A machine equipment company in Texas is tussling with its bank after organized crooks swiped more than $800,000 in a 48-hour cyber heist late last year. While many companies similarly victimized over the past year have sued their banks for having inadequate security protection, this case is unusual because the bank is preemptively suing the victim.
 Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.
Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.
PlainsCapital sued Hillary on Dec. 31, 2009, citing a letter from Hillary that demanded repayment for the rest of the money and alleged that the bank failed to employ commercially reasonable security measures. The lawsuit asks the U.S. District Court for the Eastern District of Texas to certify that PlainsCapital’s security was in fact reasonable, and that it processed the wire transfers in good faith. The documents filed with the court allege that the fraudulent transactions were initiated using the defendant’s valid online banking credentials.
Troy Owen, Hillary’s vice president of sales and marketing, doesn’t dispute that the perpetrators stole their online banking credentials, but said Hillary is still investigating how the information was taken. Owen said the transfers appear to have been initiated from computers in Romania and Italy, among others, and sent to accounts in Ukraine, Russia and other Eastern European nations.
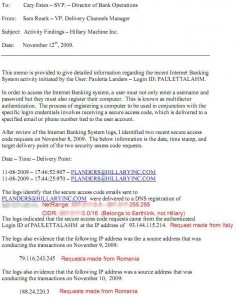 According to a Nov. 12 memo that Owens said PlainsCapital shared with him, the institution’s commercial banking platform requires that each customer not only enter a user name and password, but also “register” their computer’s Internet address by entering a secure access code sent to the e-mail address on file for the customer.
According to a Nov. 12 memo that Owens said PlainsCapital shared with him, the institution’s commercial banking platform requires that each customer not only enter a user name and password, but also “register” their computer’s Internet address by entering a secure access code sent to the e-mail address on file for the customer.
The bank’s memo states that on Nov. 8, secure access code e-mails were sent to a Hillary e-mail address, but that the request came from a computer with an Internet address in Italy. The memo further states that the actual wire transfer requests were made from computers with Internet addresses in Romania.
Owen said no one in his company received any such e-mails on or around the date of the break-in Nov 8th and 9th, and that it is likely whoever stole the company’s banking credentials also intercepted the e-mails.
“It’s pretty ridiculous that the bank is saying their security was reasonable,” Owens said. “The people who run this bank are from an area that still leaves their doors unlocked at night and their keys in the car. These security measures were probably very up to date 10 to 15 years ago, but they’re not in today’s age.”
PlainsCapital declined to discuss the memo or other details of the case, citing the pending litigation. The bank’s president Jerry Schaffner said in an e-mailed statement that “It is evident that the loss incurred by Hillary Machinery, Inc., although regrettable, was not the result of a cyber attack on PlainsCapital Bank.”
Transaction logs shared by Hillary indicate that the majority of the unauthorized transfers were international wires for roughly $100,000 each. But at least $60,000 of the money was sent to more than two dozen money mules, willing or unwitting accomplices in the United States who are often recruited through work-at-home job scams.
A copy of the bank’s complaint against Hillary Machinery is available here (PDF).
Update: Since this blog post ran, the story of Hillary’s fight with Plains Capital has been picked by several mainstream media outlets, including the Dallas Morning News, Forbes, and Fox News.




So if the VP thinks that this “hay seed bank” didn’t have reasonable security measures, why did the company choose to do business with them? Great article, Brian!
If you read Hillary’s article on thier website, they appeared to learn ‘the hard way’ just how lacking the bank’s security really was, albiet after the fact, but isn’t it a banks job to protect a depositers money?….I mean, isn’t that why they put money in a bank to begin with? You go to a construction company to build a house; a pest control company to get rid of bugs, etc..you go to a bank to keep your money safe and secure.
To quote….well, myself:
I think the following anecdotes explain the difference nicely. When a consumer wants to do online banking, the bank says, “Thanks for banking with us. And don’t worry: We will put your money back in our super-secure vault. Even if somebody should break in and rob the place, your money will still be safe because it’s protected by armed guards, and six inches of steel. But even if they get past all of those protections and steal cash from the vault, we’ll replace any money that was yours.”
In contrast, when businesses bank online, the unspoken message from many financial institutions is: “Thanks for banking with us. And don’t worry: We’ll keep your money here in our super-secure vault. Oh, and by the way, here’s a key to that vault. Just make sure you don’t lose it.”
http://voices.washingtonpost.com/securityfix/2009/11/business_e-banking_and_the_6-f.html
Brian,
First, great article.
Second, I think it’s hilarious that the bank sues the victim, claiming to have acted in good faith in fulfilling the transfer requests. Never mind the fact the request for the access code came from an IP in Italy, while the victim organization is a local one right there in Texas and geographically near the bank. Never mind the fact that many of the transfer requests originated from IPs in places like Romania, or that the transfer destinations were to places like Ukraine.
