Authorities in New York on Tuesday announced the indictment of thirteen men accused of running a multi-million dollar fraud ring that allegedly installed Bluetooth-enabled wireless gas pump skimmers at filling stations throughout the southern United States.
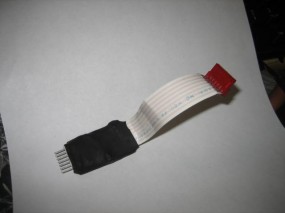
According to documents released by Manhattan District Attorney Cyrus R. Vance, Jr., the accused stole more than $2.1 million in the scheme. Investigators say the men somehow gained access to pumps at Raceway and Racetrac gas stations throughout Georgia, South Carolina and Texas and installed skimming devices like the one pictured below.

A Bluetooth enabled gas pump skimmer lets thieves retrieve stolen card and PIN data wirelessly while they gas up. Image: Manhattan DA.
These devices connect directly to the pump’s power supply, and include a Bluetooth chip that enables thieves to retrieve the stolen data wirelessly — just by pulling up to the pump and opening up a laptop. The defendants allegedly then encoded the stolen card data onto counterfeit cards, and armed with stolen PINs withdrew funds from victim accounts at ATMs. The defendants then allegedly deposited the funds into accounts in New York that they controlled, after which co-conspirators in California and Nevada would withdraw the cash in sub-$10,000 increments to avoid triggering anti-money laundering reporting requirements by the banks.
This blog has featured several stories about gas-pump skimmers that were Bluetooth enabled. What’s remarkable is how common these attacks have become (Google News and Twitter are full of local news reports of apparent gas pump skimmer attacks, like this one at a Pilot station in Tennessee last week).
Last year, I received some information from a police officer in California who is tasked with chronicling many of these incidents (this seems to have become something of a full-time job for him). He sent me some pictures of a few several more common gas pump skimmers that show up at filling stations in his state, including the devices show above right and below left.
The incident reports he filed on the devices pictured below indicates that thieves involved in this type of crime have a typical playbook. These crimes, as with attacks on regular bank ATMs, tend to occur on weekends, often in the early morning hours. From his report:
“M.O.: Two or three suspects exit vehicle, look around for people watching them, then pretend to pump gas by placing the dispenser into the gas tank. One suspect will eventually enter the store, pay cash to purchase a small amount of gas or a drink to distract attention away from the pump. Meanwhile, another suspect places a skimming device inside the pump by opening the front with a universal key. Time to install/remove is between 5 – 10 minutes.”
I don’t worry too much about gas pump skimmers; there is virtually no way for the average consumer to tell if a pump has been compromised. But I would urge readers to avoid paying at the pump using a debit card. While debit cards have the same zero-liability protection afforded to credit cards, having your checking account emptied of cash can be a huge hassle and create secondary problems (bounced checks, for instance).
More information about the indictments in the New York case can be found in this press announcement (PDF).





What’s crazy about this and I for see happening more and more is that several gas stations in my area have started to offer a lower price for gas if you use a debit card or cash. I see these types of skimmers becoming more and more abundant.
In NY state the vast majority of gas stations, certainly all that belong to major oil companies, do that.
The price delta is 10 cents per gallon.
What!? I need your stations. In FL they charge less if you pay in cash (probably tax purposes 😉
You’re also welcome to pay our $.34-$.39/gallon tax burden, too. Loses its appeal once that’s revealed, I’m sure. Personally, I avoid any station that charges more for credit purchases.
Back on topic, it seems that pump manufacturers need to better design their product to protect against tampering. To leave the security of these devices to counter clerks who rarely venture outside seems a bit far-fetched, to say the least.
“Personally, I avoid any station that charges more for credit purchases.”
Ditto.
Even though you can’t blame them, being in the cut throat market they’re in, they’re simply doing it to save some of their money by passing on those costs.
But… if in a pinch, at those locations, I just pay cash – if the price is that sweet.
