First American Bank in Illinois is urging residents and tourists alike to avoid paying for cab rides in Chicago with credit or debit cards, warning that an ongoing data breach seems to be connected with card processing systems used by a large number of taxis in the Windy City.
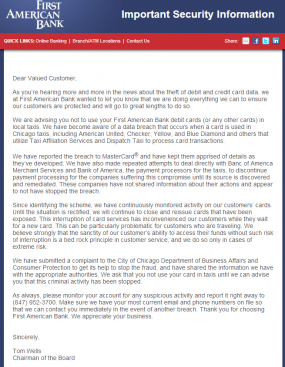
In an unusually blunt and public statement sent to customers on Friday, Elk Grove, Ill.-based First American Bank said, “We are advising you not to use your First American Bank debit cards (or any other cards) in local taxis.” The message, penned by the bank’s chairman Tom Wells, continued:
“We have become aware of a data breach that occurs when a card is used in Chicago taxis, including American United, Checker, Yellow, and Blue Diamond and others that utilize Taxi Affiliation Services and Dispatch Taxi to process card transactions.”
“We have reported the breach to MasterCard® and have kept them apprised of details as they’ve developed. We have also made repeated attempts to deal directly with Banc of America Merchant Services and Bank of America, the payment processors for the taxis, to discontinue payment processing for the companies suffering this compromise until its source is discovered and remediated. These companies have not shared information about their actions and appear to not have stopped the breach.”
Bank of America, in a written statement, declined to discuss the matter, saying BofA “cannot discuss specific client matters.” Neither Taxi Affiliation Services nor Dispatch Taxi returned messages seeking comment.
Christi Childers, associate general counsel and compliance officer at First American Bank, said the bank made the decision to issue the warning about 18 days after being alerted to a pattern of fraud on cards that were all previously used at taxis in Chicago. The bank, which only issues MasterCard debit cards, has begun canceling cards used in Chicago taxis, and has already reissued 220 cards related to the fraud pattern. So far, the bank has seen more than 466 suspicious charges totaling more than $62,000 subsequent to those cards being used in Chicago taxis.
“We got calls from several customers, looked at their transactions and triangulated what was common here,” Childers said. “We’ve been complaining to Bank of America, saying, ‘Hey, do something about this.’ They said they couldn’t give us any information and that we need to talk to MasterCard.”
James Issokson, a spokesman for MasterCard, said in a brief emailed statement that MasterCard is “aware of and investigating reports of a potential breach affecting taxi cabs in Chicago.”
According to First American Bank and at least one bank based in the Midwestern United States, the fraud related to the affected taxis shows up on cards as “Chi Taxi,” and has been going on since at least early December 2013.
Avivah Litan, a fraud analyst with Gartner Inc., said the move by First American to publicize the incident suggests that many banks are feeling fatigued over the sheer volume of intrusions involving customer card data.
“I’m shocked, and it’s pretty amazing that they put that out there publicly, because everyone is usually so scared that they’re going to piss off Visa and MasterCard,” Litan said. “I’ve never seen any bank speak up like that. They’re probably just fed up.”
If banks are experiencing breach fatigue, it’s a good bet that consumers are feeling it as well. Over the weekend, I spent several hours contacting more than two dozen online merchants — including two relatively small credit card processors — whose Web stores were apparently compromised late last year by card-stealing malware. If you weren’t fatigued by the breaches yet, just wait until the end of this week. Stay tuned.




In other breaking news.. Taxis in Chicago were actually accepting credit cards as a form of payment; the entire fleet of each affiliation must have repaired all the broken machines sometime around December 2013!
Funny, the machines in the Philly cabs are always broken too. Using a credit card cuts into the drivers income from the fare, I wonder how those machines got broken. In Philly it’s mandated that the cabs accept cards, thank you PPA regulations…
Yep. All CC machines are “broken” until you say you don’t have any cash and start to exit the cab, then it becomes fixed all the sudden.
Odd, I don’t take cabs that often, but I’ve never had that problem. I’m usually riding with Old City Cab …
Cabbies NEVER want to take a card. I used to travel frequently for work and it was the same in every city. I had a corporate card, so I always tried to use it so I didn’t have to worry about reimbursement. With the cabs, it got to the point where I asked if they’d take it before I even got in.
It’s not hard to figure out why they don’t want to take a card. They don’t get their tips right away and they will automatically have taxes withheld and go on their W2. Cash tips are immediate and many don’t disclose them fully come tax time. Same thing with waiters and waitresses. Not my problem though…
Em, there are simply so many ways to steal card info. It’s even easier than making fake money.
Thanks for the warning – I have passed it on.
Nit question: Why does MAR 14 appear at the top of this posting above the social media icons?
@techvet — the big number is the day.
Brian, I had the same question, until I figured out what the numbers represent. It could have been avoided if you used a 4 digit year. Are we doomed to repeat past mistakes? Admittedly, the year 3000 is a long way off, but stil…
+1 for getting the 4-digit year….
