Last week, I wrote about a “bulletproof hosting” provider that offers dodgy Web hosting that is insulated from takedown by abuse complaints or requests from Western law enforcement agencies. Today, I’ll look at one of that bulletproof provider’s biggest clients: Captchabot.com, a service that automates the solving of “CAPTCHAs,” those annoying agglomerations of squiggly numbers and letters that many online services require users to solve to help ensure that new accounts are not being auto-created by a computer.
 These so-called reverse Turing Tests can be exasperating for legitimate users, but these days they are little more than a speed bump for those who specialize in mass-creating bogus new accounts at popular online destinations like Facebook, MySpace, YouTube for use in spreading spyware and pimping spammy Web sites.
These so-called reverse Turing Tests can be exasperating for legitimate users, but these days they are little more than a speed bump for those who specialize in mass-creating bogus new accounts at popular online destinations like Facebook, MySpace, YouTube for use in spreading spyware and pimping spammy Web sites.
That’s thanks largely to services like Captchabot, which automate the solving of CAPTCHAs with the help of low-paid workers in China, India and Eastern Europe who earn pennies per hour deciphering the puzzles.
Captchabot charges clients based on how many thousand CAPTCHAs they ask the service solve: $1 buys about 1,000 solved CAPTCHAs. The service claims at least an 80 percent success rate, and customers only pay for CAPTCHAs that are solved correctly.
In their seminal paper (PDF) on CAPTCHA-solving services, researchers at UC San Diego earlier this year tried to estimate how many employees it would take to solve the daily workload of CAPTCHAs fed to the various services. The researchers guessed that Captchabot.com would need to have between 130 and 200 workers available more or less around the clock (for a look at how these services performed against CAPTCHAs required by MySpace, Google, Wikipedia and others, see this graphic.)
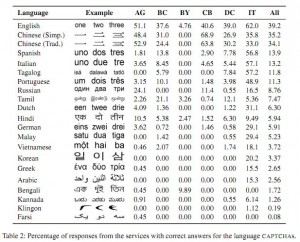 The researchers also sought to learn where most of the puzzle-solving workers resided, so they fed Captchabot and other services a variety of CAPTCHAs from different languages. The results, shown in the screen shot here, indicated that most of the workers were Chinese, English and Russian speakers.
The researchers also sought to learn where most of the puzzle-solving workers resided, so they fed Captchabot and other services a variety of CAPTCHAs from different languages. The results, shown in the screen shot here, indicated that most of the workers were Chinese, English and Russian speakers.
I contacted the owner of Captchabot.com, a hacker named Mirko Res, via online chat to see if I could fine-tune the UCSD estimates on the number of workers employed by the service, but he was unwilling to give an exact figure (“under NDA,” he explained). He did say, however, that the majority of the workers employed by his service live in Belarus, and that workers are only passed puzzles that can’t be solved by the service’s automated CAPTCHA-guessing algorithm.
“They using it for legal Webspam, like blog comments,” Res said of his operation’s customers. In fact, a widely-used forum- and blog-spamming tool known as XRumer relies exclusively on Captchabot to deliver its CAPTCHA-cracking capability.
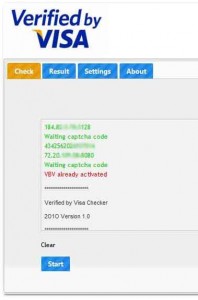 Other services that leverage Captchabot are far more plainly oriented toward illegal activity. Take, for instance, the program pictured here, a $10 product called Verified by Visa Checker. According to its author, the program takes a list of credit card numbers and checks to see if any of them already are enrolled in the Verified by Visa anti-fraud program.
Other services that leverage Captchabot are far more plainly oriented toward illegal activity. Take, for instance, the program pictured here, a $10 product called Verified by Visa Checker. According to its author, the program takes a list of credit card numbers and checks to see if any of them already are enrolled in the Verified by Visa anti-fraud program.
In the same hacker forum where I found the Verified by Visa tool I stumbled upon a discussion in which members were talking about a way they’d found to add credits to their Captchabot.com accounts without paying. I pinged Res about this, and he thanked me and said he’d sewn up the vulnerability, but not before fraudsters had used it to solve millions of CAPTCHAs for free.
