Purveyors of fake anti-virus or “scareware” programs have aggressively stepped up their game to evade detection by legitimate anti-virus programs, according to new data from Google.
In a report being released today, Google said that between January 2009 and the end of January 2010, its malware detection infrastructure found some 11,000 malicious or hacked Web pages that attempted to foist fake anti-virus on visitors. The search giant discovered that as 2009 wore on, scareware peddlers dramatically increased both the number of unique strains of malware designed to install fake anti-virus as well as the frequency with which they deployed hacked or malicious sites set up to force the software on visitors.
Fake anti-virus attacks use misleading pop-ups and videos to scare users into thinking their computers are infected and offer a free download to scan for malware. The bogus scanning programs then claim to find oodles of infected files, and victims who fall for the ruse often are compelled to register the fake anti-virus software for a fee in order to make the incessant malware warnings disappear. Worse still, fake anti-virus programs frequently are bundled with other malware. What’s more, victims end up handing their credit or debit card information over to the people most likely to defraud them.
 Google found that miscreants spreading fake anti-virus have over the last six months taken aggressive steps to evade the two most prevalent countermeasures against scareware: The daily updates shipped by the legitimate anti-virus makers designed to detect scareware installers; and programs like Google’s which scan millions of Web pages for malicious software and flag search results that lead to malware.
Google found that miscreants spreading fake anti-virus have over the last six months taken aggressive steps to evade the two most prevalent countermeasures against scareware: The daily updates shipped by the legitimate anti-virus makers designed to detect scareware installers; and programs like Google’s which scan millions of Web pages for malicious software and flag search results that lead to malware.
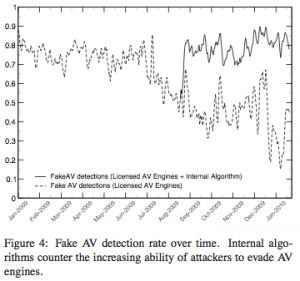
Google’s automated system scanned each potentially malicious page in real time using a number of licensed anti-virus engines, and all of the files were rescanned again at the end of the study. Beginning in June 2009, Google charted a massive increase in the number of unique fake anti-virus installer programs, a spike that Google security experts posit was a bid to overwhelm the ability of legitimate anti-virus programs to detect the programs. Indeed, the company discovered that during that time frame, the number of unique installer programs increased from an average of 300 to 1,462 per day, causing the detection rate to plummet to below 20 percent.
“We found that if you have anti-virus protection installed on your computer but the [malware detection] signatures for it are out-of-date by just a couple of days, this can drastically reduce the detection rates,” said Niels Provos, principal software engineer for Google’s infrastructure group. “It turns out that the closer you get to now, the commercial anti-virus programs were doing a much worse job at detecting pages that were hosting fake anti-virus payloads.”
In addition, Google determined that the average lifetime of sites that redirect users to Web pages that try to install scareware decreased over time, with the median lifetime dropping below 100 hours around April 2009, below 10 hours around September 2009, and below one hour since January 2010.
“These trends point to domain rotation, a technique that allows attackers to drive traffic to a fixed number of [Internet] addresses through multiple domains,” the company said in its report. “This is typically accomplished by setting up a number of landing domains, either as dedicated sites or by infecting legitimate sites, that redirect browsers to an intermediary under the attacker’s control. The intermediary is set up to redirect traffic to a set of active domains, which point to fake anti-virus distribution servers.”
Provos said the the domain rotation technique appears to be an extension of a “malware arms race” engineered to evade domain-based malware detection techniques.
“In fact, we noticed a distinct correlation between our improved ability to detect fake anti-virus, and the observed lifetime of each domain,” Provos said.
Last year, after a rogue ad on the New York Times Web site led to massive numbers of people being attacked by rogue anti-virus, I wrote a tutorial for The Washington Post called “What To Do When Scareware Strikes,” which details how to deal with these ambushes. The key is remain calm and avoid clicking on any prompts generated by the scareware. Check out that tutorial here.
