 ATM skimmers come in all shapes and sizes, and most include several components — such as a tiny spy cam hidden in a brochure rack, or fraudulent PIN pad overlay. The problem from the thief’s perspective is that the more components included in the skimmer kit, the greater the chance that he will get busted attaching or removing the devices from ATMs.
ATM skimmers come in all shapes and sizes, and most include several components — such as a tiny spy cam hidden in a brochure rack, or fraudulent PIN pad overlay. The problem from the thief’s perspective is that the more components included in the skimmer kit, the greater the chance that he will get busted attaching or removing the devices from ATMs.
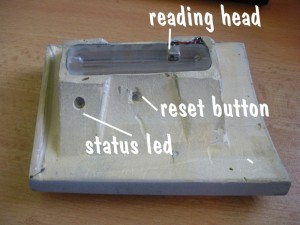
Thus, the appeal of the all-in-one ATM skimmer: It stores card data using an integrated magnetic stripe reader, and it has a built-in hidden camera designed to record the PIN sequence after an unsuspecting customer slides his bank card into the compromised machine.
The model displayed here is designed to work on specific Diebold ATMs, and can hold a battery charge for two to four days, depending on ambient temperature and the number of customers who pull money out of the hacked ATM.
 Functionally, it is quite similar to the all-in-one model pictured in the very first skimmer post in this ATM skimmer series, although its design indicates it may be identical to the one pictured here, which was found on a Wachovia ATM just a couple of miles from my home earlier this year.
Functionally, it is quite similar to the all-in-one model pictured in the very first skimmer post in this ATM skimmer series, although its design indicates it may be identical to the one pictured here, which was found on a Wachovia ATM just a couple of miles from my home earlier this year.
The tiny pinhole camera in the image above is angled so that it points at the PIN pad below and to the left, recording the victim’s 4-digit personal identification number to a flash-based memory card.
The real danger for the thief comes when he has to return to the scene of the crime to retrieve the skimmer, which contains not only the stolen card data that allows him to make counterfeit copies of the swiped cards, but also short, timestamped videos of each victim’s PIN.
 Thieves interested in hoovering up the captured data remotely might seek to invest in a skimmer that can transmit the purloined data wirelessly via Bluetooth or SMS/text message, as I wrote about in this post. However, wireless skimmers tend to cost quite a bit more than this model, which I found advertised on an exclusive underground forum: It is hand made to the customer’s specifications, and costs slightly more than $5,000 USD. Ah, but don’t count on paying for this badboy with a credit card: The seller only accepts cash (Western Union/Moneygram) or virtual currencies, such as WebMoney.
Thieves interested in hoovering up the captured data remotely might seek to invest in a skimmer that can transmit the purloined data wirelessly via Bluetooth or SMS/text message, as I wrote about in this post. However, wireless skimmers tend to cost quite a bit more than this model, which I found advertised on an exclusive underground forum: It is hand made to the customer’s specifications, and costs slightly more than $5,000 USD. Ah, but don’t count on paying for this badboy with a credit card: The seller only accepts cash (Western Union/Moneygram) or virtual currencies, such as WebMoney.
[EPSB]
Have you seen:
Crooks Rock Audio-based ATM Skimmers…The European ATM Security Team (EAST) found that 11 of the 16 European nations covered in the report experienced increases in skimming attacks last year. EAST noted that in at least one country, anti-skimming devices have been stolen and converted into skimmers, complete with micro cameras used to steal PINs. EAST said it also discovered that a new type of analogue skimming device — using audio technology — has been reported by five countries, two of them “major ATM deployers” (defined as having more than 40,000 ATMs).
[/EPSB]




These things scare the crap out of me. I know us folk who live/work in NYC tend towards being egocentric, but I really believe that this area is ripe for this kind of fraud. They look sharp enough that it’s a dubious claim that you’d notice. I used to only use the ATM near the bus station I use, and I always grab the card reader and pull as hard as I can to see if it comes off, then use my black wallet to cover my hand as I enter my pin.
But that wouldn’t stop this:
http://krebsonsecurity.com/wp-content/uploads/2010/01/lmpincapture.jpg
Maybe I should start writing checks to myself for cash and using the teller window.