Clearly the bank is trying to establish precedence in getting the true victims to be held responsible. But perhaps it’s time for the banks to actually step up and take some responsibility for the fact that for more than the last year, they’ve served as unwitting participants in these Eastern Bloc financial scams — despite the fact the indicators of these scams can be spotted from miles away.
Maybe you could enlighten them on some online banking security 101 topics like Avalanche and Zeus?
Absolutely agree with Kevin. The IPs form FOREIGN countries should trigger an alarm in bank`s security staff. Even mid-range credit card processors are declining orders if the IP of the supposed credit card owner is NOT in the same state where the card is issued. What shall we talk about transactions of a U.S. company, made from Italian IP and Romanian IP? This is an absurd! Bank should take its responsibility in the same way if masked robbers had infiltrated and empty the safe.
I court reporter for lawyers of a bank for 20 years. I would NOT assume the bank was an innocent party here. Quite often banks perpetrate fraud on their customers, forge their names and create false paperwork after the fact.
Exactly. The days of robbing banks is over for the most part. Why risk your life and limb when you can rent services of a botnet — log some credentials and rob the bank that way? FDICwhat? All this while still in your spiderman pajamas while playing xbox live.. Bank physical security great….
The bank didn’t have a compromise, the customer did. Their online banking creditials (user id’s and passwords) were obtained by criminals looking specfically to steal money. The banks cannot control what people do on their computers or what virus and malware may inadvertenly downloaded on their computer. In most cases customers are given the information they need to protect themselves and they choose to ignore it. Like having the most up to date virus protection that continuoulsy scans for problems, using a dedicated machine with no other internet access for financial transactions, and not allowing one person within the company to be able to create wires and also send them. A seperate level of approval is needed. Everyone always says bad bank but what about the companies who take no action to protect themselves?
And who are you again? How dare you be arrogant enough to assume I was wrong. I have plenty of protection on my computer. Notwithstanding, the bank is also supposed to contact its customer if a transaction is unusual. In my case, it certainly was. Hindsight is 50-50. Know what you are talking about before you open your mouth.
So, here’s the problem. Cyber-criminals have two primary methods for bypassing legacy security controls.
1) They are testing their code against the latest virus signatures from McAfee, Trend, and Symantec prior to releasing their code on the web. Those 3 companies alone make up 80% of the AV market, and the bad guys know that, and are given an opportunity to tweak their code prior to releasing it for sale or use. Also, the viruses now are poly-morphic, which means that they alter themselves everytime the infected machine clicks on a file or visits a web page.
* As a note, the VP of security at Symantec recently said that they have released more virus updates in the last year then the previous 17 years combined.
2) There is also the issue of exploit code/script. Did you know that there are 6 web application exploits that occur every 45 minutes? For example: The Aururoa attack used a vulnerability within IE 6 to provide a back door to execute commands on the victims PC and take control. From there, they can remotely do anything/everything they want and it typically depends on what type of machine they infected (Is this a Home PC or a Corporate PC). Do they want to steal passwords, send spam, or be used in a DoS attack are all options for them!
So here’s my question for everyone – especially any security professionals: If your a home user or a business, how are you going to protect against these methods?
What are you going to do when the very the bad guys are testing their malware against your AV signatures? Don’t say to just stay away from the bad sites because 70% of the top 100 sites have been compromise in the last 6 months.
How do you know if any of the applications you are running are vulnerable and how would you protect yourself anyways if there is no patch available?
I actually do have something that will greatly reduce the likelihood of this happening to you, but I would be interested in hearing what you think first.
I don’t doubt there are malware authors who specifically try to avoid detection by the three most popular AV programs. It would explain some of the poor performance by those programs I’ve seen when I upload things to virustotal.com. But I was previously assuming they were trying to avoid detection by *all* of them, so it doesn’t actually change my approach. I would never trust something just because my AV program didn’t detect a problem. And I’ve certainly found bad things on good sites, so I don’t assume I’m safe by not going to bad websites.
You can use some other operating system other than Windows; it’s a good suggestion, but not an option for everyone. You can have a dedicated machine for banking that doesn’t run Windows, as has been suggested here. You can use a CD that will boot your Windows computer using a different operating system before doing online banking, as has also been suggested.
For general web browsing, I would suggest using an alternative browser, like Firefox. In addition, I would add Noscript, so that javascript runs only if I allow it, — and I would only allow it when I expect it to be needed, usually only on a one-time basis, and only for the domains I choose. I have FF set to always ask where I want a program stored when it is downloaded, even though I always put it on the desktop. That way, I am always alerted that a download is going to occur and can cancel it if it is unexpected/unwanted. Finally, I keep up with announcements on sites like this one about other exploits that have been reported, such as those using .pdf files, so that I can be particularly alert when there is an unpatched vulnerability being exploited.
