Credit and debit card accounts stolen in a recent data breach at retail giant Target have been flooding underground black markets in recent weeks, selling in batches of one million cards and going for anywhere from $20 to more than $100 per card, KrebsOnSecurity has learned.
Prior to breaking the story of the Target breach on Wednesday, Dec. 18, I spoke with a fraud analyst at a major bank who said his team had independently confirmed that Target had been breached after buying a huge chunk of the bank’s card accounts from a well-known “card shop” — an online store advertised in cybercrime forums as a place where thieves can reliably buy stolen credit and debit cards.
There are literally hundreds of these shady stores selling stolen credit and debit cards from virtually every bank and country. But this store has earned a special reputation for selling quality “dumps,” data stolen from the magnetic stripe on the backs of credit and debit cards. Armed with that information, thieves can effectively clone the cards and use them in stores. If the dumps are from debit cards and the thieves also have access to the PINs for those cards, they can use the cloned cards at ATMs to pull cash out of the victim’s bank account.
At least two sources at major banks said they’d heard from the credit card companies: More than a million of their cards were thought to have been compromised in the Target breach. One of those institutions noticed that one card shop in particular had recently alerted its loyal customers about a huge new batch of more than a million quality dumps that had been added to the online store. Suspecting that the advertised cache of new dumps were actually stolen in the Target breach, fraud investigators with the bank browsed this card shop’s wares and effectively bought back hundreds of the bank’s own cards.
When the bank examined the common point of purchase among all the dumps it had bought from the shady card shop, it found that all of them had been used in Target stores nationwide between Nov. 27 and Dec. 15. Subsequent buys of new cards added to that same shop returned the same result.
On Dec. 19, Target would confirm that crooks had stolen 40 million debit and credit cards from stores nationwide in a breach that extended from Nov. 27 to Dec. 15. Not long after that announcement, I pinged a source at a small community bank in New England to see whether his institution had been notified by Visa or MasterCard about specific cards that were potentially compromised in the Target breach.
This institution has issued a grand total of more than 120,000 debit and credit cards to its customers, but my source told me the tiny bank had not yet heard anything from the card associations about specific cards that might have been compromised as a result of the Target breach. My source was anxious to determine how many of the bank’s cards were most at risk of being used for fraud, and how many should be proactively canceled and re-issued to customers. The bank wasn’t exactly chomping at the bit to re-issue the cards; that process costs around $3 to $5 per card, but more importantly it didn’t want to unnecessarily re-issue cards at a time when many of its customers would be racing around to buy last-minute Christmas gifts and traveling for the holidays.
On the other hand, this bank had identified nearly 6,000 customer cards — almost 5 percent of all cards issued to customers — that had been used at Target stores nationwide during the breach window described by the retailer.
“Nobody has notified us,” my source said. “Law enforcement hasn’t said anything, our statewide banking associations haven’t sent anything out…nothing. Our senior legal counsel today was asking me if we have positive confirmation from the card associations about affected cards, but so far we haven’t gotten anything.”
When I mentioned that a big bank I’d spoken with had found a 100 percent overlap with the Target breach window after purchasing its available cards off a particular black market card shop called rescator[dot]la, my source at the small bank asked would I be willing to advise his fraud team on how to do the same?
CARD SHOPPING
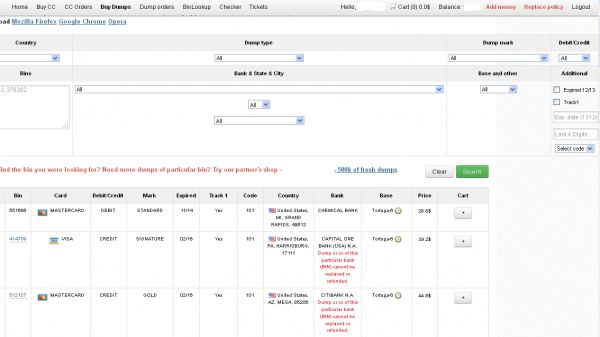
Ultimately, I agreed to help in exchange for permission to write about the bank’s experience without actually naming the institution. The first step in finding any of the bank’s cards for sale was to browse the card shop’s remarkably efficient and customer-friendly Web site and search for the bank’s “BINs”; the Bank Identification Number is merely the first six digits of a debit or credit card, and each bank has its own unique BIN or multiple BINs.
