Oracle today pushed out the third update in less than a month to fix critical vulnerabilities in its Java software. This patch plugs a dangerous security hole in Java that attackers have been exploiting to break into systems.
 Java 7 Update 17 and Java 6 Update 43 address a critical vulnerability (CVE-2013-1493) in Java that security experts warned last week was being used in targeted attacks against high-profile targets. Oracle had intended to quit shipping updates for Java 6 at the end of February, but apparently reversed course for the time being to help Java 6 users address this latest crisis.
Java 7 Update 17 and Java 6 Update 43 address a critical vulnerability (CVE-2013-1493) in Java that security experts warned last week was being used in targeted attacks against high-profile targets. Oracle had intended to quit shipping updates for Java 6 at the end of February, but apparently reversed course for the time being to help Java 6 users address this latest crisis.
I thought this was unusually speedy patch response for Oracle, that is until I read an Oracle blog post that accompanied the patch release. Oracle said that while reports of active exploitation against the vulnerability were recently received, this bug was originally reported to Oracle on Feb. 1, 2013, “unfortunately too late to be included in the Critical Patch Update that it released on Feb. 19.
“The company intended to include a fix for CVE-2013-1493 in the April 16, 2013 Critical Patch Update for Java SE (note that Oracle recently announced its intent to have an additional Java SE security release on this date in addition to those previously scheduled in June and October of 2013),” wrote Oracle’s Eric Maurice. “However, in light of the reports of active exploitation of CVE-2013-1493, and in order to help maintain the security posture of all Java SE users, Oracle decided to release a fix for this vulnerability and another closely related bug as soon as possible through this Security Alert.”
What makes Java vulnerabilities so dangerous is that Java is a cross-platform product, meaning exploits against vulnerabilities in Java can be used to deliver malicious payloads to Mac and Linux systems just the same as they can Windows PCs. The previous Java update released on Feb. 19 came amid revelations by Apple, Facebook and Twitter that employees at these organizations and dozens of others were hacked using exploits that attacked Java vulnerabilities on Mac and Windows machines.
 I’ve said it before, but it bears repeating: Java is a corporate product that somehow landed on something like 80 percent of consumer systems. Most end users who have Java on their systems probably don’t need it and can safely remove it (this advice does not scale for users of corporate systems, which may have specific applications that rely on Java). This is a buggy program that seems to produce a reliable stream of zero-day exploit opportunities for malware writers. So, if you don’t need it, junk it.
I’ve said it before, but it bears repeating: Java is a corporate product that somehow landed on something like 80 percent of consumer systems. Most end users who have Java on their systems probably don’t need it and can safely remove it (this advice does not scale for users of corporate systems, which may have specific applications that rely on Java). This is a buggy program that seems to produce a reliable stream of zero-day exploit opportunities for malware writers. So, if you don’t need it, junk it.
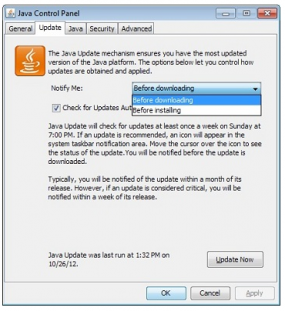
If you do need it, unplug it from the browser unless and until you need it. It is now possible to disable Java content in web browsers through the Java control panel applet. Alternatively, consider a dual-browser approach, unplugging Java from the browser you use for everyday surfing, and leaving it plugged in to a second browser that you only use for sites that require Java.
Updates should be available via the Java Control Panel (see screenshot above) or from Java.com. Mac OS X 10.6 users who have Java should check Software Update for any available updates. Mac OS X 10.7 (Lion) and 10.8 (Mountain Lion) users can grab the updated version of Java from Java.com.




Or setting it to click to play in your browser.
I blinked and missed Update 16. Wow.
Yea, they stuck strictly to the even number = feature updates and odd number = security updates convention and skipped update 16.
Why the heck doesn’t Java have an “automatically install updates” option in its control panel? That one option would do more for Java security than anything else, as most end-users let that system tray notification for a Java update sit there for ages.
I does. It’s just that by the time it gets around to updating, it’s time to update again.
There’s an option to auto-check and auto-download but I don’t think there is one to auto-install. That’s the most important one, as lass savvy end-users will simply ignore that notification until the cows come home.
If there is an option to automatically install Java after it detects an update, I don’t see it.
In my experience it has less to do with ignoring the update notification than being concerned the pop-up they just received is from a virus, and that it’ll install if they click on the message (ignoring the fact that if a pop up came up at all it means their system is already infected).
On the Java Control Panel’s Update tab, when you click the Advanced… button, which brings up the Automatic Update Advanced Settings, you can see why the updates are so tardy – The Default Frequency to check is **Monthly**!
You can change the Frequency to Weekly or Daily, and the panel will retain this setting…..
Until Java is updated, and the Frequency setting is silently reset back to check **Monthly** again. Arrgh!
