The creator of a popular crimeware package known as the Phoenix Exploit Kit was arrested in his native Russia for distributing malicious software and for illegally possessing multiple firearms, according to underground forum posts from the malware author himself.
The Phoenix Exploit Kit is a commercial crimeware tool that until fairly recently was sold by its maker in the underground for a base price of $2,200. It is designed to booby-trap hacked and malicious Web sites so that they foist drive-by downloads on visitors.
Like other exploit packs, Phoenix probes the visitor’s browser for the presence of outdated and insecure versions of browser plugins like Java, and Adobe Flash and Reader. If the visitor is unlucky enough to have fallen behind in applying updates, the exploit kit will silently install malware of the attacker’s choosing on the victim’s PC (Phoenix targets only Microsoft Windows computers).
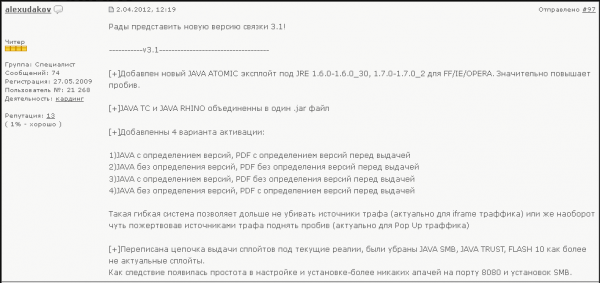
The author of Phoenix — a hacker who uses the nickname AlexUdakov on several forums — does not appear to have been overly concerned about covering his tracks or hiding his identity. And as we’ll see in a moment, his online persona has been all-too-willing to discuss his current legal situation with former clients and fellow underground denizens.
For example, AlexUdakov was a member of Darkode.com, a fairly exclusive English-language cybercrime forum that I profiled last week. That post revealed that the administrator accounts for Darkode had been compromised in a recent break-in, and that the intruders were able to gain access to private communications of the administrators. That access included authority to view full profiles of Darkode members, as well as the private email addresses of Darkode members.
AlexUdakov registered at Darkode using the address “nrew89@gmail.com”. That email is tied to a profile at Vkontakte.ru (a Russian version of Facebook) for one Andrey Alexandrov, a 23-year-old male (born May 20, 1989) from Yoshkar-Ola, a historic city of about a quarter-million residents situated on the banks of the Malaya Kokshaga river in Russia, about 450 miles east of Moscow.
That nrew89@gmail.com address also is connected to accounts at several Russian-language forums and Web sites dedicated to discussing guns, including talk.guns.ru and popgun.ru. This is interesting because, as I was searching AlexUdakov’s Phoenix Exploit kit sales postings on various cybercrime forums, I came across him discussing guns on one of his sales threads at exploit.in, a semi-exclusive underground forum. There, a user with the nickname AlexUdakov had been selling Phoenix Exploit Kit for many months, until around July 2012, when customers on exploit.in began complaining that he was no longer responding to sales and support requests. Meanwhile, AlexUdakov account remained silent for many months.
Then, in February 2013, AlexUdakov began posting again, explaining his absence by detailing his arrest by the Federal Security Service (FSB), the Russian equivalent of the FBI. The Phoenix Exploit Kit author explained that he was arrested by FSB officers for distributing malware and the illegal possession of firearms, including two AKS-74U assault rifles, a Glock, a TT (Russian-made pistol), and a PM (also known as a Makarov).
In his exploit.in post, AlexUdakov says he lives in a flat with his wife and child. The main portion of the post reads, in part:
“On _th of May FSB operative performed a controlled purchase, the money was transferred through WebMoney.
1_ th of July FSB operatives arrested me and conducted searches at the residence, registered address, in the cars that I was using. All computers and storage devices were taken except for… a Wi-Fi router.
During the search at the place of residence thy have also taken 2 automatic machine guns AKS74U, Glock, TT handgun, PM Handgun, ammo. I have no criminal record and gave a confession, was released on my own recognizance. I am indicted on 3 charges – conspiracy to distribute malicious software (article 273 of Russian Penal Code), unlawful production of firearms, ammo an explosives (article 223), unlawful possession of weapons, ammo and explosives (article 222)…..
