The U.S Federal Bureau of Investigation is warning about an uptick in online extortion scams that impersonate the FBI and frighten people into paying fines to avoid prosecution for supposedly downloading child pornography and pirated content. This post offers an inside look at one malware gang responsible for orchestrating such scams.
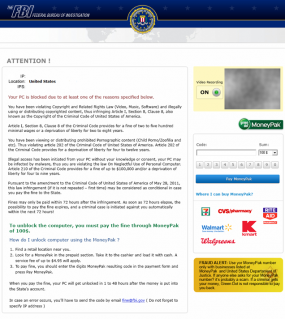
In an alert published last week, the FBI said that The Internet Crime Complaint Center — a partnership between the FBI and the National White Collar Crime Center — was “getting inundated with complaints” from consumers targeted or victimized by the scam, which uses drive-by downloads to hijack host machines. The downloaded malware displays a threatening message (see image to the right) and blocks the user from doing anything else unless he pays the fine or finds a way to remove the program.
The FBI alert said the attacks have surged with the help of a “new drive-by virus” called Reveton; in fact, Reveton and its ilk are hardly new. These types of attacks have been around for years, but traditionally have targeted European users. The scam pages used in the attacks mimic official notices from various national police or investigatory agencies, corresponding to the country in which the victim resides. For a breakdown of these Reveton-related ransomware scam pages by country, see this comprehensive gallery set up at botnets.fr.
Reveton.A is blamed in these most recent attacks, and the FBI said it appears Reveton is being distributed in conjunction with Citadel, an offshoot of the ZeuS Trojan that I have written about on several occasions. It is certainly possible that crooks are using Citadel to deploy Reveton, but as I’ll illustrate below, it seems more likely that the attackers in these cases are using exploit kits like BlackHole to plant both threats on victim PCs.
INSIDE A REVETON MALWARE GANG
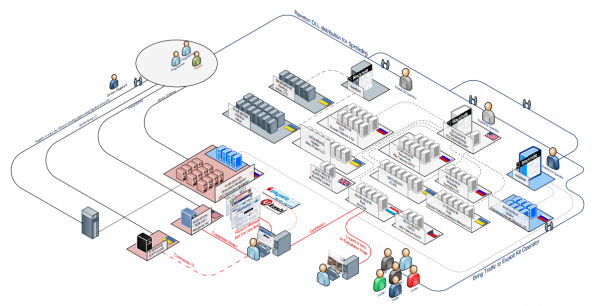
At least that’s the behavior that’s been observed by a ragtag group of researchers that has been tracking Reveton activity for many months. Some of the researchers are associated with botnets.fr, but they’ve asked to remain nameless because of the sensitivity of their work. One of them, who goes by the screen name “Kafeine,” said much of the Reveton activity traces back to a group that is controlling the operation using reverse proxies at dozens of servers scattered across data centers globally (see this PDF for a more detailed look at the image above).
Kafeine said the groups involved in spreading Reveton are constantly fine-tuning all aspects of their operations, from the scam pages to solidifying their back-end hosting infrastructure. The latest versions of Reveton, for example, serve the scam pages from an encrypted (https://) connection, and only cough up the pages when an infected machine visits and sends a special request.
Some readers may have a hard time understanding how such schemes could be successful. To those folks, I say consider the lucrative operations of the once-mighty scareware industry, which similarly hijacks infected machines with warnings about malware until the victim relents and pays for some worthless and fake cleaner program.
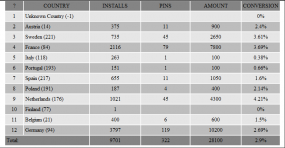
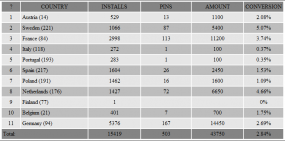
Kafeine shared a couple of screen shots of two similar and recent ransomware scams (not Reveton-related) targeting European users that shows just how successful these scams can be. Both of these images were obtained when security researchers stumbled upon statistics pages maintained by the criminal groups running the scheme.
The one on the right, for instance, shows that the attackers managed to get their malware installed on 2,116 PCs in France, and of those, only 3.7 percent — 79 victims — opted to pay to rid their machines of the ransomware. But those 79 victims each paid $100, earning the miscreants 7,800 Euros.