Nothing is ever 100% protection, especially if someone is specifically targeting you, but it lowers the risk for the average web user considerably.
> I actually do have something that will
> greatly reduce the likelihood of this
> happening to you, but I would be interested
> in hearing what you think first.
So how do we find out more?
(Note that I have just finished three 18-hour days in a row working on something that will require no awareness, much less effort on the part of organizations banking online, but would reduce the probability of a loss due to cyber-thievery against commercial accounts to *zero*! Instantaneously. )
WAKE UP! i am a victim of this exact crime and have learned there is NO protection or software I can purchase to protect my company’s online bank accts from this particular virus – but the banks CAN set up multi levels of authentification and chose not to because commercial accounts. unlike personal, take the hit so no worry on the bank’s end.. starting with a simple block when money is transferred from the US from an account that has never transferred money period, let alone to a well known terrorist group recoginized by Homeland Security! Do your homework and get back to me.
1st line of defense: Don’t bank online. But if you HAVE TO bank online, then…..
2nd line of defense: Use a dedicated machine with a Linux O.S. (see also http://www.distrowatch.com &/or http://www.linux.org/dist/list.html for comprehensive listings). Can’t use a dedicated machine? Then…..
3rd line of defense: Boot the machine off of a Linux disk and save your data to a USB flash drive. And DO NOT store your login IDs and passwords electronically; but DO store them in a physically secure place (e.g., a safe).
You got it!
You may think a larger bank offers more up-to-date electronic security, but if they don’t have a local branch, it isn’t practical to bank in person and you’ve introduced other risks in the system. A “hayseed bank” might be the best choice in a rural community if its staff knows the businesses in their town aren’t likely to wire money to Eastern Europe. A small business could represent a significant client for a small bank. They may even know their clients’ employees well enough to spot someone impersonating one of them by phone.
(BTW, is anyone else annoyed by the way the comments are threaded on this site? It’s pretty hard to see if any new ones have been added since you visited last.)
Being a recent victim myself, your remark is on one of the stupidest I’ve heard to date. Obviously a customer has an expectation that his bank is secure; that your money is safe. That is the very essence of a bank. Clearly our money is safer under our pillows. Perhaps you are smarter than the rest of us business owners who have been quite sussessful until the bank walks away and says ‘”opps, your problem.” And the saddest of all, to add insult to injury, the bank sues the business? That’s really messed up and shameful.
Karen,
If you are *that* Karen, Brian Krebs or Troy Owen can give you my phone number. Give me a call. There may be something I can do, as a private investor, not just as a “lobbyist”.
Have you talked to Pete King about what TD Bank did to you? Rep. King is on *all* the relevant committees.
–Jim Woodhill
wake up! obviously they assumed the bank was safe, – isn’t it a “bank” after all? otherwise why wouldn’t they leave their money under their pillow? Were they ever told otherwise regarding any risks? i think not. They are machinists, not fraud experts!
This will be an interesting case.. There definitely needs to be a stronger standard in the authorization process with logging on to web-based banking. The single factor authentication now does nothing once the attacker has sniffed/logged the credentials from a user’ computer with their Trojan. If the bank has some form of location based security for their site based on the origination of the IP it still becomes ineffective as the attacker (thief) can proxy the traffic through the persons computer they received the credentials. We need a stronger industry standard for online banking in terms of verification of user on account.. Right now the system is weak!
I’m Joe Hacker in St. Petersburg with my Zeus botnet sniffing your keystrokes or form entries when you log on to your US bank. All I have to do is then login with those and the bank based on their 1-factor security standard and mule away all your money. GG .
The standard for OS-based security against malware/viruses/trojans is a whole other onion to peel…
While this would help, it would merely kick the can further down the road.
Let’s say for example you added some other authentication mechanism so the bad guys can’t just log in from Romania. They still have an infected machine at the company in question – the next time someone at that machine tries to do some banking, the malware can cause the transfer to be redirected and for a different amount without the user knowing. If the malware is clever, it would alter the page being displayed to make it look like everything is normal.
The Zeus can also bypass multi-factor authentication. Banks are required now to have multiple layers of security. The fact is the crooks are better and faster at circumventing security measures then banks can update their systems.
Along with the authorization security needed to be beefed up so does the wire transfers..
Brian: I’m thinking about why the bank took the aggressive step of suing its customer, which normally is not considered good publicity for the bank. (What are the bank’s other business customers are thinking when they see the bank is suing its own customer?)