…Then there were few months of waiting, and the computer forensic examination took place which attempted to declare the exploit pack to be malware. The examination took place in _Labs, the same place that gave preliminary opinion, which in turn became the basis for opening a criminal case. The examination determined the software (exploit pack) to be malware.”
After stumbling on AlexUdakov’s exploit.in thread, I scoured the various hacked forum and affiliate databases I’ve collected over the years. Turns out that a miscreant who adopted the nickname AlexUdakov also was an affiliate of Baka Software, a moneymaking pay-per-install scheme that pushed fake antivirus or “scareware” programs between 2008 and 2009. AlexUdakov registered with Baka using the email address andrey89@nextmail.ru. That email was connected to yet another Vkontakte profile (now banned by Vkontakte for abuse violations), also from Yoshkar-Ola.
At this point in the investigation, I called upon a trusted source of mine who has the ability to look up tax records on Russian citizens and businesses, and asked this source if there was a 23-year-old male in Yoshkar-Ola who fit the name in the Vkontakte profile registered to nrew89@gmail.com.
The source came back with just one hit: one Andrey Anatolevich Alexandrov, born May 20, 1989, and currently living in a 365-square foot apartment with his wife and small child in Yoshkar-Ola. According to my source, Alexandrov is currently the registered driver of two automobiles, a Lexus RS350 and a 1995 VAZ-2109, a Russian-made hatchback.
I can’t say for certain whether the Phoenix Exploit Kit has anything to do with Mr. Alexandrov from Yoshkar-Ola, or indeed whether this young man ever received a visit from the FSB. Requests for comment sent to both emails mentioned in this story went unanswered. And it is certainly possible that the AlexUdakov persona who sold his crimeware package on so many underground forums simply assumed the real-life identity of an innocent man.
But based on previous investigations such as this one, it would not be a stretch to conclude that the two identities are one and the same. Readers of this blog sometimes have trouble believing that people involved in selling and distributing malware and crimeware would be so careless about separating their online selves from their real lives. The reality is that many top players in this space consistently show that, although they may posses fairly advanced offensive hacking skills, they are not so expert at defense.
This general lack of operational security could be the result of several factors. First, many involved in cybercrime may believe (perhaps rightly so) that it is unlikely that authorities in their countries will ever take an interest in their activities. Also, some fraudsters even like to boast about their crimes, and probably some cybercrooks simply don’t view what they do as serious criminal activity, and thus see little reason to hide.
But far more common is the bright kid who is gradually pulled into the darker side of the Underweb, and who almost invariably leaves behind a cumulative trail of clues that point to his real-life identity — all because he never expected to achieve success or make serious money from his illicit activities.
I’d like to add a special note of thanks to “Filosov” and Aleksey for their help with the Russian-to-English translations in this post.







too bad for him,but lets say i dont wright code i just use crime toolkit and is teal some 5miljon then i will get at least 2.miljon of this ammount and maybe maximum is 5 years sentence…but usually its only 2-3 years its not big deal after ill be out from prison i will have 2miljon
example uk zeus gang( jevehen kulibaba and others)
and to be honest this is eastern european business
Brian, thank you for yet another fascinating post.
Thank you for your post..and it is useful for me..
I enjoyed the article, but was surprised that you included a picture of the man you named in the article, since you admitted it’s possible he might simply be an innocent person who’s identity was stolen.
I agree. I too have often found this practice to be distasteful.
I’m still not sure I understand why developing or selling something like Phoenix Exploits Pack is any different or more worthy of penalising than things like Metasploit, or exploit-db.com or these sorts of sites. Why hold him responsible for what other people do with code he sells? That is like holding a gasoline producer and seller responsible for arsonist burning down a house.
“That is like holding a gasoline producer and seller responsible for arsonist burning down a house.”
Gasoline has a valid use, i.e. powering cars and trucks. Phoenix Exploits Pack has no valid use; it is only used for crime.
We punish fences (people who buy and sell stolen goods) for being involved in theft. All of these exploits are the moral equivalent.
