Most computer users understand the concept of security flaws in common desktop software such as media players and instant message clients, but the same users often are surprised to learn that the very software tools attackers use to break into networks and computers typically are riddled with their own hidden security holes. Indeed, bugs that reside in attack software of the sort sold to criminals are extremely valuable to law enforcement officials and so-called “white hat” hackers, who can leverage these weaknesses to spy on the attackers or interfere with their day-to-day operations.
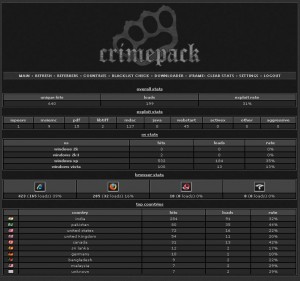
Last week, French security researchers announced they had discovered a slew of vulnerabilities in several widely used “exploit packs,” stealthy tool kits designed to be stitched into hacked and malicious sites. The kits — sold in the underground for hundreds of dollars and marketed under brands such as Crimepack, Eleonore, and iPack — probe the visitor’s browser for known security vulnerabilities, and then use the first one found as a vehicle to quietly install malicious software.
Speaking at the Syscan security conference in Singapore, Laurent Oudot, founder of Paris-based TEHTRI Security, released security advisories broadly outlining more than a dozen remotely exploitable flaws in Eleonore and other exploit packs. According to TEHTRI, some of the bugs would allow attackers to view internal data stored by those kits, while others could let an attacker seize control over sites retrofitted with one of these exploit packs.
“It’s time to have strike-back capabilities for real, and to have alternative and innovative solutions against those security issues,” Oudot wrote in a posting to the Bugtraq security mailing list.
Oudot says he is reluctant to release more information about the vulnerabilities until next month, when he is slated to discuss the findings at another Syscan conference in China. But in an interview with KrebsOnSecurity, Oudot said that in the days since his advisory was published, a number of folks in the security community have come out against the idea of sharing the exploit pack vulnerability information more broadly.
For one thing, detractors argue, telling the world about these flaws will, in all likelihood, prompt the creators of these vulnerable tools to ship updates that fix the security weaknesses. The latest version of Eleonore, for example — version 1.4.1 — is among several updates shipped for Eleonore during the past year alone. Critics also say while the vulnerability disclosure could give law enforcement officials and “white hat” hackers new tools to infiltrate and disrupt cyber crime operations, that information is just as likely to be exploited by novice hackers with far less noble intentions.
For his part, Oudot isn’t swayed by either argument.
“We will see if the defenders will be able to find vulnerabilities again,” Oudot said, of the likelihood that the exploit pack makers would patch the holes. “We can all decide to fight back, or to be victims. It’s like in some countries, there are many terrorists but nobody attacks them. It’s a choice of future.”
Oudot said his team has received several e-mails from legal and security experts questioning whether they might be violating any laws by disclosing the information.
“Also, we got some IT security friends who told us that it could be interesting to keep it a little bit secret for a short period of time, so that the blackhats who build such tools would not be able to react properly in a short future,” Oudot wrote. “Our goal was to initiate real discussions in the world about cyber security and how to handle cyber threats. Our main purpose was to offer a new vision, a new future action field. Now, the companies, the lawyers, the international organizations, etc., will have to make choices.”




I personally don’t want the detailed disclosures to the public; let the white hats share the knowledge! Fight fire with fire!
Congress needs to address this as a legal law enforcement tool and not a violation of some cracker’s rights, or something that could get the good guys in trouble.
Bravo to Oudot. I agree with JCitizen, fight fire with fire. And if anyone wants to make a federal case out of it, both literally and figuratively. this may be what is needed to get something done besides relying on strictly defensive measures.
Disclose – but hurt them first! It will cost the bad guys money if they have to start fixing bugs. If they have to start operating like a development shop, publishing and distributing updates, that activity will leave footprints for investigators. If they have to find programmers who produce better code, it will limit their choices. They can’t review candidates for reliability and skill without spending money. Looking for good programmers also leaves footprints.