In a separate report released Monday, Microsoft said its security products cleaned fake anti-virus related malware from 7.8 million computers in the second half of 2009, up from 5.3 million computers in the first six months of the year —an increase of 46.5 percent.
A copy of the Google report is available here (PDF).
Update, 4:47 p.m. ET: Security firm CA is reporting that the Storm Worm seems to have reawakened. According to CA, it was discovered bundled and distributed by Trojan downloader along with Win32/FakeAV or Rouge Antivirus malware.




All signs that we need to move towards stronger heuristics (after all CPU speeds are increasing on the consumer desktops far outside their true ‘need’), application whitelisting for dummies style software for the home desktop, and more sandboxed applications. Additionally MS needs to stop appeasing to the customer in certain situations namely UAC. The popups that ‘plagued’ Vista were for a good reason. Notice less ‘intrusive’ UAC controls in 7?
Zeus and other malware are doing everything to evade detection with various packers, polymorphism on each installation, etc. Totally crapping on the signature based detection of malware.. Yet AV vendors like to waste consumers time and continue to always be 3 steps behind the malware developers.
I think you would be hard pressed to find an AV vendor who spends much time creating ‘one to one’ or exact match ‘signatures’. Virtually all ‘one to one’ convictions will be built with automation. Most vendors do spend their time on generalized detections whether that be through generic signatures, machine learning, dynamic detection etc. etc.
What you seem to think AV vendors spend their time on might have been true several years ago but it’s not common today. Of course, even with a strong focus on generalized detection it’s still a *very* tough problem to solve as the number so clearly illustrate.
I think sandboxing and UAC are fine ideas but I think they will continue to be a failure with consumer audiences. People will simply click through, or worse yet, uninstall in favor of less intrusive solutions.
I think that the “click through” that happens with technologies results because we’re including the features but doing almost nothing to shove the information on what the feature is in front of the customer. You cannot legitmately call inserting infromation into the help file education. The average person won’t go looking in the help file for information – they’ll ask their friend who is just as un-informed. I see this every day at my work (comptuer sales). We need to make the education of good security practices and how to respond every bit as obtrusive as the scare ware is.
Well, the real anti-virus programs have their scandals too.
For instance they all (most of them?) label harmless programs used to pirate software as viruses and trojans.
They label harmless sites like 4chan as malware sites even though the sites don’t attack users.
How about if they just do their job and leave policing customers to the police?
I am asked to rescue half a dozen infected computers every week. The vast majority of these have Limewire and/or its competitors installed. No doubt someone in the family has downloaded a pirated version of some song or app, and a trojan came along for the ride. Most of these folks have no idea such a thing could happen. (I have given up cleaning infections — takes too long, success rate too low.)
I am sure this is the reason some security vendors blacklist file-sharing apps.
Of course, “it is your right” to visit shady file-sharing sites. But remember this is like hosting a party every weekend, and inviting the whole town. Sooner or later things will get out of hand. Badly.
“It is your right” to visit brothels without using condoms. But don’t come to me and expect me to pay for your cure.
For all those who say the malware removal is too hard with too low a success rate… I’d say from my vast years and years of experience that you don’t know shat about cleaning computers… I have never, ever… not once not been able to successfully clean a computer. Easiest methods: burn a good rescue cd/dvd (I suggest Avira). Boot from it… tell it to repair and if unable to RENAME. Let is scan all drives…. then when done… boot back to safe mode windows… have ccleaner, mbam, and a tdss killer on a usb drive/stick… if you don’t know what mbam or tdss killer is… google it or just stay ignorant. then load ccleaner and mbam in safe mode… yes you can install these in safe mode (unlike most win32/64 apps)…. now run your tdss killer…. if it finds anything… let it kill it then reboot back to safe mode…. now run mbam… let it do a full scan…. let it remove all it finds… it’ll ask to reboot… do that back into safe mode… run msconfig… remove from startup anything that is not legit… if you don’t know what is… you are in the wrong business…. then OK then EXIT allowing reboot into regular windows… remove any files that were renamed by Avira scan… remove any files/folders that were not legit that were in startup in msconfig…. then run ccleaner registry cleaner… fix selected issues (but just for giggles… make it backup the registry to c:\first run). then run it again… keep running until no issues… then reboot back to regular windows again… make sure you have a good AV/Security system installed already (if not… get the free MS Security Essentials)… update all… then for giggles again… run full deep scan on all drives… your done! Computer clean…. failsafe methods of cleaning a windows computer (win 2k, win xp, win vista, win 7) Servers too… it is not hard, just delicate… you either know or don’t know what the shat your are doing if you can’t successfully clean computers these days!
