I’ve long recommended that small business owners and others concerned about malware-driven bank account takeovers consider adopting a “Live CD” solution, which is a free and relatively easy way of temporarily converting your Windows PC into a Linux operating system. The trouble with many of these Live CD solutions is that they require a CD player (something many laptops no longer have) — but more importantly – they don’t play well with wireless access. Today’s post looks at an alternative that addresses both of these issues.
As I noted in my 2012 column, “Banking on a Live CD,” the beauty of the “Live CD” approach is that it allows you to safely bank online from any machine — even from a system that is already riddled with malware. That’s because it lets you boot your existing PC into an entirely different (read: non-Windows) operating system. [Not sure why you should consider banking online from a non-Windows PC? Check out this series].
The device I’ll be looking at today is not free, nor is the the tiny dongle that enables its ability to be used on a wireless network. Nor is it an actual CD or anything more than a stripped-down Web browser. But it is one of the safest, most easy-to-use solutions I’ve seen yet.
The device, called ZeusGard, is a small, silver USB flash drive that boots into a usable browser within about 30 seconds after starting the machine. The non-writeable drive boots directly into the browser (on top of Debian Linux), and if your system is hard-wired to your router with an Ethernet connection, you should be good to go.
Nearly all Live CD solution have one glaring weakness: They typically are not usable over a wireless connection. The Live CD solution I most frequently recommend — which is based on a version of Puppy Linux — technically can work with wireless networks, but I found that setting it up is not at all intuitive, especially for people who’ve never used anything but Windows before.
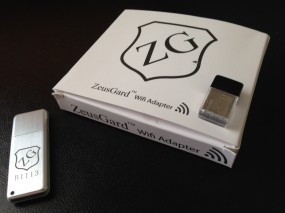 My review copy of ZeusGard came with a tiny USB wireless Wi-Fi adapter, which makes jumping on a wireless network a complete breeze. When you boot up with both ZeusGard and the adapter plugged in, ZeusGard automatically searches for available wireless networks, and asks you to choose yours from a list of those in range.
My review copy of ZeusGard came with a tiny USB wireless Wi-Fi adapter, which makes jumping on a wireless network a complete breeze. When you boot up with both ZeusGard and the adapter plugged in, ZeusGard automatically searches for available wireless networks, and asks you to choose yours from a list of those in range.
Assuming access to your wireless network is secured with WPA/WPA2 (hopefully not the weaker WEP) , click the “properties” box next to your network, and enter your network’s encryption key (if you need to see the key in plain text while you’re typing, tick the box next to “key”). Hit “OK” and then the “Connect” button. Once you’re connected, click the down arrow at the top of the dialog box and select “Exit to Browser Session.”
This is the second generation of ZeusGard, and I’m looking forward to seeing the next iteration of the device. ZeusGard is produced by Bancsec, a consulting firm that advises financial institutions on ways to beef up security (think Sneakers). Bancsec CEO J.B. Snyder said the next version should include a streamlined wireless setup, and will offer users more options inside the browser session (in the version I tested, for example, ZeusGard automatically shuts down after 30 minutes of use).
At $24.95 for the basic ZeusGard and $14.95 for the wireless adapter, this device is likely to be more appealing to small businesses than the average Internet user. But if you need or want wireless capability in a USB-based “Live CD” solution, ZeusGard is one of few easy-to-use options currently available.
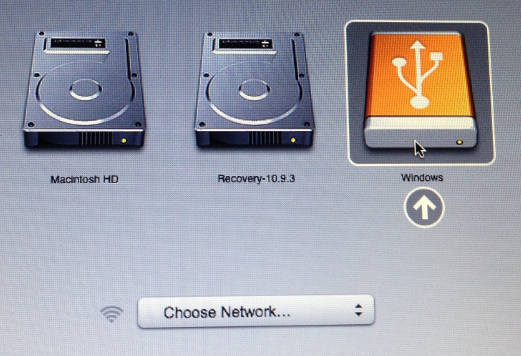
To get ZeusGard working on a Mac, hold the “Option” key while booting up, and select the volume labeled “Windows” (yes, I realize this is counter-intuitive, since the whole idea behind booting into a live CD is that you’re not in Windows).
