An article in The Wall Street Journal this week quoted executives from antivirus pioneer Symantec uttering words that would have been industry heresy a few years ago, declaring antivirus software “dead” and stating that the company is focusing on developing technologies that attack online threats from a different angle.
This hardly comes as news for anyone in the security industry who’s been paying attention over the past few years, but I’m writing about it because this is a great example of how the cybercrime underground responds to — and in some cases surpasses — innovations put in place by the good guys.
About 15 years ago, when the antivirus industry was quite young, there were far fewer competitors in the anti-malware space. Most antivirus firms at the time had a couple of guys in the lab whose job it was to dissect, poke and prod at the new crimeware specimens. After that, they’d typically write reports about the new threats, and then ship “detection signatures” that would ostensibly protect customers that hadn’t already been compromised by the new nasties.
This seemed to work for while, until the smart guys in the industry started noticing that the volume of malicious software being released on the Internet each year was growing at fairly steady clip. Many of the industry’s leaders decided that if they didn’t invest heavily in technologies and approaches that could help automate the detection and classification of new malware threats, that they were going to lose this digital arms race.
So that’s exactly what these firms did: They went on a buying spree and purchased companies and technologies left and right, all in a bid to build this quasi-artificial intelligence they called “heuristic detection.” And for a while after that, the threat from the daily glut of malware seemed to be coming under control.
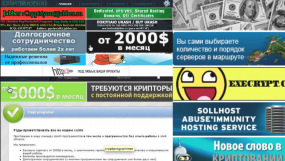
But the bad guys didn’t exactly take this innovation laying down; rather, they responded with their own innovations. What they came up with is known as the “crypting” service, a service that has spawned an entire industry that I would argue is one of the most bustling and lucrative in the cybercrime underground today.
Put simply, a crypting service takes a bad guy’s piece of malware and scans it against all of the available antivirus tools on the market today — to see how many of them detect the code as malicious. The service then runs some custom encryption routines to obfuscate the malware so that it hardly resembles the piece of code that was detected as bad by most of the tools out there. And it repeats this scanning and crypting process in an iterative fashion until the malware is found to be completely undetectable by all of the antivirus tools on the market.
Incidentally, the bad guys call this state “fully un-detectable,” or “FUD” for short, an acronym that I’ve always found ironic and amusing given the rampant FUD (more commonly known in the security industry as “fear, uncertainty and doubt”) churned out by so many security firms about the sophistication of the threats today.
In some of the most sophisticated operations, this crypting process happens an entirely automated fashion (the Styx-Crypt exploit kit is a great example of this): The bad guy has a malware distribution server or servers, and he signs up with a crypting service. The crypting service has an automated bot that at some interval determined by the customer grabs the code from the customer’s malware distribution server and then does its thing on it. After the malware is declared FUD by the crypting service, the bot deposits the fully crypted malware back on the bad guy’s distribution server, and then sends an instant message to the customer stating that the malware is ready for prime time.
Crypting services are the primary reason that if you or someone within your organization is unfortunate enough to have opened a malware-laced attachment in an email in the first 12-24 hours after the bad guys blast it out in a spam run, there is an excellent chance that whatever antivirus tool you or your company relies upon will not detect this specimen as malicious.
In short, as I’ve noted time and again, if you are counting on your antivirus to save you or your co-workers from the latest threats, you may be in for a rude awakening down the road.
Does this mean antivirus software is completely useless? Not at all. Very often, your antivirus product will detect a new variant as something akin to a threat it has seen in the past. Perhaps the bad guys targeting you or your organization in this case didn’t use a crypting service, or maybe that service wasn’t any good to begin with.
In either case, antivirus remains a useful — if somewhat antiquated and ineffective — approach to security. Security is all about layers, and not depending on any one technology or approach to detect or save you from the latest threats. The most important layer in that security defense? You! Most threats succeed because they take advantage of human weaknesses (laziness, apathy, ignorance, etc.), and less because of their sophistication. So, take a few minutes to browse Krebs’s 3 Rules for Online Safety, and my Tools for a Safer PC primer.
Oh, and check out the Wall Street Journal piece that prompted this rant, here.




I fully agree that AV remains a useful tool that the average user definitely needs. In fact, the average user should have at least one top-rated AV, a more specific antimalware utility such as Malwarebytes Antimalware, and maybe even a second one such as Superantispyware – either on-demand or running in the background depending on what system load the user wants to tolerate.
I don’t think a lot of the additional functionality most AV comes with today is all that necessary if the end user does not use Internet Explorer as their browser and installs AdBlock and NoScript or an equivalent in their browser.
But it’s absolutely true that the main defense is a knowledgeable user – which unfortunately lets out about ninety five percent of PC users…
I also think all these “smart guys” who claim they have never used an AV and have never been infected are just anecdotal, i.e., worthless, evidence for that approach.
