An exclusive KrebsOnSecurity investigation detailing how a unit of credit bureau Experian ended up selling consumer records to an identity theft service in the cybercrime underground has prompted a multi-state investigation by several attorneys general, according to wire reports.
Reuters moved a story this afternoon quoting Illinois Attorney General Lisa Madigan saying that “it’s part of a multistate investigation,” and that Connecticut Attorney General George Jepsen said that Connecticut is looking into the matter as well.
News of the breach first came to light on this blog in October 2013, when KrebsOnSecurity published an exclusive story detailing how a Vietnamese man running an online identity theft service bought personal and financial records on Americans directly from a company owned by Experian, one of the three major U.S. credit bureaus.
Hieu Minh Ngo, a 24-year-old Vietnamese national, pleaded guilty last month to running an identity theft service out of his home in Vietnam. Ngo was arrested last year in Guam by U.S. Secret Service agents after he was lured into visiting the U.S. territory to consummate a business deal with a man he believed could deliver huge volumes of consumers’ personal and financial data for resale.
But according to prosecutors, Ngo had already struck deals with one of the world’s biggest data brokers: Experian. Court records just released last week show that Ngo tricked an Experian subsidiary into giving him direct access to personal and financial data on more than 200 million Americans.
According to U.S. government investigators, the data was not obtained directly from Experian, but rather via Columbus, Ohio-based US Info Search. US Info Search had a contractual agreement with a California company named Court Ventures, whereby customers of Court Ventures had access to the US Info Search data as well as Court Ventures’ data, and vice versa. Experian came into the picture in March 2012, when it purchased Court Ventures (along with all of its customers — including Mr. Ngo). For almost ten months after Experian completed that acquisition, Ngo continued siphoning consumer data and making his wire transfers.
A transcript (PDF) of Ngo’s guilty plea proceedings obtained by KrebsOnSecurity shows that his ID theft business attracted more than 1,300 customers who paid at least $1.9 million between 2007 and Feb. 2013 to look up Social Security numbers, dates of birth, addresses, previous addresses, phone numbers, email addresses and other sensitive data on more than three million Americans.




This is very reminiscent of what happened to ChoicePoint (now LexisNexis) a number of years ago.
I can’t say enough oh Brian’s work? All of us that read and follow should support him with donation. Where else are we going to get this kink of research. I can’t thank him enough.
Aloha Brian,
You are an amazing man. While The Washington Post sinks you rise.
I think your work deserves more visibility.
Can you get an agent who can find you a more mainstream outlet. Maybe, the BITS Section of the New York Times.
I would suggest a cable news channel. I would try CNN. But, I think MSNBC would be more likely. Then, big scoops could go on the NBC Evening News. Then, everywhere.
More people would hear and begin to understand what you are revealing . With that understanding, things would change.
Let me say that it is a great thrill every time I get an email where you uncover another internet crook –(almost on a daily basis). However, there is no follow up. You can’t do this by yourself.
I think if you had more visibility that might change.
You appear to be shy– and yet brave and defiant. That’s a problem if you want to make everyone aware of what is going on.
Show your wife this email. Ask her what she thinks.
I am not an agent. I am just someone who has been following your work for a long time.
I just think that you owe it to yourself, your email buddies and decent people who want a cleaned-up internet to think this out.
Email back if you want to talk.
“You can’t do this by yourself.”
“You appear to be shy– and yet brave and defiant. That’s a problem if you want to make everyone aware of what is going on.”
“Email back if you want to talk.”
“I am not an agent.”
Yeah, right.
Do your friends call you “The Big”?
You should watch some of the talks Brian has done that are on YouTube. ‘Shy’ wouldn’t be a word I’d use…
Thanks for going into detail about how Experian got involved.
Don’t go mainstream Brian the way another person mentioned. Keep doing what you’re doing. Anybody who’s really interested in Security and Investigation will pay attention to the media and find out how to locate your website. I have an adult relative who doesn’t seem concerned about security but I can guarantee they knew who you were when I mentioned sighing up for your alerts. In my opinion you’re already Mainstream.
Nice job Brian. Again, you are providing the kind of reporting we need. Keep up the good work!
