Patch Tuesday is again upon us: Adobe today issued updates for Flash Player and AIR, fixing the same critical vulnerability in both products. Microsoft‘s patch bundle of five updates addresses 23 vulnerabilities in Windows, Internet Explorer, and Office, including one bug that is already being actively exploited.
 A majority of the vulnerabilities fixed in Microsoft’s June patch batch — 19 of them — are addressed in a cumulative update for Internet Explorer (MS13-047). The other fix that Microsoft called specific attention to is MS13-051, which tackles a flaw in Office that “could allow remote code execution if a user opens a specially crafted Office document..or previews or opens a specially crafted email message in Outlook while using Microsoft Word as the email reader.”
A majority of the vulnerabilities fixed in Microsoft’s June patch batch — 19 of them — are addressed in a cumulative update for Internet Explorer (MS13-047). The other fix that Microsoft called specific attention to is MS13-051, which tackles a flaw in Office that “could allow remote code execution if a user opens a specially crafted Office document..or previews or opens a specially crafted email message in Outlook while using Microsoft Word as the email reader.”
This Office flaw, which is present in the latest versions of Office 2003 and Microsoft Office for Mac 2011, is already being exploited in targeted attacks, Microsoft said. According to the company’s advisory, this vulnerability was reported by Google. These attacks fit the profile of previous zer0-day incidents, which use targeted email lures and previously unknown vulnerabilities to break into high-value targets.
“When Google encounters flaws that exploit users’ computers, even when the flaws are in other companies’ software, we take strong action to mitigate those attacks,” a Google spokesperson said in response to a request for comment. “Based on the exploit and the way it has been utilized by attackers, we strongly believe the attacks to be associated with a nation-state organization.”
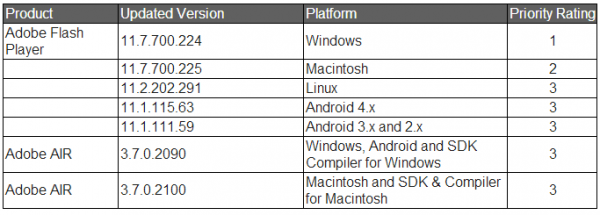
Adobe’s Flash and AIR updates also fix a critical bug that was reported by Google’s security team, although Adobe says it is not aware of any exploits or attacks in the wild against the vulnerability address in its update. The latest Flash version is 11.7.700.224 for Windows and 11.7.700.225 for Mac OS X. This link will tell you which version of Flash your browser has installed. IE10 and Chrome should auto-update their versions of Flash. If your version of Chrome is not yet updated to v. 11.7.700.225, you may just need to restart the browser.
The most recent versions of Flash are available from the Adobe download center, but beware potentially unwanted add-ons, like McAfee Security Scan). To avoid this, uncheck the pre-checked box before downloading, or grab your OS-specific Flash download from here. Windows users who browse the Web with anything other than Internet Explorer will need to apply this patch twice, once with IE and again using the alternative browser (Firefox, Opera, e.g.).
In addition, Adode AIR (required by some applications like Pandora Desktop, for example) was updated to v. 3.7.0.2090 for Windows and Android, and 3.7.0.2100 for Mac OS X. Adobe AIR checks for and prompts you to install any available updates anytime you launch an application that uses AIR; in any case, the download link is here. See the chart below for the updated version numbers for your operating system.
Update, 8:05 p.m. ET: Added comment from Google.
Update, June 12, 2:10 p.m. ET: Microsoft modified its blog post to say the IE patch covers 19 vulnerabilities, instead of 18. The above copy also has been changed to reflect that.




Permanently vulnerable.
Internet Explorer has numerous vulnerabilities that are being patched this month:
o Internet Explorer Script Debug Vulnerability – CVE-2013-3126
o Multiple Memory Corruption Vulnerabilities in Internet Explorer (there are 18 CVEs)
These vulnerabilities are all mitigated as follows:
“By default, Internet Explorer on Windows Server 2003, Windows Server 2008, Windows Server 2008 R2, and Windows Server 2012 runs in a restricted mode that is known as Enhanced Security Configuration. This mode mitigates [this | these] vulnerabilities.”