Of course, I run Linux, so malware is the least of my worries. 🙂 As long as Linux remains at around a one percent market share, it will be decades before malware is a problem for it due to the simple economic fact that there’s no profit in Linux users.
The same thing used to be true for Apple’s OS users.
Of course that is not true whatsoever and is really a laughable statment only made by people who are ignorant of Macs and OS X. Tell us all abut the viruses, and ohter malware actually out in the wild on OS X that are not prevented from doing anything by the built in malware scanner. Pretty much none versus thosuands for Windows.
I read Lisa’s comment (which was somewhat ambiguous, unfortunately) as saying that Mac users, like Linux users, don’t have to worry so much about malware. I think you misunderstood.
Also Mac users are a higher demographic than any other type of users and therefore a very desirable target. Not to mention the prestige of being able to hack OS X which very few have succeeded in doing and they have been shut out almost immediately.
As to Linux it runs a very high proprotion of the worlds corprate servers and is a veryd esirable target for that reason.
You guys are really going to have to try harder to defend the indefensible openess of Windows to every type of malware.
Windows machines are generally used for business – Macs are what the kids use to play candy crush.
I kid, but only a little.
HA! – I was also going to say that no matter how good the system is, the user is the weak link, and only too willing to click on anything that pops up.
I’ve found Mac users to be just as gullible as Windows users. I’m sure I’d find Android users to be similar, or at least in the ballpark with their propensity to experiment with too many apps..
Mass malware does not appear to be a threat to the conventional GNU/Linux desktop anytime soon (aside from email-based phishing which is pretty much OS-independent). Targeted attacks and, especially, advanced persistent threats are an entirely different matter.
I strongly suspect that the default security settings associated with most conventional GNU/Linux distros would be ‘friendly’ towards targeted attacks and advanced persistent threats.
P.S. Google’s Chrome OS, used in Chromebooks and Chromeboxes, is built from Gentoo Linux sources and is hardened substantially relative to conventional GNU/Linux distros. Still, it was defeated in the 2014 Pwnium challenge an CanSecWest.
Sorry Richard – but there are lots of linux based malware. Linux may only have 1% of the desktop market – but it has a big % of the server market – and this makes it not only a target of opportunity, but a powerful distribution point for malware.
minor nitpick: heuristics are neither quasi-AI (though perhaps as difficult to explain) nor as young as 15 years old (they’ve actually been around in the anti-malware domain for over 20 years).
Sorry, but AV was invented over 30 tears ago and has been dead for over 15 years. Get with the program.
This explains how our PCs were infected by crypto locker. Thanks for this explaintion Krebs.
AV is not dead, the communication with AVs and individual security researchers like Krebs is not good. But researchers don’t have the infra that AVs have. So they can’t publish the research/detection/heuristic to a lot of people. Only the people who listen to them are better protected.
If there is a good cooperation between researchers/reporters/ex-cyber crooks/av, then we get better protection.
This is only my view.
Siva
I think that if AV companies continue to make small improvements and invest in reliable high-tech solutions, they will eventually get to the point where only well-funded, well-organized, well-staffed organizations will be able to continue in the malware business. This would mean only nation states or super croooks.
Of course, I could be wrong and the AV/malware struggle is a perfect example of asymetric warefare! Anyway, I think we still have a long journey to go before we see how this plays out.
Regards,
Hi Brian,
The last paragraph says it all: security in layers. I wrote a similar piece about the case for whether outbound firewalls are still worth anything: http://packetinspection.blogspot.com/2013/10/outbound-firewalls-prevention-is-cure.html.
Your suggested method of prevention is much better; user awareness is the best medicine!
Regards,
Matt
Right, they can crypt it. But then it’s just a matter of tracking down the distribution points, the sites or email addresses, that pump it out. I’ve found that many malicious sites change their virus.exe (by crypting or even multiple variants of different malware) but don’t actually change the site its hosted on. And also the IPs/domains of where the malware calls home don’t seem to change either. Basically, they can keep crypting it, but its harder to change other stuff.
AVs are far from dead- no human being can substitute the automation of what they can do. They mindset of “I have an AV, nothing can ever get me!” was never warranted though.
I wouldn’t say the AV industry was “very young” 15 years ago, considering that I was a development engineer on Symantec’s Norton AntiVirus for MS-DOS 23 years ago. I saw Symantec’s infamous 1992 “Michelangelo” fear-marketing campaign from the inside, since I had written Symantec’s original analysis of that virus (though I did not name it; once we had our analysis, we realized it was the same virus that McAfee had already named “Michelangelo”). I think of that as the moment when the AV industry left its youth, and perhaps its innocence, behind. From then on, it was all about scaring the public into spending money on eternally-outdated defenses. I left Symantec/Norton in 1993 with a strong determination to never again work on an AV product. Since then I have very rarely used AV except when required by my employers; I find that, as with STDs, you can avoid computer viruses pretty well just by avoiding risky behaviors.