It’s not about taxes, it’s about paying to use the credit card. They pay a fee of around 2% to be able to accept and process your credit card. They don’t have to pay that if you use cash or debit. That’s how the banks that issue credit cards make money of people who pay their bill in full every month – the fees they charge the merchants for the convenience of accepting cards.
Stores still pay to accept debit cards. You think that is free for them? Its at a lower cost then credit cards, but they still pay a % and a small fee of about 5cents for each debit card accepted. That is why the sign says “debit/credit” and another for cash.
I think the discounts are to get people away from credit cards, because the fees onthe CC’s are higher.
“suspect places a skimming device inside the pump by opening the front with a universal key.” Universal key! So access to a corporation’s “cash register” can be accomplished with a device so easily obtained as a universal key. There is a CEO somewhere who has some explaining to do!
I believe the fire code requires the universal key so the fire department can put out a pump fire. You can buy them online so they offer minimal security.
And if true, that law is yet another example of incompetent legislation. Or at the very least, legislation that sorely needs updating for the “modern” electronic era.
Either the pumps need to be designed so that there is a SECONDARY lock internally that provides access to the electronics, or as someone else suggested, some sort of alarm whenever the pump is opened, or I could probably think of a dozen other decent options given 30 minutes.
Foresight: we [don’t] gotz it.
I’m positive that here in NJ the code requires that there be a master shut-off valve for all pumps. That seems much more reasonable than having to make the locks worthless
Rather than worry about a key, the pump makers should have created a secure area inside the box to house the mag stripe reader, like PIN pads have.
But they won’t do that now, and for good reason. There’s a different upgrade coming soon in order to support EMV. Physical security of the card reader becomes almost irrelevant once Chip and PIN is 100% rolled out, as all security operations are managed on the chip.
I guess you missed Brian’s previous article about chip and pin..
http://krebsonsecurity.com/2012/09/researchers-chip-and-pin-enables-chip-and-skim/
Brian,
Coming from someone within the convenience/petroleum industry, I have experience with the internal organs(electronics) of a gasoline pump. They make a SCR(Secure Card Reader) and an EPP kit(Encrypted Pin Pad) which in combo makes the PIN and Card unreadable by most people(I do not know whether they can be compromised but I don’t believe so) The problem is, its not an industry standard and people do not want to fork over $3000+ USD for a SINGLE pump to have this. There are also locks made by Compx that can further protect the inside of the pumps with keys that cannot be copied(legally anyway). The problem with upgrading locks is, the company I work for has had people take pry bars to the gas pump doors and break the hinges on the pump rendering the door and pump useless. The Charlotte area in NC has developed an infamous reputation for these types of break-ins, though the reason for the break in is not for a card skimmer(normally) but to get free gas through a part in the pump. Also, as one of the articles you linked said, the key for most pumps is indeed universal, sadly.
Thanks for your time(to anyone who reads this whole ramble)
– Red
I read a few years back a letter to a IT security magazine. Based on the security issues seen across the industry, the security pro strongly advised never using your debit card at any gas pump. Universal keys, the ease of installing skimmers and these are the issues we know about.
I don’t carry a regular credit card, but only use my debit card as a credit card at gas pumps and most anywhere else for that matter. Having to spend the extra few seconds to give my John Hancock is well worth avoiding the extra risk for debit card PIN theft.
Conversely, I don’t even have a debit card (or an ATM card, for that matter). If that bad guy gets money, it’ll be the banks’, not mine.
If you’re using your debit card, even though you don’t provide a pin, the criminal can take that debit card account number that you just paid with and drain your account, with or without pin, they just won’t be able to walk up to an ATM with a cloned card, they’ll have to encode the number onto a credit card or make online purchases with the number. The downside for you: nobody is going to cover your loss. If it were a standard credit card you’d be on the hook for $50/max, but if it’s your debit card with a VISA\MC logo, you can lose all your savings and nobody is going to cover your loses. Get rid of the debit card.
Hmmm, sorry, not exactly correct.
Supposedly, there is a $50 limit on debit cards (or EFT cards) and the banks have had complaints lodged against them for not following this.
