Microsoft has issued an emergency security update to block an avenue of attack first seen in “Flame,” a newly-discovered, sophisticated malware strain that experts believe was designed to steal data specifically from computers in Iran and the Middle East.
 According to Microsoft, Flame tries to blend in with legitimate Microsoft applications by cloaking itself with an older cryptography algorithm that Microsoft used to digitally sign programs.
According to Microsoft, Flame tries to blend in with legitimate Microsoft applications by cloaking itself with an older cryptography algorithm that Microsoft used to digitally sign programs.
“Specifically, our Terminal Server Licensing Service, which allowed customers to authorize Remote Desktop services in their enterprise, used that older algorithm and provided certificates with the ability to sign code, thus permitting code to be signed as if it came from Microsoft,” the company said in a blog posting today.
Mike Reavey, senior director for the Microsoft Security Response Center, said Microsoft isn’t so concerned about Flame, which is now well detected (finally) by antivirus programs, and appears to have spread to a very small number of select systems. Rather, the company is worried that other attackers and malware might leverage the same method to aid in phishing attacks and other schemes that impersonate Microsoft to gain user trust.
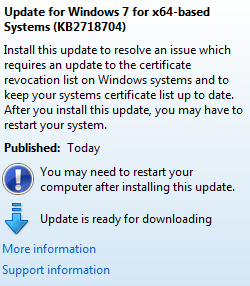
The update released this week (KB2718704) blocks software signed by these Terminal Server License Service certificates. Updates are available for virtually all supported versions of Microsoft Windows. The patch is currently being pushed out through Windows Update and Automatic Update.




It is curious how ‘flame’ has managed to stay within the boundaries of the immediate Middle East. You would think it would spread like wildfire, just like so many other new variations of modern malware. Maybe it has something to do with certain countries’ fastidious firewall policies; and their penchant for blocking free information.
Flame was probably used as a weapon in cyberwarfare. It was not designed to spread. Hence it did not spread.
What one should be worried about now are derrivatives of these kinds of malware that are designed to spread / build new botnets.
This is exactly why this security update was issued, to make it harder for others to use the same (exact) approach.
Of course if malware developers manage to get their porgrams signed by other (still) trusted authorities one is still an inclined plane wrapped helically around an axis.
Thanks rgb; the article did cover that detail. I’ll just use the excuse that I should have sipped my morning coffee first! :p
*∫∫*
[_]3
It’s quite simple – Flame didn’t spread. And if Flame did spread, then I really don’t think “firewall policies” could stop it. Flame had the ability to spread via USB (autorun and .lnk like Stuxnet) and via exploits (print spooler vulnerability like Stuxnet), but neither of the ‘spreading mechanisms’ was turned on.
I got this update this morning in Windows Update but didn’t know what it was for.l
fwiw, WinXP required reboot, Win7 x64 didn’t.
Hi Brian, I’ve been meaning to write for a while now to say, simply: “Thank you.” Thanks for all you do to help us stay current on potential problems. I’ve been reading your blog for years (since you were still with WaPo), and I have to admit that I’m often reluctant to install an update that’s been pushed to my computer (Microsoft or otherwise) until I’ve read a post from you on what it’s all about. So, again, thank you. Very much.
Thanks Xari, for your loyal readership. I’m very glad that I’ve been able to produce the type of content that keeps you coming back!
This is FAR more dangerous than it seems!
According to F-Secure, Flame had a module which attempted a man-in-the-middle attack against Windows Update!
This means that had the creators – presumably the US and/or Israel – gotten some code wrong – as they DID with Stuxnet which allowed Stuxnet to spread – this malware could have spread to scores or hundreds of millions of PCs worldwide!
The fact that it DIDN’T is no reason to be complacent!
A BBC news piece says that Flame as almost certainly targeted against Iran, just like Stuxnet, which means it was almost certainly created by the same people – either the US and/or Israel, if not necessarily by the same team (which implies the US which presumably has more such capable teams than Israel does.)
In other words, these morons put the entire Microsoft monoculture at risk over Iran – despite the fact that both the US and Israel ADMIT that Iran DOES NOT HAVE a “nuclear weapons program.” (And there is almost zero evidence that they ever did outside of a “feasibility studies” program prior to 2003.)
In my view, this puts Obama in the “impeachment” category since he authorized this crap.
You had me until your final sentence.
Thanks for the heads-up! I got that update this morning and installed it too. 🙂
Good thing it has an update for that now. I used to think that my Win 7 was like a foreign friend to me due to the many issues it had – that seem to be too bothersome to fix. When I got this update I wasn’t sure what it was for, but thanks for this info!
linux and bsd users’ laughter continues…
Hi log,
what’s a bsd user? I never heard the term.
Peter
@Peter,
A “bsd user” is someone that uses BSD Unix, one of the many derivates of Unix.
@log is insinuating, incorrectly, that Unix users don’t have to worry about security issues like Flame.
Especially since Flame has been hidden for what 2 years?
That means by the time Linux/Unix/Mac users are aware of viruses/worms threats on their systems its probably 2 years too late …
Yes; I’d imagine it wouldn’t take too much for a criminal to modify such malware to exhibit (strategic)worm behavior, and still be undetectable for some time.
“@log is insinuating, incorrectly, that Unix users don’t have to worry about security issues like Flame.”
they don’t have to worry about the thousands or millions of malware like windows users do, that’s a fact. rootkits for *nix? sure, but nothing like there is for windows.
Flame self-destruct cmd sent …
– http://www.symantec.com/connect/blogs/flamer-urgent-suicide
6 Jun 2012
.
The exploits and spoofing tricks it used to spread only would allow it to spread efficiently inside its local network, however the .lnk exploit could allow it to “escape” had it infected a USB key that was taken out of the area. Same deal if a mobile computer (laptop/netbook) was infected and brought to a new network.
UNLESS it played some UPnP magic to mess with firewalls and routers, there is very low chance of it using MS10-061 to infect boxes on another network, and the spoofing/update hijacking trick is also only effective on the LAN.
I’m surprised nobody else already mentioned,
But what are the chances that this thing was counting on a legitimate flaw versus using one that was engineered and purchased in the first place? If I was going to spend millions writing one of the most complex lines of malware on the planet, I would probably make sure the exploits it was based upon were going to be reliably present during the window they were needed for…