Pretty well, perhaps, but not entirely. On one occasion when I was browsing intel.com, my PC got infected after I clicked on a link to a third-party website.
Uh, just out of curiosity, where’d my comment go?
Fascinating write up. Very informative indeed.
Just great – another problem we need to hear about with NO solutions. How ’bout some suggestions that contain -useable- solutions folks… not the pie-in-the-sky things we hear from marketing. Some real-world workable solutions would be nice… any takers?
.
the operating software should not be susceptible to modification by an application program — whether by error or by intent. this is where you need to look for the answer to this problem. ….a problem that isn’t going away.
“the operating software should not be susceptible to modification by an application program — whether by error or by intent.”
so you want an OS that can’t be patched? can’t be fixed when a security vulnerability is found in it? somehow i don’t think that’s going to turn out well.
I agree it shouldn’t be able to be modified, but if you look at the last 15 years in particular most programs are bent on profit motive aka advertising and proprietary action instead of transparent and secure design, including Windows. Programs need updates, the OS needs updates, programs often toss a few hundred registry keys all over the place to hook in as deep as they can, which means limited rights -> admin rights are never really fully separate things. Programs aren’t designed to be modular and confined, even Windows 8 and 9 sadly appear to be hell bent on including Metro against everyone’s will. Linux is much closer but still you can only do so much and still pull down updates and run applications without drastically redesigning how things happen, and even then it is all defeated by a simple phishing website or popup that asks for admin credentials.
Yes, why were Microsoft and Apple unable to keep this old mainframe feature?
I believe the key here is the Intel processors. I’m blowing smoke, but I think you will find that PowerPC processors and earlier mainframe processors had bits that could be set for each memory page to mark it execution only (no modification allowed) or for system privileges, for example. Intel took the easy way out and omitted this unnecessary stuff (just like they made parity optional on memory).
Yes, you are blowing smoke. You don’t seem to be very familiar with Intel’s processors.
Proof you know nothing about Apple operating systems either computer or mobile.
Well, since you asked. StealthWatch as one of the layers but Brian is right, the human aspect is the most important. I used to work at a wireless defense company and saw many Fortune 100 companies ignore alarms. If the company ignores alarms, what’s the point of having security?
“Just great – another problem we need to hear about with NO solutions. How ’bout some suggestions that contain -useable- solutions folks… not the pie-in-the-sky things we hear from marketing. Some real-world workable solutions would be nice… any takers?”
My usual suggestion is application whitelisting combined with low-rights user accounts. Those two steps are also among the top 4 “essentials” in the top 35 mitigations discussed here:
http://www.asd.gov.au/infosec/top35mitigationstrategies.htm
(Australian government site)
On a Windows platform, the watered-down “Family Safety” version, which applies only to .EXE files, is within the reach of many home users. The full-strength versions, of which I favor Software Restriction Policy, are within the reach of computer geeks, although they may have to iron out some glitches (et tu, Netflix?).
Anyway, a true game-changer against malware that executes from the file system.
AV is a general and necessary component of endpoint protection which is one part of a total Defense in Depth strategy which begins with education of people, aligned to process, supplemented with technology. It’s not about being breached anymore and the magic pixy dust of AV protecting you from the bad ogre. You will be breached, the challenge is how soon you know and your incident response plan to close the hole and understand the damage and prevent the incident from reoccurring. ” The attackers need to be right once, the defenders need to be right every time!” Endpoint Protection products contain AV, which is still one tool in the security utility pouch to leverage. Indeed vanilla AV has been dead for awhile, endpoint protection is alive and well.
Perfectly stated Shonan…well done.
Yes, this comment is a nice wrap up of how operations are currently handling malware.
The weight of the layers is becoming a real burden. Right now, we’ve got a bunch of solutions to buy, configure, maintain, and respond to: End-point-protection, anti-malware, anti-virus, firewalls, IDS/IPS, DLP, SIEM, WAF, Vulnerability scanners, PKI, and more.
Sometimes it is overwhelming.
it’s certainly going to be overwhelming if you’re double-counting things. anti-malware and anti-virus are the same thing. the words may be different but there is no AV out there that deals exclusively with viruses – they are all anti-malware now.
then there’s endpoint protection, which is typically anti-malware plus other goodies like firewalls.
don’t make a buzzword checklist and try to check every box. figure out what you actually need and just get that.
All AV is anti-malware but for defense-in-depth I could have anti-malware solutions that are not AV. Application white-listing, execution controls like EMET and application controls to resist mobile code are all anti-malware solutions. On some devices or operating systems it may make sense to not install AV but to take advantage of the others for an anti-malware solution.
this, i think, goes to one of my pet peeves.
AV != scanner. the first AV was not a signature scanner, it was a behaviour blocker.