Not only are legitimate vendors hurt by the Fakes, but the number of pirate/keygen sites has exploded.
I have a Google Alert for any time my WinPatrol program is mentioned online. For every legitimate mention or review posted there are 10 posts on how to get a hacked version of WinPatrol PLUS.
Bill
Also if they label all chans as malware sites, then you can’t tell when one actually IS a malware site.
So mislabeling is the program refusing to do it’s job, it’s a kind of corporate denial of service attack.
Forget stronger heuristics. What is needed is already here.
If you use the Linux operating system, you already have a superior operating system from terms of ‘security by design’ rather than the Windows approach of extending a poor design by bolting-on afterthought security models. System processes in Linux run as separated users, users do not have Administrative privileges by default, and arbitrary applications can not perform Administrative functions such as installing software.
Add to that the SeLinux extensions *
and you have a system that provides a completely modular & policy-based system. If you want to (for example,) prevent unknown processes from ever writing to disk or opening a socket, you can prevent that.
If you start with a Linux distribution that installs SeLinux (or the similar AppArmor extension) by default, then you only have to configure any exceptions for particular programs that you trust.
While the rest of the world watches the Windows-based ecosystem crumble under it’s own weight of increasing complexity and increasing vulnerability, I continue to cruise through life with a fast clean and simple operating system which has no exposure to virii, malwares, or download-able trojans.
* http://en.wikipedia.org/wiki/Security-Enhanced_Linux
Linux is a good way to avoid viruses written for personal computers. MSM pundits, including Mossberg @ WSJ have endorsed Linux. Can’t see why this commenter was negged so severely. Nothing close to spam, not even hawking any Linux distro. No ad hominem attack on other POVs or users. No extreme language. A reasonable post, imho.
I agree that Linux is a more secure system. However, I must say that Linux is not going to end up on the shelves in laptops at Walmart anytime soon.
Linux, by nature, is far more secure than Windows. But where it adds security, it reduces usability. Most standard users want to be able to go buy a disc at the store, pop it into their computer and have it install the application of their choice. Unsavvy, computer illiterate people will not want to sit down and learn a brand new OS with new concepts and new ways of doing everything. Linux is not a user’s operating system.
Microsoft needs to change its paradigm. It is so f0cused on usability, features and sparkle that it lacks in the security market. Microsoft needs to focus on modeling their security to protect the system from the users and mitigate the damage that can be caused with better security models.
Do you think that Apple meets the criteria you lay out for Microsoft? Or are they mostly fortunate to have a smaller market share and a smaller target?
“But where it adds security, it reduces usability.”
This is what we call Fear, Uncertainty, and Doubt. (FUD)
There is no reduction of usability using a Linux-based OS. Far from it, there is much more usability in a Linux system than a Windows one. For example, almost every piece of software a user needs, from mp3 players to video players to office suites to games to databases are located in a safe repository that is tested so malware doesn’t slip in. Theoretically, you can set up everything you need WITHOUT having to scrounge around on the internet looking for .exe files of your apps. Secure? No. Not even usable.
It’s easier to use Linux than Windows now, check out Linux Mint or Ubuntu. Pop in the disc and 20 minutes later you have a desktop more functional than a Windows one.
