A new open source toolkit makes it ridiculously simple to set up phishing Web sites and lures. The software was designed to help companies test the phishing awareness of their employees, but as with most security tools, this one could be abused by miscreants to launch malicious attacks.
The Simple Phishing Toolkit includes a site scraper that can clone any Web page — such as a corporate Intranet or Webmail login page — with a single click, and ships with an easy-to-use phishing lure creator.
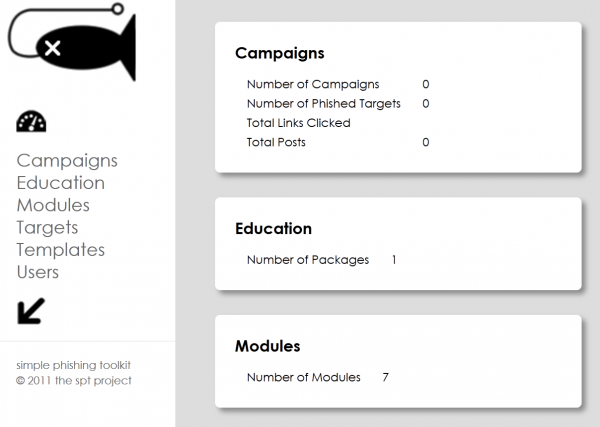
An education package is bundled with the toolkit that allows administrators to record various metrics about how recipients respond, such as whether a link was clicked, the date and time the link was followed, and the user’s Internet address, browser and operating system. Lists of targets to receive the phishing lure can be loaded into the toolkit via a spreadsheet file.
The makers of the software, two longtime system administrators who asked to be identified only by their first names so as not to jeopardize their day jobs, say they created it to help companies educate employees about the dangers of phishing scams.
“The whole concept with this project started out with the discussion of, “Hey, wouldn’t it be great if we could phish ourselves in a safe manner,'” said Will, one of the toolkit’s co-developers. “It seems like in every organization there is always a short list of people we know are phishable, who keep falling for the same thing every six to eight weeks, and some of this stuff is pretty lame.”
First released in October 2011, the Simple Phishing Toolkit is already in its fourth revision. The latest version includes an education module with the options to ‘educate on link click’ (to warn users about the dangers of drive-by malware downloads), upon form submission (credential harvesting), or not at all.
Partly to deflect criticism about the tool’s potential for abuse by miscreants, the toolkit doesn’t include the capability to capture data that recipients enter into forms in the phishing pages, although its creators say this feature will be offered in a future version as an optional add-on.
While more comprehensive open source phishing toolkits (the Social Engineer Toolkit for Backtrack/Metasploit, e.g.) have been in existence for some time, Will and project co-developer Derek said they wanted a more lightweight approach.
“We wanted a stand alone project that doesn’t cost money and doesn’t take a lot of devotion to learning,” Derek said.
The toolkit lives up to its name: It’s extremely simple to install and to use. Using a copy of WampServer — a free software bundle that includes Apache, PHP and MySQL — I was able to install the toolkit and create a Gmail phishing campaign in less than five minutes.
It seems that not long ago, the idea of organizations phishing their own employees was controversial. These days, there are a number of organizations that offer this awareness training as a service. If you’d rather design and execute the training in-house, SPT looks like a great option.




I phis this would not happen, but it is happening everywhere — even in my head. When you phis upon a star. . .
I think this is software that should not be available. I have no doubt that it will be used for malicious purposes. It should make a phisher’s job easier. All we can do is treat it as a PUA!
Now why don’t they work on an anti-phishing tool!
Hiding tools doesn’t make the problem go away, nor prevent attacks from rolling their own. And you’re not going to find any such thing as an anti-phishing tool when it is human judgement that is the root problem.
While I don’t necessarily agree with it, phishing your own employees is still controversial, regardless whether more firms offer the service. It is hard to sell managers on the idea that you trick and possibly publicly shame your own employees. Few people react positively to being tricked, and managers don’t want to make it seem like they’re mistrustful or insulting of their own employees.
If I ask you to hold the door for me while I struggle with a pallet of servers, then point and out you for letting me in the building, you likely will just resent me rather than learn a valuable lesson.
These are good points, but if you don’t do it first and spread the education (and practice incident response), the attackers will.
I understand your train of thought, but network admins must take time to train the end user. The reason a tool like this is handy is it will help you with training your end user. All to often network admins and people that work with network security forget that end users don’t know as much as we do. We must share our knowledge.
What I have been doing for years having annual training with all my users on email phishing and the dangers of email. Yes I have been sending fake emails. All employees with an email address know that at various points through out the year they will receive on fake email from IT. They know this is to test their awareness of what is going on and their training. If one good thing has come from this is I have less infections coming from email.
All the layers of security are useless if we do not take the time to train the end user on why security is the way it is and how the bad guy try to get into our secure networks. You did not study and train to do the end users job so you don’t know how to do theirs. Same thing goes for the end user. They have not studied, trained and keep up with the latest threats. That is part of our job and one of the best ways to protect your network.
What you both seem to be saying is that phishing your own employees can be very valuable, but it must be done with some sensitivity as well as political awareness.
Repeat offenders require a careful approach as well, ideally integrated with the organization’s HR department. Even if they don’t care about customers, they are a threat to everyone else’s continued employment if the company goes down in flames due to a breach.
Yes. 🙂
The point is not to publicly “out” failure and humiliate the person but to give the end user a chance to see something realistic and respond to it. People learn best by doing. As educators we can lecture until we’re we’re blue in the face and most of it will go in one ear and out the other.
The Navy has a concept to traing “train the way we fight”. While we train in the classroom sure most of the training is done real world – we just don’t arm the missiles or put rounds in the breach. If a captian really wants to train his security team for example he will call up a SEAL team. The training method is for the SEALS to break into various areas of the ship. By doing this we get the chance to excersize against “real” attackers and learn from them after it’s over. There are many more examples of this but by trainnig in a nearly live environment rather than lecuture the responses become second nature and more people will “get it”.
That is a great summary of my point. You can tell people all day long but until they see it in action it will not really sink in. I have had great success with the phishing emails. Once someone falls for it and sees how easy it is to create this fake email they become more aware of what is going on and think about what the email is asking them to do. So far I have not had anyone fall for the fake email twice.
It might be nearly as effective and more ethical to just tell your employees that you’re going to be using this — whether you do or not — so they’ll be on their guard against convincing phish emails.
Tell people about ZeuS infections and theft from payroll accounts, and they roll their eyes like you’re having paranoid delusions. But no one wants to be fooled by a coworker’s practical joke, no matter how gently it is handled by the employer. That more tangible threat is more likely to change their behavior.