Then too, the actual maximum losses occurred has different ranges, from:
a) $500 – if the victim reports it to the bank MORE THAN 2 business days after learning of the fraud or
b) everything – if the victim does not report the situation WITHIN 60 days or
c) $50 – if the EFT card is lost/stolen and there is an unauthorized withdrawal AND if the victim notifies the financial institution WITHIN 2 business days.
The rub here is, how many people check their checking accounts every day or every other day…???
except that they can drain your account, cause you to encur fees and the bank can take days or weeks to refund your money and make you whole (less the $50 you are liable for)… wells fargo refunded a bogus transaction within 2 days but it took weeks to complete the investigation. it was a relitively tiny amount, $137 or so but with thousands in question they may not be so accomidating.
Yes, very true.
I debated about adding the time frames for recovery and investigations but didn’t want to make my post that much longer.
I probably should have done so in order to make it more comprehensive for folks who do not about that process and/or did not look it up.
But accommodation of customers, yep, not always so nice for them/us…
Thanks for the added info Jeffb.
Since I heard about gas station skimmers in Fla. several years back, I now use a gift card/prepaid gas card which I will do now in other retail stores, since the Target hacking. I thought people would know better to not use debit cards at gas stations since it’s been talked about for several years. Not knowing this fact now days shows ignorance.
Hardly fair since only a minority of the public reads a newspaper or watches the news. I have been building embedded systems for 30 years and this is the first I have heard of skimming gas pumps.
Debit cards I don’t think universally carry the same loss limit protection as credit cards. I never use a debit card anywhere anytime for that reason.
Can you use some sort of Bluetooth scanner to determine if there is a Bluetooth receiver close by? All smartphones have a BT radio on them. I’m sure Android and Apple have APIs to discover devices.
Harry, I think you’ll be wanting to download a Bluetooth scanner that looks for signals being transmitted not receivers. Many to choose from but also many devices transmitting that frequency so you may have quite a few false positives.
Better to just say no to using debit cards on readers that can’t be secured to your satisfaction.
A Bluetooth detector won’t help. The Bluetooth radio in the skimmer is listening for a connection from the thief, and only transmits the data when requested. And since every other person in the station will have Bluetooth on their smartphones, you’ll get nothing but false positives.
To follow up my own comment about detecting Bluetooth (BT) with a smartphone, I see the protocol supports a device discovery call. This would presumably be executed by my phone when I clicked “Scan BT devices”. However it appears that the attackers would be smart enough to disable answering device discovery requests. So the attackers would be set up to contact it directly thus the phone would not be able to scan and detect the BT device.
Regarding extra security on the lock – that doesn’t help for an inside job. But I don’t know what percentage of these attacks fall into that category.
If there was ever a justified reason for ‘mandatory minimum’ sentences, participation in the perpetration of this type of criminal fraud should certainly deserve a very stiff allocation of hard time.
Is any progress being made in moving the US to chipped cards?
Since the Target hack there’s some talk about it again, but talk is cheap and implementing it would be massively expensive
Larry: yes, we need to get the chip cards, and it appears that Target will file bankruptcy as there is no way they can pay back over 3.5 billion in lawsuits. I dropped out of the class action when I heard it went from 40 mill to 110 mill customers; no one will get anything. Avoid shopping at these stores or use cash if you need to get something there. Use a Walmart prepaid card to buy gas, or Shell prepaid, etc.
What?!!? Target may get pounded and face significant lawsuits that could force executive turnover, but bankruptcy?!?
They typically spend $2-3 BILLION / year on share buybacks and dividends while keeping $700-2bn in cash on the balance sheet. There’s a LOT to amputate in a crisis. In a severe pinch they might even be able to sell their RedCard book to a bank.
Investors have finally figured out that this is surely going to leave a major mark on Target, but insolvency doesn’t seem to be in the cards (sorry, couldn’t resist).
Good idea to purchase gift cards. Do you use a card (debit/credit) to purchase the gift cards?