Getting ZeusGard (or any other live distribution, for that matter) working on a Windows PC may be a bit more involved. Rather than reinvent the wheel, I’ve excerpted and modified the following instructions from my Banking on a Live CD post.
We next need to make sure that the computer knows to look to the USB drive first for a bootable operating system before it checks the hard drive, otherwise ZeusGard will never be recognized by the computer (this only needs to be done once). When you start up your PC, take note of the text that flashes on the screen, and look for something that says “Press [some key] to enter setup” or “Press [some key] to enter startup.” Usually, the key you want will be F2 or the Delete or Escape (Esc) key.
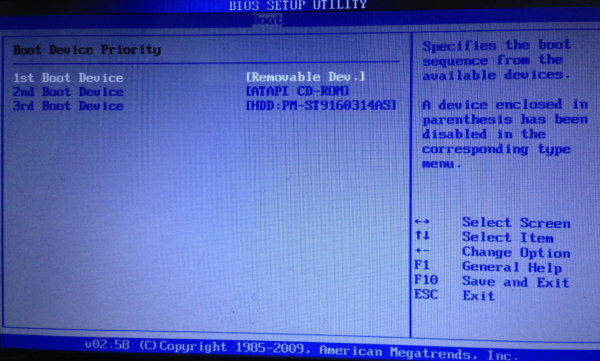
A Windows BIOS screen. If you’ve done it right, the “removable dev” option should be listed as the 1st Boot Device.
When you figure out what key you need to press, press it repeatedly until the system BIOS screen is displayed. Your mouse probably will not work here, so you’ll need to rely on your keyboard. Look at the menu options at the top of the screen, and you should notice a menu named “Boot”. Hit the right arrow key until you’ve reached that screen listing your bootable devices, and then hit the Enter key What you want to do here is move the Removable Devices option to the top of the list (it may be listed as merely “Removable Dev”). Do this by selecting the down-arrow key until that option is highlighted, and then press the Shift and the “+” key on your keyboard until the Removable Devices option is at the top. Then hit the F10 key, and confirm “yes” when asked if you want to save changes and exit, and the computer should reboot.
Unless you know what you’re doing here, it’s important not to make any other changes in the BIOS settings. If you accidentally do make a change that you want to undo, hit F10, and select the option “Exit without saving changes.” The computer will reboot, and you can try this step again.
If you’ve done this step correctly, the computer should detect the USB drive as a bootable operating system, and boot into ZeusGard.





It’s not called a “Windows BIOS screen”. The BIOS setup screen does NOT have any relation to Windows (or any OS).
It is the BIOS screen one can expect to see on a computer that runs “Windows” software. OK now?
not ok, such ignorance can’t be ignored.
Such ignorance is curable. Trying to demonstrate your superior knowledge with snark just makes you look the fool.
That being said, that type of BIO screen is generally displayed on a Windows or Linux type computer, and will be familiar to those who have used them and new and frightening to those who have not.
It only looks scary. Follow the instructions and you will be fine.
Like a lot of nerds that aren’t grounded in reality you’re completely missing the point: people don’t want to waste their time learning the technical ins and out of computing, they want to use it for something that is productive for their circumstances.
Similarly I’m sure you wouldn’t expect to learn the ins and out of combustion engines in order to mow your lawn. Or understand the ins and out of radio transmission before using your mobile phone. Or learn before using .
So they aren’t doing things like learning the differences between a part of the computer they almost never use in order to conduct their online banking with additional security because that is a waste of their time that they could be doing something productive like running their business or whatever else they want to do.
Actually, you don’t need to learn the “ins and outs” in order to follow some instructions. Once a user has set this option in the BIOS the one time (look for USB first), then all they will ever have to do afterwards is plug in the USB device, and then boot the machine.
Your analogies are flawed. If you’ve never used a gas mower before, you end up reading the instructions to figure out how to properly start it (unless of course, you think you know everything about anything and then you’re just a statistic). Thus, you learn something simple without needing to know how to tear the engine apart.
This is an advanced security blog, not wikihow.com.
“Similarly I’m sure you wouldn’t expect to learn the ins and out of combustion engines in order to mow your lawn.”
Most people’s lawn will never be a conduit for things designed to destroy their lawn mower or empty their bank account, is yours?