There’s a small learning curve as the directory structure is a little different and the tools vary, but to say that familiarity is more important than usability is foolish.
Microsoft has introduced so many new features (bloat) that it has become even less secure. Instead of adding things, Microsoft should build small programs that do something really well, then build on top of those instead of putting everything into one application. (MS Office, for example)
Sure, Linux isn’t for everyone, but it’s far more usable than Windows. And you don’t have to worry about pretend anti-virus programs stealing your data.
Case in Point: Unless you slipstream an XP cd, you cannot install XP on a SATA hard drive. Sata drives now make up most of the hard drive market, along with newer SSD hard drives. You still need to hunt around for drivers even with 7, whereas Linux generally includes all drives you need.
I am writing this from a computer I built about 3 years ago, with an Intel motherboard and two SATA hard disk drives. It runs Windows XP Pro. There is absolutely no problem installing XP, with or without RAID, if you carefully install Windows according to Intel’s instructions. No slipstreaming.
You really should not disparage something until you have tried it. Talk about FUD.
I agree completely with SoloOwl… you obviously don’t know what you are talking about… if need be, at worst, you can install the SATA controller drivers during install…. but plenty of onboard controllers from that era were natively supported.
I am also a fan of Linux, but I cannot agree about the usability. Out of the box, Mint and Ubuntu are great but if you add peripherals, you often have to know more about your computer than the casual user. Drivers are not as easy to install if they are available for your scanner/tv card/etc. at all.
As far as being more secure, have any attempts been caught? Or is it that black hats are more likely to run Linux and not keen on voiding their bowels in their own sandbox?
I disagree. The solution to this kind of thing isn’t heuristics that magically work or better AV, its sandboxing browsers and not letting web sites remove UI elements like title bars, forward reverse buttons, etc.
I think locking down the browser and other applications is a good approach. However if you focus solely on the browser you run the risk of putting a steel door on a grass hut. Browsers are in vogue today for delivering malware but that could always change. I am a big fan of application sandboxing but I still think it falls apart if it needs heavy UAC from your average consumer.
Pretty much agreed with ApeLord on this one. If the application vendors were not making so many holes in their browsers to be exploited these scareware tactics would not be nearly as effective.
Just because you have the walk symbol at the cross-walk does not mean you should cross the street without first making sure a car is not going to hit you.
AV software is pretty much the same way. Just because you have it does not mean you should willy nilly click every link on the internet.
One of the rotating series of ads that accompanies this post on Brian’s blog says that “Thousands of PCs are infected with SPYWARE every day… Is Your PC Infected?” and offers a “Free PC Scan”. But one of the things I’ve learned from reading Brian’s work over the last couple of years is NEVER to click on a link that looks like that. Furthermore, this comes from “Ads by Google” which in my experience is notorious for foisting scams of various sorts on unwitting web surfers.
Brian, what assurance do you offer your readers that this advertisement is for a legitimate service? And why should we disregard everything you’ve been saying for years?
Brian, I hate to tell you this, but I have yet to see any ads on your site — just two gray frames labeled “Advertisement”. I run Firefox with NoScript, but allowing all scripts on your page makes no difference. I also run SpywareBlaster, which blacklists over 13000 items. On any other site, allowing scripts shows more ads, many of them annoyingly animated. Of course, this might not be the reason at all.
It doesn’t bother me that I can’t see ads supplied by or with spyware &c, except that it is unfortunate for your bottom line.
Ah rats. Mind clearing the cache for the site and trying again? I had some issues with the ads that were supposed to have been resolved yesterday. Thanks.
Hi Charles,
Thanks for your comment and question. I would agree that the ad you mention is not particularly well distinguished from the stuff thrown up by scareware. And I cannot vouch for the quality of the software it offers, no. Similarly, I do not maintain that I endorse any of the products or services that may show up in ads on this blog. Nor can I guarantee that a rogue ad won’t slip into Google’s network.