My guess is that the bank decided it needed to seize the initiative. $200,000 is pretty much all that is at stake monetarily in the lawsuit. That’s is a relatively small amount for a lawsuit on a sophisticated topic like this. From the perspective of the customer (a smaller enterprise), the sheer cost of gearing up for the lawsuit (marshaling lawyers, experts and evidence and distracting management) pretty quickly starts to approach the $200,000 figure. The litigation costs become an incentive for the customer to just give up . . . settle and agree to stop talking about the incident.
From the bank’s point of view, suing a customer is not fun. But the incident is already publicized, and the bank apparently thinks it can (sorta) clear its name by prevailing with the lawsuit and forcing the customer to remove and/or retract the news item on its web page. Plus, if the bank prevails, it avoids reimbursing the customer for the $200K.
–Ben Wright, Dallas, Texas
Although I agree with what you are pointing out here; it does seem ridiculous to pay lawyers $200,000 to initiate and follow through to a lawsuit, when simply paying the victim the same money would have been settled out of court instantly!
I realize the bank probably doesn’t want precedent set here also, but it is still ridiculous.
^ Interesting case ^ Uh Huh!
What a retarded thing for an apparently foolish bank to do! I hope Hillary Machinery have shipped out by now to somewhere with real 2 factor auth, transaction profiling and a CSO worth their salt!
WTFH didn’t they spot the foreign access ? .. I’m sure that they could deny all transactions from IPs outside the US and cause very little loss of business too. OK, thats a little extreme… Put them on hold and make a damn phone call …
If you log in to paypal via a proxy/tor node in another country and then from home within a very short space of time your account is frozen.
Yes I said login… You don’t have to do anything else. & the exact same thing happens with the two factor auth tokens too!
I hope this causes bouts of hilarity for the prosecutors involved… on both sides & they learn and invest in a CSO.
CSO for hire… (It’s cheaper than taking your eye off the ball).
Private to Brian- so how do we reach you now? Good to see your “voice”
This should interesting in court. Most people do not realize that when the bank takes your money as a deposit, it becomes the bank’s money, no longer yours. The bank statement is more like an IOU that is collectible when you choose.
I would argue (and no, I am not a lawyer) that the bank lost its own money and I want mine back.
This is going to be a very interesting precedent and it will be interesting to see how the courts rule on this one. The key to solving this problem in the long term is to create a much higher level of integrity in the ACH supply chain. Think tamper-resistant seals in the physical world and translate that to information supply chains. Trusted timestamping (see ansi x.995) and software like Trusteer or TrustDefender on the desktop are starting points in creating infrastructure with a higher level of resiliency.
Saying that “requiring your private credentials information” is “reasonable security measure” is a joke. In my opinion, reasonable measures should include:
– Require “side channels” confirmation for transfers that exceed an estipulated amount. You need to go to an ATM or call the bank’s hotline to confirm the destination account’s data entered online.
– Set a “max number of transactions/day” trigger to contain the damage if the perpetrators try to make several small transfers like in the example here.
The only problem is that the side channels can get compromised in a coordinated attack. That is, the thief could implement the transfer and then call the bank hotline.
Here’s another idea already in use. My Etrade account uses a physical key that I carry with me. The key shows a six-digit combination that changes every minute. Once I log into my Etrade account, I authenticate with the six-digits appended to a password that I memorize. On the other end, Etrade locks into my IP address and TCP source port (my session identity), so even if an eavesdropper were to capture my keystrokes, he would not be able to log in because the Etrade session would only accept my session identity. The thief could even proxy through my machine, but the session identity would be different, so he would not get through. Additionally, the password changes every minute, further complicating the process for the thief.
I’m not saying that this is a foolproof system, but it’s the best I’ve seen so far.
But if your machine became compromised, then even the eTrade keyfob is no longer adequate protection. I suppose you are correct in saying that it would be a huge improvement in what most people have now, and if a few people were to start doing it, all it would mean is that that the bad guys would pick on those who don’t. But eventually if enough people started using tokens, the bad guys would change their methods as required.
This gets to the point of why Brian was recommending that people use something like a boot CD for online banking. Both to keep people from capturing your credentials, and also to ensure that your own machine itself isn’t compromised.
Yes that was his point. And it was a very good point. But it would seem by reading these comments that the subtlety of it all went over everyone’s heads.
IP Addresses can be temporarily moved by a Hacker and even CUNA Alerted all Credit Unions across the nation on Oct. 8th, 2008 that using IP addresses to ID your PC was not secure.
Real-time Keloggers, such as the Zeus Trojan, have made any security requiring the user to type in their credentials to be a useless solution, including the OTP token that changes every minute.
The SoundPass solution that Anheuser-Busch Employees’ Credit Union has been using for a couple of years is the best MFA solution available. Check it out.
Uh, where do we “check it out”?
Since the weakness being exploited is not authentication, I do not see any form of MFA solving the problem. Unfortunately, the weakness is in the customer computer.