AV is an umbrella term that covers a wide range of technologies that stop viruses, including things like whitelisting (a rudimentary form of whitelisting existed in thunderbyte anti-virus in the early 90’s).
as umbrella terms go, anti-virus really should be considered obsolete and replaced by anti-malware since there are no pure anti-virus products anymore, but people just can’t seem to let go of AV.
+1
Curious why no one’s gone after, or if they have why there’s no mention of it, the crypting services. The way I read it, they are the big reason viruses are so successful.
you can’t leave out the inherent vulnerabilities of the Windows operating system while having an honest discussion about security
Symantec said this because of their dead revenue. But if their AV is the first choice of many end-users, I doubt if they will say this.
The only thing I wish to be ‘dead’ is the phrase, ‘____ is dead.’ I have grown tired of reading articles from the alleged experts about how a technology is dead – only to read another article (often on the same site) attempting to explain how that same technology isn’t dead.
Let’s face it, Mainframes, PCs, AntiVirus, and the like are not dead. Their popularity and role within the computing industry has shifted but, trust me, they are not dead.
Hi Chris,
I agree with the spirit of your comment. Instead of labeling things such as AV as “dead,” we should refer to them as commodities. When an item becomes a commodity, the best economic choice from the buyer’s perspective is the cheapest purchase.
Regards,
Matt
Words spoken straight from my experience. It’s the best argument for effective security awareness training as part of the defense-in-depth approach.
Hi Kreb,
The article is nice but it is totally contextual to certain aspects of AV technology(pattern signature). For example FUD uses scanner of all the AV which will in turn uses file pattern signatures and heuristics but their are other technologies like
**emulator: all the FUD are already crypting well known malware code(which AV company already know) which were designed earlier. So if a good av emulates it and detect at bottom level code and can protect the user.
**Behavior monitor: Their will be common behaviors that malware will show while its running which FUD cant change or detect . For example particular reg entry or file name writing in a specific windows location
**sandbox: Some AV av even have running any unknown new files in the sandbox and then only tries to run it real machine(but has performance issue).
in these days of high end computing at least some percentage system resources should be given to AV.
The real outbreak happens when malware tries to evade these technologies by gaining privilege of permission(zero day) and infect the machine.
FUD is just another business where to infect users who doesn’t use the full suite Security sw or unpatched machines.
I have tested new malware which are not detected by any one of the AV in VT, but when i try to execute them in the user machine with full AV suite ON ,some how the user is protected.
But very sad aspect of this article is Symantec is saying like this.. i dont know if this new trend of marketing
One more thing this comment doesnot mean every time AV suite will detect. In fact nothing is 100% right, other than living in present…
IbusR
In recent years, Symantec has significantly relied upon acquisition to improve its AV/security products, and in the process, it failed to choose the proper acquisition targets. Consequently, it failed to properly monetize their security products. Perhaps that is why it now says AV is dead!
Also, the AV industry needs for business management to realize the importance of security and support it with sufficient resources, employee training, and implement proper security systems for the environment in which they operate.
It seems to me that almost every “sophisticated” attack I hear about has been aided or abetted by one or more untrained, unconcerned, or greedy employees. Someone has to click on that malicious link, execute that malicious file, or realize the importance of that entry in a security log.
Perhaps AV would not be so dead if management and employees
played their proper role in the security process instead of relying almost entire on their AV product.
People need to realize that security is just as important as paychecks and bonuses!
Regards,
I agree Bob. If you read the WSJ article and check Virus Bulletin or AV Comparatives testing, you can see the effectiveness of AV is on a steep decline, some tests showing as low as 45%.
Security Awareness training should be mandatory, not just for compliance, and employees held accountable for their efforts good or bad.
As a counterpoint, consider watering-hole attacks. The attacker compromises a legit site that their intended victim would be likely to visit. We all have sites that cater to our interests. For you it might be guitars, for me it might be bicycles.
Or there’s the more mundane version of that scenario: malvertising. If your employee is exposed to a malicious ad on, let’s say, Yahoo’s news page, you can’t really blame them (assuming that’s OK by your policies).
I agree that reliance on antivirus is fraught with hazards for the general populace.
I’ve noticed Symantec has a bad habit of just buying something because it is free for the users, so they can take it off the market – even if it was a relatively good product! I don’t have good feelings about them because of this. I only have one client using it anymore anyway.
If they would have developed some of those utilities, or even used them as a tag to attract customers to their paid products, I think they would have been miles ahead. MBAM started out free with a choice for the lifetime license – look how successful they’ve become!
The free version of MBAM (that’s Malwarebytes Anti-Malware, for those who don’t know) gets updates for life. What the paid versions* have is the ability to actively monitor for malware, instead of just scanning your PC for infections after the fact. However, PCMag.com’s reviewer found the active monitoring not so great and recommends using the free version as a second line of defense, behind other anti-malware software.