A neighborhood branch at one of two local banks with which I do business physically inspects its outside ATM every 30 minutes during their business hours. The same bank recently alerted me of fraudulent use of my credit card # before the bogus transactions reached $20. Let this hereby be a plug for U.S. Bank.
I rarely use ATMs. However, I frequently swipe my check-card at gas pumps for non-PIN purchases. That’s a habit I am considering discontinuing sooner than later, having read previously in this blog that card skimmers are sometimes installed in pumps via inside access to their mechanisms.
I understand why people react the way they do to these skimmers. They’re pretty scary, and they make you feel violated, as does most theft.
It’s important to remember that having your money stolen from your account because of a skimmer may inconvenience you in the short run, but the banks can’t very well hold you liable for it. That’s assuming, of course, you spot the fraudulent withdraws if they don’t, which is unlikely.
The safest thing to use for purchases is a credit card that is not linked to the bank where you keep your money. If you have enough $$ in your bank account to cover ATM check-card charges, then you have enough to pay the credit card in full and avoid paying interest.
This is especially important for establishments that have swipe card readers (gas stations, grocery stores, etc.) that are often targeted by skimmers, but it goes for all purchases. It limits your exposure and you’re fully covered by consumer protection law.
Sorry for being dense, but is the name of the bank “U.S. Bank”?
Yes, the bank in question is indeed called “U.S. Bank”
I noticed my credit union’s latest ATM’s have flashing green LEDs at the insertion slot, and seem to have been designed to be as flush as possible. The card insertion area is also off to the side where it might be difficult to attach a skimmer at all.
I suspect ATM manufacturers are in a cat-and-mouse game on updating their hardware (a Bluetooth or obstruction detector would be very simple, no?), but ATMs aren’t replaced all that often, are they?
No, and that’s really a big issue here. A lot of the ATMs being hit are in fact older models that are probably nearing the end of their install life. As you might guess, these machines are not cheap to replace or maintain.
Who manufactures these skimmers? Are they simply made by criminal elements and sold covertly ilke malware?
If sold openly is there any possible legitimate use for them? If not, they need to be banned if they aren’t already.
You can find lots of places online *claiming* to sell these, but very few places where you can actually get them. Most are mass-produced, cheap and frankly not very good. The ones that really are worth buying (probably) are hand made, and if you lurk on the right forums and approach the “approved” vendors and ask the right questions, if they think you’re serious about buying they’ll ask for a photo of the ATM you want to rob, and custom make something or at least make sure what they’re sending you matches and fits the ATM you’re hacking.
I don’t know if these have any legitimate uses: I doubt it. I’m not sure what “banning” the possession or sale of these is going to accomplish, as they pretty much only have one function and the people buying and selling them both know what that use is.
My best theory as to how my credit card was fraudulently used (see second comment) for two online purchases is that the thief simply wrote down the needed info from it while it was out of my sight. That narrows my suspects down to two establishments. I don’t think the card was skimmed. The fact that the two fraudulent purchases totaled less than $20 suggests either that the thief was “probing” before attempting any larger scores, or else taking his ill-gotten gains by nickels and dimes in the hope that no one would notice. In any case, this was a first for me in over 35 years of using credit cards.
We seem to get issued a new credit card about every other month because of some data breach that might potentially include us. At least once, it was a server at a local restaurant where we eat that was selling credit card information collected from patrons.
I’m surprised most restaurants still expect you to allow the server to take your credit card out of your sight. They need to bring back the practice of paying at the register on your way out.
@Mark, my only firsthand experience with fraudulent transactions was similar, seemed most likely to have been a physical copy when the card was being swiped (in both senses of the term) at a restaurant. Around six to eight transactions were processed within a short time span, all of them in a local area on France’s Cote d’Azur. As I commented, I wouldn’t object to buying lunch in Nice if I were in Nice, but…
They were easily reversed when reported but there seemed to be no interest at all in trying to determine where the numbers were skimmed, by either the issuer or law enforcement authorities. That seems the biggest factor in encouraging continued thefts, no investigation to stop future theft let alone prosecution of those responsible.