At the same time, do what the bad guys do – exploit vulnerabilities immediately. This will force them into a rapid reactive cycle in which more mistakes will be made. It also exploits a weakness – their programmers don’t have to put up with the development cycles that commercial professionals do. If the work gets to hard, they’ll bail, and it will introduce more churn into the dev cycles.
I read somewhere (can’t remember where offhand) that most DDoS today is criminal vs. criminal; a tool used for competitive advantage. Disclosure of these types of vulnerabilities in the article may open a new doorway for additional criminal in-fighting. Imagine the new Zeus flavor, Kneber, had a flaw that allowed hijacking its nodes. While bad for the creators of Zeus and their customers, wouldn’t that also be a forensics nightmare for investigators? Perhaps that is a small price to pay.
Why disclose openly? Announce you have these, and let any legit security researchers, law enforcement agencies, etc – have the details – but unlike flaws in legit software, public disclosure of the flaws in malware doesn’t do anyone any good (assuming that the legit organizations can get their hands on it).
I’d be cautious about counter hacking thought – the legal framework does not seem to be in place to support that kind of activity, and you could be doing harm to 3rd party machines…
Oudot is somewhat overconfident IMO. The reason why these security issues are there and easily found is that nobody cares much about them. I can easily imagine that after this disclosure or maybe the next one the blackhats will put more effort into securing their products. And securing a relatively small piece of software like Eleonore really isn’t unrealistic. In future security researchers might find themselves confronted with exploit kits that don’t have any security vulnerabilities they could use.
I remember one of my security instructors asking us one question: “What’s the difference between a hacker and a security professional?”
The answer was: “Permission.”
So my question would be whom is authorized to go on the offensive? If its anyone (including white hats), we have essentially frontier or vigilante justice.
While the thought of becoming a virtual Batman might be interesting, it may also open up Pandora’s box. Although the criminal element is relatively organized at this point, what if this emboldens them to become ever more organized?
We may then see open warfare at that point.
The criminals are already as organized as anybody else. There are well organized groups and disorganized mobs amongst them, just as there are better organized nation-states and some pretty dysfunctional ones. It’s a free market world, nation-state cyber attackers and common crooks can both buy the same exploit kits. What they do with them may overlap too, isn’t the underlying reason for war economic?
The implied assumption in your instructor’s question that you can stereotype hackers with such a broad brush is simplistic, as is his answer.
Frontier or vigilante justice existed in the 19th century frontier because that was all they had. Just recently a registrar maintained several domains for 6 days which were used to deliver the zeus trojan. This is not exceptional. This is common.
Our choice is not between Vigilante justice or law and order, it is between vigilante justice and nothing at all. There is no governing body that can force these registrars to remove domains clearly used for criminal purposes.
The same thing is true of web hosting sites which continually support sites which volunteers in many organizations have already identified as existing for criminal purposes.
And I for one am sure not going to take the attitude that we shouldn’t annoy these criminal sociopaths for fear that they may get really crazy. It may take a good dose of frontier justice to get the world to recognize that something has to be done.
This isn’t some strange new opportunity. Antiphishing teams have been exploiting back doors purposely built into phishing kits for years. The back doors are not programming failures; they’re there so the creators of the kits can make some extra profit by surreptitiously harvesting data from the script kiddies they sold the kits to. No one is fixing them as long as the kits still sell.
It’s a race between white and black hats to find the phishing sites and grab their drop files before the domains are shut down for AUP violations. If the good guys get them first, the victims are notified and their accounts are protected. The only thing considered controversial is what happens if a company working for one bank finds data on victims from another bank — do they share the data with a bank that isn’t paying their fees? When Castlecops.com was operating, everyone got notified, but I don’t know if anyone has taken over that role since they ceased operation.
Even though the mitigation teams are private volunteers or private companies working for the banks, law enforcement is kept informed of everything they do. So there is no question of them facing legal liability for having hacked the hacked servers hosting the phishing kits.