That’s the haul from just one country; bear in mind that this stats page shows the total take from a single day (May 17, 2012). According to these stats, at least 322 people from all countries they ran the scam in opted to pay the ransom that day, earning the attackers more than €28,000 (~$34,500)! The next day (the screen shot below left), the miscreants earned €43,750 (~$54,000).
Unlike scareware scams, ransomware schemes do not rely on credit card payments from victims — a key pressure point for squashing affiliate programs that help spread this crud. Most previous ransomware schemes have used alternative payment systems such as Ukash and Paysafe. The Reveton attacks that spoof the FBI instruct victims to pay their “fines” via MoneyPak, which allows people who don’t have bank accounts to send money and pay bills at participating businesses. MoneyPak cards are available for purchase at Wal-Mart, CVS and other retailers, and can be reloaded with cash, and can be used to send money to PayPal accounts, prepaid credit cards, and to pay bills for some cell phone companies and DirectTV.
I mentioned earlier that most of these Reveton attacks that have been tracked so far used versions of the BlackHole exploit kit to deploy the malware. These are kits that are stitched into hacked or malicious Web sites, so that all visiting browsers are checked for a variety of insecure, outdated plugins, from Flash to Java to Adobe Reader. Browsers that are found vulnerable will be handed a Trojan downloader that fetches Reveton and most likely a copy of the password-stealing Citadel/ZeuS Trojan.
Kafeine and his fellow researchers recently gained access to one of the three main BlackHole exploit panels used by a Reveton malware gang. The screen shot below shows the BlackHole administration page; in the upper left portion of the image, we get a sense of how much traffic these crooks see on any given day. It shows that in just one day, the exploit kit was sent more than 187,000 potential victims, and that more than 11,000 of those were successfully seeded with Reveton. The “exploits” stats in the upper right portion of the image show that, once again, insecure and outdated installations of Java remain by far the most popular vehicle for exploiting PCs.
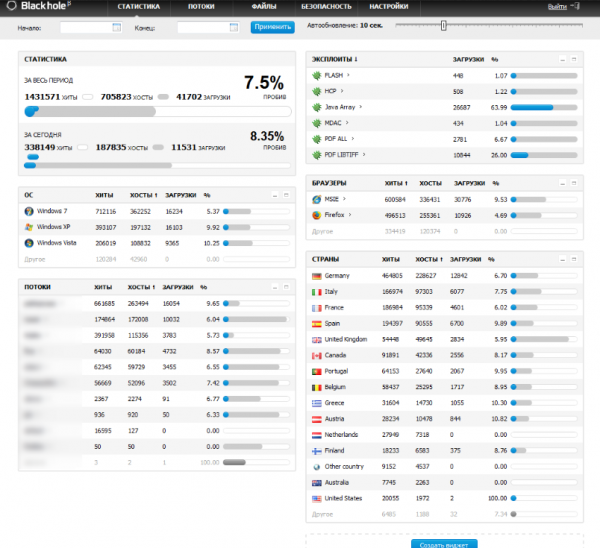
A recent screenshot of a BlackHole exploit kit panel used by a group spreading Reveton. Source: Kafeine from botnets.fr
A number of Web sites include instructions for removing the Reveton malware without having to pay the ransom (here’s one example). But it’s important for readers to understand that if you have been hit by a ransomware attack, the ransomware component is almost certainly just the most visible of the threats that reside on your system. For one thing, Kafeine said, the latest Reveton versions will steal all passwords stored on the victim’s PC. What’s more, the FBI’s report indicates Reveton is being bundled with Citadel, which is an extremely powerful and advanced family of malware that can be quite difficult to remove.
Attacks such as Reveton illustrate the need to have a solid plan for backing up your data, because the surest way to clean a machine infected with the likes of Reveton is to completely reinstall Windows (from the Master Boot Record on up). The most advanced ransomware threats (the subject of a future post) will steal your passwords and then encrypt all of your important files before demanding a ransom payment.




The crooks misspelled “zoophilia” 🙂
Sure, everyone reading this infosec blog knows they should keep their software and plugins up to date at all times, but the unnerdy masses have no clue about that stuff. If we are ever to really get a handle on the explosion of malware and variants, the publc at large must be steered toward a free-software based operating system where updates occur automatically.
