“Firesheep,” a new add-on for Firefox that makes it easier to hijack e-mail and social networking accounts of others who are on the same wired or wireless network, has been getting some rather breathless coverage by the news media, some of whom have characterized this a new threat. In reality, this tool is more of a welcome reminder of some basic but effective steps that Internet users should take to protect their personal information while using public networks.
 Most online services use secure sockets layer (SSL) encryption to scramble the initial login — as indicated by the presence of “https://” instead of “http://” in the address field when the user submits his or her user name and password. But with many sites like Twitter and Facebook, subsequent data exchanges between the user and the site are sent unencrypted and in plain text, potentially exposing that information to anyone else on the network who is running a simple Web traffic snooping program.
Most online services use secure sockets layer (SSL) encryption to scramble the initial login — as indicated by the presence of “https://” instead of “http://” in the address field when the user submits his or her user name and password. But with many sites like Twitter and Facebook, subsequent data exchanges between the user and the site are sent unencrypted and in plain text, potentially exposing that information to anyone else on the network who is running a simple Web traffic snooping program.
Why should we care if post-login data is sent in unencrypted plain text? Most Web-based services use “cookies,” usually small, text-based files placed on the user’s computer, to signify that the user has logged in successfully and that he or she will not be asked to log in again for a specified period of time, usually a few days to a few weeks (although some cookies can be valid indefinitely).
The trouble is that the contents of these cookies frequently are sent unencrypted to and from the user’s computer after the user has logged in. That means that an attacker sniffing Web traffic on the local network can intercept those cookies and re-use them in his own Web browser to post unauthorized Tweets or Facebook entries in that user’s name, for example. This attack could also be used to gain access to someone’s e-mail inbox.
Enter Firesheep, a Firefox add-on released this past weekend at the Toorcon hacker conference in San Diego. Eric Butler, the security researcher who co-authored the tool, explains some of the backstory and why he and a fellow researcher decided to release it:
“This is a widely known problem that has been talked about to death, yet very popular websites continue to fail at protecting their users. The only effective fix for this problem is full end-to-end encryption, known on the web as HTTPS or SSL. Facebook is constantly rolling out new ‘privacy’ features in an endless attempt to quell the screams of unhappy users, but what’s the point when someone can just take over an account entirely?”
In his blog post about Firesheep, I believe Butler somewhat overstates the threat posed by this add-on when he says: “After installing the extension you’ll see a new sidebar. Connect to any busy open wifi network and click the big ‘Start Capturing’ button. Then wait.”
It appears, however, that this add-on will only capture cookies from other users on a wireless network in cases where the attacker has already compromised the security of the entire network itself. Still, a number of free, open source tools are available to accomplish this task and could be used in combination with Firesheep to collect a ton of user logins on a busy wireless network. For example, Ettercap is an extremely useful program that lets you trick other computers on the local network into thinking that your computer is the wired or wireless router, effectively routing all of the incoming and outgoing traffic on the local network through your computer. Ettercap is a standard component of many Live CD installations of Linux that allow users to boot into a fully usable Linux distribution from a CD or USB device.
I pinged Butler for an interview about his add-on, but have yet to hear back from him. If that changes, I’ll update this post.
I tested Firesheep on a regular wireless network without running Ettercap and, sure enough, the only time Firesheep recorded any logins was when I logged in from the same computer that was running Firesheep: It did not capture cookies when I logged in to the same accounts from other machines on my wireless network. I tested this using two separate, commonly-sold wireless routers — with and without WEP/WPA encryption enabled — with the same results.
Combine Firesheep with something like Ettercap, however, and you have a very powerful, point-and-click method for hijacking social networking and e-mail accounts belonging to other users on the local network. This is exactly what McAfee director of research Dave Marcus found and explained quite well in his take on this tool earlier this week. Marcus also found that the add-on doesn’t collect cookies from other computers on a local network with the help of tools like Ettercap.
“What I like about Firesheep is that it is a very graphical way of showing people a problem,” Marcus said. “That said, it doesn’t do anything new. People have been talking about session and cookie hijacking since at least 2003. [Butler] has just come out with a nifty extension for you to show the extent of this threat graphically and uniquely.”