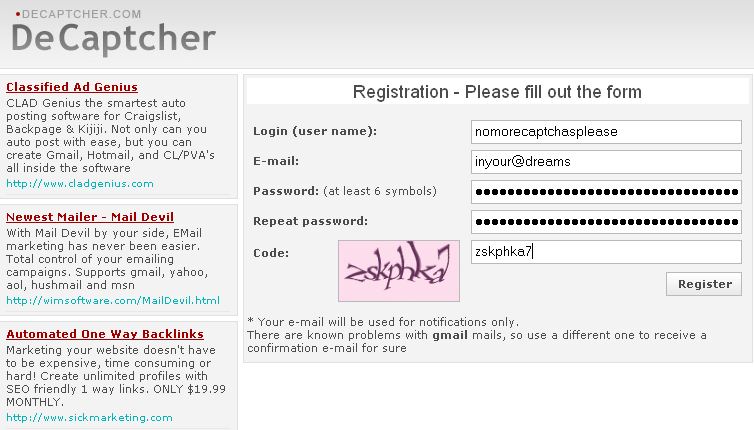
While Captchabot only accepts virtual currencies such as Webmoney for payment, other solving services named in the UCSD paper accept more traditional forms of payment, including credit cards. DeCaptcher, shown in the screen shot below, somehow is able to continue accepting both Visa and Mastercards for its service, even though according to one trusted source in the criminal hacker underground, a large number of DeCaptcher customers pay for the service using stolen credit card data.
Even at a fraction of a penny per solved CAPTCHA, it wouldn’t take long for fraudsters to rack up sizable charges using à la carte features that these services advertise. For example, DeCaptcha and Captchabot allow customers to offer payment over the market rate in exchange for a higher priority access to solvers when demand for system resources is high.
In the course of reporting this blog post, I signed up for an account at DeCaptcher and was mildly amused when the service asked me to solve a CAPTCHA before it would let me create an account. Unsurprisingly, DeCaptcher’s home page is littered with ads for third-party services that depend on its puzzle-cracking technology.




CAPTCHAs aren’t “Turing tests”, which are (hypothetical) tests a computer passes if a human can’t distinguish it from a human (by asking questions etc). Because by using a CAPTCHA a computer tries to distinguish between humans and computers, it is sometimes called a reverse Turing test.
Great post btw 🙂
Thanks, Martijn, you’re right. I tweaked the copy above to reflect that.
Verified by Visa is a crock! Other than conditioning people in poor online security habits, it provides a false sense of security and lends itself to phishing attacks.
I first came across it a while back on Verizon’s website. I immediately thought it was a phishing attack and cancelled out of the transaction. Even after learning it wasn’t an actual phishing attack and how the process works, I still didn’t feel any more secure. In fact, it made me feel less secure as it’s requesting more personal information. It annoys me to no end that Verizon is still using it!
Security researchers knock ‘Verified by Visa’ Security
http://news.cnet.com/8301-1009_3-10442305-83.html
http://en.wikipedia.org/wiki/3-D_Secure#Criticism
I was trying to purchase computer parts from a reputable online merchant. NoScript prevented the Verified by Visa dialogue from coming up, but the payment still went through and I still got my delivery. Even if this is just an implementation problem on the part of the vendor, I fail to see how Verified by Visa adds any value when you can just skip it.
‘Verified by Visa’ is not about security, it is about merchant/card issuer liabilities and relations. If a shop uses ‘Verified by Visa’, the risk/costs of a card abuse or charge backs stays with the bank, but the shop has, of course, pay for it. So, it is merely an insurance for shop operators by the card issuers.
If there would be the will to increase security for credit card transactions in the web, there would be more security tokens offered.
The simplest solution would imho probably be a text message for every transaction to a registered mobile number — with the payee, the charge and a transaction number, unique for the specific transaction, that had to be entered to authorize the whole transaction.
But, apparently, the costs of frauds are still not high enough to justify the costs of a text message…
I am a student in Computer Tech. I am doing a paper on computer anti-forenics. Could you please post a article on the subject in the next couple of weeks. Thanks
You learn more if you do your own homework.
Maybe even try out that remedial spelling class. I’ve hurd gud thangs bout it.
http://lmgtfy.com/?q=computer+anti-forensics
80% прохождения через капчу – это очень плохой результат.
Брайан, ты пишешь о каких-то дилетантах.
Babelfish:
“80% of passage through [kapchu] – this is very poor result. Brian, you write about some amateurs.”
2F-3000
Thank you, sir.
But Brian are studying the russian language, i help him, heh.
Капча==CAPTCHA, its russian slang.
I’m aware of that he’s studying Russian, but plenty of the blog readers ain’t. For example me, I can only wish I could, but I’m poor with languages.
Alex, I appreciate your tutoring. But I believe Капча is just a cognate. Not complaining: It’s one of the things that makes studying Russian technology press and writing so much fun and so easy: There are so many Russian words that when you read them aloud sound just like their English equivalent.
Да пожалуйста, Брайан, всегда рад помочь.
В общем это нередкий случай, но как я уже писал есть такие идиомы, которые резонируют больше в русском ухе, чем в английском. Например, бздя – идиома, обозначающая FreeBSD, но для русского уха происходит резонанс с жаргонным словом бздеть – бояться вплоть до непроизвольного испускания газов из кишечника. Поэтому тут должен быть очень осторожный подход к переводу “экспертами”.
Я бздю == Я боюсь.
