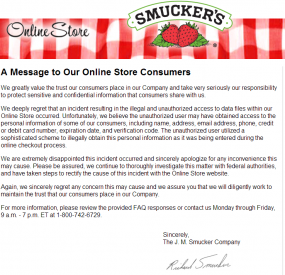
Jam and jelly maker Smucker’s last week shuttered its online store, notifying visitors that the site was being retooled because of a security breach that jeopardized customers’ credit card data. Closer examination of the attack suggests that the company was but one of several dozen firms — including at least one credit card processor — hacked last year by the same criminal gang that infiltrated some of the world’s biggest data brokers.
As Smucker’s referenced in its FAQ about the breach, the malware that hit this company’s site behaves much like a banking Trojan does on PCs, except it’s designed to steal data from Web server applications.
PC Trojans like ZeuS, for example, siphon information using two major techniques: snarfing passwords stored in the browser, and conducting “form grabbing” — capturing any data entered into a form field in the browser before it can be encrypted in the Web session and sent to whatever site the victim is visiting.
The malware that tore into the Smucker’s site behaved similarly, ripping out form data submitted by visitors — including names, addresses, phone numbers, credit card numbers and card verification code — as customers were submitting the data during the online checkout process.
What’s interesting about this attack is that it drives home one important point about malware’s role in subverting secure connections: Whether resident on a Web server or on an end-user computer, if either endpoint is compromised, it’s ‘game over’ for the security of that Web session. With Zeus, it’s all about surveillance on the client side pre-encryption, whereas what the bad guys are doing with these Web site attacks involves sucking down customer data post- or pre-encryption (depending on whether the data was incoming or outgoing).
IN GOOD COMPANY
When a reader first directed my attention to the Smucker’s breach notice, I immediately recalled seeing the company’s name among a list of targets picked last year by a criminal hacking group that plundered sites running outdated, vulnerable versions of ColdFusion, a Web application platform made by Adobe Systems Inc.
According to multiple sources with knowledge of the attackers and their infrastructure, this is the very same gang responsible for an impressive spree of high-profile break-ins last year, including:
–An intrusion at Adobe in which the attackers stole credit card data, tens of millions of customer records, and source code for most of Adobe’s top selling software (ColdFusion, Adobe Reader/Acrobat/Photoshop);
-A break-in targeting data brokers LexisNexis, Dun & Bradstreet, and Kroll.
-A hack against the National White Collar Crime Center, a congressionally-funded non-profit organization that provides training, investigative support and research to agencies and entities involved in the prevention, investigation and prosecution of cybercrime.
TOO MANY VICTIMS
Not all of the above-mentioned victims involved the exploitation of ColdFusion vulnerabilities, but Smucker’s was included in a list of compromised online stores that I regrettably lost track of toward the end of 2013, amid a series of investigations involving breaches at much bigger victims.
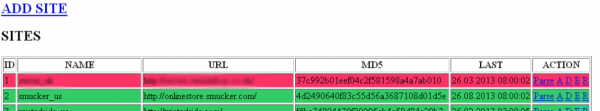
As I searched through my archive of various notes and the cached Web pages associated with these attackers, I located the Smucker’s reference near the top of a control panel for a ColdFusion botnet that the attackers had built and maintained throughout last year (and apparently into 2014, as Smucker’s said it only became aware of the breach in mid-February 2014).
The botnet control panel listed dozens of other e-commerce sites as actively infected. Incredibly, some of the shops that were listed as compromised in August 2013 are still apparently infected — as evidenced by the existence of publicly-accessible backdoors on the sites. KrebsOnSecurity notified the companies that own the Web sites listed in the botnet panel (snippets of which appear above and below, in red and green), but most of them have yet to respond.
Some of the victims here — such as onetime Australian online cash exchange technocash.com.au — are no longer in business. According to this botnet panel, Technocash was infected on or before Feb. 25, 2013 (the column second from the right indicates the date that the malware on the site was last updated).
It’s unclear whether the infection of Technocash’s secure portal (https://secure.technocash.com.au) contributed to its demise, but the company seems to have had trouble on multiple fronts. Technocash closed its doors in June 2013, after being named in successive U.S. Justice Department indictments targeting the online drug bazaar Silk Road and the now-defunct virtual currency Liberty Reserve.
SECUREPAY
One particularly interesting victim that was heavily represented in the botnet panel was SecurePay, a credit card processing company based in Alpharetta, Ga. Reached via phone, the company’s chief operating officer Tom Tesmer explained that his organization — Calpiancommerce.com — had in early 2013 acquired SecurePay’s assets from Pipeline Data, a now-defunct entity that had gone bankrupt.
At the time, the hardware and software that powered Pipeline’s business was running out of a data center in New York. Tesmer said that Pipeline’s servers had indeed been running an outdated version of ColdFusion, but that the company’s online operations had been completely rebuilt in CalpianCommerce’s Atlanta data center under the SecurePay banner as of October 2013.