Terry,
You are correct that nothing that goes through Windows can be trusted. There are, however, TOOBA (Totally Out-Of-Band Authentication) solutions available.
What needs to be “authentified” (to coin a verb ) are transactions that *add a new payee* (vendor or employee). Lighter-weight authentication can then be used for logon and even making a payment to an established payee.
The PlainsCapital memo sent on November 12 reads, in part: “The process of registering a computer to be used in conjunction with the specific login credentials involves receiving a secure access code, which is delivered to a specified email or phone number tied to the user account.” Did I miss something? That’s like locking a door and hanging the key by a string from the doorknob.
There are a gazillion ways to hijack email accounts, so using an email account to register a computer IP address does nothing to provide an additional layer of security.
The bank ought to cough up the extra $200k and then fire their online security team.
Exactly, if emails were secure, we wouldn’t need ssl or secured e-commerce sites, we could just send a cc# over on an email or simple cgi mailto: form.
The security team aren’t necessarily to blame. The security team are hired by the pinstripes who hold the purse strings and decide what software is going to be used. Some security teams are worthless because even today all they know is MSFT seen through rose coloured glasses. But it mostly wouldn’t matter anyway. It’s about management. A good security team would categorically refuse to use Microsoft products if they were allowed to. Often they’re not allowed to and they have to work around incredibly stupid situations. And because they can’t pick the environment, the companies will always be compromised and they’ll always be given the blame, even though they knew better and tried to get the pinstripes to listen. The blame goes to the pinstripes. To those who made the decisions. To those who said ‘yes we can work with MSFT for our online banking systems’.
I agree the blame falls on a whole raft of things, including management, the OS, etc. But I think the situation is a lot deeper than that. The fact that management can act like boneheads is nothing new, yet great things are still accomplished at companies. Same goes for MSFT: I’m not a big fan of them, but I can’t deny that there’s some awesome software written on that OS, perhaps despite its shortcomings.
In my original comment, I was only pointing out that the failure highlighted in the memo goes to a fundamental flaw in logic. Qualifying an IP address with an email is a bad idea. I don’t know the whole situation, so I can’t pass judgment on anyone, but looking in from the outside, it appears that such a fundamental flaw in logic is indicative of a basic failure to understand security, and as such, whatever security team decided on that approach ought to be examined closely.
There are really two problems here: First, the bank should have had two factor security. Second, they should have had a real verification process in place. Email is not trustworthy for something like this. Shoot, email isn’t trustworthy for anything you don’t want other people to see.
It amazes me that the bank didn’t make a phone, that they didn’t shut down the transactions until they had actually spoken with a pre-approved representative of Hillary. Who was in charge of their security, anyway?
Fantastic case. Want to see innovation in online security? Place the liability on those with the resources and ability to manage the risk. It’s time to update the laws to hold finserv accountable. We owe Hillary a cold one (please don’t take that out of context :))
Years ago there was a German insurance company sued by a client who’d lost a lot of money through the insurance company’s flawed bookkeeping. The insurance company went into a panic and started hunting the bug and were able to prove it was caused by customised software they’d bought from a German software house. They sued the software house.
The software house went into a panic and started hunting the bug further. They were able to prove the bug was actually caused by a flaw in Lotus Symphony. So they sued Lotus.
Now Lotus went into a panic and started hunting the bug further. They were able to prove the bug was actually in their C compiler. The compiler was generating a short jump when instead it should have been generating a long jump.
The compiler was built by Microsoft.
Hillary’s site isn’t much to look at but at least they had the brains/good fortune to pick a secure web server.
HTTP/1.1 200 OK
Server: Apache
Accept-Ranges: bytes
Content-Length: 70210
Keep-Alive: timeout=10, max=100
Connection: Keep-Alive
Content-Type: text/html
Not so with the bank. Note their ‘expires’ date is over a fortnight ago. Class.
HTTP/1.1 200 OK
Cache-Control: private, max-age=0
Content-Type: text/html; charset=utf-8
Expires: Tue, 12 Jan 2010 02:50:02 GMT
Server: Microsoft-IIS/7.0
X-AspNet-Version: 2.0.50727
X-Powered-By: ASP.NET
MicrosoftSharePointTeamServices: 12.0.0.6421
Content-Length: 35351
Connection: close
One can in theory criticise Hillary’s for one thing: not knowing enough (or asking enough) to shun any bank using Microsoft’s dangerous web software. There are IIS/ASP zero-days out there even Microsoft can’t find.
But that’s not the point. The point is that good security people know to avoid Microsoft web software like the plague. And they also know enough to be able to implement an Apache/Linux system if they have to. And they know in general how to build and sustain secure infosec systems. But the likelihood here is the bank never gave that a thought and went and hired on people who don’t know how to give that a thought either.