My card from a large bank was recently replaced and it has a chip in it. So I guess, now, there just needs to be a reader for it.
Yep, that looks to be the next big hurdle, getting the chip readers in all POS locations – moving from stripe to chip is going to be big in the U.S. because many vendors are going to balk at putting out more cash for new readers.
Too bad the U.S. bank/credit cards issuers (with all their vast wisdom) didn’t keep up with the E.U. and Canada… Look at all the loss of revenue compared to what they would have to pay up front to implement these early on (and a lot of folks were of the same mind that these institutions should have just moved forward).
I live in Canada where chip and pin are commonplace. However there are still some downfalls to using this method. One being a dispute I currently have on-going with my card issuer whereby a merchant (or employee) have modded their POS system to reboot upon engaging the built-in printer. Since you the card holder have entered your PIN, you have “authorized” the transaction (in my case two “failed” attempts). You would think these issues would be quickly resolved and the merchant disqualified from using a POS system… trouble here is having the issues escalated through your CC company to stop this behaviour. I suspect future scams will emerge that are also designed to trick consumers into “authorizing” fraudulent purchases will become more commonplace and eventually CC companies will need to enforce/police this when the losses and complaints become overwhelming.
They are slowly rolling out the cards. There are some liability shifts coming up which should help to encourage merchants to upgrade their terminals.
http://en.wikipedia.org/wiki/EMV#United_States
Unfortunately for pay at the pump, the liability shift comes in October 2017. For all other POS terminals, the liability shift will be in Oct 2015.
While I get it that retailer need to go to great lengths to keep customer data safe (any PII, not just CC#’s), the whole idea of liability shift seems to be just another way for the banks to make more money/avoid expense. The truth of the matter is that the transaction that is happening using a swiped card (debit or regular CC) is a transaction between the consumer and the BANK – not the retailer. The retailer is actually transacting with the bank in that case.
While it’s true that the premise equipment belongs to the retailer, the banks have not provided the infrastructure needed to deliver a secure transaction channel between it’s customer and itself!! If a retailer wants to provide a secure channel today, the only choice is end to end encryption, and the banks and other middlemen want to charge them for the privilege. This seems backwards to me.
If universal key access is available what is the cost to each station to install a trigger button so that when the pump door is open with it sounds an alarm to the clerk who has to take manual action to silence the alarm as well as contact the authorities. That along with proper video surveillance should deter it from happening
The problem with that is cost to implement is greater than their probable loss…so that mean$ it won’t happen.
Looks a lot like freshgoodcvv.blogspot….
Similar ribbons, wrapping
Good article, I posted it on my facebook account
Time to install/remove is between 5 – 10 minutes.
How can you distract cashier for 5-10 min without him looking at the pump not even once ? Unbelievable .
“How can you distract cashier for 5-10 min without him looking at the pump not even once ? ”
Simple.
The cashier often does not have a view of the pump. The cash register is at a location/at an angle that the cashier would have to walk out from behind the counter to see the pump. So the crook keeps the employee busy at the cash register.
Even if s/he faces the pump and there is a large window towards the pump the window is often used display large posters of advertising.
Not to mentiom, the freaking vehicle is normally parked in from of the pump. If they were wise, they’d use a big vehicle to completely erase any view of the pump at all, with tinted windows.
The problem is, there isn’t any alerts/alarms when a pump is opened. It would have to be silent to the crook who opens it. The clerk writes down the State and License plate number, date and time, so if there is any video, its a good reference spot.
If the crooks can place Bluetooth skimmers inside the pumps, can’t the pump owners install Bluetooth alarms to let attendants know that the pump door has been opened and they should take action, like calling the police, getting license numbers, taking pictures of those at the pumps???
Why would they? Are the station owners getting hit with fines or lawsuits? As far as they care, a legitimate transaction was made at their pump so they’re not losing any money.
There are two things that I am curious about, is it possible to detect the bluetooth signal and is this door on the gas pump sealed by a security tape? Is it as simple as confirming the security tape is not broken? I have seen the tape but not noticed what it secures.