For years—decades—the lame-o local movers and shakers have bemoaned the alleged blandness of people’s perceptions (if they have any at all) of Ohio’s capital city. Apparently, it’s not enough that Columbus is the capital city; the poobahs can’t stand that most news media items list the city as “Columbus, Ohio.” (Brian, how dare you follow that suit!)
They’ve said “If only we get a professional hockey team or hold a national political convention or some such, then Columbus will really get on the map and people will quit referring to us as a ‘cow town.'” (Readers may by now have noted the amnesia in re “The” Ohio State University that anomalizes this attitude.)
Talk about an identity crisis!
Well, I think the crisis has finally been resolved. Just think of Columbus henceforth as the Identity Theft Capital of the US. (Meanwhile, I remain so immensely satisfied that I live in a nearby township.)
Oh how I hate Ohio State!
(Sorry. having graduated from another Big 10 school, I couldn’t resist. Also, to the uninitiated, it comes across better when you say it out loud.)
If I did not have thousands of better things to do, I might also hate Ohio State. It’s not that I don’t think much of Ohio State. I tend not to think of it at all.
You are so far ahead of any other reporting on security issues. I do wish that the “rip and read” crowd would take notice. Thank you.
They should stick Hieu Minh Ngo in the super-max federal prison in Colorado for the rest of his life , once found guilty of the crimes committed
No way. To go to jail for life you have to use a computer to prove that school officials or politicians are breaking the law. Only whistleblowers who engage in “hacking” (like visiting publicly available web pages) go to jail for life.
Mr Plebs you are – To0 little to0 late – so close and so far away – again .But there are always some breadcrumbs left behind .I hope you Enjoy the left overs and when you finish with it make sure you clean the dishes .Its a Rule last one out cleans the dishes .
Mr. Plebs??? Who Dat??? And what’s a mouse doing leaving crumbs? Need to get a CAT to eat that mouse. CHOMP. YUM.
How can one find out if they are a victim?
You should call Experian and ask for a list of companies that have purchased your credit history. While you’re at it, you should do the same with the others (Brian has identified them before.)
Thank you. I’ll do just that.
No, thank you Elaine for being the first one in 14 comments to raise a serious query about this breach, potentially far more damaging to consumers than Target’s.
I believe what CRA Experian was selling, was your Credit Header. If you have a prior Credit Report in front of you, it’s all your data in Section one, plus what Experian chooses to add (unrevealed to you) based on what service levels, “Standard, Gold, or Platinum” their customer purchases. Enjoy.
You can also thank the FTC, who allowed in 1992, the CRAs to sell the “just the credit header”, not the lower debt history of the Credit Report, to virtually anybody. Complain to FTC, Congress.
The entire Credit Report is very restricted and has been since 1974 (FCRA).
The Header should be returned to that same restriction to protect consumers in the internet age, or that the consumer must Opt-In (agree) to having his Header data sold.
Blanche, thank you. My name, SSN, date of birth, telephone number, current and former address are all sold so Experian can make money. With that information, nothing I do is safe.
We do live in a Big Brother world where non.e of us are safe, we have absolutely no privacy, our own government spys on us, and anyone can easily steal our identities
So Experian is legally selling
a) All information required to steal someone’s identity to *cough* “trusted entities”
b) Identity theft protection services to end users
So it’s basically a self sustaining money printer where we are the only ones carrying the risks and fallout.
+1
Elaine, Re. Calling Experian
I forgot to add, “Good luck” on your plan to call Experian or any CRA, and asking if your data was sold by them.
I don’t know of any victim’s right in law to be so informed in any state or Federal statute until “a thorough and complete investigation” is completed by the firm (which can take years).
Same for any consumer to get access to the customer list of any US private company.
Don’t expect charity, or concern for consumer or victim angst, to be the CRAs’ dominant mode, if you get a live person (likely in India, or Philippines) on the phone. You are not their paying customer, just their data base’s raw material.
I believe your only hope of knowing for sure, is in the hands of these AGs and any court orders, made public. Until then, you can assume like me and 200 million others, that you were the product sold, and do what you can. Written complaints to FTC and Congress reduces anxiety.
I agree with you on all points.