More here (the link is provided in Brian’s article):
http://technet.microsoft.com/en-us/security/bulletin/ms13-047
Microsoft, please make Enhanced Security Configuration available as an option to Internet Explorer users on Windows client OSs.
P.S. Did I correctly understand from the article that some Mac users are currently being hacked via an exploit in Microsoft Office for Mac 2011?
Microsoft says Office for Mac 2011 is vulnerable, and that the vulnerability described by CVE-2013-1331 is being attacked. But it didn’t say whether it was on Mac or Windows that the attacks occurred. I have outstanding requests to Google and Microsoft about this.
Just heard back from MS: The attacks they saw in the wild were against the Windows version of Office 2003.
Thanks, Brian
Saw the Office 2003 update so I checked for updates for Office 2004 for Mac. No updates at this time
Sadly with the release of Office 365 for Mac Microsoft took 2004 and 2008 off life support.
Not even critical hotfixes will be issued for them anymore (at least for free, you’re welcome to try and negotiate a support contract with MS).
The wonderful thing is, of course, that neither 2011, 365, or the forthcoming 2014 work on PowerPC systems.
Fortunately, even x86 Office for Mac exploits are uncommon, let along the PowerPC version which would require exploits developed for the completely different PowerPC architecture.
I installed the Office2011-1435UpdateEN dmg file, after rebooting it, I noticed that the Guest User account had been re-enabled. I have also removed Microsoft’s install of 365 from the Library various times as well; seemingly each time MS does an update. 365 is kinda the new Silverlight add on. I didn’t sign up for it and I don’t want it.
Doesn’t http://blogs.adobe.com/psirt/2013/06/security-updates-available-for-adobe-flash-player-apsb13-16.html imply that Flash 10.x is being pushed to the curb next month?
Yes, that’s what it looks like. Thanks for spotting that, Tom.
I hate the way flash has to up date all the time.
Could someone please explain to me why this is an issue? I can understand attacking a financial institution or something with an obvious gain, but Microsoft office? What will they gain, my essay on technology’s role in the 21th century?
David, the vulnerability is used generally in email attacks; it is merely a vector for delivering malware.
In a typical attack, the attacker will send a poisoned Word attachment to a target; if that target is running an unpatched system and opens the document, the malicious attachment can download malware of the attacker’s choosing and install it silently.
Why attack office? Chances are that many tasks done by people in financial institutions use office. Now let us try and see if we can get system privileges by creating a malicious word doc. Okay malicious doc is created now let us see if we can send it to the right person that will get us tons of juicy details. Person with juicy details opened doc progress. Now we might be able to get all the juicy details about financial institution X. So by exploiting office you may be indirectly exploiting financial institution X. All if not most explorations done are to try and get data; you can’t just go and attack company X you need to find something they use, get that something to do something it is not suppose to do – like grant remote code execution (a command prompt or terminal shell with escalated/root privileges are the best) – then use that remote code execution to do Y (get data).
Perhaps a bit too long of an explanation…
Mr. Krebs and Juan thanks for the breakdown! That really makes sense now. I thought most attacks were SQL injection based. Oh well, I guess its just another crafty threat we need to watch out for.
p.s. Juan I’m a first year info sec student so feel free to throw as much info my way as you can, it helps!
If you have Windows 7 then be sure to run Windows Update twice. For my system, nine fixes were downloaded the first time Windows Update was run. After the fixes were installed and the system was rebooted, I ran Windows Update a second time which downloaded three fixes for .NET .
That’s a good thing to do regardless of what version or even what OS you run. Every time I get an update, I rerun it until the updater says there’s nothing to do.
It’s on my calendar to run an update on every machine, Windows or Linux, every Wednesday morning. I may not be an expert on security, but you don’t have to be an expert to take common sense precautions with your computers.
Windows has had this problem for years. I really wish that Microsoft would give us a feature that would just keep updating until there are no further updates.