I can see retaining previous saved update settings as a potentially valid choice, or even Adobe’s pre-selection of update choices upon every Flash update, but silently opening your potential vulnerability window as wide as possible – I just don’t understand Oracle’s implementation choice here..
Just a clarification, Java autoupdates, but it needs user intervention to install the update. What Gantry wants is a mechanism that is truly hands free, in the background aka Chrome, Flash, etc etc.
The problem with Java is a lot of consumers don’t even know what Java is as you stated. Thus even when they are notified that there is a Java update, many just ignore it b/c it is an hassle, requiring several clicks, and the whole shady business with the bundled ask toolbar.
Correct. There is *no* auto-update feature. My understanding of the decision behind this is Sun/Oracle were afraid of breaking enterprise apps if they pushed out updates automatically.
Frankly, though, at this point with the state of java what it is I think this is unforgivable. They need to include autoupdate now. Adobe learned this lesson and now offers autoupdate for flash and reader.
Java updates are manual on Windows, OS X Lion and OS X Mountain Lion.
Only Snow Leopard users get auto-updating as responsibility for Java is taken by Apple which ships Java 6 updates using the same software update mechanism it uses for updating the OS. But just because Oracle updates their versions of Java does not mean that Apple will also update theirs. Sometimes Apple is in step, sometimes not.
That Java requires manual updating is, no doubt, a big reason bad guys live to exploit it – so many people have old versions installed.
Since Brian’s article mentioned Linux, most GNU/Linux desktop distros get Java updates automatically via the package manager as long as one is running open-source Java, OpenJDK and Iced Tea. Whereas Oracle’s proprietary Java SE must be manually updated via download and install for most GNU/Linux distros. Exceptions include the commercial GNU/Linux distros (e.g., Oracle Enterprise Linux, Red Hat Enterprise Linux), where the package manager takes care of Java SE updates.
P.S. I’ve noticed some cases where the OpenJDK developers have made security improvements to the source code relative to Oracle’s proprietary Java SE.
It’s manual on OS X Lion and Mountain Lion because Apple treats it like any other application that a user installs on their own. That’s because Apple stopped including Java among its installed software starting with Lion. The same thing for Windows.
That’s why only Snow Leopard (and earlier OS Xes) receives auto updating of Java. Most of the people I know, who bought a Mac after the arrival of Lion, did not install Java. So applying Brian’s advice: If you don’t need it, don’t install it.
I don’t believe manual updating has anything to do with it: Java is simply a target. Users, who installed Java, simply have to stay on top of the updates. Thankfully, that task is made all the more easier by reading KrebsOnSecurity.
FYI. Coincident with Oracle’s security updates to Java SE 6 and 7 today, Security Explorations has provided Oracle with five additional Proof-of-Concept issues for Java SE 7 (numbered 56 through 60):
http://www.security-explorations.com/en/SE-2012-01-status.html
http://www.security-explorations.com/en/SE-2012-01-poc.html
Thanks for the heads-up, Brian! 🙂
“What makes Java vulnerabilities so dangerous is that Java is a cross-platform product, meaning exploits against vulnerabilities in Java can be used to deliver malicious payloads to Mac and Linux systems just the same as they can Windows PCs. ”
And furthermore, Java exploits may sidestep the browser’s arsenal of mitigations, too. Dino Dai Zovi’s “Attacker Math” presentation reckons (on page 10) that Java is “the easy path,” as Yoda would put it:
http://www.trailofbits.com/resources/attacker_math_101_slides.pdf
He says the attacker will choose the least “costly” avenue of attack, and that is Java in the browser. It looks like time has proven his point.
“Java is a corporate product that somehow landed on something like 80 percent of consumer systems. Most end users who have Java on their systems probably don’t need it and can safely remove it”
I wouldn’t be safe, my boy would tear me apart if he couldn’t play Minecraft!
You don’t need Java enabled in your browser to play Minecraft which has its own client.
https://minecraft.net/download
Leaving this here for anyone that could use it:
Download page (i still uninstall the old version of Java) :
http://www.oracle.com/technetwork/java/javase/downloads/jre7-downloads-1880261.html
And for Firefox users, Firefox recently started blocking old outdated plugins from loading. You can however change a setting that forces all plugins to be “click to play”:
https://blog.mozilla.org/security/2012/10/11/click-to-play-plugins-blocklist-style/
One of my fellow employees has to use Java 6 to work with the FDA. And use Firefox 2.0 in order to use an xpi written by them. She also has to have the latest Java for a program that creates submissions for the FDA (which is uploaded in a browser that requires Java 6.)
I really didn’t like setting Java to not update for obvious reasons. My solution was to install VirtualBox to run a Windows XP VM that has Java 6, Firefox 2 and IE8. She only uses the VM for the two FDA websites and shuts it off when not in use. Her actual machine (the VBox server) is a Windows 7 machine that is set to update Java.