That said, there seems to be a big difference between an ad like this that shows up in a dedicated ad box on a site and those associated with scareware, which typically hijack the browser process with incessant pop-ups, and make clicking “no” and “cancel” equally ineffective.
I appreciate your willingness to allow ads from my site to appear in your browser. Please feel free not to click on any ads you’re uncomfortable with.
Vista and Windows 7 can be setup like Mac and *nix PC OS’s by setting up a single Admin account (named Admin) with a password. All other accounts should be Standard users. Any changes or program installs will now require the Admin password. No more “Cancel or Allow” popups when Vista/7 are set up this way unless one logs in as Admin, which should only happen as required. Users need to be educated that Vista/7 are capable of high security. PC companies set them up as targets for infection with the way they are shipped.
I agree that education is badly needed – and not just publishing books that get religated to the dust bins of the bookstore/office store shelves – but shoving that education under the end user’s nose.
On a side note – Microsoft years ago advocated disabling the Administrator account because the attackers would look for it without blinking. Admin as a username is really the same thing. I advocate using the end user’s last name 0r if a business – maybe the initials of the business. Makes it a slightly less obvious target to quickly written malware.
Bob Sireno wrote:
“…by setting up a single Admin account (named Admin) with a password. All other accounts should be Standard users.”
I fully agree here. The “BeyondTrust 2009 Microsoft Vulnerability Analysis” states that “90% of Windows 7 vulnerabilities are mitigated by eliminating admin rights”
I set my wife’s computer up this way 5 years ago & she has never had a virus attack.
I use Linux myself. Never had a virus & don’t need antivirus software because it’s built secure & I don’t operate as root/Administrator.
While undeniably more secure, you still have your own updates to be vigilant about. I forgot about a linux box on my network for a couple months and came back to find it compromised and trying to sniff the network/mail the results to a yahoo address.
To the kind of hacker not building a botnet, a linux box is still a juicy prize 😀
You can’t say on the one hand that you need stronger heuristics, and on the other hand say that the AV programs should not have any prejudice against piracy/filesharing sites.
Even sites that mostly have valid downloads will have occasional malware. Downloading illegal files is risky, and the fact that a file comes from a site known to allow that activity should be one of the factors taken into account when the program calculates the probability that something is malicious.
If it is your choice to download illegal software, then it’s appropriate for your AV program to warn you that you’re on your own. You’re going to have to choose a different authority to tell you which files you can trust. Don’t expect the same software vendors whose products are being pirated to cooperate with the download sites by providing an imprimatur for the safe ones.
I’m not clear on what sandboxing really is, but I’ve been running a stripped-down Linux in VirtualBox on Windows and using the Browser in Linux “seamlessly.”
This gives the impression that the Browser is running in Windows when it is really not.
The Tramp
This just speaks to the level of social engineering going on by the bad guys. As I’ve said before, there seems to be a growing deficiency in critical thinking skills by the general population creating a lot of low hanging fruit ripe for the picking. So you can implement all the security measures you want, but if the user behind the keyboard continues to be security unaware, this type of stuff will continue to increase.
You don’t have to postulate “a growing deficiency in critical thinking skills by the general population”. What has happened in the last 15 years is an expansion of home and small office computer use from a technically adept minority subculture to the general population.
Families are being encouraged, even forced, to acquire computers by local school systems, with no regard for training. They have no clue — not because their thinking skills have diminished, but because they are new to it and don’t know where to ask.
I agree – no one is going to look in the help files for obscure topics. They’re just going to set up as the default administrator and click through any prompts. They’ll install free “anti-virus” utilities not knowing or having anyone there to inform them that the functions of the “free” utilities stopped being enough protection by themselves years ago. Even the Geeks that are supposed to know don’t know how to properly secure computers because they’re relying on their frinds and the “corporate” sales pitches rather than good sound security advise which they don’t know how to find and don’t care to look for.
Unfortunately there’s plenty of bad advise. For example Google “turn off uac” and you’ll a half million hits.