The moral is that if your bank is running IIS/ASP then they’re probably not too clued in about security and should be shunned. That’s Hillary’s only indiscretion. Everything else is firmly at the feet of that ‘stable and strong’ bank.
I am on the customer’s side here. One glance at their website should tell you everything you need to know:
http://www.hillaryinc.com
I can deduce from this page that they don’t even have a CTO, much less a CSO. The bank has the burden of being up-to-date on technical security issues, especially when the login IP of a Texas company is from *Romania* and they are transferring $100K chunks by wire. There should have been red lights flashing and red flags waving, or at least a phone call made to the company manager to verify the transfers.
Hilarious…..PlainsCapital is now looking for a Wire Transfer Risk Specialist in Fort Worth.
http://www.careerbuilder.com/JobSeeker/Jobs/JobDetails.aspx?lr=CBCB_FWST&SiteID=api_WDHR8F96W06WY727794B&Job_DID=J8G4676B6HNBZ28RN69
Oh that’s funny alright! But use a URL shortener. Don’t ruin Bk’s blog!
http://bit.ly/9yxu95
yeah, and you gotta love the job requirements, HS diploma or bachelor’s depending on which part you read, and one year experience. That qualifies you to prevent wire transfer fraud and in your spare time process wire transfer requests as back up to the regular staff.
I’m impressed. NOT!
It appears that the bank has pulled the Wire Transfer Risk Specialist career opportunity listing off the web. Maybe they found someone or maybe they are rethinking the job requirements. I looked at it on the bank’s website on Tuesday and should have printed/screen-captured it. From what I remember they were looking for someone with a Bachelors degree and 1 year of direct or similar experience. Those requirements are alarming. Hopefully it was an inexperienced employee who posted the opportunity incorrectly. The alternative is a reflection on the bank management’s overall awareness of infosec.
Hillary’s being pretty vocal with the alert on its web page and its statements in the press. I think that is a key reason the bank has initiated suit.
To prevail in the lawsuit, little Hillary may have to spend a lot of money, quite possibly much, much more than $200K. If Hillary fights and loses the lawsuit, the bank might then (in theory) sue Hillary for defamation, which could cost Hillary a whole lot more. I suspect the bank would like Hillary to think about all those costs and decide it’s in Hillary’s best interest to just settle this and shut up.
Then perhaps if there’s enough negative publicity and loss of clientele, the bank can be induced instead to drink from the cup of STFU. One would hope so!
PS. Again: kudos to Bk for getting all this fantastic material. Nobody else covers it. Bk deserves our thanks.
maybe so, but I can find no case law on any similar cases; can you? And geez!, can you imagine what follows if Plains can’t prove thier case?
@tx_plow_boy “I can find no case law on any similar cases; can you?”
In the 1990s, I devoted a chapter of my book The Law of Electronic Commerce to this topic. To refresh my memory, I’m looking back at that chapter. . . . The dispute is largely governed by Uniform Commercial Code Article 4A and the online banking agreement between the bank and the customer. Although the topic is complex, generally speaking, Art. 4A protects the bank if the bank can show it used commercially reasonable security. Section 4A-202(c) even provides a procedure where the bank can get the customer conclusively to agree in advance (such as in the online banking agreement) that the procedures to be used are commercially reasonable. Given the terms of 4A, a well-crafted online banking agreement can go a long way toward positioning a bank for victory in a case like this.
The 1995 edition of my book analyzes form agreements published in the banking industry as of that time, where the form language was tilted to favor the bank in the event of a dispute like this. I suspect that most banks today use agreements that tilt pretty strongly in favor of the bank’s interests.
For this case, of course, I have not read the agreement, and I don’t know the details.
I think Brian is right on the money when he bascially says that consumer accounts have all sorts of protection under the law but business accounts have to fend for themselves, hence the need for “a well crafted online agreement” the banks need to assert that thier security is “commercially reasonable” to protect themselves from claims that it really isn’t that secure.
I deduce from Brian’s statement that a consumer can truely trust the bank to secure thier money and although a bank will gladly take a businesses deposits, the security rests with the business, not the bank. If this is truely the case then banks really are giving thier commercial customers a false sense of security.
it’s not defamation when only the facts are stated and no mention of “not a good bank to do bus. with” or similar comments.
Lets assume online banking keeps using one factor authentication for everything, and this password keeps getting sniffed. But if you want to add a new payee account to your profile, you have to confirm this action with an SMS (out-of-band).
It’s been a long time since I last had to add a payee to my online bank – folks and shops I need to pay don’t change much from month to month. Thus, locking down this function would effectively limit what the bad guys can do, and would not hardly annoy the average customer once the “regular” payee accounts are set up. But I guess banks prefer to spend our tax TARP money on lawyers and lawsuits rather than on improvements to their products that would actually benefit their customers.