Yes, but while you have pointed out my imperfect analogy you have not told me how Phoenix is better or worse than Metasploit and such. I think some real-world “penetration testers” even use things like Phoenix and Blackhole to test client networks. Code is not good or bad in and of itself. You have to use it for something good or bad.
Very interesting point, voksalna
When I studied for my C|EH the company that charged 4 figures for the training courses also provided, with that price, DVDs full of malware and “penetration testing” software. FWIW, a lot of it is developed by people and for who are clearly not white-hats (not by the training company).
A for-profit company that provides training videos is apparently allowed to sell (which includes distributing) malware without recourse, while an individual who develops, sells and distributes similar or the same software is a criminal – or in some areas seen as the dreaded T-word.
So where is the distinction? There’s an obvious separation of interest/intent, but both are doing it for profit. A well-meaning person who commits crimes though is still conventionally criminal. It’s not like there is a vetting process for upstanding morality from either parties of sellers.
Thank you, Andrew. I’ve often thought about these ‘toolkit CDs’ also. Perhaps it is informative for some people on here who do not know, but many people who are ‘new’ who want to learn “these sorts of things” often start with the very same training materials (though typically downloaded from other places). In fact many or most of the tools are used by both sides. Do we arrest sqlmap developers or Backtrack committers? I can guarantee you both tools are being used by the ‘bad guys’ by most readers’ definitions, no matter whose side you are on.
Suppose you could see the communications between AlexUdakov and his buyers, many of whom are well known to be running large botnets, and you could see he was helping them to set up the kit so that it works just so with their cybercrime operations. Does that mean he’s just a consultant who’s offering a service just like any other? At what point does offering tools morph into aiding and abetting?
By the way, this is exactly what most exploit kit authors do: They will sell you a copy of their kit so that it is tied to a specific domain; it’s called “domain locking”, and it’s a security feature designed to protect the exploit kit maker from having his kit shared amongst miscreants who didn’t pay for a license. So in a very real sense, the business model of most of these exploit kits is predicated on the idea that the author must know a fair amount about the operations of each of his clients, and can easily see how many of them are being used for “pen testing” and how many are being used to create botnets.
I don’t completely accept this explanation, in part because often the coder of the software is not the person who ‘locks’ the site nor do I believe most people want to know the business details and dealings. Knowing a site does not equal knowing intent. I am particularly bringing this up because it does not appear that he is being charged for criminal conspiracy with anybody else as far as hijacking traffic and exploiting people directly — from what I can make out from his postings it appears to be more related to the code itself.
I also see a parallel to the RAT situations of some months back, among other cases.
By the way I am sure you know that many of the people who ask for support for things with metasploit are ‘criminals’ by your own definition. Just like many people who visit Xylitol’s site and compliment him are using things for ‘no good’. Metasploit does not seem to make a distinction in whom it supports. In fact most of the commercial exploitation vendors do not, either, provided you pay their fees.
Ironically, by the way, in most cases these exploit packs are ripping their exploits almost directly from metasploit or similar tools itself (with exception of Blackhole who has created novel Java exploits which then were modeled *by* metasploit).
Obscurity is not security, but it limits damages.
I appreciate your contrary opinion here, Voksalna, as usual. But I think you may be giving the exploit pack makers a bit too much credit. They are, in fact, the ones locking the domains to their customers; if the customer gets a domain shut down because of abuse or whatever, he has to contact the exploit kit author and get the author to unlock the old domain and lock it to another. And in many cases (as in this one) the exploit kit makers are helping their clients set up malware distribution networks so that everything works properly with the exploit kit. In some cases (Blackhole, e.g.) the exploit kit makers also sell ancillary services, such as malware cryptors and bulletproof hosting.
Of course there are legitimate uses for all security tools. That is axiomatic. All security tools can be used for good or bad. That’s not the question here. The question you seem to be asking is, is the exploit pack maker just a software writer, or is he more deeply involved in the criminal operations that result from the uses of his software? Based on the way I see this industry operating, the answer is that in most cases (this case is no exception) the exploit kit maker does in fact know what some of his customers are using the software for, because he is helping them to use it that way. There’s very little ambiguity there, IMHO.