Actually, if we’re ever going to get rid of this, we need to change the default security posture of operating systems from running any arbitrary executable to only running those on an explicit approved list (AKA “Application Whitelisting”).
Problem is, it’s going to be really hard to agree upon who maintains that list.
I doubt that would work, problem is the people will be using whitelisted apps when the exploit happens, then the code might be able to get that list and/or infect the OS.
A permissions system could work, defining how much access each app has e.g access to other processes. Problem is, every program would have to be coded and recompiled to comply (an extra error check on all the API you use), code added to the O/S’ API would make the API slower.
Even then there will probably be holes in the system itself, or something else that gives access where it shouldn’t be.
And I decree that this free operating system have a mascot that is an aquatic, flightless birds living almost exclusively in the southern hemisphere. All malware shall be eradicated and cyber criminals will cringe and cower. And there shall be peace…..
Yes, OR…we could continue to recommend software that helps remove the lazy factor, which frankly will always be there. Secunia’s Personal Software Inspector and FileHippo’s Update Checker work pretty darn well in that regard.
Yes OR… they could buy a mac 😀
Someone has had their head buried in the sand for a few years.
I have used Heimdal from CSIS, and it also does the trick. If one opts to pay for the agent it also ads malware protection, while it does patch management in the free version.
https://www.heimdalagent.com/en/home
How true Brian;
File Hippo has stopped alerting on limited accounts, and unfortunately I’m typically remiss in checking the administrator every day. One good thing, is that Secunia PSI v. 3 does attempt to update your apps automatically even if you are working on the limited side. So far, most of the time, it is successful(at least in Vista x64).
It never alerts me to this; I am relying on Winpatrol to let me know the update is occurring. Secunia will alert me if I need a manual update though. I’m surprised that PSI has almost kept up with File Hippo on timeliness lately. The update checker used to beat PSI by up to 5 days occasionally; I’m not so sure it does anymore.
When Winpatrol barks, I check the program list in CCleaner, and just assuredly the version of the target application will reflect the proper updated version number. I’m also amazed at the many applications Secunia now tracks!
I NEVER cease to be amazed how many times Secunia catches Microsoft Update with its pants down, for not updating something that was required. Redmond has become a fail more often in this area. It is getting to be, that I just don’t trust MS update anymore; I’m constantly double checking with various utilities to see what was neglected.
Fifty grand a day… I’m definitely in the wrong line of work… 🙂
Even if these guys get caught and do ten years in the joint, at this rate, it will be worth it. Most crims do time and the net profit is less than minimum wage… The average bank robber in the US gets maybe $4,000 (in the UK, $20,000). After an average of four robberies, he’s usually caught.
If these guys can run this scam for even six months without getting caught, they will gross maybe 10 million dollars… Even after paying their lawyers, they will live well in the joint on that commissary budget… 🙂
This is why computer crime will continue to get bigger and bigger. The profits can be enormous and especially so compared to the overall risk factor.
This has implications for end users, home and business alike. It means computer crime is not like other security threats (fire, disaster, etc.) or other types of physical crime (burglary, mugging, etc.) It is far more ubiquitous and will become more so. One computer criminal can attack literally hundreds or thousands of victims whereas one burglar or mugger is pretty limited in his victim count due to sheer physical limitations.
Some insurance companies are coming out with “hacking insurance” and some businesses are falling for this idea, thinking it is cheaper than actually trying to do real security.
The problem with that notion is that as computer crime becomes more prevalent, the insurance companies will start noticing more and higher payouts. Then they will do what they always do – raise the premiums to the point where it’s profitable again. OR they will start demanding that businesses prove their security is adequate before issuing policies, as they do with many high-value clients.
Which means businesses will start paying what they might as well have paid on security in the first place, PLUS high premiums. They won’t win that game.
I continue to hope for the increased use of separate Administrator and Limited User accounts.
For example, in the case of the Master Boot Record (MBR), a limited user account is prevented from modifying the MBR.
I realize that Limited User accounts can still be infected with malware. But this limited infection is often easily resolved by the many anti-malware programs available.
Use of separate Administrator and Limited User accounts is very important. If all users followed this procedure, then malware such as the Reveton would have a much smaller effect.
Use of separate accounts has been standard procedure in business environments for decades.