Tesmer told me the company was unaware of any breach affecting SecurePay’s environment. “We’re not aware of compromised cards,” Tesmer said in an email. This struck me as odd, since the thieves had clearly marked much of the data they had stolen as “SecurePay” and listed the URL “https://www.securepay.com/” as the infected page.
Following our conversation, I sent Tesmer approximately 5,000 card transaction records that thieves had apparently stolen from SecurePay’s payment gateway and stashed on a server along with data from other victimized companies (data that was ultimately shared via third parties with the FBI last fall). The data on the attacker’s botnet panel indicated the thieves were still collecting card data from SecurePay’s gateway as late as Aug. 26, 2013.
Tesmer came back and confirmed that the card data was in fact stolen from customer transactions processed through its SecurePay payment gateway, and that SecurePay has now contacted its sponsoring bank about the incident. Further, Tesmer said the compromised transactions mapped back to a Web application firewall alert triggered last summer that the company forwarded to its data center — then located in New York.
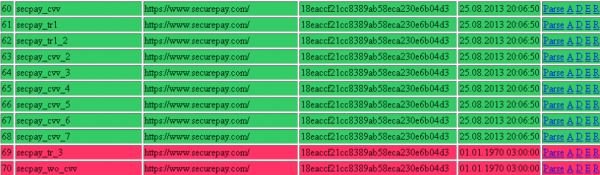
Several servers from credit card processing firm SecurePay were hacked by the ColdFusion botmasters.
“That warning showed up while the system was not under our control, but under the control of the folks up in New York,” Tesmer said. “We fired that alert over to the network guys up there and they said they were going to block that IP address, and that was the last we heard of that.”
Turns out, SecurePay also received a visit from the FBI in September, but alas that inquiry also apparently went nowhere.
“We did get a visit from the FBI last September, and they said they had found the name SecurePay on a list of sites that they were pursuing some big hacker team about,” Tesmer said. “I didn’t associate one with the other. We had the FBI come over and have a look at that database, and they suggested we make a version of our system and set that one aside for them and create a new system, which we did. They said they would get back in touch with us about their findings on the database. But we never heard from them again.”
Tomorrow, we’ll look at Part II of this story, which examines the impact that this botnet has had on several small businesses, as well as the important and costly lessons these companies learned from their intrusions.




email notify
Who buys jelly online? I guess hackers thought it was a sweet target…I hate seeing Smucker’s in a jam…. It sounds berry serious.
Sorry, I couldn’t resist.
Keep up the great work as always sir.
It appears you can also buy coffee, peanut butter, evaporated milk, and flour on that web site, and probably more. Who knew? I have actually bought flour online, I feel a bit odd admitting this. It was Bob’s Red Mill, primo overpriced organic.
Lol,
If they get caught, the hackers may find themselves in a pretty sticky situation!
You can say they’re toast. (*rimshot*)
Most of the hackers that are in it for the money jump all in. The “smart ones” hide any cash well, and if they have hundreds of thousands to millions of dollars, and the Feds only recoup 1/4 to maybe 1/2 of that, guess who walks out of court, or jail with a boatload of cash stashed some where ?
Sure not all crooks are smart, and the Feds are getting smarter about all of this. But it shouldn’t be this way in the first place. Software can be broken by other software, and it is only a matter of time. Strict guidelines should exist between the server network and computers that are internet facing. Relying on a piece of software called “antivirus” is foolish as it gives many a fall sense of security – but for many – its the only security they have. = /
The thieves made off with a bunch of broken jars of strawberry jam. The police hope to catch them red-handed.
Why isn’t the Falafel store crime more important? One’s a theft; the other’s hummucide.
(*rimshot*)
I find all this alarming that companies don’t pay close attention to security. In the beginning anybody would put up a site so you expected intrusions. These days such behavior is outrageous and those processing credit cards should be liable for any breaches with fines and public disclosure that they are not safe. Until there are consequences for sloppy work it will continue and jeopardize commerce.
I bet Tom Tesmer will become one more avid reader of krebsonsecurity.com. Would not want to be him at the next board meeting.
Nope, wouldn’t want to be him. There’s no way he can ‘preserve’ his job now.
Actually, I don’t think they care all that much. Am trying to help a client resolve numerous CC gateway auth issues with Securepay, and they seem utterly unconcerned. Their online / virtual terminal functionality was completely unusable on Monday, March 10th, and since then this client has had constant CC auth issues. Not impressed with SecurePay / Calpian whatsoever – but doesn’t surprise me that they’re nonchalant about protecting customer data.