I’m somewhat mystified at how they require a particular patch to be installed before they’ll let you install another patch. Why couldn’t they look 15 seconds ahead and say “hey, since you’ll have this patch installed, how about we also install a patch for it at the same time, just schedule one to be installed after the other” and have everything done in one pass?
But I say somewhat because I know why… it takes effort, forethought, and planning. It’s way easier to just piecemeal your way from the previous patch to the current patch rather than have to look back at previous work.
But it is possible. Just look at any Linux package management system, they figure out the myriad of individual components that have to be installed and what order they need to be installed in.
This is on XP : after Windows automatic update delivered the IE and Windows updates, I checked for any non-priority updates and found four. Three were the .NET updates that Old School mentioned, the fourth was KB2808679, which “protects an external network from verifying whether a uniform resource identifier (URI) port on an internal network is open or closed.”
I’m just learning how to install security updates in Windows 8, never mind the other Adobe patches.
I know a lot of people still use it, but “the latest version of Office 2003” is something of an oxymoron. Office 2003 is scheduled to sunset next year along with Windows XP.
http://www.microsoft.com/en-us/windows/endofsupport.aspx
People sometimes keep older versions of programs for compatibility. For example alot of times when you get a clients files sent to you from their computer….it might be incompatible with a certain program or version on your computer. So its best to keep a couple diff versions just in case, say if your an accountant.
alot of times clients never update….its also an easy way to get viruses lol.
Here’s tips: Get Linux. And don’t install Flash or Java or all those other crap. Also get NoScript.
Linux is also permanently vulnerable, even if it’s more secure than Windows.
Real security means using BSD, especially OpenBSD.
All OS is also permanently vulnerable, if your computer is plugged into the Internet.
PULL OUT THE ETHERNET PLUG.
^ That will fix all security vulnerable 🙂
I thought computers were for stuff like 1+1 and !100 and (10+2*2/6) – (13*!37)
Yeah… pretty much.
“All OS is also permanently vulnerable, if your computer is plugged into the Internet.”
So true.
The really serious DOD projects have no Internet connection at all inside the workers’ Faraday cage (a common name for the room was “Tempest tank” but I think that is an obscure name).
But how much trouble would someone encounter when he tried to set up OpenBSD on his personal computer? Seems like quite a bit of continuing trouble, and for what security gains?
OpenBSD is easier to install than Linux. Once installed, though, it’s real Unix. It won’t hold your hand but it’ll be the most solid friend you’ve ever had.
A typical Linux desktop has more in common with Windows than with OpenBSD. It just depends on the person and what kind of environment they want.
I’ve been using OpenBSD on the desktop for years. Haven’t run Windows since (I think) Win98.
“OpenBSD is easier to install than Linux”
Total horse manure.
Anyone who has not previously built Unix and goes to the Boulder mirror site at http://ftp3.usa.openbsd.org/pub/OpenBSD/ will have a panic attack and never return.
Yes, Unix is more secure than Linux, not to mention Windows. But the installation process for OpenBSD is only for dedicated geeksters.
“A typical Linux desktop has more in common with Windows than with OpenBSD”
Given that OpenBSD supports GNOME, KDE, and Xfce GUIs, standard fare for Linux distributions, your assertion is nonsense.
And once installed, maintaining OpenBSD isn’t exactly a walk in the park either. Patching the OpenBSD kernel (which, thankfully, happens infrequently) and X.org is also not for the faint of heart.
IMO a better BSD recommendation for ordinary users is PC-BSD which is based on FreeBSD and is much easier to install and manage:
http://www.pcbsd.org/
In addition, PC-BSD offers users the option of installing Java (the OpenJDK JRE) and Adobe Flash Player. While OpenBSD supports OpenJDK, I don’t believe that it supports Flash Player.
P.S. I’ve used all three of these BSDs in the past. Currently, I’m using Debian’s GNU/kFreeBSD because I also use Debian GNU/Linux and like Debian’s package management, apt.
