Over the past four years, KrebsOnSecurity has been targeted by countless denial-of-service attacks intended to knock it offline. Earlier this week, KrebsOnSecurity was hit by easily the most massive and intense such attack yet — a nearly 200 Gbps assault leveraging a simple attack method that industry experts say is becoming alarmingly common.
At issue is a seemingly harmless feature built into many Internet servers known as the Network Time Protocol (NTP), which is used to sync the date and time between machines on a network. The problem isn’t with NTP itself, per se, but with certain outdated or hard-coded implementations of it that attackers can use to turn a relatively negligible attack into something much, much bigger. Symantec‘s writeup on this threat from December 2013 explains the problem succinctly:
Similar to DNS amplification attacks, the attacker sends a small forged packet that requests a large amount of data be sent to the target IP Address. In this case, the attackers are taking advantage of the monlist command. Monlist is a remote command in older version of NTP that sends the requester a list of the last 600 hosts who have connected to that server. For attackers the monlist query is a great reconnaissance tool. For a localized NTP server it can help to build a network profile. However, as a DDoS tool, it is even better because a small query can redirect megabytes worth of traffic.
Matthew Prince, the CEO of Cloudflare — a company that helps Web sites stay online in the face of huge DDoS attacks — blogged Thursday about a nearly 400 Gbps attack that recently hit one of the company’s customers and leveraged NTP amplification. Prince said that while Cloudflare “generally [was] able to mitigate the attack, it was large enough that it caused network congestion in parts of Europe.”
“Monday’s DDoS proved these attacks aren’t just theoretical. To generate approximately 400Gbps of traffic, the attacker used 4,529 NTP servers running on 1,298 different networks,” Prince wrote. “On average, each of these servers sent 87Mbps of traffic to the intended victim on CloudFlare’s network. Remarkably, it is possible that the attacker used only a single server running on a network that allowed source IP address spoofing to initiate the requests. An attacker with a 1 Gbps connection can theoretically generate more than 200Gbps of DDoS traffic.”
NO TIME LIKE THE PRESENT
Prince suggests a number of solutions for cleaning up the problem that permits attackers to seize control over so many ill-configured NTP servers, and this is sound advice. But what that post does not mention is the reality that a great many of today’s DDoS attacks are being launched or coordinated by the same individuals who are running DDoS-for-hire services (a.k.a “booters”) which are hiding behind Cloudflare’s own free cloud protection services.
As I noted in a talk I gave last summer with Lance James at the Black Hat security conference in Las Vegas, a funny thing happens when you decide to operate a DDoS-for-hire Web service: Your service becomes the target of attacks from competing DDoS-for-hire services. Hence, a majority of these services have chosen to avail themselves of Cloudflare’s free content distribution service, which generally does a pretty good job of negating this occupational hazard for the proprietors of DDoS services.
Mr. Prince took strong exception to my remarks at Black Hat, which observed that this industry probably would destroy itself without Cloudflare’s protection, and furthermore that some might perceive a credibility issue with a company that sells DDoS protection services providing safe haven to an entire cottage industry of DDoS-for-hire services.
Prince has noted that while Cloudflare will respond to legal process and subpoenas from law enforcement to take sites offline, “sometimes we have court orders that order us to not take sites down.” Indeed, one such example was CarderProfit, a Cloudflare-protected carding forum that turned out to be an elaborate sting operation set up by the FBI.
He said the company has a stated policy of not singling out one type of content over another, citing a fear of sliding down a slippery slope of censorship.
In a phone interview today, Prince emphasized that he has seen no indication that actual malicious packets are being sent out of Cloudflare’s network from the dozens of booter service Web sites that are using the service. Rather, he said, those booter services are simply the marketing end of these operations.
“The very nature of what we are trying to build is a system by which any content can be online and we can make denial-of-service attacks a thing of the past. But that means that some controversial content will end up on our network. We have an attack of over 100 Gbps almost every hour of every day. If I really thought it would solve the problem, and if our network was actually being used in these attacks, that’s a no-brainer. But I can’t get behind the idea that we should deny service to a marketing site just so that it can be attacked by these other sites, and that this will somehow make the problem go away. I don’t think that’s right, and it starts us down a slippery slope.”
As a journalist, I’m obviously extremely supportive of free speech rights. But it seems to me that most of these DDoS-for-hire services are — by definition — all about stifling speech. Worse yet, over the past few months the individuals behind these offerings have begun to latch onto NTP attacks, said Allison Nixon, a researcher for NTT Com Security who spoke about DDoS protection bypass techniques at last year’s Black Hat.
“There is a growing awareness of NTP based attacks in the criminal underground in the past several months,” Nixon said. “I believe it’s because nobody realized just how many vulnerable servers are out there until recently. “The technical problem of NTP amplification has been known for a long time. Now that more and more attack lists are being traded around, the availability of DDoS services with NTP attack functionality is on the rise.”
(S)KIDS JUST WANNA HAVE FUN
The shocking thing about these DDoS-for-hire services is that — as I’ve reported in several previous stories — a majority of them are run by young kids who apparently can think of no better way to prove how cool and “leet” they are than by wantonly knocking Web sites offline and by launching hugely disruptive assaults. Case in point: My site appears to have been attacked this week by a 15-year-old boy from Illinois who calls himself “Mr. Booter Master” online.
