The author of Blackhole, an exploit kit that booby-traps hacked Web sites to serve malware, has done so well for himself renting his creation to miscreants that the software has emerged as perhaps the most notorious and ubiquitous crimeware product in the Underweb. Recently, however, the author has begun buying up custom exploits to bundle into a far more closely-held and expensive exploit pack, one that appears to be fueling a wave of increasingly destructive online extortion schemes.
An exploit pack is a software toolkit that gets injected into hacked or malicious sites, allowing the attacker to foist a kitchen sink full of browser exploits on visitors. Those visiting such sites with outdated browser plugins may have malware silently installed. In early October 2012, security researchers began noticing that a new exploit pack called Cool Exploit Kit was showing up repeatedly in attacks from “ransomware,” malicious software that holds PCs hostage in a bid to extract money from users.
“Kafeine,” a French researcher and blogger who has been tracking the ties between ransomware gangs and exploit kits, detailed Cool’s novel use of a critical vulnerability in Windows (CVE-2011-3402) that was first discovered earlier in the year in the Duqu computer worm. Duqu is thought to be related to Stuxnet, a sophisticated cyber weapon that experts believe was designed to sabotage Iran’s nuclear program.
About a week after Kafeine highlighted the Duqu exploit’s use in Cool, the same exploit showed up in Blackhole. As Kafeine documented in another blog post, he witnessed the same thing happen in mid-November after he wrote about a never-before-seen exploit developed for a Java vulnerability (CVE-2012-5076) that Oracle patched in October. Kafeine said this pattern prompted him to guess that Blackhole and Cool were the work of the same author or malware team.
“It seems that as soon as it is publicly known [that Cool Exploit Kit] is using a new exploit, that exploit shows up in Blackhole,” Kafeine said in an interview with KrebsOnSecurity.
As detailed in an excellent analysis by security firm Sophos, Blackhole is typically rented to miscreants who pay for the use of the hosted exploit kit for some period of time. A three-month license to use Blackhole runs $700, while a year-long license costs $1,500. Blackhole customers also can take advantage of a hosting solution provided by the exploit kit’s proprietors, which runs $200 a week or $500 per month.
Blackhole is the brainchild of a crimeware gang run by a miscreant who uses the nickname “Paunch.” Reached via instant message, Paunch acknowledged being responsible for the Cool kit, and said his new exploit framework costs a whopping $10,000 a month.
At first I thought Paunch might be pulling my leg, but that price tag was confirmed in a discussion by members of a very exclusive underground forum. Not long after Kafeine first wrote about Cool Exploit Kit, an associate of Paunch posted a message to a semi-private cybercrime forum, announcing that his team had been given an initial budget of $100,000 to buy unique Web browser exploits, as well as information on unpatched software flaws. Here is a portion of that post, professionally translated from Russian:
Dear Ladies and Gentlemen!
Everyone is aware of the problem which exists now on the exploit market! To solve this problem, our team prepared the following exclusive program of purchasing new browser and browser plugin vulnerabilities. Not only do we buy exploits and vulnerabilities, but also improvements to existing public exploits, and also any good solutions for improving the rate of exploitation.
The “meat” of the project: We are setting aside a $100K budget to purchase browser and browser plug-in vulnerabilities, which are going to be used exclusively by us, without being released to public (not counting the situations, when a vulnerability is made public not because of us).
Not only do we purchase weaponized (ready) exploits, but also their descriptions and proof of concepts (with subsequent joint work with our specialists).
Paunch’s team emphasized that they would not buy exploits that were already public, and that newbies to the fraud forum who nevertheless had good exploits could work with the crimeware team via an agreed-upon 3rd party.
It’s unclear how many takers Paunch is attracting to Cool Exploit Kit with its hefty price tag, but according to Kafeine and others, the new kit is being used exclusively by two different crimeware gangs. One of the gangs is using Cool to spread the Reveton ransomware that I profiled recently.
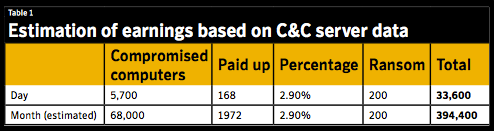
If any miscreants have the ability to pay $10,000 per month to rent an exploit pack, the gangs spreading Reveton certainly fit the bill. Symantec recently published an in-depth analysis of the ransomware scourge (PDF), and in it the company managed to gain access to a control panel used by one ransomware gang that showed the number of incoming connections to the booby-trapped sites used in the scheme. Symantec estimated that this group extorted from ransomware victims more than $30,000 per day, and likely close to $400,000 per month. This is on par with the amounts I found one ransomware operation was earning back in August 2012.
The best way to avoid ransomware and other nasties is to keep your system up-to-date with the latest security patches, and to remove software you don’t need or use. If your system does get infected with ransomware, by no means should you pay the ransom. F-Secure offers a free removal tool, and Microsoft claims its Windows Defender Offline Disc can remove most ransomware.