“And once installed, maintaining OpenBSD isn’t exactly a walk in the park either. Patching the OpenBSD kernel (which, thankfully, happens infrequently) and X.org is also not for the faint of heart.”
Unix is something you should either
A) already know, or
B) be willing to learn
in order to use it.
Here are the instructions for patching a kernel for a recent vr(4) bug (if you don’t use a vr ethernet card, as most people don’t, then it’s irrelevant):
cd /usr/src
patch -p0 < 002_vr.patch
Then build and install a new kernel.
If you can type these 2 commands, and run make, then patching the kernel is a walk in the park. If you can't type these commands, OpenBSD is not for you. (Do you really prefer apt-get update; apt-get upgrade? and if it doesn't work, try apt-get upgrade? Not substantially different, except that the inner workings of the system are hidden, depriving the sysadmin of actually knowing the system.
http://ftp.openbsd.org/pub/OpenBSD/patches/5.3/common/002_vr.patch
With Linux (e.g. Ubuntu) you still have to type almost the same amount, except that the commands hide the inner workings from you.
It just depends on what people want from their computers. If they want Windows-like, then Linux is a great choice, because that's the direction Linux is taking. Someday you won't even have to type anything at all in Linux. Won't have to know anything, just like in Windows.
Here’s what’s involved in running Make:
# cd /usr/src/sys/arch/i386/conf
# config GENERIC
# cd ../compile/GENERIC
# make clean && make
[…lots of output…]
# make install
And if one wants a backup of the kernel prior to running make install (in case something goes wrong):
# cp /bsd /bsd-backup
Sources:
5.3.4 – Building the kernel
http://www.openbsd.org/faq/faq5.html#BldKernel
How to Build OpenBSD Kernels
http://cromwell-intl.com/linux/openbsd-kernel.html
P.S. I use the CLI in Windows too. 🙂
Heh. You didn’t follow the (simple) directions. You’re not supposed to log in over FTP and download a bunch of files. Please do a little investigation before you talk authoritatively about this subject.
You’re supposed to either
1) buy a CD set
2) burn an ISO to CD
3) boot from new bsd.rd if you know what that entails
4) use a boot floppy, if you happen to use an ancient system that no clueless person would have
If you don’t read the directions, don’t blame someone else.
I’ve recently installed OpenBSD, FreeBSD, NetBSD, Dragonfly BSD, and Debian. OpenBSD was the easiest, hands down. Debian was clearly the hardest, partly because it kept crashing, partly because it’s formatted badly. (ask a question, install some packages, ask another question, wait a long time while it slowly does stuff. Much better to “batch” the questions. Debian’s installer is much better than Gentoo’s, though.
“Heh. You didn’t follow the (simple) directions.”
As I said before, horse manure.
Those “simple” directions are at http://openbsd.org/faq/faq4.html for 5.3. They are quite lengthy. If I wanted to install OpenBSD, I would find them very useful, but they sure as heck are not simple.
” You’re not supposed to log in over FTP and download a bunch of files.”
Guess again. Work your way down from that webpage (5.3/amd64) and find install53.iso for amd64. You just assumed it was ftp because of the pathname. I downloaded the file without logging into anything. Maybe you should read the instructions, especially the part at the very beginning “On several platforms a CD-ROM image (cd53.iso for just booting, or install53.iso for the entire install).”
I know how to install Unix, Linux, and Windows. However, unlike you, I realize that most people will not pursue it.
You are a terminal geek and love playing with Unix. Congratulations. But only a tiny fraction of people are capable of understanding the lengthy instructions. X-Windows? Only Unix weenies know of this. I programmed in X-Windows / Motif years ago and I cannot remember anyone else having an easy time of it.
Saucy, Gem, and Rabid,
Surely we aren’t going to rehash a debate which has been running for decades now, without any solution so far, are we?
It’s wonderful that people can use the CLI and type in strings of esoteric code that makes sense to them. I respect that choice. It’s nice that Ubuntu makes it easier to do this by button-pushing, because Linux does have a steep learning curve and you can start with training wheels and work your way up, if you want to. And for those who are willing to pay someone else, it’s nice that Windows will allow you to use a computer without having to know anything about it. People have been driving cars for decades without having to know how to change a spark plug – why should the computer be any different?