“The back doors are not programming failures; they’re there so the creators of the kits can make some extra profit by surreptitiously harvesting data from the script kiddies they sold the kits to.”
Boy, you just can’t trust anybody these days 🙂
How often are malware distribution sites shut down? What’s the average lifespan for these cesspools?
Actually, I usually get fairly prompt responses from registrars and hosts when I report phishing. Phish and child porn tend to be the two issues almost all companies take seriously, even if they’re completely unresponsive regarding anything else. I figure phishing complaints get attention because they can’t stay in business without being able to process credit cards, so they can’t get on the bad side of the payment processors. Companies suspected of being completely in league with the scammers will respond to complaints, even while continuing to sign up more scammy domains. (The now defunct EstDomains was highly responsive to complaints, for instance.)
The biggest problem is that phish domains are also added to spam filters very quickly, so it’s hard to get your report through some companies’ spam filters. If you can find an online form on their websites for submitting complaints, it’s usually a better bet than an email from someone they don’t know (you).
To add to what AlphaCentauri said I would like to point out that they are never shut down in the same sense that a distributer of poisoned aspirin would be shut down in the brick and mortar world.
If someone opened a store in your local mall selling kits to inject arsenic into brand name aspirin it would be shut down immediately. You would not have to rely on volunteer groups to email the drug manufacturers and the drug retail stores with the hope that they would take action. There are laws and agencies with authority to enforce the laws in the brick and mortar world. Unfortunately, this is not true in the digital world of the internet.
As Alpha pointed out, fortunately, most registrars have cleaned up their act. I have noticed a big change in the registrars being used to provide domains for the botnets used by zeus to deliver their trojan since last year.
However, zeus still manages to find a registrar to register their domains. Reference Krebs’ blog titled “ZeuS Trojan Attack Spoofs IRS, Twitter, Youtube” and you will see that the registrar used, NAUNET-REG-RIPN (NauNet SP), kept the domains active over a six day period. From June 18 through June 23, they would deactivate a domain temporarily only to reactivate it later on. This simply would not be tolerated in the brick and mortar world.
But the botnets and their supporting domains/registrars aren’t the only problem. Many web hosting sites are notorious for hosting sites for phishing activity. I do not even have to mention them here, they are documented quite well by phishtank. See: http://www.phishtank.com/stats/2010/05/ under the heading “Top 10 Domains (valid phishes)”.
These are web hosting sites and most have been in the top 10 for a long time. Again, you have volunteers identifying member sites as engaged in phishing activity but somehow the host provider is not able (not required) to monitor their own sites and shut down the fraudulent ones.
So, my short answer would be: 1) not often enough and 2) too long.
Working on their level is no solution. It’s fun but it’s self-destructive. Make them obsolete instead. That’s easy.
Message from NL.
The same company, who was the first one to show how to strike back attackers, has published new results of research in Europe. Dramatical security issues for millions of people.
TEHTRI-Security, an innovatice cutting-edge french company, has just released new threats during “HITB Amsterdam”, an international conference for experts. They first explained that most Internet services (yahoo, hotmail, linkedin, twitter, facebook) are not hardened properly, so that millions of people take risks by using them. Moreover, they have shown that many phone devices with Wifi embedded are vulnerable to attacks, like the iPhone, the HTC, the BlackBerry and also the brand new iPad. To finnish, they explained some security issues on Thalys European trains, with the Wifi Internet access on board. Half a million of people could be concerned by those security issues related to privacy and security during their travels. Those issues are the same on many Internet access shared worldwide in airports, stations, trains, in-flights, hotels, etc. They are full of security vulnerabilities, because no real penetration test were organized with IT Security experts before the service was open to the public..
More information here (local press from Amsterdam) :
http://tweakers.net/nieuws/68316/wifi-netwerk-thalys-treinen-is-slecht-beveiligd.html
http://www.security.nl/artikel/33760/1/Internet_in_Thalys_kwetsbaar_voor_hackers.html