I’ll highlight that having consumer personal information go to other countries, such as India is inherently unsafe. The various US institutions have reduced influence with foreign countries (eg. the recent diplomatic flap when an Indian was charged with visa fraud). And of course foreign state-side spying has no ‘red-line’ (despite their public statements) on use of that information (no restriction on giving their industries, hackers, etc. access). We can’t vote the Indian prime minister, Or Chinese Premier, out of office if their governments misuse/steal the data.
So it’s hard to argue that Experian (or any other US entity) can possibly be exerting ‘best practices’ when they require folks to tell their personal information to a foreign country just to discuss their credit rating).
The other thing to highlight is big data breaches that do damage to the consumers due to private enterprises are borne by public taxes, enforcement, etc. This means that government picks up the pieces, whether the breach is from private or public entities. This is the moral hazard; the private enterprise makes the money, and the public picks up the tab (sooner or later). We will all end up paying, but relatively few get rich from the gambling with other people’s data. Who is carrying the risk is an under appreciated difference between public (government) data collection, and private (for profit) data collection.
Well, we are headed for an election this year, and I’d bet if enough uproar happened on this subject, and folks calling their congressmen, they’d be scrambling to finally regulate the big three reporting agencies. They’ve been fighting that happening for 30 years, and now it looks like it is time to do it. I hate over regulation, but I don’t see an option here.
I sent a small donation to Brian a few weeks back, in appreciation for the time and effort he expends on my/our behalf.
I respectfully suggest that others might consider doing likewise.
As a consumer, how can we expect to be protected when so many companies, government entities and employees have access to our most personal data and share them like candies? Honestly? All these people prefer to deal with a data breach than put the effort to really protect our most personal informations.
We’re all numbers to these people and that’s scary. “Oh, your data got stolen, just subscribe to this monitoring service and good luck with the rest.” Unfortunately, this kind of behavior is widespread across the planet, shared between consumers, businesses and government entities and no one is (feel) accountable when this happens.
It still blows my mind seeing the IT security teams of these entities focusing 100% on how to TRACE a data leak than how to PREVENT it. Unencrypted laptops and USB keys with sensitive information are being lost/stolen and still, most of them deal with that like if an orange had been lost.
I strongly believe it’s our duty, as readers of this blog to spread out the information to other consumers regarding the impact of a data breach. Otherwise, don’t count on businesses and government.
Kudos to Brian for exposing this.
Chriz, you put your finger right on the problem. Somehow information that we have to give to thousands of organizations is somehow supposed to remain secret. It’s like you are going around telling everyone your locker combination. It is unrealistic, though, to expect that every single one of those thousands of entities is going to keep the information “secret” (Can it even really be called a secret after you have told it to so many people?). That means thousands of them have to do everything right, and only one bad guy needs to find a weakness. This equation doesn’t favor the good guys. A more effective solution would be to stop using public information as an identifier. The technology exists to do this, we just don’t use it since we feel the cost is too high.
Agree with the general thrust of your column. But tracing and detecting leaks is as important if not more important than preventing them. We’ll never stop every leak. But if we notice them in time, we can greatly mitigate the damage.
The Target case was a great example of this. One huge part of their failure is that Target ignored alarms that detected the intrusion. If they had noticed and responded promptly, there would have been little or no damage done.
Actually, this Experian case illustrates the point too. It’s hard to blame Experian for purchasing a company with a hidden leak. But it’s quite easy to blame them for letting the leak persist for almost a year.
Sorry, agree with the general thrust of Chriz’s comment, not column.
@Jon Marcus – To further on your point, leaks must not only be detected, but businesses need to go a step further and do a better job of performing a postmortem on the events that lead to the breach. It shouldn’t always be about “how quickly can we return to normal operations?” after an incident. While these incidents are often messy to clean up, they provide valuable real-life intelligence on your current (and probably future) attackers.
Lulz @ Chriz: “It still blows my mind seeing the IT security teams of these entities focusing 100% on how to TRACE a data leak than how to PREVENT it. Unencrypted laptops and USB keys with sensitive information are being lost/stolen and still, most of them deal with that like if an orange had been lost.”
Chriz, just because you haven’t seen me and my colleagues doesn’t mean we’re not working our tails off shoveling against the tide trying to stop the data loss.