Interestingly, at least in the United States, much of the law here is not clear; writing malicious software is not per se a crime; it’s a form of free speech. Spreading malware, on the other hand, is illegal. Knowingly and actively helping other people to spread malware is almost certainly also illegal. Many people are surprised to know that it is not illegal to sell someone’s Social Security number (SSN); but prosecutors can and do make cases against people who do this with full knowledge that the people buying it intend to use it for illegal means, such as obtaining credit in someone’s name or assuming their identity. Intent is key in this cases, and my guess is prosecutors (here or abroad) would have little trouble establishing cases against almost any exploit pack maker out there showing that the software provider’s actions showed he intended to help cybercrooks further their businesses. It doesn’t get him off the hook if some of his customers happen to be legitimate security researchers who merely want to better understand the software.
Brian, thank you for your long and detailed reply. I will leave full response tomorrow, too tired to summon the English right now. I did want to quickly point out in case of further posts before then that a lot of these pack makers do not do their own support, and even at times do referrals through third parties. I would not mind your opinion as to whether this would make the software author(s) less culpable, in your eyes and/or eyes of the law in whatever jurisdiction(s)?
But that is not what he is charged for.
I work for a pentesting company and there is NO FUCKING WAY we are ever going to buy blackhole or phoenix or anything like that. They might be legitimately better exploit kits than SET or anything in metasploit, but the fact is we will never be able to trust the authors. Also their price range is so high we can never justify spending that much. It’s only worth it if you can profit from mass infections. There is no question at all that it’s 100% evil software, and there is no way ever that it will be purchased and used in legitimate pentesting.
Maybe companies who have employees who do not scream invectives at random strangers on the internet might? 🙂
Hahaha this made my day
Take another analogy, tanks. To slightly paraphrase what you said, steel is not good or bad in and of itself. You have to use it for something good or bad. So someone who has a pile of steel is not doing anything wrong, because that steel can be used to manufacture refrigerators or autos. But if another person buys a hunk of steel and fashions it into a tank, we intervene because tanks are dangerous. Tanks are highly regulated in civilized societies for good reasons.
The same is true with code. Code can be used to build good things or bad things. But don’t be coy and suggest that someone selling a tank in the Russian underground isn’t doing something wrong. If he contacted security companies or potential victims and offered to sell either his product or his expertise, then his behavior would be acceptable.
But I will wager that you and I have a entirely different way of looking at the world. You, like most young people, probably believe that because something is digital, it should be regulated differently. I do not believe that.
For example, eBay has Chinese sellers offering counterfeit wares on the site. I see no difference between eBay and a fence. eBay has a duty, to speak in legal parlance, to ensure that counterfeit goods are not sold on its site.
Another example is Napster. Their original business model was based on theft. Many young people seem to think that because music is now easily transferable, there is nothing wrong with taking a copy for personal use without paying for it. I see little difference between that and taking money out of the hand of a woman who is 150 years old and barely able to move, let alone defend herself.
P.S. I think all exploits should be regulated.
It sort of irritates me a little bit when people claim that copyright infringement is theft. This is perpetuated so as to equate the act with something (theft) that a majority of people find objectionable. I can only conclude this is because people do not find the act of copyright infringement as objectionable.
It isn’t theft. Making a copy doesn’t deprive anyone of any property. In many jurisdictions non-commercial copyright infringement doesn’t even leave one liable to criminal prosecution although one can be sued in a civil case. Where prosecution does occur it’s not under legislation that infers or implies theft.
In modern day, John Cusack character in Say Anything would have been guy going to jail for mix tape, not hot girl’s father for embezzlement. Hot girl’s father would have been given buyouts, severance pay, and perhaps political junket to Thailand.
I may be older and wiser than you, gravy. Do not count me out because we do not agree. If y ou even read my argument, and interpret it sanely, you may even see my issue is with hypocrisy.