*The paid version of Anti-Malware 1.x was called Anti-Malware Pro and came with a license that was good for life. The paid version of Anti-Malware 2.y is called Anti-Malware Premium and comes with a one-year license. Fortunately, users of Pro can upgrade to Premium at no charge and use it for life. (If I’m not mistaken, it can even be transferred from one PC to another.) Furthermore, Malwarebytes was, and may still be offering, license keys for Premium that are good for life for just a one-time purchase (as was the case with Pro) in a secret sale. Check Malwarebytes’s twitter for the link.
The email I got from the company said the name would change to MBAP just like you said, but that they are going to the annual payment model because of development and maintenance expenses. So there is no Pro version for now, just the Premium. They did also say that they might have lifetime licenses as a promotion in the future, but previous version would be honored, unless they are OEM. So yes, the older retail lifetime license versions were completely transferable. I made the mistake of buying some OEM disks, and discovered they were not transferable to a new machine; but at least they were good for the ‘lifetime’ of that machine! 🙂
Hi, Brian,
I’d also mention “bundling” where hackers would get few known malwares and bundle them together escentially producing a new variant of malware that might evade AV scanners.
Keep up the great work!
Last night I had AVG detect malware on a Facebook video of a man on a boat being eaten by a shark ( okay I just had to see it). The antivirus detected it immediately, and stopped the loading of the website. I don’t think Antivirus programs are dead but rather think it’s a question of teaching people not to click on questionable links to stop the spread of this junk from affecting other internet users.
I disagree, if only for things like boredom and slow loading pages people will move the mouse around or click things that take too long right as the page loads – I think the only real way to lessen this risk is making is so their clicking or not doesn’t have a way to pull down the malware, popups, ads, scripts, etc.. If it CAN happen it WILL happen given enough time and opportunities.
It’s peaking a person interest towards something that’s absurd or never seen before through the use of social engineering. I knew not to click on it, something in my head told me not to do it , but I went ahead and did it anyway knowing that the link looked highly suspicious ( ending in a .pw TLD)
My antivirus caught the crap (Facebook Exploit) right away, luckily for me. A lot of people just don’t care and won’t use any antivirus at all , which then becomes the problem . The persons online bad behavior will rule out the “if it sounds to good to be true” type of human logic.
If you are aware enough about clicking on odd looking hyperlinks in say Facebook then the opportunities for infection won’t come up that often or even at all.
I don’t agree, antivirus programs are dead , but think that they need to evolve a lot more to catch up the cyber-criminals more advanced. abilities In my opinion the antivirus program should be installed at the hardware firewall along with intrusion detection not on the computer itself .
Technology just adds more ways and chances for it to happen as well. Pretty easy to spoof some mistress or girlfriend email + photos, you might know to not click but what is your wife going to look for the second you leave your email logged in? Or what about if you get a text on your phone while you’re in the can from ‘your lady’ and the wife clicks the link? Plenty easy to spoof inter department emails about expenses or benefit issues or other things too.
“I knew not to click on it, something in my head told me not to do it , but I went ahead and did it anyway knowing that the link looked highly suspicious ( ending in a .pw TLD)”
*snort* (puts on overcoat and does a flash: hey buddy, i have some sweeeet links for ya) wink-wink
Plus how many kids have smartphones today that didn’t a generation ago and will click on anything that shows up?
I think one of the reasons INTEL bought out McAfee was to develop a new way a CPU can thwart potentially unwanted software, and probably protect the kernel and all parts important.
Only time will tell if the AV and Chip combo will produce anything significant.
For an AV vendor to state that their software is dead, should have been stated AFTER signifcant research has been vested in a new technology. What that rant tells me is that their product is inferior, and any subscriptions that they sell are pretty much worthless when it comes to the newest type of malware that is out there.
When I worked at another location, I’d see a malware technology come into the network that were a series of .TMP files, and eventually these files would manifest itself into some really bad stuff. We monitored the boxes, watched the file sizes and shortly after birth, saw AV and other components defeated and we yanked the hard drive and destroyed it, wrote our documentation and blocked the IP ranges the evil stuff came from.
Now its not necessarily more complex, just a different avenue of attacks. The miscreants use tried-and-true techniques that people STILL fall for. All it takes is one box on the network to fail and when it does, it can become a harvester, scanner or other bot related function that the dark side wants to control. Unless people clean up the filth thats around them now – no matter the newer way of doing business – the malware that could be on the boxes may thwart any sort of new AV software the same way.
The new AV software can be broken by other software, and all it takes is one config file to be changed and the new, polished AV software is just as useless, under control of the malware that already resides on the box.
Its not a secret that a new technology is out there, the dark side reads about the potential technology. If there are BETA testers out there, and one of the boxes that is a BETA tester is infected with an advanced threat, then that new software potentially could already be in the hands of the dark side and easily defeated before it is even launched.
Time will tell if the way of doing “AV” will work, or its a trendy, new shiny box that isn’t much better than its legacy product.