In any case, Firesheep was meant to raise awareness about this problem, and it appears to have succeeded in doing that. So what can you do to protect yourself? There are at least two Firefox add-ons that can dramatically increase the security and privacy of your Web browsing while on public networks, and that directly address the weakness exploited by Firesheep. These add-ons force any Web site you specify to encrypt all traffic (that is, always use an https:// connection), not just logins.
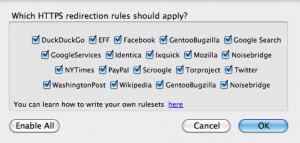
The Electronic Frontier Foundation‘s add-on, Https-Everywhere, is nice because it comes with about 20 sites pre-selected, including Facebook and Twitter. But some users may find its instructions for adding other sites to be a bit complex.
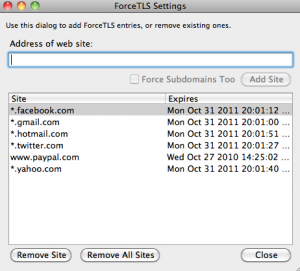
Another plug-in that makes it easier to add new sites is Force-TLS, although it does not include any sites by default.
One final note: The truly scary aspect of these types of network-level attacks is that they work against all computer users, regardless of operating system type. As for the helper add-on, Firesheep is available for Windows and OS X systems, and the authors say they are working on a version for Linux.
Update, 4:06 p.m. ET: A couple of readers have pointed out a blog post from Robert Graham at ErrataSec, which notes that the ForceTLS add-on may not succeed in forcing https on all sites. He also offers some reasons why I may not have seen the Firesheep add-on working to capture cookies over the network. Graham writes: “FireSheep works only as well as the underlying packet-capture. On a Macintosh, the adapter can be fully promiscuous, capturing everybody’s traffic on the local access-point. On Windows, some adapters (like Broadcom) will see all the traffic, others (like Intel) will only see your own traffic (useful for watching which of your own websites can be sidejacked, but not useful for sidejacking others).”




Which network are you testing. I am playing with Firesheep at a Starbucks right now and have access to 6 Facebook accounts and someone’s Hotmail account — which is letting me see things like their handy LOGINS folder which has the info for a bunch of their accounts including PayPal.
Firesheep is demonstrating a very real threat that has been ignored for far too long.
Saywhat — are you also using another tool to do ARP poisoning?
During the last weeks more and more users of Firesheep were looking for the possibility to use it in a switched environment. So the next step to support the target of Firesheep (showing how dangerous the usage of plain HTTP really is) was to find a easy solution to perform HTTP session hijacking in a switched network environment by combining Firesheep with ARP spoofing.
Our paper describes how to archive this goal with a user friendly interface.
You can find it here https://www.antago.info
Nope. On open networks like you find at most coffee shops Firesheep is a one click tool.
Ah. Well, I didn’t want to test it against unwilling participants on a live network. That will teach me, I guess.
Wifi is broadcast by nature, so once you’re associated with the network you see all traffic .. no arpspoofing necessary.
Perhaps you have a personal firewall or something else installed that is preventing the traffic from reaching winpcap?
I’m not a networking guru, but for Firesheep to work, wouldn’t the prospective victims have to be in the same collision domain? That is to maximize Firesheep’s exposure to other users’ packets & traffic.
So if two machines are plugged into a hub, Firesheep and Winpcap will allow this to work, but if you’re going through a switch (where each port is its own collision domain) Firesheep won’t encounter anyone else’s traffic.
Can you circumvent this with an ARP flood so that this works on enterprise-class ethernet networks? If so, anyone know when some other guy is going to release a Firefox add-on for automatic ARP flooding?
I bet there are some DNS poisoning or ARP related functions in SpyEye or Zeus. Man I wish I paid more attention in Scam U, but I was just there cause my parents made me go. Hindsight’s always 20/20!
Russ,
Circumventing the inherent security of a switch’s collision domain has long been shown to be not effective. You are right that under normal circumstances, sniffing on a switch port would only show traffic destined to and from the machine on that port (and broadcast traffic of course). However, an attack known as ARP spoofing can be used which essentially informs all users on that broadcast domain to use a new MAC address for the default gateway. That MAC address just so happens to be owned by the attacker, which then allows that attacker to sniff all the traffic that would normally go to the default gateway. The attacking machine then forwards the traffic to the MAC address of the real default gateway, and the users are none the wiser (besides seeing the MAC address change).
