Adobe today pushed out an emergency update that fixes at least two zero-day vulnerabilities in its ubiquitous Flash Player software — flaws that attackers are already exploiting to break into systems. Interestingly, Adobe warns that one of the exploits in use is designed to drop malware on both Windows and Mac OS X systems.
 Adobe said in an advisory that one of the vulnerabilities — CVE-2013-0634 – is being exploited in the wild in attacks delivered via malicious Flash content hosted on websites that target Flash Player in Firefox or Safari on the Macintosh platform, as well as attacks designed to trick Windows users into opening a Microsoft Word document delivered as an email attachment.
Adobe said in an advisory that one of the vulnerabilities — CVE-2013-0634 – is being exploited in the wild in attacks delivered via malicious Flash content hosted on websites that target Flash Player in Firefox or Safari on the Macintosh platform, as well as attacks designed to trick Windows users into opening a Microsoft Word document delivered as an email attachment.
Adobe also warned that a separate flaw — CVE-2013-0633 — is being exploited in the wild in targeted attacks designed to trick the user into opening a Microsoft Word document delivered as an email attachment which contains malicious Flash content. The company said the exploit for CVE-2013-0633 targets the ActiveX version of Flash Player on Windows (i.e. Internet Explorer users).
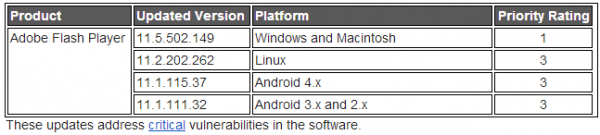
Updates are available for Windows, Mac, Linux and Android users. The latest Windows and Mac version is v. 11.5.502.149, and is available from this link. Those who prefer a direct link to the OS-specific downloads can grab them here. To find out if you have Flash installed and what version your browser may be running, check out this page.
Flash Player installed with Google Chrome should automatically be updated to the latest Google Chrome version, which will include Adobe Flash Player v. 11.5.31.139 for Windows, Macintosh and Linux. Likewise, Internet Explorer 10 for Windows 8 also includes an auto-update feature, which should bring Flash to version 11.3.379.14 for Windows.
Adobe’s advisory notes that the vulnerability that has been used to attack both Mac and Windows users was reported with the help of the Shadowserver Foundation, the federally funded technology research center MITRE Corporation, and aerospace giant Lockheed Martin‘s computer incident response team. No doubt there are some interesting stories about how these attacks were first discovered, and against whom they were initially deployed.




What about Chrome?
@Ben – Did you read the last paragraph?
Thanks. Obviously I didn’t see that before I posted. I searched Ctrl+F but the browser didn’t find “Chrome” as the cursor’s focus was beyond the last paragraph. So I learned something.
I followed Per Soderlind’s instructions and the Flash in my Chrome (24.0.1312.57 m) is 11.5.31.139. It had updated early in the week and I wondered why. Apparently Google was out front of Adobe in releasing the patch.
🙂
Yep, Chrome very often will update its built-in Flash player a day or more in advance of the official patch from Adobe, although prior to this update I experienced a few cases where they lagged Adobe’s advisories. Good to see that they’re back in front!
In chrome, open chrome://plugins/ and search for flash. My Chrome (v 26.0.1403.0 dev) is running Flash v 11.6.602.167
i have the update 11.6.602.161
Believe it or not; I did that, and the Mozilla flash version is listed! (not active X) Apparently Comodo Dragon Chrome and Google Chrome differ on this!? :/
Thanks again for the alert, I just updated. Flash is set to check to see if updates are available, but I guess it does that only once a day or not even that often.
As far as I can tell, neither Safari nor Firefox sandbox the Flash Player plug-in on Mac OS X. Google Chrome on Mac OS X, however, does sandbox the Flash Player plug-in, which is probably why the miscreants targeted Safari and Firefox.
As for Flash content embedded in Microsoft Office documents, Microsoft Office 2010 provides protected view on Windows Vista, 7 and 8, but not on Windows XP and Server 2003. Protected view will prevent flash content from executing by default if the document originates from the Internet or Untrusted Zone, including Outlook attachments, but significantly not from the Trusted Zone.
This Flash Player update for Windows adds functionality that will provide the user with a prompt before executing flash content if it determines that the flash content is embedded in a Microsoft Office document for Office 2007 and earlier. More here:
“Raising the Bar for Attackers Targeting Flash Player via Office Files
http://blogs.adobe.com/asset/2013/02/raising-the-bar-for-attackers-targeting-flash-player-via-office-files.html
Correction: The prompt regarding the execution of embedded flash content in a Microsoft Word document for Office 2007 and earlier will be in an *upcoming* Flash Player update for Windows (IE Active-X).
Once again, you beat File Hippo to the punch Brian – KUDOS!! 😀
i just wanted to let you know that i got this post about flash player 3 times at 4:44pm, 4:45pm, and 4:48pm.
regardless, i appreciate the heads-up about the flash player update.
Me too! It happens once and a while. Apparently the server hiccups occasionally! 😐
Why does it continue to be the case that Adobe (and others…) can’t find these vulnerabilities themselves before they release their junky software, but have to keep asking us to update 3-4-5 times a month? And this has been going on, literally, for years.
It seems to have been a while since last emergency flash update addressing in the wild exploits.