The Security Tape on most gas station card reader doors…. Was the tape replaced or removed? I’d like to know what was done or not done to the secrity tape at the Racetrac locations. Is the security tape being easily defeated???
Good advice about using a credit card at the gas pump. Sometimes a debit card will work as a credit card if the pump allows you that option and you select it. However, some pumps don’t always offer that as an option so you’re stuck having to use your card as debit. Probably better to go inside the store and pay if you’re using debit. I always learn something new from these articles and posts. It’s a bit unsettling to think that people are out there trying to take advantage of you and obviously don’t mind doing it.
The universal or brass key problem has existed for years. Visa issued two formal warnings in 2006.
See http://usa.visa.com/download/merchants/20071117_datasecurityalert_petroleum.pdf and http://usa.visa.com/download/merchants/Alert_AFD_Sept_2006.pdf
For more general alerts see http://usa.visa.com/merchants/risk_management/cisp_alerts.html
I use the Google Wallet debit card. It can only be drained of as much cash as I have loaded into it; it is not connected to a checking account. I’m using it more and more in ‘public’ places.
Russ B – How do you fund that Google Wallet card if it isn’t connected to youir bank acount? It’s 2.9% to fund it by another card.
@BradS – There is a checking account associated with the card (and/or you can do a credit card) but the funds don’t automatically flow from the bank to Google Wallet. You have to login to Google Wallet and specify how much to transfer (and where to transfer from) to the card when your card balance is getting low. That remaining balance is the limit that will be able to be drained from your card. When the card reaches $zero then purchases are refused until you add more money.
Yeah…. criminals, jeez, they just keep coming…
a) I for one always look for the corporate tape on pumps before I use them (but what if they use counterfeit tape…).
b) I always use credit cards (have done so for the past 10 years ’cause of punk criminals) or cash depending on the city and location.
But crap, I would not have noticed this Bluetooth device INSIDE the pump.
— Nichan had a GREAT suggestion about having an in-store alarm of some sort triggered if a perp jimmies the pump open in any fashion.
And sure, as Rick indicated there may be some additional cost to implement that setup but that would only be for the moment. Looking down the road at even one single hijacking of card info from skimmed cards would be more than worth it than the loss of business & revenue, possible law suit(s) from an individual (or bank?) and involvement with law enforcement (ask Brian K. about the hassle with LE from his past SWATTING incident and other situations from various punks).
These idiots continue to get more ingenious with their methods, we need to figure out how to do better…
Check out this story I read a few weeks ago about in a public FBI info blurb about criminals using tin foil on gas station roof tops to block the credit card authorization process – meantime, the station attendant manually approves the credit card purchase thinking it’s yet another glitch in the network (and Brian, if you already wrote about it, sorry, I didn’t know – and after my not having commented on anything here for quite a while… ;-}
http://www.creditcards.com/credit-card-news/feed_horn-scheme-curses-foiled-again-1282.php
sorry, I just found another earlier “tin foil” story from 8/11/13 and if it weren’t so serious you’d laugh by the time you got to the 6th paragraph (all short)…
http://www.wptv.com/dpp/news/region_n_palm_beach_county/jupiter/thieves-try-using-aluminum-foil-to-make-bad-credit-cards-process
Now I’m wondering how long this ruse has been in play…??
Thank you Brian Krebs for sharing another great blog
Sorry to add to the confusion. But it would be the state weight and measures people that would demand a universal key. The FD would have no reason to be inside a gas pump. But weight and measures would want you to get the gallons you pay for. The owner, not so much. But weights and measures would place a seal, tamper seal on the pump, at least they do here in the state of Missouri, pronounced misery. Always check the seal. That seal tells you that you get 99.99% of what you pay for.
Identity theft is another possible threat from schemes like this, especially with the very poor bluetooth security that comes with many new cars now.
I just purchased a new VW, which comes with a “Just Works” bluetooth that goes into pairing mode every single time the car is turned on. It will pair with any device that asks to pair with it, completely without a security code, and you can’t turn off this “feature”.