Because there aren’t uac exploits.
In addition to backing up data daily to an external drive, this is exactly why everyone should have a pristine “system image” that can be easily restored via a rescue CD or USB.
In my case (I use a relatively small 50 GB partition), restoring the system image takes all of six minutes.
It takes me 20 minutes on a 500Gb drive. I use a third party free image backup program, and the generic Windows for Vista file backup utility for incremental. If I had Win7, I’d use their image backup, but I still like regular file backup for incremental restores; so that I can contain the date of infection. One never knows when the first compromise happened.
“Restoring” the system after infection will not help much if the keyloggers / password stealers were running for a while. Thus it is more important to identify all the infections coming with Reveton (which is relatively easy to remove compared to Gimemo or other ransomwares) rather than reinstall right away. If there was a banking trojan too, one should check their account on safe PC right away, and change the passwords.
If your computer is completely locked up by ransomeware , it’s pretty obvious that a multitude of malware is possibly installed and running on the machine. If your concerned about what specific malware is installed, use the rescue CD/USB to make another image of the infected system prior to restoring the pristine image. Then, the second image can be mounted and scanned in isolation.
Actually, the locking is done by Reveton itself, so while more malware is possible, it is not always the case. Fixing PC is secondary to assessing if there is possibility sensitive data was transmitted to scammers already.
While using disk images is perfect recovery strategy (if one does them regularly enough and ensures that they are really clean), they might give false sense of security against banking trojans and spyware which do not cause easily detectable symptoms.
Good enough security can be achieved only using combined approach only.
This is the problem with doing system images: 1) they have to be done on a known clean machine, and 2) they go out of date frequently – which leads to making updated images which might have already been compromised.
The only real solution is to do a complete reinstall of the OS, apply all updates to current, then take the image. This should be done periodically, maybe every few months.
OTOH, if you’re pretty sure your machine is clean when it’s time to do a new image – meaning you’ve done full scans with both AV and antispyware tools and you’re fully patched and you’ve seen no evidence of any compromise to this point – you can either just take a new complete image or an incremental image using one of the programs that do incremental image backups.
Image backups AND data backups are BOTH necessary.
“The only real solution is to do a complete reinstall of the OS, apply all updates to current, then take the image. This should be done periodically, maybe every few months.”
Well stated! That’s exactly what I was recommending in my original post, i.e., a pristine system image (a.k.a disk image), which shouldn’t be confused with a “system restore point.”
That’s good advice. It’s very similar to what I do. I advise the backup procedures be started when the PC is first purchased, otherwise reinstall OS or restore to factory state. Here’s the process for other readers.
1. Purchase PC or get it to factory state.
2. Before online, strip any unneeded bloat/crapware & turn on all security features/services.
2-1. Be sure to strip Java and Adobe Reader
3. Get online & run Microsoft’s updates. Do nothing until these finish. Reboot as necessary.
4. If you bought security software, install it now & update it immediately.
5. Get the needed third party apps. Good browser & security plugins first. Then Foxit PDF, security suite, backup app, DivX, VLC, Office/OpenOffice, 7-Zip… and so on.
6. Run the update procedure on all of them.
7. I also say run each once to get past the “first use” stuff, do file associations, set long term settings, etc.
8. Get offline & immediately do a full backup. Ideally, your backup software can also split the backup into pieces that can each fit on a DVD. This ensures malware can’t infect backup on, say, a USB hard disk.
8-1. If your software supports it, create a boot CD for the backup system so you can do a backup or restore without loading windows. It’s safer.
(Also, OS’s do weird stuff behind the scenes sometimes. Or all the time, depending on who you ask. Making sure the OS is “off” by using the boot disc might eliminate any problems the OS might cause that have nothing to do with malware & corrupt your backup anyway.)
Regarding OS vs Data, I agree with RSH that it’s best to keep them separate. Many keep them on separate partitions. Put the OS & main apps on one, then your music etc on the other. I typically do a disk image style backup for the OS partition & a file-level backup for data. There are some good free tools available, with step by step guides online, for creating partitions. It’s easy enough for a non-expert to do. Just don’t change it after making a disk image backup. 😉
Maintaining the “Good” Backup. It’s a pain, but here’s a safe procedure.