Not all wireless cards can sniff all traffic in windows. Other cards like with the Atheros chipset can see everything. Robert Graham at Erratta Security blogged about this earlier.
http://erratasec.blogspot.com/2010/10/re-firesheep.html
Just boot to Linux and you’ll be able to sniff in promiscuous mode. I have an Atheros card where I can do this in Ubuntu, but not in XP.
The drivers supplied by manufacturers for use under Windows are often limited. Sometimes an alternative driver can be used to resolve the lack of promiscuous mode. AFAIR, Wildpackets used to have some special drivers for use with their product, Airopeek.
So far I have tested this on a Windows 7 computer, a Windows XP ASUS netbook, and a Macbook Pro, with the same results.
Well now the lower end of the tabloid journalists armed with Firesheep will be staking out airports for the unwary celebs and politicians dirty secrets, should be fun! Any one know if Goldman Sachs and the like has a nearby Starbucks, insider trading by digital telepathy, be afraid, be very afraid.
It’s creepy when you think about it… but again, it’s been known for awhile. Thing is – people aren’t taking it seriously or just don’t care. If they cared they’d be doing something about it already.
On one hand I don’t like that it’s released and puts that opportunity into the hands of more people which could exploit it, but again – others were already out there. On the other hand, maybe since it’s now put in this ‘visual’ form and getting more face time, perhaps something will finally be done about it… it may just be the extra push needed to get people to care.
The problem is not with “people” (if you mean end users) the problem is with the websites like Facebook. And yes, its absurd that they have not dealt with an exploit that was documented back in 2004.
Exactly right.
SayWhat: I updated my post above with a link to a blog post from ErrataSecurity, which offers some explanation of why some people aren’t seeing this add-on capture cookies across a network.
Sorry – I meant mostly people like those who run the sites not caring. In some ways, individuals can secure themselves – but the reality is that most wouldn’t know how… and really, shouldn’t need to.
So FireSheep is bringing Session-Hijacking to the masses.
I for one can’t wait to see all the drama this will cause.
Brian, please check http://hackademix.net/2010/10/27/forcing-https-with-noscript/ (HTTPS-Everywhere actually reuses part of NoScript’s code).
Exactly. Giorgio Maone’s “Noscript”, which I assume everyone on here already uses, offers HTTPS forcing. No reason to add another addon.
I wasn’t aware of this, Giorgio. Many thanks for the link.
It’s probably worth noting that there are a couple of sites out there which are to my knowledge “well behaved”, they are Google (e.g. Gmail) and PayPal. Of course, as noted if someone saves their PayPal login in a hotmail account and then uses hotmail (which is apparently not well behaved), your protection is only as good as your weakest link.
FWIW the technology we want sites to deploy is called HSTS [HTTP Strict Transport Security] – . Well, of course we want sites to actually properly support accessing all content via HTTPS….
Are there plug-ins that force encryption for Google’s Chrome?
Try KB SSL Enforcer.
Brian, I believe the reason why you have not captured cookies from other machines on unprotected wifi, it maybe because your wireless adapter is not in promisc mode (sniffing mode).
Faust : Thank you for the tip about using Noscript to force websites to use https. Just done that and it appears to work for facebook and GMX (email). I should run up Wireshark to make sure the packets are encrypted. I have added the info to my blog and emailed my friends. I will be checking it with other websites I use as well.
A really cool tool which does a great job of demonstrating the inherent weaknesses and vulnerabilities in modern day “unencrypted” communications that have been going on for far too long.
Just an FYI, in my research it does not appear that the Twitter for iPad/iPhone apps are vulnerable, presumably because they are using other backchannels for communication.
“the attacker has already compromised the security of the entire network itself” What by logging onto his office network? Or connecting to his local coffee shop’s network? Or logging onto the pay-for-use airport network?
The whole point of this plugin is that it removes any need for technical knowledge and makes it easy for people to hijack others sessions.
Saying that, so far it hasn’t picked up any traffic from other computers on my local network while running on my MacBook Pro even with tcpdump pulling session cookies out of the air at the same time.