Apparently many manufacturers are moving toward the “no PIN required” model for bluetooth pairing.
I fully expect to read some future report from Brian that uncovers scams based on poor automobile bluetooth security.
What…? Talk about stupid.
Yes, maybe VW (and whomever else) is trying to “make it convenient” for the consumer but, yet, another hole.
I wonder if they are relying on the consumer to tap “ok” when the pairing attempt occurs?
— Did you have to do that in your VW for the first time or does that “ok to pair” screen never come up?
When I bought my new Honda in Jan. 2013, and for any new BT device, it requires authorization to pair.
It’s a sad day if this is true if car manufacturers are all going down that rabbit hole of convenience of “just works” without any authorization.
Brian,
What about getting a pre-paid visa debit card & using it for day-to-day spending. if comprimised, you don’t have to replace CCs or loose personal data.
If you researched that, I bet you could get on the radio again.
All Iranian names mentioned in the indictment? Can someone verify the country of origin of these last names?
@ Joe J
Why do you say the names sound Iranian ? If anything they sound Armenian to me.
Where I live, people who pay with credit have to pay about .10-.15 more for gas than those who use cash. I’ll admit that I don’t carry a lot of cash around, but since I started working in cybersec I’ve stopped using my debit card directly at the pump. I go inside for the transaction to reduce skimmer risks.
I’m in agreement with @what what….how these crooks manage to tamper with these pumps without ANYONE noticing is amazing…most gas station mangers are super paranoid about robberies, etc. I guess this type of thievery is too “sophisticated” to notice initially.
The US has been avoiding upgrading cards to EMV technology (EURO, MasterCard, Visa) because merchants and banks do not want the expense of having to upgrade equipment and terminals. Mostly the merchants- as banks have been required to upgrade ATM machines. In European countries, the cards use a chip that constantly changes the codes needed for approval, thus making counterfeit cards nearly impossible. In the US, all of the information needed to hack is located in a plain magnetic strip, which is easily hacked.
If people want to see real changes, they should contact their congressional rep about enforcing an upgrade to EMV technology.
While I received this via the Krebs On Security email notification, the good folks at Consumerist.com also linked to the story.
So, to thank them for doing so, since you (Branson) suggested that folks contact their rep, here is the Consumerist.com story about how to go about doing just that.
http://consumerist.com/2014/01/23/a-simple-guide-for-contacting-your-local-lawmakers-and-what-to-say-to-them/
http://www.a2t.ro | Camere de supraveghere
Americans are not going to buy surveillance cameras from Romania, especially not with a credit card.
Universal key??? Good lord. I just received my first fraudulent charge from the Target breach. Someone tried to up a copy of AVG as a test. *snip* *snip*
Aside from the obvious silliness of a “universal” key, shouldn’t there be anti-tamper switches in these things. Heck, just a really hard to reproduce sticker across the doorway could help. Even low cost PC cases have anti-tamper switches in them, they can’t honestly say they didn’t see this coming.
Aaaand then I read all of the above comments that totally duplicate mine. And do a better job of it. I guess I just needed to vent.
African Criminal Enterprises, indeed.
One gas station i use asks for the zip code of the debit cardholder instead of the pin number…….no idea if it helps or why they do it.
If you go inside they ask for the pin
The reason they ask for the zip code is to perform an AVS (address verification( check. The pump is considered card present unattended, and the merchant will get a better interchange rate by supplying the zip code on the auth request.
Not to threadjack, but now that LR is down and the Feds are presumably exploiting everything they’ve seized, what is the new coin of the shyster realm?
I’m sure that something has popped up in it’s place and I really don’t want to get anywhere near their nasty world.
Brian, has anyone (so far, anyway) submitted your name for a Pulitzer Prize in journalism this past year (2013)? The deadline for entries is midnight tonight (January 25th, $50 entry fee by one of the 4 major credit cards), and I would certainly think you have demonstrated repeatedly that such a nomination is well-deserved.