1. Backup all Data to an external hard disk or something. Remember bookmarks, contacts, whatever.
2. Make notes of any important settings you need to manually set later.
3. Use one of the boot CD’s to boot into your backup software. Recover your last good backup from it. (Preferrably from DVD’s)
4. Microsoft/Windows Update first. Then update 3rd party software.
5. Install any new software & manually apply recent settings.
6. Import bookmarks, contacts, etc.
7. Use boot CD to make a new full backup from this system.
The idea is you start in a known “clean” copy. Apply all updates to make it safer. Then, import and set everything to bring it up to recent situation. Then, make a full backup again.
Sounds durn near ID-dentical to the procedure I use. Like you said, it may seem like a pain until you have a disaster, and then recovery seems like a breeze, and you wonder why everyone hasn’t been doing it all along.
I separate image by external drive, and file incremental backups by a second internal drive. Sometimes I repeat using DVDs to spread out disaster recovery chances(fire, flood, etc.) Since the recovery CD can read anything plugged in later, I’m not as worried about malware knowing the jig is up. I can always nuke the secondary drive from space after the image is restored.
A local medical practice (not a client of mine) informed a family member that they had been victims of a ransomware infection on their EHR server in the past month. FWIW, this was in the USA
I agree with previous posters – small system administrators really do need to be aware of and implement the principle of least privilege. In this specific case, the victim shared with their customers that it was their main data server specifically that was compromised – a machine that should be isolated from the internet to begin with
Kudos Brain, now you’re on the right track. Forget script kiddy miscreants and their ddos tools. The big game these days is ‘Lockers’, *swears he mentioned this a little bit earlier.*
I never realised the ransomware was so lucrative! Insightful article, definitely going to share.
I was at a friends house when their laptop got infected and she freaked out, ready to go and do whatever was asked from her from this “official notice”. If I hadn’t been there to talk her down and fix it she would have paid up. Weirdly she’s one of the most sensible people I know?!
The payment systems these scamsters use in the ransomware force people that aren’t tech savvy into using a product they didn’t want to use and then gives them a bad name for example the “Paysafe Virus” or the “Ukash virus”, both decent enough products but now associated with the word “virus”. So in this case the scammers didn’t get anything from her machine and now she’ll never use an e-money product because of her experience. Hopefully a solve can be found once and for all!
Typo in second sentence in third paragraph.
“These types of attacks have been around for yeas, ”
I just got done cleaning a windows 7 computer which had a different version of the ransomware. The warning screen had white text on a black background and wanted $200. The computer had multiple Trojans / root kits including Alureon, Sirefef (ZeroAccess) and rootkit.boot.pihar.c. There was an old version of Sun Java, which probably was an entry point.
The computer probably got infected with malware in mid-June at a hotel in Florida. It started running strange after that. Software from Play Pickle, a fake game site, known for malware, was installed at some point. The FBI Ransomware didn’t appear until early August.
I was able to clean the computer using Bleeping Computer’s guide at http://www.bleepingcomputer.com/virus-removal/remove-fbi-monkeypak-ransomware, which recommended EMSISoft’s Emergency Kit at http://www.emsisoft.com/en/software/eek/. I also used Kaspersky’s Root Kit Killer TDSSKiller at http://support.kaspersky.com/faq/?qid=208283363.
Lastly, I installed Secunia PSI to get everything up to date.
People should be careful with TDSSKiller. I used it on a client’s netbook and it utterly destroyed the partition table AND the file system… Might have been a fluke, but it made me paranoid.
Also, they update that thing frequently (a new version out today), so make sure you have the latest version.
I’ve never had problems using TDSSKiller, so I’d have to say your experience was a fluke… unless it was a fake experience and you want to smear TDSSKiller because it’s too effective against malware you’d prefer to keep running on machines!
I use TDSSKiller through the Kaspersky Rescue 10 CD and download it from their site using the embedded browser. TDSSKiller is know for not working for everything, I couldn’t get it to work on a backdoor infection just the other day. That doesn’t mean I’m going to give up on it – that’s what version update support is for.