According to the “base” name for all stolen cards sold at this card shop, the proprietor sells only cards stolen in the Target breach.
A quick search on the card shop for the bank’s BINs revealed nearly 100 of its customers’s cards for sale, a mix of MasterCard dumps ranging in price from $26.60 to $44.80 apiece. As one can imagine, this store doesn’t let customers pay for purchases with credit cards; rather, customers can “add money” to their accounts using a variety of irreversible payment mechanisms, including virtual currencies like Bitcoin, Litecoin, WebMoney and PerfectMoney, as well as the more traditional wire transfers via Western Union and MoneyGram.
With my source’s newly registered account funded via wire transfer to the tune of USD $450, it was time to go shopping. My source wasn’t prepared to buy up all of the available cards that match his institution’s BINs, so he opted to start with a batch of 20 or so of the more recently-issued cards for sale.
Like other card shops, this store allows customers to search for available cards using a number of qualifications, including BIN; dozens of card types (MasterCard, Visa, et. al.); expiration date; track type; country; and the name of the financial institution that issued the card.
A key feature of this particular dumps shop is that each card is assigned to a particular “base.” This term is underground slang that refers to an arbitrary code word chosen to describe all of the cards stolen from a specific merchant. In this case, my source at the big bank had said all of the cards his team purchased from this card shop that matched Target’s N0v. 27 – Dec. 15 breach window bore the base name Tortuga, which is Spanish for “tortoise” or “turtle.”
Indeed, shortly after the Target breach began, the proprietor of this card shop — a miscreant nicknamed “Rescator” and a key figure on a Russian-language cybercrime forum known as “Lampeduza” — was advertising a brand new base of one million cards, called Tortuga.
Rescator even created a graphical logo in the Lampeduza forum’s typeface and style, advertising “valid 100% rate,” and offering a money-back guarantee on any cards from this “fresh” base that were found to have been canceled by the card issuer immediately after purchase. In addition, sometime in December, this shop ceased selling cards from other bases aside from those from the Tortuga base. As the month wore on, new Tortuga bases would be added to shop, with each base incrementing by one with almost every passing day (e.g., Tortuga1, Tortuga2, Tortuga3, etc.).
Another fascinating feature of this card shop is that it appears to include the ZIP code and city of the store from which the cards were stolen. One fraud expert I spoke with who asked to remain anonymous said this information is included to help fraudsters purchasing the dumps make same-state purchases, thus avoiding any knee-jerk fraud defenses in which a financial institution might block transactions out-of-state from a known compromised card.
The New England bank decided to purchase 20 of its own cards from this shop, cards from Tortuga bases 6-9, and Tortuga 14 and 15. The store’s “shopping cart” offers the ability to check the validity of each purchased card. Any cards that are checked and found to be invalid automatically get refunded. A check of the cards revealed that just one of the 20 had already been canceled.
The bank quickly ran a fraud and common point-of-purchase analyses on each of the 19 remaining cards. Sure enough, the bank’s database showed that all had been used by customers to make purchases at Target stores around the country between Nov. 29 and Dec. 15.
“Some of these already have confirmed fraud on them, and a few of them were actually just issued recently and have only been used at Target,” my source told me. Incredibly, a number of the cards were flagged for fraud after they were used to make unauthorized purchases at big box retailers, including — wait for it — Target. My source explained that crooks often use stolen dumps to purchase high-priced items such as Xbox consoles and high-dollar amount gift cards, goods that can be fenced, auctioned or otherwise offloaded quickly and easily for cash.
My source said his employer isn’t yet sure which course of action it will take, but that it’s likely the bank will re-issue some or all of the 5,300+ cards affected by the Target breach — most likely sometime after Dec. 25.
The bank is unconcerned that its cards compromised in the Target breach might be used for online shopping fraud because the stolen data does not include the CVV2 — the three digit security code printed on the backs of customer cards. Most online merchants require customers to supply the CVV2 as proof that they posses the legitimate, physical card for the corresponding account that is being used to fund the online purchase.