Meanwhile it’s knuckleheads like you that fight security because it’s inconvenient and costs money. You try to get data on laptops encrypted and tell us how you do.
TANSTAAFL. Security is neither cheap nor easy, but the masses demand both. Want to find the problem? Look in the mirror! How secure is your PC, phone, coffee maker?
I empathize with your struggle.
I think all three of you (Chris, David, and yourself) are trying to solve the same problem, namely keeping the data from causing undo harm.
Part of the reason you are in the unenviable position of securing the data is the untenable view that folks can collect endless data forever, leverage it (sell it, aggregate it, front run it, etc), and not expect that at some time in the future it will do harm (often in unexpected ways).
I do empathize with your task. Yet, why was a memory stick ever manufactured without requiring encryption to begin with? Isn’t that akin to building a car without safetyglass or seatbelts? (not a great comparison, but you get the idea. Perhaps ‘without a key’ is better). Basically other business folks built stuff they could not control, and then expect you to bail them out, without mistake, forever.
We can keep databases more secure but it won’t be perfect. So let’s look at the problem from another angle as well (Often it’s a good idea to invert seemingly impossible problems and solve for the other variable.).
question: what is the largest scale for a data breach that we are willing to endure? (By largest, I am of course aggregating not just record counts, but economic harm, social issues and all other vectors of ‘big data’). If the answer is the most we can, for as long as we can, then I suggest that info security will be compromised.
As with the financial derivatives, big data (the aggregate distributive uses, not the aggregate accretive uses) is a fundamentally flawed economic model. It’s true that the finance guys employed really smart people to work on those derivative models (to make them ‘safe’), but they never had a chance. Nor do the Infosec folks. Unless we learn from the financial engineers and reduce scale (rather than leveraging up).
While I agree with you (actually I agree with all three of you) that we need to address the problem, making larger less frequent breaches only piles up the risk into tail risk (out of the bell curve). I suggest that given we won’t ever make it 100% safe, the only option is to reduce scale. Taleb discusses precisely this approach in “The Black Swan”. He suggests first recognizing that we are in what he calls the “forth quadrant”, and then working on getting out of uncertain yet high impact events.
In short, I’m saying your job is tough because we have deceived ourselves in thinking infinite scale, infinite time and a non-zero chance of failure is somehow ‘safe’ (exactly what we did with the CMBS of the financial crisis).
I think folks in Infosec need a larger voice in challenging the collection and retention of data to begin with. Otherwise you are given an impossible task to secure ever increasing data pile forever. Unfortunately an infosec guy that says “we can’t secure that data” is more likely out of a job to the guy that falsely asserts they can (until they don’t). To bring back the car analogy, it’s as if we have no speed limits and are wondering why folks are not safer drivers. The folks hiring the drivers don’t want a guy who says “i’ll drive slower” (who wants their company at a competitive disadvantage?).
And if you think you are frustrated, understand I’m watching the train wreck of a movie I’ve already seen (too many times).
Chris makes an excellent point but it is more insidious than that.
* It’s not just tracing a leak and sizing holes when they happen (although that is important)
* It’s not just putting in place stronger basic security technologies (which are frankly behind the times in most organizations – far too many unencrypted portable storage device, weak authentication, apps storing clear text passwords, apps requiring access to everything because the technology isn’t granular enough or the developers too lazy)
The basic challenge and one that happens here is the problem of ABUSE of AUTHORIZED access. And while technologies can help, it is a management and business problem. No amount of technology alone can solve these – they require business and management solutions.
Well, you (and all of us Americans) could start to realize that “Government” (Federal, state, local) is the only entity that by law and regulation, has the power to direct the inclusion of Consumer Security (just like crime, an evolving entity), into the business plan, net profits, and IT budgets of private entities (includes non-profits) and even Government itself.
When the net turnout of registered voters in an off-year election is 38% (with 19% being the victory turnout, within our archaic “first around the post system”); and a mere 54% turnout for a Prez election (Gee, that’s a lot of patriots stiffing their civic patriotic duty to vote) then don’t expect a responsive Congress or state legislature for consumer privacy and equity issues vs. legit business interests of reasonable profit.
There’s real reasons why the EU (What? An actual Minister of Consumer Affairs!) leads the world on data security, breaches, and even EMV PKI security chips in credit/debit cards. Drop the chauvinism and discover an improved wheel.
