In any given week, I read at least a dozen reports and studies, but I seldom write about them because their conclusions either are obvious or appear slanted toward generating demand for specific products and services. Occasionally, though, a report will come along that is so full of useful data — and resonates so loudly with some of my own investigations — that it forces me to reassess my immediate research and reporting priorities.
One report released today that falls squarely into the latter category is Nart Villeneuve‘s superbly researched and detailed analysis (PDF) of “Koobface,” a huge network of hacked computers that are compromised mostly by social engineering scams spread among users of Facebook.com (Koobface is an anagram of “Facebook”). As the report describes, the Koobface infrastructure is a crime machine fed by cyber criminal gangs tied to a variety of moneymaking schemes involving Web browser search hijacking and the installation of rogue anti-virus software.
This report traces the trail of Koobface activity back through payments made to top criminal partners — known as Partnerka (PDF) — a mix of private and semi-public affiliate groups that form to facilitate coordinated malware propagation.
From the report:
“The Koobface operators maintain a server known as the mothership [which] acts as an intermediary between the pay-per-click and rogue security software affiliates and the compromised victims. This server receives intercepted search queries from victims’ computers and relays this information to Koobface’s pay-per-click affiliates. The affiliates then provide advertisements that are sent to the user. When a user attempts to click on the search results, they are sent to one of the provided advertisement links instead of the intended location. In addition, Koobface will receive and display URLs to rogue security software landing pages or will directly push rogue security software binaries to compromised computers. As a result, Koobface operators were able to generate over two million dollars in a one-year period.”
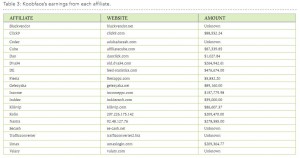 The report lists the nicknames of top Koobface affiliates, showing the earnings for each over the past year and the Web addresses of their associated affiliate programs. This is the kind of intelligence that — if shared broadly — has the potential to massively disrupt large scale criminal operations, because cybercrime researchers can use it to make sense of seemingly disparate pieces of information about criminal actors and groups. Nevertheless, it is rare to see this kind of raw data published, at least while those implicated remain at large.
The report lists the nicknames of top Koobface affiliates, showing the earnings for each over the past year and the Web addresses of their associated affiliate programs. This is the kind of intelligence that — if shared broadly — has the potential to massively disrupt large scale criminal operations, because cybercrime researchers can use it to make sense of seemingly disparate pieces of information about criminal actors and groups. Nevertheless, it is rare to see this kind of raw data published, at least while those implicated remain at large.
Part 3 of the report, titled “The Takedown,” indicates that operations to shutter the Koobface infrastructure may already be underway. Earlier this year, McAfee published an analysis I wrote about takedowns that classified them into two groups: “Shuns” — which seek to shame the peers of a malicious network into severing its connections — and “stuns,” which refer to efforts to disconnect the physical and network control infrastructure used by a botnet. According to the report’s authors, a stun against Koobface is in the works.
“Prior to the publication of this report, notifications were delivered to the owners of the infrastructure that Koobface is abusing,” Villeneuve writes. “They include: fraudulent and stolen Facebook and Google accounts, stolen FTP credentials, and dedicated command and control servers. We are working to synchronize notification to the operators of these elements in order to have an impact on the operations of the Koobface botnet.”
Almost certainly more to come soon. Stay tuned.





love the image at the bottom. is that dude on the bench supposed to be a fed or a reporter? it looks like the guy is hiding behind a copy of The Washington Post.
Heh. Dunno. But the graffiti on the bench says “Here was [cut],” whatever that means.
And on the right, instead of the usual “user name” and “password” is “[secret] meeting location” and “code word”, followed by “enter”
No, this image and the text next to it seem to mean a secret meeting (with money transfer?). With “Here was [cut]” on the bench implying full anonymity. I would consider “The Washington Post” that this shady guy is reading a tribute to Brian’s investigative work – there is no other reason why the Russian-speakers who apparently designed the image would put it there instead of the far better-known “The New York Times” for example.
Great read.
Is it just me or do both of the links to prior PDFs lead to a 404?
Brian – the link for the “Partnerka” is incorrect – it needs to point directly to the Sophos site.
Sorry Abe, qka. I think I’ve fixed the links, thanks.
Hi Brian,
Thank you for pointing to this report, indeed very well researched and readable, almost anyone would understand it, as specific terms are explained as they are introduced. Not only the report itself, but also the foreword written by Ron and Rafal, which I’m considering printing a few copies of and distribute it to my parents, elderly neighbor, etc.
Well look at the pic in the news paper and combined the here was cut and the dude hauling the monies off . This is only my thoughts of it , someone just got a piece of the pie . I still laughing my 6 o’clock off . Nice one .
Gelezyaka.biz is down. Usually I get annoyed by Verizon redirecting me to a parked domain with links to sites they think I must have misspelled. But this time their page includes links to this blog as well as to the infowar-monitor.net article. (Right after the link to a site selling styling gel, of course.)
Yes, Gelezyaka has been down for quite some time; definitely not a recent development. I actually forgot I had that image from their site until I saw the domain mentioned in the report, and was happy I still had it around.
So my ISP is not the only provider that believes we need a redirect. I have made numerous complaints via e-mail and telephone, but occasionally I am hit with the irritating redirect.
Hi I have a quick question. Virus blocking internet connection? My families computer was recently infected by some malware (win32/koobface?
I doubt a trojan (a type of malware, or “bad software,” like a virus) would block your internet connection. The bad guys want you hooked up to the internet on a high speed connection, and they’d prefer you didn’t know you’re infected.
A more likely possibility is that your ISP is blocking you, because an infected computer is a menace to everyone else. If you don’t know how to tell if you’re infected, you probably are. But you could just have a bad modem or router, or may only need to unplug the modem and router and let them discharge their power for a few minutes before plugging them all back in.
There are websites like spywarehammer.com and bleepingcomputer.com where expert people will help you diagnose and disinfect a computer free. (If you register at spywarehammer, be sure to choose the option to not have your email address be public — there’s a bug in the forum software and the default is public.) Read all the instructions and follow them in order. Be patient, as these guys are mostly professionals with other jobs doing this in their spare time. You can use a read-only CD or a thumb drive you don’t mind discarding to download the free programs they recommend using, then install them on the disabled computer that way. Don’t put any read/write storage device into another computer after it’s been in one you believe is infected.
Dean@which juicer are you stating you still have this infection ? Next not to taken up Brians forum but there are many products out that will get rid of them . Some are free but I’ll leave Brian with this answer like I said this is his forum . (win32/koobface? it does all kinds of bad stuff .
Koobface take down…
– http://www.pcworld.com/businesscenter/article/210608/researchers_take_down_koobface_servers.html
Nov 13, 2010 – “Security researchers, working with law enforcement and Internet service providers, have disrupted the brains of the Koobface botnet. Late Friday afternoon, Pacific Time, the computer identified as the command-and-control server used to send instructions to infected Koobface machines was offline… Coreix took down the servers after researchers contacted U.K. law enforcement…
– http://www.theregister.co.uk/2010/11/15/koobface_take_down/
15 November 2010
.
looked at the list of “affiliates”, i’m surprised to see some many familiar nicknames. half of the list are wellknown people, who’s location and real names are also known.
very interesting.
how Nart Villeneuv got all this information?