Update, 5:20 p.m. ET: In a message to consumers, Target CEO Gregg Steinhafel said Target would be offering free credit monitoring for affected customers. Not sure how credit monitoring helps with this specific breach, but at any rate here’s the rest of his statement:
“Yesterday we shared that there was unauthorized access to payment card data at our U.S. stores. The issue has been identified and eliminated. We recognize this has been confusing and disruptive during an already busy holiday season. Our guests’ trust is our top priority at Target and we are committed to making this right.
We want our guests to understand that just because they shopped at Target during the impacted time frame, it doesn’t mean they are victims of fraud. In fact, in other similar situations, there are typically low levels of actual fraud. Most importantly, we want to reassure guests that they will not be held financially responsible for any credit and debit card fraud. And to provide guests with extra assurance, we will be offering free credit monitoring services. We will be in touch with those impacted by this issue soon on how and where to access the service.
We understand it’s been difficult for some guests to reach us via our website and call center. We apologize and want you to understand that we are experiencing unprecedented call volume. Our Target teams are working continuously to build capacity and meet our guests’ needs.
We take this crime seriously. It was a crime against Target, our team members, and most importantly, our guests. We’re in this together, and in that spirit, we are extending a 10% discount – the same amount our team members receive – to guests who shop in U.S. stores on Dec. 21 and 22. Again, we recognize this issue has been confusing and disruptive during an already busy holiday season. We want to emphasize that the issue has been addressed and let guests know they can shop with confidence at their local Target stores.”
[EPSB]
Have you seen:
Non-US Cards Used At Target Fetch Premium”…An underground service that is selling millions of credit and debit card accounts stolen in a recent data breach at retail giant Target has stocked its virtual shelves with a new product: Hundreds of thousands of cards issued by non-U.S. banks that were used at Target across the United States during the retailer’s 19-day data breach. It’s not clear how quickly the non-U.S. cards are selling, but they seem to be fetching a much higher price than those issued by U.S. banks.
[/EPSB]






There is an excellent book on this topic written by Kevin Poulsen entitled Kingpin. It’s fascinating, eye-opening stuff. The genesis of the book can be found in this paper:
http://thenewtech.tv/tech-life/cybercrime-paper-kingpin-by-kevin-poulsen
So if one bought alcohol with their card at Target during this time period did the hackers have access to their Drivers License information as well? Just curious…
How would the Hackers be able to get hold of anyone’s Drivers License information? I don’t think Banks put that information on the Magnetic Strip, that’s on the back of Credit/Debit Card, but I’m not really sure.
It is common practice at Target for the cashiers to request a drivers license from anyone purchasing alcohol. They then scan the barcode on the license (what do they do with the data? Who knows?). If you ask that they not scan, and instead merely visually confirm your age, they will do so, but it requires a supervisor override (similar to when a cashier wants to void a purchase). This means the customer has to wait, etc. So, the net result is that Target scans a shitload of licenses at their checkout counters. No clue how or whether the data are stored, but this is undoubtedly what prompted the question.
Never knew you could ask for a visual verification. After this clusterf&ck, that’s all they’re getting from me going forward.
Oh! I don’t purchase any Alcoholic Beverages, from Target…I did, however, purchase some Vicks “Day Care” for my Daughter, on one of my visits to Target. That requires showing ID.
The Cashier asked for my Driver’s License…I handed it to her…She looked at it, and handed it back, to me. I don’t remember her scanning my Driver’s License, though! Maybe they only scan it, if you purchase Alcoholic Beverages…I don’t know, though. :o/
Sorry to assume everybody knew about this Target practice during routine alcohol purchases. Yes thats right they ask you to scan your ID Card. Since Target has been fooled I’m wondering what happens to this data. Is it encrypted? Where is it stored? I think they should explain to consumers how they keep it safe forever or stop the practice. I no longer let them swipe it, but, many do. Anybody know how long or any details about this process? They aren’t the only retailers who do this. They are just more anal about it than others. Ask your local retail employees and they don’t have a clue. You just get a “its store policy” response.