Securepay ain’t that secure:
https://www.ssllabs.com/ssltest/analyze.html?d=https%3A%2F%2Fwww.securepay.com%2F+
(just a bad HTTPS rating)
Also:
https://onlinestore.smucker.com/message.cfm
“We greatly value the trust our consumers place in our Company and take very seriously our responsibility to protect sensitive and confidential information that consumers share with us.”
Well, you can start by dropping SSL 2!
https://www.ssllabs.com/ssltest/analyze.html?d=https%3A%2F%2Fonlinestore.smucker.com%2Fmessage.cfm
Smuckers? Now they’ve gone too far. When they hit me in my sweet tooth, they’ve gone too far.
You can’t fix stupid. A growing number of sites require signing up through facebook …of all things! Then one can ‘rest assured’ that all initial & subsequent information is in good hands -not!
That’s a deal breaker for me. Mainly because I refuse to sign up for Facebook.
If they used Raspberry Jam to jam up the site as the title entails then I know the cuplrit. Only one man in the universe would dare use raspberry…LoneStar!!!
now quit all this mucking around in the comments.
The crooks should have added a logo like
Schmuckers to the website. If security is lax, maybe the attention to detail would have not been there as well.
Did Smuckers preserves the evidence?
After the criminals are apprehended, do you think they will make a confection?
Funny comments today! Not funny the situation. This pre- and post-transactions, pre-encryption hacking is not new for sure. IBM Security Systems did a white paper on it years ago. (Don’t ask me where). At that time, big retailers and banks were the primary concern, but the cloud has made this an equal-opportunity scourge, kind of like the Black Death.
Recently, one security company reported what they called a “god-zilla sized” cache of personal data being sold on the black market, http://bit.ly/1n8POjf. Grandma data, as some here call it. They didn’t know where it came from but likely a collection of smaller breaches, like the Smucker-y one covered here. (Sorry for one more pun, Brian).
“Australian online cash exchange technocash.com.au”
Shouldn’t that be “technocrash”?
And given the likely country of origin of the culprits for the Smuckers affair and what that country is doing in Europe right now, do you think Smuckers management is saying “Crimea river”?
Best comments in awhile. So much new information on the crappy state of our credit card safety. A little levity is a nice change.
Krebs: Hi, uh, my name is BrianKrebs, and it looks like your web site has been hacked.
Admin: Uh, nope, uh, we looked at everything, and, uh, everything is hunkey dorey.
Krebs: Well, uh, have you taken a look at this?
Admin: Uh……..
You might have also included in the Admin’s final response:
Aw, [expletive deleted]!
OK, so we see some entries going to some IP. Let’s call New York.
New York promises to block the IP. Talking about solving the root-cause …
Also no need to follow up. We didn’t hear from them, so we’re good, right?
So seems both HQ and New York datacenter didn’t really care about the issue.
Another interesting article, B.K. is real “jamming” this website with good articles as of late
They thought about stealing some peanut butter, but they realized that would stir things up too much. They might end up left in the cold.
You missed the Smucker’s entry in the Coldfusion botnet panel because it was …. (wait for it)
… sandwiched between the others.
I am sure the crooks tried a site as a test guinea pig. It looks like they all may have had a common break in point, and the crooks test it on a lower level “target” and when its tried and works, they can then smack the bigger fish on the first attempt.
…or, it was just spread too thinly.
Hey people, this isn’t funny. This is serious business and these criminals are going to get caught. They all make the same mistake. First they jam things up then they spread it out to thin…..And what about poor Tom Tesmer? He thought he was all over his job like jelly on toast but Brian made him wake up and smell the coffee.
Jam…smucker’s….good one
Makes wonder what percentage of online sites are compromised?
And since you don’t know which ones are compromised, should you even be buying anything online?
The previous breaches reported here were not online purchases, ie., Target, possibly Sears, Neiman Marcus, etc.
Someone above showed us the ssllabs.com results for various sites. I would definitely run a site’s url through that tester, or another similar one if you know of one, before signing on to anything new.
I’m beginning to think 50%+ are compromised. Or at least that’s what I’m going to assume. My reaction: I scrutinize my credit card activity more than ever before. I assume now that my data has been stolen and my only task is to catch it as quickly as possible. I feel like I’m being hunted by some invisible predator. Now I know how small animals feel. 🙂 (Kind of.)
Thanks Brian, your site is the first i check for when opening my email……
Just love computer-related nerd humor/. love it
So who put the jam in their jelly roll?
With a name like Smucker’s, it HAS to be hacked..
http://s2.quickmeme.com/img/89/896b055bcfc03c91309265052d749a7e4ef72db4e04038ee7b9a8182fcc35a08.jpg
Hi! I realize this is kind of off-topic but I needed to ask.
Does building a well-established website like yours take a lot
of work? I am completely new to blogging however I do write
in my diary on a daily basis. I’d like to start a blog so I can share my own experience and feelings online.
Please let me know if you have any kind of ideas or tips for brand new aspiring bloggers.
Thankyou!