A year ago today, Apple released a software update to halt the spread of the Flashback worm, a malware strain that infected more than 650,000 Mac OS X systems using a vulnerability in Apple’s version of Java. This somewhat dismal anniversary is probably as good a time as any to publish some clues I’ve gathered over the past year that point to the real-life identity of the Flashback worm’s creator.
![]() Before I delve into the gritty details, a little background on this insidious contagion is in order. A keenly detailed research paper (PDF) published last year by Finnish security firm F-Secure puts the impact and threat from Flashback in perspective, noting that the malware boasted a series of “firsts” for its kind. For starters, Flashback was the first OS X malware to be “VMware aware” — or to know when it was being run in a virtual environment (a trick designed to frustrate security researchers). It also was the first to disable XProtect, OS X’s built-in malware protection program. These features, combined with its ability to spread through a then-unpatched vulnerability in Java made Flashback roughly as common for Macs as the Conficker Worm was for Windows PCs.
Before I delve into the gritty details, a little background on this insidious contagion is in order. A keenly detailed research paper (PDF) published last year by Finnish security firm F-Secure puts the impact and threat from Flashback in perspective, noting that the malware boasted a series of “firsts” for its kind. For starters, Flashback was the first OS X malware to be “VMware aware” — or to know when it was being run in a virtual environment (a trick designed to frustrate security researchers). It also was the first to disable XProtect, OS X’s built-in malware protection program. These features, combined with its ability to spread through a then-unpatched vulnerability in Java made Flashback roughly as common for Macs as the Conficker Worm was for Windows PCs.
“This means Flashback is not only the most advanced, but also the most successful OS X malware we’ve ever seen,” wrote F-Secure’s Broderick Ian Aquilino.
The F-Secure writeup answers an important question not found in other analyses: Namely, what was the apparent intended purpose of Flashback? Put simply: to redirect Google results to third-party advertisers, all for the author’s profit. It’s name was derived from the fact that it spread using a social engineering trick of presenting the OS X user with a bogus Flash Player installation prompt. F-Secure notes that this same behavior — both the Flash social engineering trick and the redirection to fake Google sites that served search results for third-party advertisers that benefited the author — was also found in the QHost malware, suggesting that Flashback may have been the next evolution of the Mac QHost malware.
BLACK SEO
A year ago, I published a series that sought to identify the real-life hackers behind the top spam botnets. Using much the same methodology, I was able to identify and locate a young man in Russia who appears (and privately claims) to be the author of Flashback. As it happens, this individual hangs out on many of the same forums as the world’s top spammers (but more on that at another time).
Given Flashback’s focus on gaming Google’s ad networks, I suspected that the worm’s author probably was a key member of forums that focus on so-called “black hat SEO,” (search engine optimization), or learned in illicit ways to game search engines and manipulate ad revenues. Sure enough, this individual happens to be a very active and founding member of BlackSEO.com, a closely guarded Russian language forum dedicated to this topic.
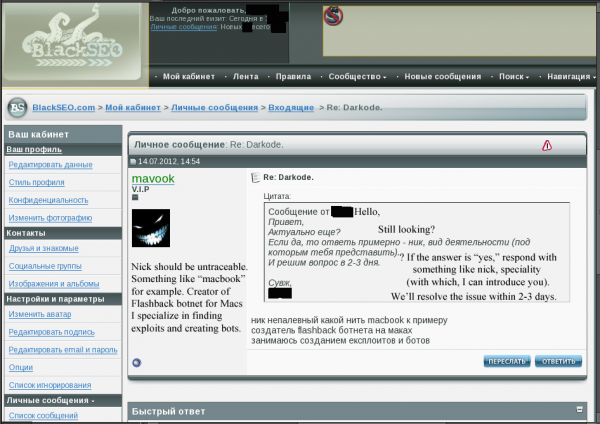
Below is a screen shot taken from a private message between a “VIP” user named “Mavook” and a top forum member on BlackSEO.com. The conversation took place on July 14, 2012. A rough translation of their conversation is superimposed on the redacted screen grab, but basically it shows Mavook asking the senior member for help in gaining access to Darkode.com, a fairly exclusive English-language cybercrime forum (and one that I profiled in a story earlier this week).
Mavook asks the other member to get him an invitation to Darkode, and Mavook is instructed to come up with a brief bio stating his accomplishments, and to select a nickname to use on the forum if he’s invited. Mavook replies that the Darkode nick should be not be easily tied back to his BlackSEO persona, and suggests the nickname “Macbook.” He also states that he is the “Creator of Flashback botnet for Macs,” and that he specializes in “finding exploits and creating bots.”
The senior member that Mavook petitions is quite well known in the Russian cybercrime underground, and these two individuals also are well known to one another. In fact, in a separate exchange on the main BlackSEO forum between the senior member and a BlackSEO user named JPS, the senior member recommends Mavook as a guy who knows his stuff and can be counted on to produce reliable attack tools.
 In the conversation screen-shotted here to the left, JPS can be seen asking the senior forum member for recommendations about reliable individuals who sell unique exploit packs, software toolkits built to be stitched into hacked Web sites and exploit common Web browser vulnerabilities. JPS says he’s looking for a pro who can deliver decent exploitation rates.
In the conversation screen-shotted here to the left, JPS can be seen asking the senior forum member for recommendations about reliable individuals who sell unique exploit packs, software toolkits built to be stitched into hacked Web sites and exploit common Web browser vulnerabilities. JPS says he’s looking for a pro who can deliver decent exploitation rates.