“…The bank is unconcerned that its cards compromised in the Target breach might be used for online shopping fraud because the stolen data does not include the CVV2…”
According to [semi-private] talk given by a member of the FBI’s cybercrime unit, the CVV2 is from a formula derived from the CC number. You have the number and the formula, you get generate the CVV2. I wouldn’t bet on the criminals not having the formula.
They need to triple DES secret too! Not as easy as one might expect. If the card had been a chip card and the USA merchants had invested in EMV enabled terminals offering real security this all would be interesting but not troublesome.
it is not about the CC nr but about the CCV2, isn’t it? what do you think?
I’ve been trying for days to get Target to cancel my Target Red card (Debit). They refused on the phone because they said I had to have used the card for an online purchase. (I didn’t). I e mailed Target Headquarters saying cancel my card, giving them the card number. I received an e mail back saying “There is no immediate need to cancel your REDcard or any other credit or debit cards” even though I specifically told them to cancel immediately. My bank has reported suspicious activity pertaining to my card. Is there something further I can do short of withdrawing everything from my bank and having all automatic deposits changed to another bank account?
Pauline,
Just call them back and say that you have a better card with lower rates and that you would appreciate if they could cancel out the card.
While they have a point in that your card may not have been part of the breach it is fully your right to cancel when you want.
I would push the issue and if they do not honor it I would kinda say that you will take legal action if required as you no longer want the card.
If it persists after that call your attorney general and they will take care of it for you.
F@ntum
Can a regular person log onto one of these websites and check to see if their own card numbers are being sold?
if you registar you could its rescator.la
Remember if you log on to a site that sells stolen data a) the FBI may be watching and you may get wrapped up in the hoopla, and B) If they are the unscrupulous type and sell peoples cards do you think it would be easy for them to also monitor who connects and inject malware into the systems that are connecting??
Just a thought, I would make sure you use a public wifi connection not your house and also use a computer that is ready for the scrap heap then pull the hard disk out and junk it…DONT use the computer you surf the web for on a day to day or you may get something you didnt ask for.
-F@
I thought about this after I posted the question. Decided not to go to the website. Just very frustrated that the banks and Target aren’t trying to let people know how this happened and what exactly did they grab….
It is not the banks that can tell you how this happened, it would be all TARGET. It is only the banks who lose in the situation because at the end of the day, the banks will refund any fraudulents funds used out of consumers accounts, pay to reissue the cards, and man hours used.
I don’t believe that the banks will truly lose. When a fraudulent purchase is made the banks deduct the transaction directly from the merchant that made the purchase. The merchant loses the product and the profit. Then has to fight to prove they did their best and followed verification protocol. Usually if the merchant wins the customer loses, not the bank. Maybe in this instance the banks will absorb some of the loss, but somehow I doubt it.
Actually most major banks have a credit card fraud department that have real time access to fraud trends world wide. They can pin point the common point of compromise and enable protocols that cuts off card use in specific locations. The banks work hand in hand with Visa and Mastercard. There are several web based restricted access sites that they share infomation and discuss where fraudlent card activity is occurring.
Use Tor to connect to it for anonymity. That said, the site currently does not respond…..
I guess this may put damper on the new product COIN (onlycoin.com) was working on.
I actually had one of those “shut up and take my money moments”. Problem is, there isn’t a chip on their current offerings – yet.
After this breech, I imagine we’re going to see chip cards coming out faster now.
The crime is not victimless, it is the bank that suffers the fraud losses and in turn the consumer because the bank has to sometimes increase fees to absorb some of those costs.
Just a thought; sign up for SMS or e-mail alerts. Virtually all major card issuers have this functionality. If you are reading AT you probably have e-mail, if not an SMS (text) capability. Alternately, many will ring your phone(s) with an account alert. My AMEX card responds to purchases over a selected amount so rapidly that it often comes in as I am signing the chit. There is also a ‘Card Not Present’ alert. Chase will also leave me a voicemail if I am out of range or on an aircraft etc. Do this NOW. Wells Fargo sends an update on all account activity about 3:00 AM every day there is a change if you sign up. This can include autopay, checks cashed and so on.
Both of my Chase Debit Cards are signed up for “Alerts”. If either of them has any suspicious activities, or has an ATM withdrawal or Purchase over my Daily limit of $250.00, for each, I automatically get a Text message, from Chase, letting me know that the Card, in question, is over my $250.00 Daily limit.