Everyone has to make the decision about what is important to them. Security? Ok, become a Linux guru and build it yourself. Not enough time for that? Ok, pick something simpler and ease your way up to guru level, or perhaps just knowledgable user. Not enough time for that? OK, use Windows and pay someone to fix your problems.
Is there some reason to demean others just because they didn’t make the same choices you did?
When someone writes “OpenBSD is easier to install than Linux,” “A typical Linux desktop has more in common with Windows than with OpenBSD,” and “You didn’t follow the (simple) directions,” with these assertions being demonstrably false, I become annoyed.
If someone wants to write something like “Unix is more secure than Linux and much more so than Windows” and “Administration of Unix can be rather difficult and involved, but I love it anyway” then I will stay out of it.
Most Unix clones/based OSes are more secure than Windows
Windows is a piece of crap
@saucymugwump and @uyjulian The GNU/Linux and BSD desktops’ best friend is their very low market share. In the current malware landscape, one is much safer running a GNU/Linux or BSD desktop than running either Windows or OS X (UNIX). Safety is not the same as security.
Qubes OS is a relatively new desktop solution based largely on the Xen hypervisor and runs Fedora GNU/Linux AppVMs (the default) and can also run Windows AppVMs. Why run Fedora in AppVMs? The short answer is that both the Linux kernel and X.org are bloated and scary. More on Qubes OS here:
http://theinvisiblethings.blogspot.com/
Lot’s of interesting and enlightening reading … two of my favorites:
http://theinvisiblethings.blogspot.com/2011/04/linux-security-circus-on-gui-isolation.html
http://theinvisiblethings.blogspot.com/2010/08/skeletons-hidden-in-linux-closet.html
Alternatively, you could protect your GNU/Linux desktop with SELinux, the most comprehensive LSM, and/or grsecurity/PaX. (Gem would love grsecurity/PaX as it requires that the Linux kernel be patched and built just like with OpenBSD.)
Mere mortals like me can simply run the most recent Ubuntu LTS release, 12.04, along with Google’s Chrome browser to bump up their security a bit from the default. Although I use the open-source Chromium browser (since I don’t need or use Flash Player) and have created my own AppArmor profile for Firefox/NoScript.
P.S. @Toad, one can get paid support for the Ubuntu desktop from Canonical, Ltd. That’s currently what Google does.
Rabid Howler Monkey wrote “Mere mortals like me can simply run the most recent Ubuntu LTS release, 12.04”
Aren’t you slightly worried about Canonical’s new relationship with the Chinese? Given that China (for IP and national security theft) and Russia (for cyber-crime) are the two biggest players, don’t you think the source tree might end up with brilliantly crafted malware inside?
I like Fedora Linux with Gnome for that reason.
“X.org are bloated and scary”
X-Windows is really old now, so that does not surprise me.
@saucymugwump The Chinese government will be working in concert with Canonical to create a Chinese derivative of Ubuntu. Don’t forget that Canonical sources Ubuntu from Debian unstable.
If the Chinese government wants a backdoor in GNU/Linux (or the Linux kernel in the case of Android), they’d be much better off having their miscreants commit source code directly to the Linux kernel and other open-source projects. In this way, their backdoors wouldn’t be specific to a particular Linux distro. Remember that Red Hat Enterprise Linux and SUSE Enterprise Linux are used by most enterprises and governments.
Google, however, with its Goobuntu shell, is an example of a large, multi-national enterprise that uses the Ubuntu desktop heavily in its operations. Given that China has already hacked Google (operation Aurora), I suspect that Google will look more closely at any Ubuntu source code that bypasses the Debian Project and comes directly from Canonical.
In addition, according to the following linked article (also note the authors credentials):
http://resources.infosecinstitute.com/exploiting-gresecuritypax/
which is really about exploiting the Linux kernel in spite of the considerable protection provided by grsecuriy/PaX, the Linux kernel could use considerably more code auditing that it has gotten in the past. Thus, the Chinese government would also be likely to discover Linux kernel vulnerabilities and craft exploits as necessary.