I use LiveLawnMower … plug it into my USB port and I can safely use my remote-control lawn mower without the fear that Zeusbot will infect it and use my lawn mower as part of a botnet attacking my flower beds and chasing the fat neighbor woman down the street.
Oh, and the reason the Mac’s boot disk selector displays “Windows” is beacuse the boot partition of the live USB uses BIOS (the interface that the rest of the computers uses) instead of (U)EFI (the interface that Macs and newer Windows computers uses)
That may also explain why Zeusgard does NOT work on all Macbook Pro’s. I have tried two, and neither work – ZeusGard Support has told me that it seems to work on Macbook Air’s with no issue, but that there are problems with several Macbook Pro’s. be warned, YMMV with this one.
The concept you’re outlined is most certainly admirable. When there is a manner in which one may safely have account names and passwords accompany the browser within the secure zone, perfection will have been achieved. As it is now, it’s only nearly perfect!
What about this in conjunction with a password manager like lastpass?
Also if you use the same pc often, you can set the boot order to use usb then hdd. Then whenever you, um, stick in the stick, it boots there.
I’ve done this a lot with a bootable ubuntu stick.
Hmm, not banking over wifi, working as intended?
Comments that attack others or are generally rude and profane will be deleted. I’m reminding readers because I had to take the rare step of deleting several from this post.
This is a great concept for the consumer end. It’s also not new, as another comment pointed out. He (commenter), like Krebs, has been aware of booting to a live disk to do browsing without leaving local traces and to keep the booted system from being corrupted. These guys have just made it more turn-key for the less-tinkery crowd. Good job.
My curiosity is how this protects us from when banks and corporations get hacked. If my transaction information gets sniffed/stolen elsewhere, then this solution does not protect my account from unauthorized usage. Still, if I had malware on my own machine, this would prevent attackers from getting my banking log-in information from me. Every drop counts, I guess, even in an ocean.
I’ve been toying with VMWare recently.
I remember back when people would ask about your new hardware, “Yeah, but can it play Crysis?” I didn’t know what Crysis was at the time–not a heavy gamer. Nowadays, after Win7 came out and the first 2 generations of iCore processors, I started asking people, “Yeah, but can it play Myst?”
That said, I wonder if you can boot this Live disk (USB) in a VMWare session. That would eliminate the need for a full reboot, if it stayed secure wile tunneling out through the Windows system.
Can VMWare boot an existing disk partition that’s not the already-running system?
I prefer VirtualBox to VMware. You can boot anything in a virtual machine that you can boot on the bare hardware. With a virtual machine you are still using the Windows WiFi driver, so don’t have that problem. You can also set them to revert to a known state (snapshot) and thus remove any changes that might have occurred due to web usage. Only thing a virtual machine does not get you is around a keylogger, etc, on Windows.
You can also make your own bootable Linux USB drives using
http://www.linuxliveusb.com/
What? You started asking people if it can play a game that was released almost 20 years ago instead of a more recent game that still gives pricy hardware a run for it’s money?
Yes, technically VirtualBox and VMWare can boot raw disks.
http://www.virtualbox.org/manual/ch09.html#rawdisk
http://superuser.com/questions/451573/use-virtualbox-to-boot-a-physical-drive-partition
However, please be aware that this approach isn’t actually “secure”.
1. If something successfully attacks your host os, it can write to other drives, including your inactive Windows / Linux partitions. (One common way malware, –including Stuxnet– spreads is by writing to other drives)
2. If something successfully attacks your guest os, and there’s an exploit available for your VM, then it can escape and attack your host. Attacks against the VM subsystem are incredibly rare, but it’s worth being aware of the flaws in a solution before blindly choosing it.
3. If something successfully attacks host OS or guest OS, and the guest VM is “bridged”, then in theory the host and guest can attack eachother in interesting ways via their “ethernet” ports.
4. If you configure shared clipboard, then an evil application in the guest (or host) could snoop or poison the clipboard — this isn’t usually a problem, but if you happen to paste commands into Terminal.app/cmd.exe, then it’s a potential risk.
5. If you configure shared folders, then an evil application in the guest (or host) can have some impact on the other side.
Lightweight Portable Security is a live CD with wireless ability.
