it . “Very Interesting” . Job well done Brian…
MacDefender was not served or updated after 6/23. Great reporting!
Awww! Pavel Vrublevsky, the gentlemanly criminal? We might miss him! NOT! 😉
I just had a disturbing thought; what if these gangs actually started making an AV that worked; of course it would only remove competitors in their game, but it would be very ironic if they eventually morphed into some kind of legitimate malware company in the end! :O !
Anti-malware – just to clarify.
Great job, Brian. I just noticed that both the UK’s “Guardian” and “Mac Rumors” are citing your excellent investigative work.
http://www.guardian.co.uk/technology/blog/2011/aug/04/apple-macdefender-malware-disappeared
http://www.macrumors.com/2011/08/04/raid-on-russian-firm-may-have-taken-down-macdefender-malware/
Hay’
very interesting article for anti virus computer security system.
I buy Norton 360 at http://www.Teezsoft.com
Cheap and easy
lisamosley: I suspect you picked the wrong place to pollute with your spam. Bad, bad move!
What if the Russian government decided to ‘nationalize’ the fake AV industry for its’ own benefit?
A little additional income to balance the economy…
This is what they were already doing.