I found the release of a new Java 6 JRE a great surprise. Oracle had said that Java 6 was going out of support at the end of February. Perhaps they are changing their mind due to the events of the last few months?
I develop Java servlets that run on Tomcat. Do these past few security updates affect my servlets, affect the jvm, or both? ( or neither if it is a browser only issue? )
Confused in flyover land.
If you are asking about the recent Java security vulnerabilities CVE-2013-0422, CVE-2013-0809, and CVE-2013-1493, these all affect client-side Java deployed within a browser (e.g. Java applets and Java Web Start applications). They do *not* affect server-side Java (e.g. servlets running in a web server like Tomcat). The vast majority of Java security exploits seem to occur on the client-side of Java.
Thanks for your well-targeted answer. That was exactly what I was asking for.
Regards,
Bill
Yeah.
Java programmers: it’s time to begin shifting to another language. Your ecosystem has peaked, and is now on a permanently downward trajectory. Jump ship while there’s still time.
I don´t have the update part in the control panel of Java just general , java, security and advanced
When I clicked the prompt to install update 7-17, another prompt appeared that my system already had the latest version. . . Odd, since in Programs the latest update was 15. I couldn’t easily find another way of downloading from Oracle, my preference, so did it here. Thanks for being on top of this!
“Emergency Java Update!!!” – Please uninstall Java a soon as humanly possible.
In other words stop using Java by way of disabling or uninstalling the plugin until Oracle can get their #### together Oracle is now on ‘internet def con 3’, after this update.
J.S. gone Phishing !
Oddly enough File Hippo had the 64 bit update, but wouldn’t point to the other update. So once again, I had to use the Avast software updater to find the available file. Installation went without incident.
Navigating the Oracle site has never been my forte.
So how do companies handle Java in the corporate environment? Patching a large estate is time-consuming, requiring pre-rollout testing etc and with the regularity of updates being released, this is a costly exercise (and in fact a new version is usually released prior to completion of the previous rollout!). There’s also the need to maintain functionality with legacy apps that may require older versions of Java, which Brian mentions above.
Why doesn’t Java have functionality, whereby you can opt specific websites ‘in’ to run Java code from?
I second that great question.
My company is looking at purchasing a web-based MIS and E-Commerce system. It’s very powerful, but it uses Java in the browser.
I don’t know how to handle this – the Front End and Back End connections are SSL.
I informed the system vendor of our concerns, but have not yet received an answer.
We don’t know what our customers policies are or will be concerning disabling Java in the browser.
chris, if you’re stuck with Java in the browser, one way to reduce exposure (on Windows systems with Internet Explorer) would be to use Group Policy to disable Java entirely in all zones except Trusted Sites Zone and Locked-Down Trusted Sites Zone, then add the necessary site(s) to Trusted Sites Zone so they are the only ones where Java will work.
The relevant Group Policy setting is the “Java permissions” setting. Set that to “Disable Java” in all zones except Trusted Sites and Locked-Down Trusted Sites, then test to make sure it’s being enforced by trying a Java site like http://www.time.gov.
MrGreedy wrote:
“There’s also the need to maintain functionality with legacy apps that may require older versions of Java, which Brian mentions above.
The only product I’m aware of that takes on the multiple Java version problem in the the enterprise is Browsium’s Ion. More here:
http://www.browsium.com/faqs/running-multiple-versions-java-sidebyside-in/
Note the PDF download entitled “Managing Java Versions with Browsium Ion”. Perhaps it will help with your situation, perhaps not.
Oops, muffed up the link. Try this:
http://www.browsium.com/faqs/running-multiple-versions-java-sidebyside-ion/
I had completely forgot about Browsium! Good on RHM!
@mechBgon: the group policy you’re referring to has limitations – it blocks only the use of the APPLET tag; there are other more generic ways to invoke Java (e..g, OBJECT tag) that the policy doesn’t impact. (More info here: http://blogs.technet.com/b/fdcc/archive/2008/01/31/internet-explorer-security-setting-java-permissions-disable-java.aspx )
One problem that is difficult to overcome is that many Java developers design and test their apps against a specific version/build of Java, and then put a check in their code that INSISTS on that specific version, which locks their users into those older versions, even after vulnerabilities are discovered. (I wrote about that and related issues here: http://blogs.technet.com/b/fdcc/archive/2011/10/18/alert-java-s-forward-compatibility-promise-has-been-revised.aspx ).
I appreciate the Krebs blog and all the helpful and informative comments.
We have customers ordering print products in custom portals on our website.
If we move to a new ecommerce provider that uses Java in the browser, I could see those customers with Java disabled either not ordering from us because of their security policies, or we would be forced to school our customers to allow Java specifically for our website.
However, that doesn’t do anything for prospective customers checking us out for the first time.
Because knowledge of Java exploitation is ubiquitous, the fact that a website needs to be hacked and infected for Java to be a threat, is a moot point.