Mr. Krebs you do great work! please keep it up.
I am an american who is stationed and live in the Philippines and if you saw the amount of hackers there you would be amazed. They are mostly young chinese who set up shell companies But they hack away everyday. Thanks for all you do.
Milton
“I am an american who is stationed and live in the Philippines and if you saw the amount of hackers there you would be amazed.”
The world is waiting to hear your stories but do be aware that the work is potentially dangerous. When the stories are ready for publishing or further investigation, use the email on http://krebsonsecurity.com/about/ .
So let me get this straight:
Experian compiles all this data on citizens and sells it to any number of resellers. They make money selling data without our consent.
These resellers sell to anyone who says they are a PI, including a Vietnamese national who is severely mentall ill.
They don’t monitor access to that someone can query and extract millions of records without anyone getting concerned.
And law enforcement are going after the Vietnamese guy. Not the resellers, not Experian.
What a country.
As Blanche Dubois pointed out above, it is legal for this (Header) information to be sold, and that’s the root of the problem. At the very least such sale should require an opt-in (not opt-out) process.
I doubt that Experian can or will be held responsible for having failed in their stewardship of this data, and so consumers will be left holding the … messy end of the stick again. Call me cynical.
You forgot to mention Experian is double-dipping by also selling identity theft protection services 😉
At this point I’d like them being forced to make Identity Theft Protection a permanent, free, and automatic feature of their service. It seems not only fair to consumers, but eminently appropriate in light of this mess.
Darn right! That is what I’m pressuring my congressman to do, and also my Consumer’s Union Policy & Action Fund. They have the big muscle to make politicians quake in their boots!
From the Department of Irony:
http://www.experian.com/consumer-products/identity-theft-and-credit-protection.html
Identity Theft Protection
$15.95 /month
Ryan, another monopoly where only three credit reporting agencies supply all of the “credit worthiness” information to all of the entities that control whether or not one receives a loan, the terms of that loan, a mortgage and it terms, and sells our personal information for profit and we individuals have ABSOLUTELY NO INPUT OR CONTROL over them.
We do not live in a free country in any way, shape or form.
It seems regardless of whose sign is on the front door Experian bears responsibility. Part of their due diligence should have been a review of security and customers against their records. This is a liability issue which they would have loved to reserve against the prior owners. In any case, new procedures and checks should be part of any resolution. Its unthinkable that such a breach existed with people’s data that they did not authorize Experian to collect in the first place. I’d also like to see stiff fines as government agencies levy when the public is at risk.
This is all very interesting, arguing on merits of data security. But our government demands backdoor access to data, from all. As some one once said, if there is one unknown back door, are there more?
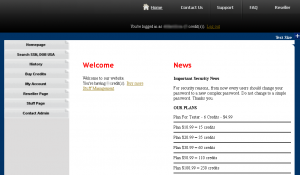
Hi Brian, I have a thought for you sir. You quite often post screenshots, like the one in this piece, of the websites you are reporting on.
Firstly, I really like this, I don’t personally want to visit these places, partly out of fear of being a victim of some drive-by malware attack, however I open every photo and look over them with great interest.
I often notice that you are logged in to these websites. Here’s my thought. If I was operating one of these sites and wanted to figure out which account belonged to you, my first port of call would be to look at the length of the area you’ve obscured.
This would allow these people to narrow down a list of users basis that alone. An examination of log in time, threads / items viewed, posting style and email addresses etc… could (albeit possibly incorrectly) result in your account being identified.
Basically, whilst you have obscured the information directly, there is potential for you to be leaving your own bread crumbs behind that might lead people to your account should they apply some investigative practices.
I would suggest (if you’re not doing it already) that you use some sort of image editing software to artificially extend, or shorten, these parts you blur out (misdirection is a powerful tool). Perhaps a simpler solution would be to just use a long black bar, to a degree with a little overkill, so the bad guys can’t figure out anything.
Maybe I’m just being paranoid, but you obviously don’t want people to easily see what your account names are, however your current method seems to be something of a half measure, I’m sure you can think of numerous additional reasons as to why going full measure, would be of good sense.