Jezus, guys, just enjoy this new fresh mllenium, be happy you can experience it, see it as a one off chance; By the year 3.000 AD nobody remembers Brain Krebs or any of us, it doesn’t matter whether you use 2 or 4 digits, there won’t be any computers anymore, probably not even humans.
Instead of the four digit year, how about the old fashioned ‘ as in MAR ’14?
I know it hasn’t been in style as much this century, but it was recognizable in the last one…
I hadn’t realised about the day number until you mentioned it. It looks like «post #4», not as something related to the date.
If you don’t want to move it to the same line as the month, maybe adding a border to the small tag will make it look more like a calendar.
For you real smart geeks out there: you realize, of course, that some enterprise start-up is going to find the definitive solution to these kinds of consumer data breaches, earn everyone’s eternal gratitude, and make an awful lot of money.
solution already exists, it’s been in place for years now in Europe. it’s called ‘chip and pin’ and it’s coming to a Visa or MC near you, October ’15
There is no definitive answer – try a search on this site for chip & pin problems.
It’s really hard to imagine, btw, that the rollout will be done by October, 2015. Maybe the cards will be done, but there are literally millions of terminals that will need to be replaced. Anyone know about vendor capacity in that regard?
Duane,
You’re correct that chip/PIN isn’t perfect but it’s hugely more secure that mag stripe, especially in making it much more difficult for criminals to create fake cards.
I agree what chip and pin does is make fewer breach events. However all the consequences of breaches would be contained in those fewer events.
It doesn’t does not reduce overall risk. It just moves it to online merchants, scams to grandma, etc.
I posted a CRC analogy/allegory in an earlier thread. The chip and pin is no doubt a better CRC. So sure, let’s do it.. but we should understand it’s the large packet size that’s the problem. We are metaphorically batching up all the data into one huge packet and then trying to make a single CRC tell us where in that packet the error(s) are located. (and by packet size I’m not talking about the single transaction, i’m talking about aggregating all sorts of data into large persistent dbs – big data etc.).
Rather than setting up one super huge breach, we must make the errors more manageable. Reduce data collected, moved, stored, and protected (not as the quote in brian’s previous post suggest, make it larger!). The hackers introduce some noise, and because we insist on putting everything we can into that one huge pile (and no, having segregated data with the same access methods doesn’t qualify as segregated) we have essentially one packet of data.
So just as the CRC polynomial detects certain types of errors, the various security mechanisms, policies etc. handle certain types of breaches, such as chip and pin. So folks mistakenly get more confident of error detection, and scale up packet size.
We see the results.. the smaller entities with data in that pile get delayed, and harmed. The CRC detects the target bit burst, and the entity with a few bits in the huge packet detects their single bit error. The protocol favors the bit burst (20 bits is more important than 1), so the little banks have to wait while the large packet is reassembled and resent (or cards produced, investigations made, etc). Had we constructed the system with smaller packets, we could more easily recover from errors. Of course the overall efficiency isn’t as good, as we have packet overhead, so profits to the folks moving large packets would not be as good. (but to smaller folks they only lose going with a single large packet).
This is the price of data aggregation. When we find ourselves with a noisy data pipe, we should reduce packet size.
Well folks, we have a noisy pipe when it comes to grandma’s data. Aggregating it isn’t the answer, it’s the problem. The difficulties we see with echos from the detection by intersection (CRC equivalent) are made worse by large amounts of data all flowing through one process/system (essentially becoming one giant data packet).
Chip and pin, like a better CRC is great, but we had better reduce the amount of data we hold if we are serious about security.
I do agree we should have already taken the low hanging security fruit and implemented chip and pin years ago. But hey, when it comes to handling of grandma’s data, i’m less popular than Warren Buffett on an executive compensation committee 🙂
The fraud will shift to Card Not Present fraud once EMV is rolled out in the US. And the criminal syndicates will double down on their investment to figure out how to monetize (decyrypt) the info they are already skimming from EMV machines.
Observationalist, you’re exactly right. the credit card brands are busy in the US trying to figure out how to reduce card not present (CNP) fraud once EMV gets deployed. Because they know in europe CNP fraud is through the roof and card present fraud is ticking back up.
Also worth keeping in mind that EMV is a fraud protection not data protection standard. And that fraud protection only works when all fraud enforcement technologies are active, which during the transition they usually are not. So a breach of EMV data will allow that data to be used for card present and card not present fraud sadly.
And what is the best way to protect consumers? I want to see encryption from the point of swipe to the processors. It is being done today, and it protects my data when I use a card at those merchants. EMV doesn’t protect the data.
And while we should get to EMV as well, one industry estmated that they could save $10 billion in fraud by spending $60 billion on upgrading all their systems to EMV. that doesn’t sound like a beneficial calculation. But almost all industries have been able to incrementally add encryption support at a reasonable cost. We need to do encryption now and EMV tomorrow.
For limos there is Uber. I Googled ” smartphone apps for taxi service” and got a good many hits. Is there a smartphone guru out there who could elaborate on this subject?
Some folks don’t like Uber, for their price gouging. Ymmv.
Way to go First American Bank! Perhaps this public pressure will start the other banks to speak up and demand action beyond PCI standards. Thanks again Brian for the tip off yet again.