Secure operating systems work even better.
Brian:
On articles about money being stolen, would it be possible to somehow work into the article that spyware, malware, and stuff like that is no small matter.
When I read articles like this, it’s easy to form a mental picture of sophisticated break-ins, but the usual route is almost always some common malware on a PC.
Thanks for publishing, I’ve enjoyed reading your stuff for years. Keep up the good work.
jp
Hi Jack. Whenever possible, I always include information about the malware that may have hit the victim. I think this is important information, but unfortunately in this case I was unable to learn what malware was responsible, or indeed even confirm that it was malware-related.
That said, I don’t doubt for a moment that malware *was* involved, and I would estimate that there is a better than 75 percent change that the culprit is once again our friend Mr. Zeus/Zbot.
Set aside the foolishness of calling the use of an IP address as a second factor in multifactor authentication. Set aside the many ways an attacker can compromise a system, keylog or otherwise obtain credentials. What worries me is that the bank seemingly has no abuse monitoring on account activity.
Are $100,000 transactions common for this customer?
Are *multiple* $100,000 transactions within a relatively short business timeframe common for this customer?
What percent of the account balance did these transactions represent (cumulatively) and is this frequency and amount atypical for this customer?
Has this customer transacted with these recipients before?
Credit card abuse programs analyze buying patterns. I would expect banks to do no less. If PlainsCapital represents an industry norm, we should re-think online banking. If PlainsCapital’s practices are anomalous in the industry, then it’s no surprise they are proceeding as you describe.
I looked at the hillaryinc dot com website and it appears they deal in machine tools and other industrial equipment, so a $100,000.00 transaction should not be out of the norm for them. And while they might not have directly done business in the past with anyone in Eastern Europe, other businesses do import equipment from there.
The gotcha here is that the business and the bank had no procedure in place for out-of-band authorization of money transfers. Cell phones are cheap these days, one can get a “TracFone” and put a 1-year card on it for less than $100.00 a year. This phone would be the contact number for the bank’s authentication team/software to send a text message requesting authorization for a specific transfer. The business has a pre-set validation password they can text back or voice-call back. More than one cellphone number for backup in case the primary phone is lost or stolen. The bank sits on the transaction request, not allowing it until the authorization comes in.
If such a system is compromised, it means an inside job, at the bank or/and the business.
The time will come when all transactions over a certain dollar amount will require a “second channel of authorization” – probably a voice confirmation or phone call from a reliably-traceable telephone.
In the meantime, if a bank senses a login from a computer that “doesn’t make sense” for this customer, like Romania, it should treat it with suspicion.
The bar to preventing this fraud is pretty low, for instance the european TAN system would have prevented this loss but thats irrelevant, what on earth would this bank do if this loss had come via a man in the browser attack that pwn’s dual factor auth, and where this loss came from the victims actual PC? or ‘local’ attacks via one of the proxy networks where the crooks use PC’s in the victims home town?
When banks realise that they cannot rely on authenticating to a point of reasonable confidence the better.
For anyone who’s not aware: http://en.wikipedia.org/wiki/Man_in_the_Browser
In all fairness, some banks do get it, I play havoc with my banks transaction profiling by using some cards only online or only when I travel. They false positive all the time, even with verified by visa etc, but they have an automated service ring my mobile within seconds, I answer a few out of band security questions and I’m good to go again.
No banks perfect though, their 2 factor device implementation is poor as it does not authenticate the transaction amount so I still call them mostly insecure 😉
Not that it was the best security BUT I’m guessing the bank didn’t hide the “features” from the company.
Sorry but if the features were laid out in advance and the company didn’t find any problem with them then, they have only themselves to blame for getting hacked.
My bank has crappy online security, I chose not to sign up for the online banking option.
The bank is in the right here though IMHO, the bank was not compromised, the company was. The company needs a security checkup more than the bank.
You know, given that a site like Facebook, which processes precisely zero financial transactions, has a feature which can tell when you’re signing in from an “unfamiliar location” (as reported by F-Secure last December,) you would think that any financial institution’s online properties would be doing this by default!
Seriously it is not rocket science.
I think we’re on the verge of a seismic shift in terms of how banks handle these incidents. Unfortunately I also think it’s far, far too late for the victims of these rampant thefts.
At what point does this become perceived as an “international incident” by a government? Witness Google v. China at the moment. This is a far more damaging series of crimes, and very clearly Russian, Ukranian and Romanian law enforcement are not doing anything about it.
SiL / IKS / concerned citizen
I agree with many of the commenters.
The “strange computer” notification happens with my bank if I use a computer that is not one of my usual computers.
The multiple transfers within a short period of time to “new” accounts, never used before.