It’s just amazing! I still get folks asking why people write Waldemar. Now I have the answer! I always knew it was profitable, but $30,000 PER DAY?
Perhaps there would not be many exploits to be used if Kaffeine and other security “researchers” quit supplying the material!
Regards,
The stuff posted here in many cases is a report on what is being posted on the sites/forums selling this stuff.
=> Is already in use => the information is not new to those that develop this kind of software.
It is not clear from your post, but maybe you are alluding to responsible disclosure practices?
That is, that researchers (no quotation marks needed) should only inform the developers of the software (Microsoft, Oracle, etc) and not make their findings public?
This has been tried. It leads to firms not fixing the vulnearbilities because there is no preassure from the public to do so. Leaving attackers (who can find vulnerabilities independently of the researchers. As seen above they have a pretty strong incentive to do so) a huge time window to use the exploits.
Therefore making these vulnerabilities and developments public is the best strategy to insure that they are fixed in a speedy fassion. And hence to increase the security of people on the internet.
Don’t hesitate to correct me, I did not research any of this. I am just procrastinating (should be researching (something else)).
I think this speaks more to the growing momentum google and other have had in success in the bug bounty programs. It isn’t only the bad gus buying exploits, you have goverment agencies who buy them ( foreign and domestic) you have the security companies and vendors buying them, and then the bad guys are vuying them as well. I think this speaks more to keeping exploits that are unknown out of the domain as long as possible. I think the bad guys are finding the exploits are being detected and a solution or patch coming too soon for them to attain a lot of success. We all know they are using vulnerabilities that are known and not yet patched but look at the attacks that the chinese have been using, 7 to 8 unknown exploits were used for some verious long periods of time to capture a lot of info with a great deal of success. Now imagine if you could do the same with a financial goal in sight, it could turn oput to be very profitable. To PAY 10, 20, 30000 for a unknown exploit that could reap you hundreds of thousands or millions. I think the bad guys are seeing this as a small price to pay for something that could be quite lucrative. Could be the watering hole attacks have shown them how a unknown expolit could lead to a great pay day
This sort of thing is another indication that cybercrime is a “growth industry” that will show no signs of slowing over the next decade or two unless the computer and telecommunications industries can come to some standard on embedding security design into their infrastructure and products.
In my view, cybercrime is where the drug business was…in the 1920’s just after the anti-drug laws were passed which enabled the rise of organized crime; i.e., it’s just getting started.
They just today arrested some Algerian kid in Thailand who has broken into 217 banks, supposedly one hit for $10-20 million (which I doubt; I’d like see details), and has apparently been just flying around the world living it up on the proceeds of his random hacking.
I’m definitely in the wrong line of work. 🙂
Richard,
I am wondering if that 10mm usd plus figure the Thai are quoting is the actual loss he allegedly stole in a single act (I doubt this, for a number of reasons), or what the bank estimates is the “damage” to their systems — which tends to be more the situation in almost every case like this.
Quoted in the article:
“We are setting aside a $100K budget to purchase browser and browser plug-in vulnerabilities
How far will $100K get them? See the second figure in this linked article from March, 2012:
http://www.forbes.com/sites/andygreenberg/2012/03/23/shopping-for-zero-days-an-price-list-for-hackers-secret-software-exploits/
Not very far as browser exploits *start* at $60,000 to $80,000 U.S. and browser plug-in exploits *start* at $40,000 U.S. There appears to be a highly competitive market for selling one’s exploits. The miscreants may have to start the Cool Exploit Kit with purchases of exploit “descriptions and proof of concepts”.
P.S. Am assuming that currencies are all $ U.S. (if incorrect, I’m sure that someone will let me know).
I think you are falling prey to the idea that all money is created equal, and failing to grasp that it is not.
For one thing, not every exploit-finder wishes to arm a government potentially against them and their friends. Not everybody trusts governments (or the middlemen who “sell” to them indiscriminately in most cases), especially in the ‘underground’, in general, and the ones who do tend to use these exploits in the loudest manner often have the most difficult track record when it comes to justification.
Once you do sell to a government or third party, you don’t tend to know what is done with anything you’ve sold — you have no say, while they have the only say. While ‘fraud’ may be ‘bad’ it is still a known quantity — more known than the majority of governments.
And as I stated — all money is not created equal: To assume everybody sees $40k from an American or European government contractor who wants to know everything about you (or at least will likely be very interested in you after) as equivalent to maybe even half that much from somebody who asks few or no questions is to lack any understanding whatsoever about what is currently going on in the world. I would presume once you are on their ‘list’ as a supplier, you will always be on a list of some sort. Governments (not only the US) don’t tend to trust the people that supply them with their weapons, especially ones they have little control over.
Last but not least: Exploits have always been for sale in the ‘underground’. This really is not anything that new, it is just more open than usual (and probably more of a guaranteed paycheck, given I am sure that Paunch cares about his reputation, and the ‘underground’ tends to be self-reinforcing when it comes to scamming and ‘trust violations’).
PS: Brian, your site ate my first several firefox attempts at this comment. I wish you did not insist on scripts so much. Or are you moderating?