It seems the security utility industry was working closer to the kernel space every year, and I’m sure your right about Intel – they probably want a firmware anti-malware solution baked into their chips – preferably nothing that can be flashed. With something like that, they could take a novel new approach and ignore the malware altogether, by making end runs around them and running in an infected environment without losing function or security in the process. Some of the newer kernel space solution are attempting this already.
I really wonder why a lot of businesses haven’t gravitated toward some thing like the old Microsoft Steady State, where the underlying operating environment cannot stay modified for long.
It is /was called aggrevated money collection and wreckless speed, over a secure environment.
When a company sees a niche, they tend to use it until they feel they are losing money. If an AV corporation says AV is dead, they are more than likely speaking past tense. They have people in the trenches fighting the losing battles to see a more sophisticated enemy and software than they have. To blurt out that statement shows no confidence in the current products they create and keeping up or thwarting the threats is futile. BUT, they will continue to offer the services for a charge, and keep feeding people a subscription of false hope and security by obscurity.
They are lazy. Too comfortable in the security field and unwilling to get off their behinds and try to overcome a seemingly overwhelming condition. Bah, all it takes is a few bright security engineers sitting around and growing a thinkpot, vice a gloom and doom stink-pot.
Go back to the days of the conseal firewall which used to alert people on every change to a firewall rule or inbound connection. The stuff that resides in the USA is garbage, it’s all a money making scheme to keep people content and saying, BUT! I have Antivirus. Its an old technology that has been dissected and sewn back together many times and using that old way of doing business seems to keep the quaint content – until the company spouts off that the software is flawed and useless.
Its simple. ALL outbound connections should be approved by the user. There are many out there that will blindly click Ok, Ok, Ok, and its on them to clean up their mess once again.
The only way this malware sewage is going to get off the planet is IF a software company can make strides against the malware, offer a Free 6 month subscription for those who wish to run a scanner and clean their machines. People like free, and its a win-win situation. BUT the money hungry corps out there aren’t in it for the true meaning of security. They are in it for the money. Thus, you get what we had the other day – a Corporation that works in security saying that their product is basically useless.
I agree, and it has been my experience that freeware companies that offer basic serviced for free, but have an upgrade path to an actually improved product, have been accepted by my clients. They see how well the utility works and they are willing to donate, or buy the upgrade. The smart companies have kept that fee low, because they can make plenty of money if the adoption rate is high. Sheese, if 100 million people buy a 1 dollar utility – well you get what I mean.
There are actually some companies out there that are showing some innovation. The only ones I haven’t fully investigated yet are the cloud based solutions. I’ve used Prevx, and it made a good reactionary partner to whatever AV was already on the machine, but I never used it to actually remove the threat – I didn’t have to – all I had to do is run a file cleaner, and voila, the threat was gone from the temp/app-data files. When you run as a limited rights user, you can do a lot to foil anything that runs with user rights.
The Windows 64 bit NT6 kernel has been working well enough for me that I’d almost swear all you need is a good HIPS and a file cleaner to rid yourself of almost all threats but the APTs. After that the kernel space solutions pick up the slack. Tomorrow all bets could be off – anyway, here lately keeping up with application and operating system updates is actually more important now than worrying about AV/AM. Again tomorrow may change it all. I spend all my spare time trying to keep up with the threatscape with my honeypot, and I find the work fascinating. This is a good thing because, I should be bald from tearing out my hair by now! 🙂
Multi-layered approach is best, nothing beats having more than one vendor providing protection on a network.
Some of the best Malware solution software out there is from over seas, hands down.
Dabbling in security, or relying on a single vendor across the board and putting all your eggs in one basket isn’t the best solution. I won’t describe my environment to anyone, thus it takes the attackers quite a while just to figure out whats there, vice reading it in a post. Miscreants will do their homework and in the end, it makes their life a little easier when it comes to attempts to punch a hole in your network.
Port 80 is almost always wide open. It doesn’t take much for a miscreant to get into a network. The last line of defense in most cases is going to be whats protecting that device.
The kernel isn’t the problem in most cases. APT’s can poison the prefetch and it becomes an ugly scenario. If people surf with admin rights, any software that climbs into the box will have admin rights and thus be allowed to install unless a “known” threat is thwarted by anti-malware / anti-virus. All the unknown threat has to do is install itself, whether it needs admin install or not, and continue beating on the device until it achieves victory.
People tend to have that false sense of security for one APT, but another threat may use a totally different tactic. Its an ever-evolving threat and sometimes can be determined by the evil software.
There is much that is not known about the capabilities of the evil software, and usually its too late once its on the box. People don’t care, or, have the time to dig through logs and see whats ticking on their devices. The logs are cryptic and buried, and if the software pwns the box, the log entries for that APT my not even be logged.
If it isn’t port 80, then its going to be an encrypted channel that does the dirty work. Most people do not have a device to unencrypt, inspect, and then re-encrypt the data to check to see if it is malicious.