This is my favorite Reveton article on the internet. Even the comments are educational on how to beef up the security on a Windows system to battle this advanced form of garbage. I have been fighting malware on Windows machines for years but have never seen anything as sick as the Reveton malware. I would go as far as to say this malware has grown my curiosity in computer security. After cleaning it once it evolved within a few hours and was sending out Windows message boxes claiming there was a problem with the ISP’s intrusion detection system. Doing a system restore does not kill the keyloggers and other crap it spews into your computer. The case I dealt with yesterday rendered the system unavailable to even boot into safe mode.
Sometimes, their isn’t actually anything wrong with the MBR files, as far as corruption, or in-operation goes. You can test every one of the boot processes and pass with flying colors and still not successfully boot the computer. It is always possible that something is simply blocking the boot process. This is where nuking the drive from space is usually effective – unless it is a zero day exploit, and then you may have to wait 24 to 48 hours for a definition to arrive for you rescue CD.
I usually just DBAN the drive and start over, but if time and the client permit, I try to learn something along the way.
>I’m definitely in the wrong line of work
Crime definitely pays. It doesn’t always pay indefinitely.
My PC was effected by Reveton a few days ago. I could not do anything except removing the hard drive and hook it up to another computer via a USB prot and run Symantec. Unfortunately, Symantec did not detect the virus but found other trojan horses instead.
I reinstalled the defected hard drive back to see if the ransomware disappears; of course, not. I then discovered that if I do not connect my computer to the LAN I’m able to access my files normally. This is good for those who do not have a second computer to be able to retreive their important files before going to the extreme of restoring their PC to the factory cofiguration.
I later found interesting Reveton removal instructions at
http://www.f-secure.com/v-descs/trojan_w32_reveton.shtml.
Good lucks to those who were victimized by the geedy smart crooks that use their talent the wrong way.
Symantec is one of the WORST antivirus in the world… Of course it won’t find anything. I’d recommend Eset Nod32, or Kaspersky they are updated at least 10x quicker than the lazy bafoons over at Sym.
Er no it is not “the worst in the world”, far from it as a matter of fact (read testing against present day and historical malware).
Granted NOD32 and KAV do test better though. I suspect nowhere near as better as you might believe though.
Fanbois eh … prone to wild exaggerations.
Neej once again, as usual you are terribly wrong. Symantec is the worst antivirus, with the exception of Mcafee at a close 2nd of major brand antivirus.
My definition of major means it pops up on scan4you(dot)net or virtest(dot)com.
I work closely in related field to malware un-detection… That is taking a detected file and returning it to a state where zero antivirus on scan4you or virtest detect it.
I can tell you on the topic of new threats Eset will catch a clean file (0/35) usually within a day and tend to do well at generically detecting all versions (using different stubs). Kaspersky will also tag within a day but tends to not gen that often. A close 2nd/3rd at catching new threats would be Bitdefender/Avast.
I could even go into the patterns of what certain Antivirus favor in tagging (length of encryption key, size of encrypted file in resources, location of encrypted file in stub, hell even Eset likes to be annoying and go after Compile settings every once in awhile). To actually do this and give you a play by play per each antivirus would be an entire research paper of its own.
IF, let me stress the IF part of this statement Symantec decides to care about a threat it may be days or even a week later (long after it has done the intended damage). You REALLY have to gain PR before Symantec bothers with a sample. Their antivirus may look pretty with bells and whistles but when it comes to keeping up with new threats they are about as slow as you can get besides not having antivirus at all. To exaggerate my point, I can dig-up samples from MONTHS ago that nearly every Antivirus will detect but Symantec never bothered to even look at.
You should’ve learned by now if I take the time to write a comment there is a extremely good chance it is backed up by experience –Not just some nonsense I read on the internet. I’m talking from battling against antivirus for a few years now… not from some nonsense tests put forth by antivirus companies (quite possibly the last place you should be looking to see how they compare since they created it).
Kindly get lost, and stop replying to every comment I post with your incorrect information. You really do not know what you are talking about, anyone knowledgeable on the topic knows that already.
I only know what happens to me in my honeypot lab. Norton used to let a lot of bad stuff through after 2004, but when I tested NIS 2010, the PC was clean every time. None the less, I still consider it in 4th place at best, behind ESET, Avast, and Kaspersky.
I’m only talking about viruses and worms though; one should have good anti-malware alongside the best AV also. Like MBAM, SAS, and Emisoft.