Anyone know how long it took for Adobe to patch this from the time it was reported to time to put out the patch? I hope it wasn’t IE slow.
Hi Chika,
Symantec mentioned that they blocked malicious attachments on the 4th of February in the following link:
http://www.symantec.com/connect/blogs/adobe-zero-day-used-ladyboyle-attack
On February 2nd, Microsoft added anti-malware signatures for the attack. This is according to the following ComputerWorld article:
http://www.computerworld.com/s/article/9236636/Adobe_releases_emergency_Flash_fixes_for_two_zero_day_bugs
In my opinion, this is quite a quick reaction. As mentioned Adobe and Microsoft do share info as part of the Microsoft Active Protection Program (MAPP) as well as providing to anti-malware companies.
In addition Adobe is working on a adding a sandbox for Flash content to Microsoft Office version prior to 2010 to add another barrier for the attackers to overcome before their attack can begin. Details in are given in the following Adobe blog post:
http://blogs.adobe.com/asset/2013/02/raising-the-bar-for-attackers-targeting-flash-player-via-office-files.html
I hope this helps. Thank you.
Apologies for the typos in my comment, the relevant parts should read as follows:
In my opinion, this is quite a quick reaction. As mentioned in the second article linked to above, Adobe and Microsoft do share info as part of the Microsoft Active Protection Program (MAPP) as well as providing it to anti-malware companies.
In addition Adobe is working on a adding a sandbox for Flash content to Microsoft Office versions prior to 2010 to add another barrier for the attackers to overcome before their attack can begin.
“Adobe is working on a adding a sandbox for Flash content to Microsoft Office versions prior to 2010 to add another barrier for the attackers to overcome before their attack can begin.
JimboC, it’s not a sandbox. It’s just a prompt warning the user about executing flash content embedded in Microsoft Office document. Reread Adobe’s blog.
Hi Rabid Howler Monkey,
You’re right, it is only a warning prompt. My apologies for the misunderstanding and for not noticing your prior mention of the same Adobe blog post.
Thanks for the clarification.
JimboC, no apologies are necessary. Look at it this way, it’s more likely that readers will understand what Adobe is up to with embedded flash content in Microsoft Office documents.
Cheers
I didn’t see the e-mail notice from Brian yesterday afternoon but FileHippo identified both the AX and non-AX versions’ updates when I booted up this morning. However, I was truly irritated to discover that the FH links were to 65kb stub installers which would then download and install the associated flavor of Flash with some other crapware — I left a pointed comment to that effect on their related webpage, but as a result my opinion of FH as an honest broker of legitimate updates has declined a bit further.
BTW Brian, there were 3 identical e-mail notices from your site which all arrived simultaneously about 3:42pm Central (US) — did your server have a one-off hiccup or something more problematic which multiplied the addresses to which it issues notices?
Agree about the stubs installers.
I got re-directed to Adobe which as usual prompted me to install the Linux versions whereas I’m looking for the Windows versions for client purposes. That really irritates me because Adobe does not make it easy to override that automatic detection.
I had the same problem with Google Chrome updates, until I found and saved the direct download links for the Windows versions.
There are times when “being helpful” via autodetection is not helpful.
Thanks for the heads-up. I did that. 🙂
Yes,
in reference to Zero-Day, can you explain to me exactly what this means in terms of computer hackers and technology?
Sincerely,
Dana W.
Dana, it just refers to a security vulnerability which the vendor finds out about at the same time as everyone else — when it is already actively being exploited to attack users. It means that the vendor has zero days notice to come up with a fix for the flaw.
New Flash Player 11.6.602.171 version(s) released today, but beware of FileHippo — they are pushing a very small stub installer that will then download the Adobe variant which incorporates the McAfee add-in. Use the direct link Brian provides above to avoid both.
I just make sure and uncheck anything extra the installers try to put on the machine. FileHippo is too handy to not use it. The other updater tools out there, that I’ve tried are worse – especially CNET’s – that dad-gum thing IS malware!! :O
Here lately though, on Adobe, Brian beats my File Hippo by at least three days now – they’ve fallen down lately – but I must admit, these emergency patches are probably out of FIleHippo’s mission capability.
Even MajorGeeks, who are fairly well known to dispense with junk, now have stub installers with many of the handy utilities listed on their site. It is a grim reality of the money making needs of the sites – otherwise they will probably go away.
When FH gives notice that an update to Adobe Flash is available, I make a point of looking at the “technical” tab first to see what the file size of the download for which it offers — today’s was an insulting joke at 64Kb, when the full installer is 15+Mb. Who knows what sort of junk crapware is being tagged with the post-stub download, or whether a user is even provided the option of a choice in its installation?
After the previous FH stub installer posting I made a reasoned explanation in my comment on their site about preferring a full installer file rather than a stub, and got roundly flamed by some fanboy jerk for “whining” about their service that were following a bundling-as-profit-center business approach, so ever since I’ve stopped blindly clicking on the summary download link for any of their notifications and generally just use the source vendor link for a direct download.
Adobe doesn’t easily or readily provide the key master version link Brian usually references in his posts on Flash updates, which I’m sure is intended to drive as many people as possible into downloading what they bundle (McAfee or whoever) so as to boost their own profit center revenues.