So prevention and protection up front is paramount. Security is not just the use of software, but good surfing strategies, and jumping through hoops to make security work. Its a very long story and open to debate, but the best security practices – most which are user based are typically free. People just want ease of use over security and the human being is prone to making mistakes, one inadvertent click and they pwn you.
Due care, due dilligence and the prudent man rule may need some adaptation to the new way malware is evolving, but keeping thy guard up 24/7/365 is the best defense.
Getting the users to accept limited rights can be challenging in both enterprise and home environments, that is for sure! That can go a long way toward the ultimate goal of better practices. That darn startup folder can be a corker too, when dealing with Zeus variants.
Also speaking of ports, it seems one of the most effective tools the better anti-malware use now it simply blocking outbound communications to known bad IPs or domains. When those pop up, you know you have a miscreant in your midst! I would think the list of those sites would be easier to keep up with than signatures any day; although with IP v 6 out now, and the domain naming system expanding, that won’t last long. For such a simple tool – Web of Trust does a pretty good job of avoiding accidental stumbling onto sites that one might want to avoid – of course it is reputation based, but it can’t hurt in a blended defense. Comodo’s DNS service come to mind as well. All of which can be subverted if the user doesn’t maintain awareness of what is going on, and what is aberrant behavior.
AV should be finally recognized as dead as the “solution” to malware, it has been part of the solution for defense-in-depth for quite some time but security professionals need to recognize the limits of AV. It should not be treated as a requirement for all use cases.
Like all applications AV takes resources, it adds complexity and expands the attack surface. For Windows based end user devices that browse the web and read email AV in most cases has more of a value add than downsides. Many security professionals take that use case and expand it to the world of mobile devices, servers, special purpose devices with different use cases, and other Operating Systems. “A real computer must have AV and a firewall…”
The focus should change in reducing the risk of a computing device of not executing untrusted code (Use access controls to reduce the attack surface, don’t read email or browse the web on specialized devices), reducing the capability of untrusted applications to run (Whitelisting), reduce the number of installed applications that are frequently attacked (you need Java and Flash in IE for what?), use software that has fewer exploits developed against it.
“AV should be finally recognized as dead as the “solution” to malware”
i would go further and say that the concept of a “solution” to the malware problem should be considered dead.
to say that one has solved the malware problem suggests that people can just use the solution and not think about the problem anymore. that’s something that’s not ever going to happen, so we really need to stop chasing after “solutions”.
Maybe “solution” was the wrong word. I agree completely with you kurt that there is no solution to the malware problem. I guess I should have said that AV should no longer be considered the default response to the malware problem.
i’m glad you’re aware that there is no actual solution to the malware problem.
unfortunately many other people aren’t aware of that, or if they are aware of it on a rational level, they still frequently operate on an emotional level that hasn’t accepted that yet.
i wish i knew how to get people to forget about “solutions”.
Hi Kurt,
I agree with you. There is no single resolution, because security is a moving target. It’s all best effort!
Regards,
Matt
My guess is that he (Brian Dye) understands there is more money to be made developing\providing DLP solutions. When it’s all said and done, there are only so many ways for data to enter and exit a network, that’s not saying providing DLP is easy, but it could be “easier” if organizations would wake up and develop\enforce stronger security policies and stop making excuses why they can’t. Besides, malware research and keeping AV patterns and software up to date is expensive.
I personally think the biggest threat, (removing the user) is software development and poor testing and QA prior to going to market. Developers still don’t get it and in most cases they’re not developing applications with security in mind… because we all know that you can always put some third-party “thing” on, in front or around an app or system to protect it, the same with an OS.
I don’t think AV is dead, I think Symantec is ready to move into more profitable areas.
DLP was part of symantec’s efforts to reinvent themselves back in 2006. it was part of their “security 2.0” campaign.
if there was more money to be made with DLP, don’t you think they’d already be making it?
…it’s too bad that you’d rather make bland comments than try to understand what the words are saying. I said Symantec can make more money in the DLP space while saving money that would otherwise go toward AV research and the business of AV.
the point is they already have DLP and they’ve already been marketing DLP, so they shouldn’t have to change what they’re doing if DLP was serving their interests.
Whatever, kurt… you’re right as always, at least judging from your comments you think you are … but hey, you have a great day!
🙂
Once again, thanks Brian.
With the built-in curiosity we all have, the ‘bad guys/girls’ will always have a way to tease/tempt us by using some type of ‘OMG’ thing, or to put it another way – click this- kind of thing that gives them (bad guys/girls) access into places.. and with all the folks feeling the need to be constantly connected, that just opens more possibilities.
Thus, the primary point of Brian’s website, Stu’s training stuff, and several other “good folks” sites.. train the USER. (No, you do NOT need more smileys; no, FedEx/UPS does NOT have a package for you at the post office; no, you do NOT have a bazillion dollars waiting for you once you send all your info; etc.)
And now it comes down to each of us.. the one’s who train, the one’s who are the ‘go-to’ folks when our “people” get in trouble (HELLLLLLLLP!!!!!).