You should also check with your Credit Card Company, and your Bank, to see what your Daily Spending/ATM limit is. This is the second time the Credit/Debit Card, for this Chase Account has been Compromised. Last time it was Stolen, whoever got hold of it, spent almost $4000.00 before it was discovered. (Chase did replace all the Money, back into my Account, though.)
When I went to my Chase Bank, to get a temporary Card, I asked them what my Daily Spending/ATM Daily limit was, they said, “$3000.00, for both”! I was absolutely floored!! I never set the Daily Limits that high…Chase did! I immediately had them lower it to $250.00! So, make sure you know what your Daily Spending/ATM limit is!
Signing your card “check ID” may only help in the case your card is lost or stolen. In the circumstance of a fraudulent card manufactured using your card information, it will not be your true card present and there will be no such note to “check ID”. It’s a well intentioned action that offers no deterrent in fraudulent card circumstances.
None of the “see ID” on the back of your card works if the criminals are using a self checkout. Even if the cashiers go look to verify ID, the name and the 16 digits on the front of the card can be different than the magnetic stripe from which the purchase is made. The USPS is the only place that I have experienced a cashier entering in the last four digits from the FRONT of the card that must confrim what is swiped off the magnetic stripe.
These criminals tend to buy gift cards that they unload as quickly as they can or buy high priced items to sell cheap for cash. WE ALL PAY FOR THIS eventually regardless of the EMV system that should be in place.
The “rescator.la” is now changed to “rescator.su”…
.la is no longer responding , they have changed the domain.
It’s “rescator.so” not “rescator.su”….it was a typo in my previous post..
Wow. I went to that website but left quickly. I just wanted to see if it was real. Hope the fbi dont knock on my door . Wonder how do they get away with it.
What Angel wrote may sound unbelieveable but it’s true. A similar thing happened to me and I showed it to my lawyer. He said that they had no grounds to charge me late fees on a credit card that I never used. His advise was to ignore it which I did. However, it’s been about 10 years now and every 6 months or so I get more made up bills for a settlement for something I never owed in the first place. They also called me and said they had a wrong address just like Angel wrote. I also never received a credit card by mail. My only mistake was to deal with a company that tries to scam consumers. I wonder how many people were scared into paying Target illegal stolen money. This may sound crazy but it’s the complete 100% truth.
When I originally commented I clicked the -Notify me when new feedback are added- checkbox and now each time a comment is added I get four emails with the same comment. Is there any manner you’ll be able to take away me from that service? Thanks!
Noyification:
Response time – SMS, call, e-mail etc. varies widely by provider. My AMEX threshold is set at USD 50.00, which means that 80% of my transactions elicit a response. Using Sprint SMS, generally I get a text before a waiter can get the chit back for signature. Chase Visa takes about half an hour max to get a phone call. WFB sends an e-mail nightly with all transactions.
One attempt with a stolen AMEX number in a jewelry store resulted in a decline, not as good as a bust, but good. We called AMEX immediately and they did something.
The other thing is when you have a card you need to ditch, don’t argue, report it stolen and fill out any kind of report you have to. People who will not cancel a card immediately upon request are not being straightforward which removes your obligation to be straightforward with them. You do not have to concoct a story. “I can’t find my card and I think it may be stolen. I was at Far Niente and when I got home I didn’t find it.” Document the call, ask for a name and a replacement card even if you never activate it, then shred the original. My soon-to-be ex was arrested while trying to withdraw $5K with a card I reported ‘missing’ the day before. Not charged but did not get the $pondulies either.
Just issue a free 90 day fraud alert to prevent identity theft.
Therefore causing the thief will find a different victim.
https://www.alerts.equifax.com/AutoFraud_Online/jsp/fraudAlert.jsp
I was just notified last week my card was breached. Now I’m having a new one issued, all because the one time I shop at target. I live in Holland Michigan and my target is just down the road. They said that there helping people who have a card trough target but what about the people who don’t . My god what is wrong with people I don’t have a lot of money to began with but to take the little I do have those people should be put away for the rest of their life.