Он (она) бздит == Он (она) боится.
Они бздят == Они боятся.
Чуваки, бздя, вернулись == Парни, боясь, вернулись.
По-поводу слова “капча” – заметь, по-русски неудобно говорить три согласных буквы подряд, поэтому буква “т” выпадает из произношения.
Yes please, always glad to help.
In general, it is often the case, but as I wrote there are idioms that resonate more in the Russian ear, than in English. For example, bzdya – idiom denoting FreeBSD, but to the Russian ear resonance occurs with the slang term bullshit – fear until involuntary flatulence from the intestines. Therefore, there should be very cautious approach to the translation of “experts.”
I bzdyu == I’m afraid.
He (she) bzdit == he (she) is afraid.
They bzdyat == They are afraid.
Man, bzdya returned == Guys, fearing returned.
In about the word “captcha” – mind you, in Russian uncomfortable talking three consonants in a row, so the letter “T” drops out of the pronunciation.
Alex,
By your own admission in an earlier post (in the column about Bredolab) you are yourself a bot-ware coder – only much smaller than Bredolab and other large botnets – you said. If true and you would agree to share with us some of your insight, I would be very interested in your opinion: what makes some botnets grow so large and other linger small, is it time ? effort ? money ? expertise ? promotion ? sheer luck ? a mixture of all those ? Do some botnet currators choose to stay small in order to stay under the radar ?
У меня есть маленькая сеть из 170000 ботов в Живом Журнале, но я не считаю себя специалистом по ботам. Я мастер Самоделкин, если кто знает советскую детскую литературу. Очень неспешно я три года делал программу управления ботнетом и вот буквально несколько месяцев назад она начала давать первую прибыль. Это не вирусная сеть и не спамерская. Как я уже сказал, я не считаю себя экспертом по вирусным ботнетам, но, так как сел за компьютер 30 лет назад и больше не вставал из-за него, то кое какое мнение имею.
Отвечая на вопрос, скажу – как и всё в этом мире, успех вирусной сети зависит от таланта её создателя. Но это уже вопрос к Богу, это его епархия. Создатель Зевс-сетей, насколько я понял, очень талантлив. Отсюда и успех.
I have a small network of 170,000 bots at LiveJournal, but I do not consider myself an expert on bots. I am a master Samodelkin if anyone knows of Soviet children’s literature. Very slowly for three years I did the program and control the botnet that’s just a few months ago, it started to give first profit. This is not a viral network and is not spam. Like I said, I do not consider myself an expert on viral botnet, but since sat at the computer 30 years ago and never got up from behind him, something which I have an opinion.
Responding to a question, I say – like everything else in this world, the success of a viral network depends on the talent of its creator. But this is a question for God, it’s his diocese. Creator of Zeus-based networks, as I understand it, very talented. Hence the success.
Companies should notice that CAPTCHAs are no longer a strong way to stop bots from getting into their systems.
If you want proof of that, try a Yahoo chat room.
After the age of 40 it is impossible to learn and properly speak new languages. After age 25 it becomes extremely difficult. The best age to learn a new language is around 5.
Its because neurons in your brain die etc…
This has been proved by various academic studies, you can look it up if you wish.
I would count on learning Russian any time soon if your over 25. You will be fighting against yourself, in fact there is a better chance you will learn latin over Russian cause English uses the same alphabet.
Someone learning a new language after childhood is unlikely to speak without an accent — but no one’s talking about Brian fooling anyone with his spoken Russian. The ability to learn the significance of visual symbols like letters and words isn’t lost. Otherwise no one would add any new words to their vocabularies as adults, and that’s clearly not the case.
Also, the common wisdom about language acquisition is based on people who grew up in a different world than now exists. In contrast to people a hundred years ago, most of us have heard people from multiple areas of the world speaking English in their own accents via recorded media while we were young enough to absorb that information. So the sounds of their languages aren’t entirely new to a late language-learner. If you can speak English with a Russian accent, you’ve got the capability to do better at speaking Russian with a Russian accent if you really make the effort.
Это не так – это смешно обобщить так!
это для Simon
Simon: “After the age of 40 it is impossible to learn and properly speak new languages.”
“Impossible” is too strong a claim. Although the ability to discriminate phoneme contrasts in new languages is diminished if those contrasts don’t occur in languages you already know, and the degree of brain plasticity in learning those contrasts is diminished very early in childhood, there is evidence that specific training can allow non-native speakers to develop the ability to distinguish and generate those contrasts.
See, e.g., http://accent-american.com/files/Download/CallanEtAl_2003_PlasticityWithFAT_impt.pdf
Here’s a new twist on the theme: NuCaptcha Engage Puts Security Feature in a Video
http://mediadecoder.blogs.nytimes.com/2010/10/25/nucaptcha-engage-puts-security-feature-in-a-video/
http://www.nucaptcha.com/