I have ESET NOD32 & still got this virus
I look at this “ransomware” as malware, and maybe not so much as a virus. Some may not say it fits the definition at all. You cannot rely on one product to do it all. However, I believe ESET has an anti-malware module to go along with its AV. They are one of the few that separates the various functions by modules in their suite products.(Of which I consider this as superior) I’ve never tested their all in one suites; but you can bet it is better than just having the AV alone.
Why do I feel inordinately smug for successfully insisting that my family use Linux?
(Yes, yes, yes: nothing is invulnerable, but some things are a metric train load less vulnerable than others. OTOH, poorly configured Linux servers seem to be pretty open to infection by rootkits via PHP.)
37.58.64.0/18 is actually Softlayer Amsterdam, not Ukraine
46.30.42.0/24 is also in the Netherlands, not Russia
50.7.224.0/19 is in FDCs Czech Republic facility, not USA
97.170.136.0/22 is in the USA, not Czech Republic
31.148.144.0/24 is in the Netherlands, not Russia
Most of the PI ranges seem to be registered by Alfa Telecom (ip-as.ru) which seems to be mainly used by German based cybercriminals for their IP needs (The russians use jump.ro – never RIPE LIRs in Russia or speaking Russian)
Infium is known as Warez host in the German internet, but not as botnet provider – so i guess the servers there won’t survive long.
Same with ITLAS, which is actually a Russian hostingprovider that does NOT like botnets at all (send me a mail for contact, don’t want to post it public).
Just my 2 Eurocent 🙂
Hello William,
The Hosting provider/Country part of the map was feed using data from whois origin asn.shadowserver.org.
I do not have a deep knowledge on Hosting providers.
Ip range are valid.
Brain, you have some pretty significant errors/typo/incorrect information in this blog post…
At first glance one would assume the “Conversion” meant percent of installs that yielded pins. However unless these guys are using servers that don’t know how to count properly it is not very difficult to see this is not the case.
For example from your first screenshot:
From Austria there was 375 installs and 11 Pins so the % of installs which yielded pins was 11/375 or 2.93% which != 2.4% found in the “Conversion” field.
From Sweden there was 735 installs and 45 Pins so the % of installs which yielded pins was 45/735 or 6.12% which != 3.61% found in the “Conversion” field.
From France there was 2116 installs and 79 pins so the % of installs which yielded pins was 79/2116 or 3.73% which != 3.69% found in the “Conversion” field.
…
and so on, none of the %s line up with a percent based on the # of installs that yielded pins for any given country.
Then the question is left to ask, what is this mystery % all about? And the answer: Many people enter fake pins instead of paying to unlock. If you have never looked at a panel like this before (it is common to have a % or total # of pins that work out of submitted pins) then it would be easy to assume otherwise.
Now that you understand the “Conversion” tab stands for a percent of valid pins out of all submitted for that country see below.
For the first day in question there was a total of 28,100 EUR recorded this would only be the income for that day if EVERY pin was valid. However, you can see to the right of the “Amount” field is the “Conversion” field — None of these #s are near to 100%. The final “overall” conversion rate was 2.9%. This means the profit for the day in question was 2.9% of 28,100 EUR (IE: 814.9EUR).
Looking at the second screenshot the total for the day was 43,750 EUR, but with a 2.84% conversion rate. So only 2.84% of 43,750 EUR or 1242.5 EUR was the income for the second day.
There is also another error in this post where you talked about the victims from france. See Below…
“malware installed on 2,116 PCs in France, and of those, only 3.7 percent — 79 victims — opted to pay to rid their machines of the ransomware. But those 79 victims each paid $100, earning the miscreants 7,800 Euros.”
If each victim paid $100 that would be $7900 which is 6386.41 EUR (not 7800 EUR). If the locker was ran on *EU* systems it will ask for 100 EUR, but if on *US* 100$. You can note 79 * 100 doesn’t add up to 7800. This is because along with many people entering “fake” unlock codes for their computers others will only opt to purchase a voucher worth 1/2 the requested amount or some other value. My guess would be 2/79 only bought 50 EUR vouchers which would explain how the total for 79 vouches was only 7800 EUR.
I have seen this. I used Combofix. It was fully removed in minutes. Nothing complicated at all.
It actually made perfect sense to me and I am really happy to have seen this blog! Thanks man, keep them coming!