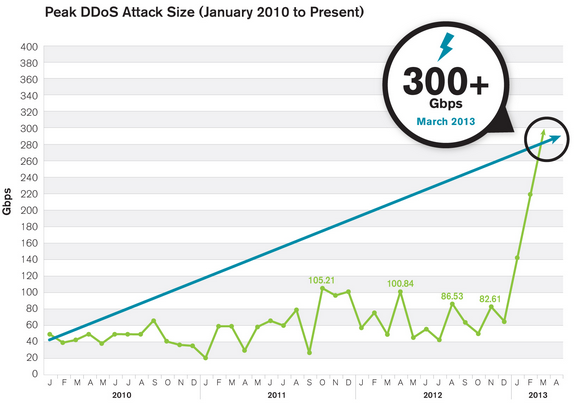
Prolexic Technologies, the company that has been protecting KrebsOnSecurity from DDoS attacks for the past 18 months, said the attack that hit my site this week clocked in just shy of 200 Gbps. A year or two ago, a 200 Gbps attack would have been close to the largest attack on record, but the general upswing in attack volume over the past year makes the biggest attacks timeline look a bit like a hockey stick, according to a blog post on NTP attacks posted today by Arbor Networks. Arbor’s writeup speaks volumes about the motivations and maturity of the individuals behind a majority of these NTP attacks.
The NTP attack on my site was short-lived — only about 10 minutes in duration, according to Prolexic. That suggested the attack was little more than a proof-of-concept, a demonstration.
Indeed, shortly after the attack subsided, I heard from a trusted source who closely monitors hacker activity in the cybercrime underground. The source wanted to know if my site had recently been the subject of a denial-of-service attack. I said yes and asked what he knew about it. The source shared some information showing that someone using the nickname “Rasbora” had very recently posted several indicators in a private forum in a bid to prove that he had just launched a large attack against my site.
Apparently, Rasbora did this so that he could prove his greatness to the administrators of Darkode, a closely guarded cybercrime forum that has been profiled at length in this blog. Rasbora was anxious to show what he could contribute to the Darkode community, and his application for membership there hinged in part on whether he could be successful in taking down my site (incidentally, this is not the first time Darkode administrators have used my site as a test target for vetting prospective members who apply based on the strength of some professed DDoS prowess).
Rasbora, like other young American kids involved in DDoS-for-hire services, hasn’t done a great job of separating his online self from his real life persona, and it wasn’t long before I was speaking to Rasbora’s dad. His father seemed genuinely alarmed — albeit otherwise clueless — to learn about his son’s alleged activities. Rasbora himself agreed to speak to me, but denied that he was responsible for any attack on my site. He did, however, admit to using the nickname Rasbora — and eventually — to being consumed with various projects related to DDoS activities.
Rasbora maintains a healthy presence on Hackforums[dot]net, a relatively open forum that is full of young kids engaged in selling hacking services and malicious code of one kind or another. Throughout 2013, he ran a DDoS-for-hire service hidden behind Cloudflare called “Flashstresser.net,” but that service is currently unreachable. These days, Rasbora seems to be taking projects mostly by private contract.
Rasbora’s most recent project just happens to be gathering, maintaining huge “top quality” lists of servers that can be used to launch amplification attacks online. Despite his insistence that he’s never launched DDoS attacks, Rasbora did eventually allow that someone reading his posts on Hackforums might conclude that he was actively involved in DDoS attacks for hire.
“I don’t see what a wall of text can really tell you about what someone does in real life though,” said Rasbora, whose real-life identity is being withheld because he’s a minor. This reply came in response to my reading him several posts that he’d made on Hackforums not 24 hours earlier that strongly suggested he was still in the business of knocking Web sites offline: In a Feb. 12 post on a thread called “Hiring a hit on a Web site” that Rasbora has since deleted, he tells a fellow Hackforums user, “If all else fails and you just want it offline, PM me.”
Rasbora has tried to clean up some of his more self-incriminating posts on Hackforums, but he remains defiantly steadfast in his claim that he doesn’t DDoS people. Who knows, maybe his dad will ground him and take away his Internet privileges.








Brian… they were just sending you “Valentines” because they love you… Keep fighting the good fight!
In the distant past we had Smurf and Fraggle. Following this convention should the NTP reflection attacks be called Barney, as they are big and f……. annoying.
Congrats on make Australian News Site Sydney Morning Herald. (SMH)
http://www.smh.com.au/it-pro/security-it/meet-brian-krebs-the-it-security-blogger-cyber-criminals-love-to-hate-20140217-hvcrr.html
Can’t help but lol at the alias Mr Booter Master. I used to skid around too but to think a name like that actually boosts somebodies ego is pretty hilarious. Oh, to be 15 again…
I suppose MasterBooter would have been more hilarious….
Can we conclude then, that the increase in scope of these ddos attacks, correlates with how many more computers are infected out there nowadays?
Actually, no. This recently-common attack relies not on infected computers, but on perfectly legitimate devices running an NTP service. Worse, some of these NTP servers have a lot of bandwidth at their disposal, so they’re very effective unwitting “bots”.
15 Years old doesn’t mean he’s not a criminal.
There are PLENTY of DDoS attacks coming out of Cloudflare and Amazon and other cloud service providers’ networks. I have to firewall their AS records every month.
The attacks are legion, using all known methods. We don’t need these cloud networks nearly as badly as their investors need them.
Some people deserve to be found, shot in the head and rolled into a shallow hole for the benefit of mankind.