“I have no time (and no desire) to roam chats and argue there with cool hackers,” JPS said. “I need to check traffic in terms of exploitability, and in the future, if everything is alright, I can work on a continuous basis” with the hired expert.
The senior member tells JPS to ask Mavook. “If Mavook won’t budge, saying that he is no longer doing this stuff, write to me again.”
WHO IS MAVOOK?
If we take a closer look at Mavook’s profile page on BlackSEO.com, we can see that he is a longtime member, dating back to 2005, when he was the 24th member registered on BlackSEO (out of thousands). Mavook’s profile also shows that his personal home page was at one time mavook.com. The WHOIS registration records for mavook.com have long been hidden by commercial WHOIS privacy protection services, but I found the original WHOIS record for this domain using the indispensable historic WHOIS service maintained by domaintools.com. Those records show that the domain was originally registered in 2005 by a Maxim Selikhanovich in Saransk, the capital city in Mordovia, a republic in the eastern region of the East European Plain of Russia.
The email address used to register mavook.com was “h0mini@mail.ru” (the second character in the address is a zero). A search for that email address in Skype’s user database brings up a user with the screen name “Maximsd”. Mavook also used the email address “mavook@gmail.com.” That address is tied a Maxim Selikhanovich in Saransk via the registration records for the now defunct Website saransk-offline.com, which at one point sold popular MP3 files for pennies apiece.
One of the emails used by Maxim for that Website and a related site was “troxel@yandex.ru,” which was the same email used to register a now-deleted Facebook account under a Maxim Selikhanovich from Saransk. Yet another abandoned music sales site — mavook-mp3.com — was registered to a “Mavook aka Troxel” and to the h0mini@mail.ru” address used for mavook.com.
MACS, MAX and MAKS
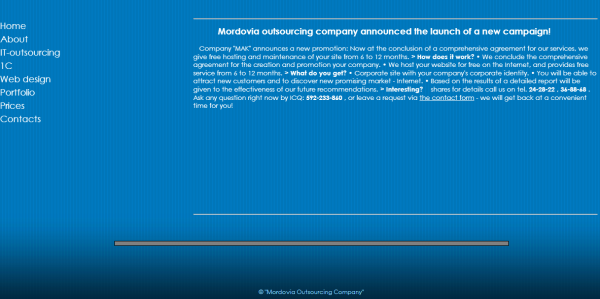
The final clue offers perhaps the most tantalizing details: The h0mini@mail.ru address is the contact point of record for a business in Saransk called mak-rm.com, the domain name registered to a IT-outsourcing and Web design firm in Saransk called the Mordovia Outsourcing Company (the “mak” part of the name comes from the Russian version of the company name, which is “МОРДОВСКАЯ АУТСОРСИНГОВАЯ КОМПАНИЯ”). That domain is registered to a “Max D. Sell” in Saransk (see a cached image from mak-rm.com’s homepage in 2010 at the Internet Archive).
According to a trusted source who has the ability to look up tax information on citizens and corporations in Russia, the Mordovia Outsourcing Company was registered and founded by one Maxim Dmitrievich Selihanovich, a 30-year-old from Saransk, Mordovia.




I keep reading these blog posts and while I find them quite fascinating, there is one thing I don’t understand:
I would imagine you would have to be quite intelligent in order to do what many of these criminals are doing, e.g. creating something like the Flashback worm and to making its “business model” work.
Yet time after time, these people make what I consider to be stupid mistakes that allow their virtual identities to be linked to their real id. Like, in this case, using personal data to register a domain name for the nick name you’re using while doing shady things, or using the same email address for legal and illegal things, and so on.
Why is that? Any theories?
I think it is due to the fact that when they started doing this stuff, they were completely confident no one in their own countries would care if they committed computer crimes against Westerners, as long as they did not attack computers and bank accounts of their own countries’ citizens — and as long as they shared some of the money with the local politicians/law enforcement officers.
Affiliate programs like Spamit were basically pyramid schemes that were doomed to eventually collapse. Stupin and Gusev got in trouble when they could no longer pay their affiliates and bribe officials, not because of a sudden surge in interest in ethical behavior by Russian law enforcement.
fully true 🙂
спомони отписался – блог можно закрывать
Афтар мудаг и пидарг
Things must be pretty slow in Saransk, the capital city in Mordovia,,,
DennisPerm: spomoni unsubscribed – a blog can be closed
Are these translations helping anyone or should i just stop? lol
spomoni (a well-known person on RU SEO forums and blogs) left a comment – the blog can be closed (mission accomplished)
Spomoni – ukranian Chuk Norris
Да я вам пиздов дам! Шакалье!
At least in Russia he is free to do this. If he was in the US, UK or Australia, where the governments fear and hate their own people, he would be on his way to prison. People say Russia and China are so bad, but to me it looks like they respect their citizens more. At least they have the common sense not to imprison people for attacking the enemy.
Всем привет, я собака Spomoni. Не собака-spomoni, а собака Spomoni. К делу. Spomoni хороший человек. Я закончила
I read your article with great interest.
I have just been asked to speak at a local city event on cyber security. As a security professional I realize this is a vast domain and my experience (CISSP) is more focused on business and systems security. I was hoping you could point me to some pertinent material for the public sector, which perphas included US government pending mandates for US cities. Of course, I would be pleased to attribute your information to you / your column during the presentation.
Looking forward to your reply.
Mark
I’ve heard spomoni treats his dog badly.. He even forces it to write eulogistic comments everywhere!
Who’s next? Guess it will be spomoni’s ravioli, stop him before he hasn’t proceeded!
Make spam not war 🙂
Воняет Кребс и немного палево