PS: What right do you have to say if I can make a tank or not with my steel? In fact is a tank even harmful unless it is armed and then USED? Some things may be dangerous in and of themselves — refined nuclear material, for instance. But that analogy does not compute for code, except on the very rare edge case of a massive worm. If something does not self-spread (and not that many things do these days, outside from maybe the immediate local network and via USB (rarer too now because of changes in Windows handling of insertion) then your entire argument falls apart.
One has to remember that each country has its own laws and ways they will deal with this. I think it was a multi-country concern, and the countries involved seen it as a threat that if released had the “potential” to create great harm.
The reason more people are not busted almost immediately is that the Feds are typically busy looking into something else. Its only when something that is brought to their attention that is considered a pressing matter.
Another issue it could be is that the Feds, not only seeing it as a threat, want or wanted to get their hands on the code. If it is relatively new, then they can analyze it and potentially see the direction the bad code is going.
If there is ample evidence, then the person is guilty. If there is a lack of evidence, but the Feds have analyzed the data and over time ( some times many years) they may return the property.
I am sure they will look over all data for additional people to watch and track. Big brother watches, and eventually you will see a slew of arrests.
Many people who don’t even consider crime as an occupation are somewhat normal. They lead a normal life, leave some trail of information on the internet. It can be tracked back, and as the puzzle pieces fall into place the picture becomes clearer.
If you show intent – you are skirting the edge of breaking the law in “most” countries. in order for countries to gain ground on the criminal world, they are being proactive, vice reactive.
Its about time the law has woken up. People who stand up and say, I am planning on doing this illegal act – what are you going to do about it? Are being called on, and arrested.
Call it unfair, unjust or otherwise. the Feds probably call it illegal and in bated breath, call it Intelligence gathering.
His operational security might not have been clueful enough to protect his sorry butt from the FSB .. but I bet that it was good enough to make sure someone else continues the development and peddling of Phoenix :(.
Is Adidas the official apparel provider of cyber fraudsters? They all look they they are from south Boston.
No, it’s actually russian national dress.
nice
Very interesting post, I’d have thought cyber criminals take better precautions to protect their identity.
Brian,
more info. Alexudakov’s account on verified.ms
http://pastebin.cc/paste/b855df25a56db95c0ba34e0eab27c80642f2ba05#saVndoj10ycto9t1hwUjXwk1TWZqho4tmT4QFqngYBI=
Yet another great and interesting post. Once again it shows that when a person openly brags about their criminal activity , eventually they will get caught.
I was reading a article about street gangs in New York City who where openly talking about their crimes on both Facebook and Twitter. They had absolutely no idea that law enforcement where monitoring their posts on a daily basis Goes to show that criminal are in fact stupid when it comes to defending what they do
Hey Brian, I just want to ask you something: is the second post that I see you posting personal pictures from people that you don’t even know if they are the ones you are talking in your post. This guy, before doing a exploit kit, is a father of his family, and you start with your Sherlock Holmes play, putting information about his family, his house, his cars… What is that? You think you are god to judge and make public other persons life because in some way they did something wrong in your point of vision? Sorry man, but I can’t agree with you… That’s why you are getting your house intruded by SWAT, because you playing too low with this guys. Making public their personal informations because they did some mistake in life is not your business. Take care of your family, instead of make a blog to talk about other people’s life and their mistakes… One thing is make analysis of malware, another thing is do what you are doing here.
Would you still think the same if you had been a Victim of his malware?
Criminals should be outed and made public no matter what sort of crime they have committed?
Your words, I stress: CRIMINALS should be outed and made public…
While we may all wish to be Fury in Alice in Wonderland, it is good for nobody to think they deserve to be judge and jury; to be accused of a crime is NOT the same as to be convicted of a crime (yet or otherwise).
Which is not to say I agree with the OP. There is a line where one can and should be unbiased. There are also vast areas to either side of that line; both sides can be ridiculous.
Yes, Haggis, and burnt at the stake! You could have been a keen Inquisitor.
By the way, I agree with Nancy – there is no excuse to put such information public…
Give it to the FBI – they are the new world Inquisitors with the economic legitimacy of the world’s leading power…
Oooops, did I get caught in a vicious circle here?
🙂