Well it isn’t so bad.. Anybody can download Nmap and some packet sniffer and exploit any vulnerable computer on the same network, and for the record you can also manage the traffic this way.
Some ISPs have ‘neighborhood hubs’ where a central router traffics a block of buildings or more or public open networks etc… So many computers are essentially on your network all the time and you could monitor them or do other nastier things, there isn’t anything really new about it except its coded into a fire fox addon, which is nice I guess.
If i am not wrong, any packet sniffer will intercept those unencrypted pages and you can just browse them, it is facebook and company who are at the fault for this.
First Handlers for other Sites like the german social networks
http://stacksmashing.net/2010/10/27/firesheep-handler-for-schuelervz-studivz-and-meinvz/
Just a couple quick things to add:
For anyone using HTTPS everywhere, it does not protect hotmail. If you are using hotmail, even with HTTPS everywhere it can still be hijacked.
Second, if you want to mess with people using firesheep there is now a program out there called fireshephard that sends out packets to deliberately crash firesheep. At least until firesheep is updated, one computer running fireshephard would crash all firesheep add-ons running on a wifi network.
Hi,
Most probably you know about the browser extension “ForceHTTPS” from Stanford Web Security Research.
I’ve been using it for some time now on FF.
Brian, given the the following statement writtin in this blog:
“This is a widely known problem that has been talked about to death, yet very popular websites continue to fail at protecting their users. The only effective fix for this problem is full end-to-end encryption, known on the web as HTTPS or SSL. Facebook is constantly rolling out new ‘privacy’ features in an endless attempt to quell the screams of unhappy users, but what’s the point when someone can just take over an account entirely?”
I was curious to know why you dont use HTTPS, but your URL is: http://krebsonsecurity.com. Doesn’t that make your site vulnerable too? Just curious.
Marlene — As John said, if you had to log in to my domain to access the admin panel, you would indeed be switched over to https://. However, just for visiting the site and viewing the content, what’s the need for https? What information are you trying to secure? Https:// really only encrypts data from point to point (and gives some measure of validation, although that’s not reliable). But if the data you’re passing from my site to your browser is just words and stories, what’s the risk that requires the https://?
Brian,
Thanks for the reply. It makes sense. However, I did have to log on initially to sign up to receive your blogs and admit I didn’t notice the URL at that time. Seeing how all further visits to your site have been through the link in your emails, it wasn’t until this blog that I noticed it!
It was more a question of curiousity that I posted the inital comment. My curiousity is now satisfied. Thank you for taking time to clear up the situation for me! Great blog!
Dear Marlene,
Do you have to log in to http://krebsonsecurity.com?
If so, you have a point.
Dear John,
It just struck me funny as I started this reply “Dear John,” as if I were sending a “See ya” note! LOL! Back to the subject at hand.
I have only posted comments here within the last week or so even though I have been receiving the newsletter for quite awhile. When I have, I have used the link to the site. It never occurred to me about the URL, prior to reading this blog. At that point, I did check the URL and just happened to notice it was an “http” and not an “https” and was curious as to why that was after it was plainly clear it was less secure according to what had been written.
Also, I admit, not every site I log onto is an “https” site, but when dealing with secure transactions, I am well aware of the site’s security. Additionally, I have been reminded of the risk I take by signing onto a less secure site as I have always been, to be more conscious of what personal information I give out. To be honest, I often use aliases unless the site is using the proper security and requires correct information.
Did I answer your question to your satisfaction? Just one question, what was the point you believed I might have if I have to log in here? Just curious, as usual!
The irony of all this is the level of trust you and everyone else has granted Firesheep and the developer that wrote the extension. Installing the extension requires granting admin privileges to the extension. Notice how the developer’s web site does not address why it needs this access? I think I know why it needs this level of access, but how does anyone know that the developer would not be trying to make yet another point: That too many people download applications, plugins, extensions, etc and grant the program access to their computer with no questions asked? The developer is a hacker afterall.
Yup, and all the source is available. You are free to inspect and build the tool yourself.
Has anyone heard more on Blacksheep? I hear it’s anti-Firesheep and actually alerts you when someone is trying to take/sniff your credentials through Firesheep.
Yes, it’s built on the same code base as Firesheep. Supposedly, you cannot have both Firesheep and Blacksheep installed in the same Firefox instance as they will interfere with each other.