These are all things that the bank should be aware of. Just the idea of a series of transactions within a short time that is out of the norm for this company should trigger some sort of pro-active response from the bank to the customer. Even if the transactions were delayed by a certain amount of time while being verified wouldn’t seem to be unreasonable.
Someone mentioned that the credit card companies will notice unusual cc behavior and contact the customer. That’s because the cc company gets to absorb the cost of the improper charges, less the $50 ‘deductible’. A business bank has absolutely NO incentive to stop the transfers since it’s up to the business customer to notice that extreme amounts of money have vanished from their accounts. They also have to notice this happening within a relativeyl short period of time.
I think the Hillary case should be an eye-opener to the business banks to step up to the plate and make the banking experience for their customers a mutually positive experience.
Does the bank require businesses to use Internet Explorer to do online banking? If so, do they provide a list of all the URLs that should be added to the “Trusted Zone” in order for their site to function?
It’s absurd that financial institutions insist a company allow its employees to not only use IE, but to do so with the general security level at the lowest setting in order for their site to work. Add to that the fact that no matter what a small company tries to set up for its employees to use, its Windows computers will reset IE to the default browser every time Windows gets an update, and you can easily predict they’re going to get pwned.
If you go to the hospital for surgery, the surgeon doesn’t insist on an HIV test first then only sterilize the instruments afterwards if the test is positive. Hospitals use “universal precautions.” If you would treat a patient’s blood differently if you knew that patient had HIV, then you should treat *all* patients’ blood that way. You assume a certain percentage of patients are infected but have false negative tests. It’s the only way to make sure all HIV positive blood is handled safely.
Similarly, you can’t expect computer users to keep their computers 100% safe, and you can’t expect an up-to-date AV program to detect 100% of infections. If companies who have computer experts on their payroll, like Google and Adobe, can get hacked, why do financial institutions set up systems that assume small businesses will be completely able to avoid it? Why don’t they have systems that assume hacking will occur occasionally, no matter how careful the customer is, and take that into account?
If your computer is hacked, the attacker has the passwords to your bank and your email account. He can use your computer as a proxy to log in to the bank from your IP address. He can always spoof your phone number for caller ID, even without having access to your computer or phone system, and if your business uses VOIP, I suppose he could log into your account and receive your incoming phone calls. He may get enough information to take control of your home computer, too. Banks need to assume those things can happen and are happening when there’s $800.000 of incentive involved. Then they need to come up with some type of “universal precautions” based on that assumption. (Not wiring hundreds of thousands of dollars to Romania without pretty good methods of confirming it would be a good start.)
The bank had an opportunity to take a step forward… instead they have chosen to take a step backward. Instead of suing the customer the bank should be working with its security vendor(s) and the customer to pinpoint where the security broke down then take steps to ensure it will not happen again.
Lets take a moment and think about this, how did this happen? If a business PC is capable of being hijacked, then this is a Windows security problem. *PERIOD*
Implementing additional security at the expense of the end-user and the bank in question, does nothing.
We are attempting to cure the symptom and NOT the disease.
D.
If you computer is owned by a trojan all bets are off, no matter what. That’s why Brian in the past has pushed for Non-Windows based OS or boot CDs, because once your owned there’s nothing the hacker can’t mimmick. Or just hijack a legiment session you started. 2nd factor methods just help with brut force and maybe some old fashion phishing schemes.
While I don’t know what standards and procedures USA banks may adhere to, here in Australia, it’s common practise to use two phase security.
With this procedure in place, in order to complete any transaction over any value, business customers request an on-line transaction, then get a confirmation via SMS, to their nominated mobile (cell) service.
The also get a follow up link (URL) to click on.
They can’t finish the procedure without the random key code provided via the SMS.
The SMS also provides the date and the amount.
This method is as near as drop dead secure as it can get, as even if your local computer system has been compromised, hijacking your SMS receipt, via a different service, is magnitudes of orders, more difficult.
(Unless your a three letter, US Fed. Gov. security acronym)
This method is also very low cost, is easily implemented and is easily sold to clients, as it is terribly secure.
The only consideration is that it takes slightly longer to process a transaction.
I am a business owner who uses this method, I find it terribly convenient.
As do banks, which find it helps to almost eliminate fraudulent transactions.
The there is no argument, as the audit trial will soon prove whether it was attempted fraud, or a criminal act of identify theft.
That’s funny! I had always read SMS is one of the easiest forms of communication to intercept and manipulate. Maybe you country has a different SMS form of service than the rest of the world?
http://www.zdnet.com.au/sms-two-factor-authentication-dead-in-3-years-nab-339284387.htm
let me get this right, PlainsCapitalBank, an $87M TARP recipient is using taxpayer money to sue a taxpayer rather than using it to beef up security to protect them.