@Infosec Because the chance of successful prosecution is near zero, law enforcement would be wasting resources to do much, and the establishments look at cost from both a customer confidence and direct dollar perspective – it’s not worth it.
It is is a one time thing – I would agree… but if it is a constant thing, where only little amounts are being spent from each account – then it would add up and it would be worth it.
Keeping records to see if it was just an isolated event or if there have been multiple issues would help – yes I fully understand that would be a daunting task, but I have to believe there’s someway to do it. Just like each police station has it’s system and then sends some or all of their info to bigger databases – it should be the same with this type of fraud. How can you connect the dots to see the big picture if you just ignore each dot when you find it?
Say I’m a waiter and I take the card information for every other customer I ring out. Spending an average of $30 per customer so as to not get caught. If I average 30 people a day – that means I took info from 15, and got to spend $450 a day – if it only goes on for a two months (5 days a week – so 40 days) that’s $18,000… If I spaced it out only doing it every other month for a year, it’d be $54,000… Would you still say it’s not worth it?
From a customer prospective – if I thought a waiter somewhere was taking card data, and no one would do anything about it, I’d stop going there.
@Law Observer: The chance of successful prosecution of the criminals in Russia stealing the card or even the criminals in Côte d’Azur using the card may be low. But why should that be the case for the restaurant employee located in the U.S. who actually handles the card and who enters the sale in a computer that records the transaction for that restaurant under his/her username? If clusters of cards whose numbers are stolen were recently used at a single restaurant, shouldn’t the card issuer contact the restaurant and find out who was working on those shifts and who was logged into their computer when those cards were used for payment?
If the risk of prosecution is zero, you’re going to get a lot of crime committed by people who aren’t ethical but don’t want a police record. If the risk of prosecution is low but real — and if conviction means serving your time at a federal penitentiary, where they don’t have to release non-violent criminals due to overcrowding — you’re going to have far fewer restaurant servers willing to get involved in the activity.
A+ reporting as usual..
I wonder how many of these guys just buy the ATM’s straight from eBay and start making molds?
If you wanted to test your ATM, how hard would you need to pull to see if anything comes off?
So you tug on the ATM and suddenly the skimmer comes off. Then what do you do?
What if the thief is watching?
Should I limit my use to only one ATM and memorize how it looks, so that I can recognise any tampering?
You could call the police or take it into the bank if applicable. You could use it to hit the thief in the face if he confronts you….seems doubtful to me. You could also take it home and shoot some awesome photos and send it to Brian with your story.
I liked this minimalistic external ATM card reader solution shown in this article (Dutch text but with pictures) http://webwereld.nl/nieuws/63504/ns-treft-opnieuw-maatregelen-tegen-skimmers.html
Perhaps someone here can imagine a way to attach a reader, any suggestions? To my mind its minimalistic design would make it extremely difficult compared to the current ubiquitous slot method.
It would be interesting to see (any video ‘caught in action’?) of how those crooks actually install these devices.
Cause when I am thinking about that, at least here , in Israel, ATM machines are located at the very nearby to the entrances to the bank branch, and each entrance is guarded by an armed guard during opening hours,who will approach you with “Can I help you” if you linger at ATM too long. So you would need nerves of steel to do it and be super fast. And at night (also during the day as well) it is being monitored by the CCTV all the time …
Hey Yuri, if you haven’t already, check out this piece I did earlier this year, which includes just such a video.
http://krebsonsecurity.com/2010/05/fun-with-atm-skimmers-part-iii/
I’m a lot more scared by the pin overlay models. For a long, long time I cover my hand keying the pin and I’m confident it would be next to impossible to be seen from virtually any angle. In the last 1.5 years I also test-pull the pin pad but I’m not sure how well those overlays might be attached and consequently how hard to pull to eliminate any risk. Unlike just covering your hand while introducing the ping, pulling on ATM elements seem, even when relatively discrete, to raise suspicions in bystanders or bank personnel who might be around.
I would be very concerned with pulling, pushing, wiggling or any maneuvers other than the expected cash-out procedure.
The ATM cam cannot distinguish between testing for a scanner and vandalism.
Want to disable a suspect ATM machine? Simple. Buy a small tube of crazy glue and empty it down the machine’s card intake slot. The ATM is toast, permanently.