Thanks for your concern, but in general if I have reservations about posting a screenshot, I simply don’t post it. For the most part, a majority of the sites I write about and post screen shots of are free registration, which means anyone can sign up and see what’s for sale without even funding an account. In those cases, I couldn’t care less if they find out which account I use, but I tend to blur it out nonetheless.
In some (albeit far rarer) cases, I have my own reasons for actually wanting the proprietors of the forum or service to know what account I’m using. See some of my screenshots about Darkode and SSNDOB for examples of what I mean here. Usually, I will only do this after either the account in question has already been burned, or the site itself is no longer online (as is the case with Ngo’s ID theft service).
Your above comment to check out U-Tube for Krebs had me searching for hours. U-Tube search brought up a Brian Krebs Realtor selling a property on my brothers’ street. Searching this person brought all sorts of conflicting information centered around real estate and tax preparation services. The information just does not line up.
Top 4 results are all relevant for me, perhaps Google has put you in some sort of real estate bubble. Strange considering your site.
https://www.youtube.com/watch?v=Wr-PrSqI16A
https://www.youtube.com/watch?v=KGpK-xJynFI
https://www.youtube.com/watch?v=xgOPxkFgeFA
The last questioner at that Blackhat USA 2013 conference hit especially home with me. What are we going to do about the bleeding away of our intellectual property? This is a serious issue in the free world, and will surely fail us all for the future if we don’t deal with it very soon!
It would be nice to see signals from our local nation states that they are actually doing something about this, because the FBI will only take a report online, and that is it. Not all victims can show a direct loss of $5000 dollars to help initiate an FBI investigation, so they actually lose potentially millions of future dollars, jobs for local folks, and profits by their loss! What are we going to do about that? I say it is one of the centerpiece problems of the free world and also a major national security issue for each nation in this club.
What if someone were at that garage that started Apple and they stole everything from those kids and disrupted their personal lives, identity, and finances from then on? This is what is happening now! We all need a wake up call!
Why would those who already have a pile of money care about the loss of intellectual property that is not likely to do much more for them? And why would the care about the rest of us, aka those kids in the garage? If anything they would expend more money to prevent them from ever inventing or making a rival company.
I can only go by what I see personally meh; I’m on the street with these victims – they are people too BTW. I offer the early days of Microsoft as an example of how innovation made free society great. I applaud them! I don’t hold with the complainers that only seem to covet the rich and their successes. I hold to a believe that self reliant thinkers can innovate their way out of the ditch if they are lucky. The average business man fails two out of three times. So luck can be part of the equation – but it we let criminality dash the hopes and aspirations of the innovators in free society, we will not last long as free men. We would become an oligarchy like the former Soviet Union, and beholden to mafia criminal organizations, completely without any power to help ourselves or pull up our boot straps to climb out of the gutter.
There is a good reason why the people of Ukraine have been so desperate that they were willing to throw their bodies against a hail of bullets to end the injustice in their country. Living without hope of freedom is not worth living at all.
Nobody covets anything, the world has changed since those kids invented something meaningful in a garage and the same thing would not happen again today. Wealth is far more concentrated these days and the top earning industries don’t get their wealth from inventing or building things, they earn it from blocking, legal fees, and short selling stock against these companies. Facebook, a company built on sharing what teens had for breakfast recently bought out the Oculus Rift, the closest thing to the garage kids project I can think of right now – a company sharing breakfast messages ‘earned’ billions and now controls a company that was on track to make real things and real progress and will probably now fizzle because of the direction of executive board profit meetings. From the security realm, nothing is going to change to prevent this. The owner class already cashed out and they actively want to keep the rest of us from attaining anything close to what they have now, they freely GIVE our IP to communist nations to build them for us at 1000% profit margins..
I guess I’m the eternal optimist, and looking around the corner for the next Zuckerberg; but with no help from those sworn to protect us – we will surely fall. :/
I can relate more to the third U-Tube video. Thanks Anonymous for the informaiton.
I have concerns about all the companies including banks that use off shore service centers to save money, but place our personal information, including credit cards, social security numbers at risk. I am not saying that this could not happen here (U.S.A.) but here it may be easier to find and prosecute the guilt parties. If the laws would hold these companies financially liable for all individual personal losses. I think they would take customer data security seriously. What do you think!