No, I did not filter anything. I have three copies of your comment. Only one got published. Sometimes, it just has a delay before a comment is posted.
Ok, actually I did try more than 3 times by the time it posted, but this is good to know, as I believe it is the browser I was using (your site never plays well with Firefox with NoScript and privacy plugins on Linux , ironically enough). Thank you for replying.
Strange. I use all of those things you just mentioned and never seem to have a problem.
Maybe it would help if you set your controls for NoScript and other privacy plugins, to off. Brian’s trying to make a living here! I always set all of that and AdBlock Plus(or etc, for Chrome) to the off mode, by URL, while visiting his site.
With Linux you have little to fear – so far I’ve not been attacked by any adds/links here at KOS, and I’m running Windows.
His ads all use flash; I often do enable it for his site alone if only to expand the ‘not useful’ comments when they show up. Putting aside security issues alone, if you’ve ever used the flash plugin viewer in Linux you will know it tends to go “out of control”. I think it may be my privacy plugins anyway, not noscript. I am not trying to deprive Mr Brian Krebs of his ad revenue. 🙂 I’ve repeatedly said if he advocates for people to use security methods, his site should reflect the use of those methods. Flat image ads, for instance.
Just curious; have you tried or are you using Chrome/Mozilla; or will your distro run those browsers. I’m ready to try Mozilla on Puppy, but I haven’t reached that project yet.
I used to use Chrome *only* for Brian’s site. I have ceased installing any google software in my machine though. I found a smaller offshoot of mozilla to use (still, only for posting on Brian’s site). Maybe this is to make Brian feel special enough to have his own browser? 😛 I think Opera may also work. I still advocate using something that has strong privacy, cookie controlling and script controlling plugins (or build-ins) to visit anywhere else. I am minimizing an attack footprint by using this only for this site (maybe one other with the same problems). The same might also be accomplished by having two installations of the same browser, but I find this difficult to maintain.
@voksalna, thanks for your well-considered reply. It was enlightening. While my comment does not address Russia (or, more broadly, the CIS), the article at referenced by my link states that zero-day exploits are payed “very little money” in Russia. Not that it isn’t an excuse for leaving it out of my post, but just giving the Forbe’s writer some credit.
It’s sad that the only alternatives for exploit hunters are “the underground”, “middle-men” that [often] sell exploits to governments and the few ISVs that pay bug bounties for vulnerabilities (Google is a prime example).
Given the financial losses that individuals, the financial industry, many other businesses/organizations and governments incur from exploits, one would think that a non-profit organization would spring up to purchase exploits, take them off the market and work with ISVs to fix the vulnerabilities targeted by the exploits. This organization, by its charter, would not provide the exploits to “the underground”, “middle-men”, governments or private industry and would pay more per exploit than “the underground” and less than the “middle-men”. For those exploit hunters that currently work with “the underground”, such an option might provide them with higher payments for their work and keep them out of trouble with their “friends”.
Rabid Howler Monkey,
Thanks for your equally cogent response. The Forbes article is not speaking of Russian (or CIS) with regards to prices, but when it comes to exploit sales, the location of the person discovering the exploit is largely irrelevant. It is true certain things have a higher price tag in “the West” but that doesn’t mean the “value” is lower or higher; often it is more a matter of your environment when it comes to who you are willing to deal with, from what I’ve seen. In fact, I’d say the “value” of an exploit is far *higher* in Russia or CIS, as a large part of ‘value’ is the ability to wring out possible uses for a thing (something we are good at).
Your idea for a ‘foundation’ of this nature is an interesting one, but ultimately it would most likely wind up a catastrophe. The matter of trust is one of many factors, but the one that likely pushes out the other contenders for most important: unless it were a single, impeccable person only dealing with all of those vendors (and if that happened, then you’d just have a power vacuum and a very big target), those bugs would just wind up passing through many peoples’ hands (having to deal with the bugs) and that would be a recipe for disaster.
The same ‘other parties’ would continue to exist and the temptations would be rife (as I’m sure would be the infiltrators). There’d be a large window of opportunity for that ‘leaking’ (i.e. selling) to occur with nothing seeming at all suspicious, too, given the fact that ‘properly’ notifying a vendor and taking things to a patch takes a long time. Money (and politics and… so on) is a corrupter. Everything leaks. It’s unfortunate, but it is true. And once that happened once, the entire project would be shot — who’d be willing to trust it?
But then this conversation devolves into human nature (something we CIS people 😉 may perhaps be more accustomed to delving into the depths of but which, nevertheless, applies to our entire species), and I’m not sure this is the proper forum for such a discussion (though I would not be opposed to having it).
> The best way to avoid ransomware and other nasties is to keep your system up-to-date with the latest security patches, and to remove software you don’t need or use
Or in the case of a Windows OS, operate it in user mode without the authority to download/install software or scripts.
Honorable mention on the Register for Brian’s article – KUDOs!
http://www.theregister.co.uk/2013/01/10/cool_exploit_kit/