Is now the time to ask this? What difference has PCI made? Even if you’re in total compliance you can still get hit. If you’ve made no attempt at compliance, and get hit, what teeth will PCI show?
PCI is not a panacea, but it does get businesses to start paying some attention to security instead of no attention to security. The problem is that figuring out what PCI compliant vendors have been hacked is a lot easier than finding out how many have not been hacked due to the PCI process, since businesses tend to not report when attempted attacks fail (and even when attacks do succeed, they try and keep it quiet, if they discover it in the first place).
Does anyone here remember the commercial of a few years back from Visa? About half the commercial was filmed from above to show people in a restaurant twirling round and round in an efficient and symmetrical manner. Everyone was using their Visa debit card, purchasing their swill, and leaving quickly until one cash-using individualist put a monkey wrench in the works.
The moral of the story is: Visa (and Mastercard and AmEx and …) convinced us to use our debit/credit cards with wild abandon, but the many establishments which accept our cards never bothered to secure their infrastructure.
“I told you so”.
The switch to payment systems that authenticate with PKI cannot come too soon.
“I told you so”…
Switching to payment systems that authenticate with PKI cannot happen too soon.
The other protection method (and also not 100% guaranteed) is application whitelisting. While this is dysfunctional for the most part, on desktops; it’s the remediating factor that could have blocked most of the malware-based attacks that have occurred.
Why isn’t this being used on critical systems (like POS) and on Internet-facing systems (like web-servers). If your code is not changing several times per week this could be your answer.
Plastic credit and debit cards are a relic from the pre-Internet era, and were never conceived to be secure from electronic bandits. Their numbers are easier to steal than passwords, so why are we surprised that the issuers are forced to force us to change them so often? The bottom line is there will be no winning the payment-security game until both plastic cards AND passwords go away and are replaced by dynamic, multi-factor, ID-checking where each consumer chooses his own combination of factors. Open source technology is the path to this future.
The credit card scams should have been expected and better protections put in place years ago as a prevention. What banks are doing is passing these costs onto consumers through higher processing fees and those actually hit a major disruption in their lives. I not only want to be indemnified, but it to be stopped. Here again banks looking only at their bottom line and not the well being of their customers.
I would assume the taxi service is using a city wide WIFI or cellular service that has some type of vulnerability which allows man in the middle attacks to vacuum up data as it’s passed along. Maybe a unsecured WIFI connection of some type. It’s very apparent the owners of the taxi service clearly don’t care about internet security issues or the card transaction safety of their customers
Even if they use some kind of wifi as you suggest, they should be using a ssl layer inside. I find that unliklely. I think it’s more common that all the data is dumped nightly at the taxi company clerk… whose desk turns up to have been infected.
Does anyone know who processes for NYC taxis?
Tim:
Starting in 2007, Verifone Transit Systems had the contract for merchant acceptance of credit cards with the NYC Taxi & Limousine Commission. They in turn had a merchant-processing agreement with IRN Payment Systems of Westbury, NY, who used Global Payments as their processor.
Use UBER… the best frictionless form of payment in a C2B environment. For those unaware of UBER Taxi, no credit card is ever presented to the driver… And the sad part is – all the major cities initially fight to keep UBER out of there corrupt and antiquated taxi system.
Please don’t encourage a rogue (and in some cities illegal) driving service. There are some big benefits to taxis, namely regulated fares, usually plentiful supply, and they have to take you where you want to go. By the way, you don’t need to present a card to the taxi driver, all of the cabs I’ve been in have readers in the rear seat. Uber is no more secure, whether you present your card info in the cab or online or wherever, you are only as secure as the company gathering your card info. Better yet, just pay cash for your cab fares. I always do.
Brian… Do we know physically where Smucker’s was breached ??? Same question holds for a Target. Do we KNOW where the Target breach physically happened ? Are they typically in one location or are they spread across a wide field of view on the web ???
Can you help me understand this ???
the Smucker’s breach was an intrusion of their Web site. The Target breach involved the installation of malware onto the cash registers in most — if not all — of Target’s stores.
Thanks so much for the tip! I live in Chicago and checked my statements and I had around 6 fraudulent charges, all for use in taxi cabs in Long Island, NY except one in VA. All were for under $10 too so I didn’t notice when briefly going over my bill at the end of each month.
Everybody in Chicago, check your statements line by line if you’ve used a cab in 2014!
Paying cash for taxi services are good thing to avoid scams of credit card payment. you could also find taxi mobility applications and pay through internet. Some of the service providers includes, taximobility, Tdispatch, and digital dispatch offering online taxi bookings.
Don’t ride on carriage cab. When I rode with them, I got fraudulent credit card charges.
Also, a while ago a carriage cab taxi took me for a ride by telling me that he knew my destination, but in my drunkard stupor I fell asleep and he was lost when I woke up. So he took me back to my starting point and wanted to charge me $75 in fare. When I called the police, they said that I had to pay then take it up with the company.
That’s the fine Chicago police department of corruption at work.
Never will ride carriage can again.