Pass along GOOD security practices.
Those only go so far, there isn’t really an oopsie button, within 5 minutes of clicking the link there is no telling what backdoors, new users, keyloggers, or anything else that could have gotten dumped already. While anti-virus has long been viewed as the fix all, I just don’t see how every version is going to know how to fix all the myriad registry, path, user, file settings that got messed up… The real answer is they usually don’t and the system will become far less stable with even one event. While training is important, at some point it is a better use of resources to filter the contacts so outsiders never have them, filter everything on the way in, and filter on the way out so they never even see the email or attachment in the first place. This is pretty hard thing to do though, since few companies really run across the board with no flash, no java, no javascripting, full content filters, waf, etc.
Head of IAD for the NSA has been saying this for a while too. They don’t even use cellphones, they are trying to find someone to make their own custom.
1 million viruses a month at the time, probably more now, that don’t even stay in the wild long lol. Not even if all the companies pool together can they keep up with the infestations…..its impossible and naive to think so. Using a computer means your virused I don’t care who you think you are.
There is so many more bad guys then good guys too that you have to wonder if anybody cares about even their own families anymore. Especially when supposed hacktivist groups like anonymous go after everybody but other hackers…..
What society needs is for this newer generation to be more mature is what it boils down to. We need better healthcare and community environments and more knowledge sharing.
Awsome Article btw. Schooling the masses on whats common knowledge to anyone who is conscious. Krebs is always saying the things I wish someone in the media would say!
Browsing the web or opening your mail is all it takes. IT eventually happens to us all, its tough times to use a pc.
There are two things that Brian has never mentioned (at least I have never seen it here) which will drastically reduce attacks by email phishing:
1) Before clicking on a link — any link — first hover the cursor over the link and look at the bottom-left of the screen for the associated URL. The URL must be as expected, e.g. if the email is purportedly from PayPal, it had better end with paypal.com. Never click on links which have unfamiliar URLs or tricky ones, e.g. paypal-business.com. Some valid links may be thrown out with the slime, but maybe you shouldn’t be doing business with people who outsource their function to unfamiliar companies.
2) Never use admin acounts for Internet/email use, unless it is strictly sysadmin-oriented, e.g. to look at microsoft.com for forum posts similar to your problem, and only if you have the discipline to never click on irrelevant links.
Anti-virus is not dead; it is merely one tool in a toolbox.
I would add to your second point: If you’re trying to figure out what’s wrong with your PC and you’re logged in as an administrator, use a small laptop (e.g., a netbook) to research the solution and to download any needed software. Scan the software for malware on the small laptop before copying it to the problematic PC.
AV’s own marketing is coming back to bite them. For years, they marketed their product as protecting against all malware, including new malware. I remember they all had their own comparison matrices showing they had a better detection rate of unknown malware. It’s sad that even so called “experts” bought into the marketing and now call AV dead because it can’t defend against unknown malware.
Traditional AV, in conjunction with software security updates, should be viewed as a vaccination . A new computer needs AV like a baby needs vaccinations. Because of the idiots that don’t vaccinate, things like the measles and polio still endanger the unvaccinated and immunocompromised. Computer users without common sense or that are highly gullible, are the immunocompromised, and those without a traditional AV are the unvaccinated. Just like AV, vaccines are not 100% effective, so the more people that are vaccinated, the better for everyone.
Ultimately, we need to change the perception that AV protects against new threats. It protects us against known threats so we can focus on detecting new threats.
Good analogy
Considering Symantec along with RSA should have been out of business when they got pwn’d originally. And any Enterprise or Lone User of Symantec Endpoint Security knows that from a useability basis SES is a horrible tool that botches more things and muddies the water in untenable ways just from an IT support standpoint well yes, Symantec may know more than us about the repercussions of their breach so good riddance. I have my beefs with Apple because in their necessary quest to keep their cool and unbroken shiney cool power users must endure so much when they refuse to relinquish control.
Face it, internet security is an oxymoron for several reasons – from soft headed decision makers want ease of access so break all security for them. Outsource or fire your IT support team and refuse to fund IT security, to have Security Policy and stick to it-all fixable on a local level but when RSA and Symantec continue to be the industry standard after being totally owned lock stock and barrel, thst dpeaks to systemic necrosis. I am advising everyone now to re-evaluate their security policy. If they need to harden and protect Intellectual Property. They may even need to turn off the network-internet. If that is their route they need to go purchase file cases, folders, pen and paper, disconnect copiers from the net and to write up security policy regarding IP, security policy about scanning, digitizing, emailing, cloud sourcing. Face it. A lot of folks will need to draw back and reevsluate this. It is not unrealistic to consider pulling the plugs, especially in cases whether it is byod or internet that ate the weak link. I just do not buy the line that you cannot roll things back. In fact there are plenty if business cases where they can and they should.