Gem makes some good points regarding OpenBSD security. Here’s a link to the OpenBSD project’ code auditing efforts:
http://openbsd.org/security.html#process
That’s not to say that world-class hackers couldn’t find a vulnerability and craft an exploit for OpenBSD. But it would probably be a lot easier to go after X.org, Firefox, LibreOffice or OpenJDK on an OpenBSD desktop and Apache http server, MySQL or PHP on an OpenBSD server, as examples. Besides, pwning a non-root account can still result in considerable damage.
OpenBSD is so easy to install because the default options are sensible, and there are default options for almost everything — even filesystem partitions.
You should install OpenBSD and see for yourself.
Also, please stop saying my comments are nonsense, manure, and so on. It hurts my feelings and makes me feel inferior to you. *sniff*
Wait, I thought Linux WAS Unix? At least, that’s what I’m always told at work whenever I dare to associate them as something different. Any thoughts on this? Isn’t Linux just a variation of Unix?
Linux is a member of the Unix family of operating systems.
Corporate users rarely have choices like this. People sitting in cubes and the people who support them work with the tools provided by their employer.
That was certainly true in the past, but it is becoming less so because of BYOD (bring your own device). Some businesses allow this, yet do not understand the security implications of employees using devices which may or may not be secure. I have read, though I have no personal knowledge of it, that some employers are now demanding that employees bring their own devices, saving the company big bucks on hardware. It remains to be seen if these companies will attempt to demand that employees required to bring their own devices are also required to submit their personal property to IT for inspection and/or administration.
I really appreciate the emails on these things. For some reason I didn’t get any automatic updates, and filehippo didn’t find anything for flash either. Thanks for the alert.
I have Windows 7 and Office 2010. The only update that Microsoft downloaded was the Malicious Software Removal Tool. Windows Update check says “No important updates available.”
Am I missing something, or were the updates just not applicable to my computer?
Thanks.
“This Office flaw, which is present in the latest versions of Office 2003 and Microsoft Office for Mac 2011”
I turn to Krebs on Security first every day and it’s invaluable.
Today I’ve wasted 4 1/2 hours trying to get Firefox 21.0 to work with the Flash 11.7.224 update. Early on it installed but I could not see the flash ball, as the test. Later, I got errors of both Firefox and Flash running blocking the install. I’ve separately reverted to FFX 20.1 and Flash 11.7.169 without success. This is under win 7 sp1. I have done patch Tuesday updates.
I’ve seen some comments that the two do not play well together. I’ll upgrade to 21.0 and try flash 11.7.169.
Any other reports?
Thanks, Jack
Downloaded a 64 bit version and got the bouncing ball.
Perhaps I missed it earlier.
Cheers, Jack
First of all, thanks Brian.
You blog is the source to which I turn daily to check if updating is due.
I updated my four machines for Windows and Flash.
All went well, except the Flash update on the XP machine that kept timing out (allowed scripting for Adobe and popup windows). When I switched to Internet Explorer (Use Firefox normally) the same problem.
The other machines are not XP (one is Vista, one is W7, the other W8).
The wireless connection to my XP machine is excellent (144 Mbps) and my broadband is very fast (a broadband download speed test on my XP machine, done with the Firefox Speed Test extension, indicated 11.2 Mbps).
I enter this comment because Brian usually asks for information on problems with updates.
My machine installed the latest version of Flash Shockwave last lost along with all the other MS patches.
It am since unale to play my embedded video’s at my website when I use IE 9.
Luckily my primary browser is Chrome, but I have to make sure my website works OK on all browsers and it’s annoying that my website doesn’t work properly with IE at the moment….
Ever since I updated to the latest Flash Player version, 11.7.700.224, I’m unable to view certain YouTube videos, only the audio is present. I run Windows 7, 64-bit, and use Internet Explorer 10. If uninstalled and reinstalled the latest player with no good results. Any suggestion for a fix is appreciated!