Several commenters have mentioned education of the user community. The real problem is that computers are still too complex for the average user unless that user is technically inclined. How many people do you know that could set the time and recording schedule on their VCRs, a much simpler procedure than maintaining a computer (IMHO).
As the younger generations that were raised with a computer in the house mature, this will become less of a problem, but there will always be users out there who expect a computer to be no different than a TV, and put no more thought and effort into using it than they would to change TV stations. Until computers, or their successors, become more like a radio, and less like a cockpit, this problem will be with us.
I am a relatively computer savvy senior, and work with seniors to help them with their computer problems. This age group, in addition to having an innate apprehension of such a complex device. are frequently confused by the jargon, and acronyms. I would expect the boomers who used computers in their jobs would be more savvy, but still not all at the technical level needed to master the beast. I have recommended this site to many of my friends, seniors and younger, because it is a good source of information. Sadly, most don’t understand half of what they read here. Not a criticism of the site, just a fact of life.
Full disclosure: I’m a Mac user because I think Windows is more difficult to manage and use. I do not advocate for Apple however, and most of the folks I help run some flavor of Windows. My experience with W7 so far have been very favorable.
I travel around the country teaching an information security class to small businesses.
One of the tools that I need (and have a difficult time finding) is a set of case studies (can be brief) about small businesses who have been victimized by various threats.
Krebsonsecurity.com has some useful stories – buried in the rest of the material, but I would like to see a small document having useful case studies that myself and folks like me could use in our teaching.
One of the biggest problems that I have is that many (if not most) small businesses don’t think there is a problem or that they have a problem with information security (even if they do nothing to find/mitigate their vulnerabilities. They think this because they never hear of any such problems generally facing small businesses. They hear about the Fortune 500 companies, but not small businesses or organizations.
Suggestions?
Thanks!
Thanks for your praise and comment, Rich. Have you taken a look at the category in the right-hand column called Target: Small Businesses? It has all of the stories I’ve written on these attacks in one place.
http://krebsonsecurity.com/category/smallbizvictims/
Or were you referring to some other kind of resource collection?
Hi Brian,
I looked through three generations of your postings and what I find is pretty good stuff (of which, some I will use next week).
What would be more useful is to consider what could go wrong in a small business with IT/information/networks and how those things have happened to small businesses with what consequences. Much of what I’ve seen in the first three groups of stories is related to ZeuS infections which, while interesting, is a narrow range of a wide range of threats/consequences.
I’ve seen statistics (and stories) related to what happens if a small business loses all or a significant percentage of their business data. These are useful when discussing making and testing data backups.
I will dig a little deeper into your files to see what else I can come up with, but a topical organization under the umbrella of small business incidents would be helpful (and, which you might already have and I haven’t discovered yet).
Thanks for your help!
Rich
I’m glad to hear that someone is doing some sort of security training esp to small businesses who usually don’t have an IT dept. just someone who knows how to turn the box on.
A bit of a side note since you’re working with small businesses. I currently work in retail computer sales and another thing that can easily get a small business in serious trouble is improperly licenced software. Not really a security issue I know but many small businesses don’t know that they need to pay close attention to the licence agreements. I find myself constantly explaining to small business owners that no they legally cannot run the Home & Student edition of a software because they are a business. If possible you might try to mention that in your lectures. A good case study/resource is a book written about 10 years ago by a publisher in Garrison, ND because they found themselves in that bit of hot water. Title: Slapped hard for “Softlifting” ISBN-10: 0970522401. You’ll probably have to get that book on Inter-library loan as I believe it is out of print. I know the public library in Bismarck, ND has a copy.
Infection is optional. It’s a choice we all can make.
o InternetExplorer or Firefox/Opera
o JavaScript everywhere or Maintain JavaScript whitelist
o no filter or Privoxy
o Windows $$$ + AntiMalware $$$ OR Linux 0$
(Guess which side gets us repeatedly infected)