Brian, I was wondering what you thought of using more of a micro-kernel approach, similar to QubeOS (invented by the gal who wrote “Blue Pill” years ago and her team).
Note the site domain ends with .org, (not to be confused with the online virtual pc company or a nearly similar name: qube-os.com)
It’s security by domains. Pretty good explanation of how it’s setup here: https://wiki.qubes-os.org/wiki/GettingStarted
and how she uses it here (for more of an example how a real user would put it into practice, although this example is from several years ago): http://theinvisiblethings.blogspot.com/2011/03/partitioning-my-digital-life-into.html
I know this isn’t your everyday Joe kind of setup, but if someone would turn it into an appliance type thing it’d be even more secure perhaps than ZeusGuard.
And they just came out in April with the latest release.
I wondered what you think of this micro-kernal OS approach to online safety (by separating work and data into risk-based areas).
Thanks.
That should be “QubesOS” in the first sentence.
I’ve been using this for quite a while. It runs from cd and usb, and using wireless is easy:
http://www.spi.dod.mil/lipose.htm
Ouch – runs Java. While it makes sense from what it is maybe we need self-destructing/renewing sessions to continually clean up any intrusion or keyloggers etc.
Thanks for mentioning it (although the 2011 date at the top made me think it was old till I scrolled down and saw they do update it now and then, most recently in June 2014).
I’ve run into the same issue with versions of Linux either having poor support for wireless even when fully installed or having difficulty with it in non-traditional settings like a live disk or a VM. One that I found that worked was DEFT 8.0 while 8.1 did not work. This one is good to know about.
I am disappointed, but also not very surprised. At least mention that this was paid for.
@dsp
Not that anyone cares that you’re disappointed but not surprised, could you be a little more specific in your remark, “At least mention that this was paid for”?
If you were insinuating that this review was a paid advertisement, don’t be a coward, just say it outright, but my money says you’re wrong.
If you have a problem with Brian, the reviewer, receiving a complimentary product as minor compensation for writing and publishing his very helpful review, then get over it.
If professionally qualified reviewers like Brian, who is especially expert WRT online security, had to pay out of their own pocket to purchase everything worthy of a knowledgeable review, none of us would be able to learn 5% of what we glean from these reviews, simply because there would hardly be any reviews left.
What’s to say that the producers of this won’t take as many (or as little) dollars as possible until one day they finally activate a keylogger contained in the OS distribution?
Maybe I’m missing something but that is a concern whenever I use something Linux-based. I simply cannot tell how to check a free (or commercial) Linux distro for any bad code.
I mean, I create a Linux tool, it gets popular, and one day the timer goes off and every subsequent use of the distributed image reaches out to my command and control servers, and then I tell each one to grab any and all credentials that are used in any and all sessions. And send them back to me.
Then I take the 200+ customers, and give them the finger. Who cares. I’ve got 30 sets of credentials — or more.
What am I missing? Is this not possible and likely? Especially when someone starts selling something (and therefore, it looks more trustworthy than something that might be free)?
You’d make a lousy bad guy.
Never hard-code the time-bombs. Just slip it into an update of a fairly innocuous package (maybe CUPS?), and call it a day.
To top it off, advise all to update to the latest version, claim you closed security holes, and call it a day.
Bam.
Is that my white van outside?
@ROCG
Good point. I don’t see anywhere where I can access the source code to check for backdoors/rootkits etc.
Now it comes to the part that we think: in capitalism, everything is good. Look how many anti-virus and other security (and people like journalists), earn their money from this kind of fraudulent activity. If you analyse deeply this situation, is clearly that anyone (including Krebs) who talk about cyber crooks and blame them, and try to destroy them, in fact don’t want them to disappear. No one is hero. It’s all business.
Gosh, Pedro, you are so right. I am certainly never going to go see a doctor or a dentist again, because they must certainly be making me more sick so they can make more money!
You know, I eat every morning and by noon I am hungry again! What a racket by those farmers.
In related news, because everyone says the sky is blue, therefore it must be green.
Brian, presuming you are aiming at the large number of end-users who are only familiar with the Windows environment and lack the technical skills to run a Linux environment, is there a reason you wouldn’t use Windows PE on a USB stick for this purpose ?
Or are you merely perpetuating the myth that non-Windows operating systems are inherently more secure?
Kon-boot should have ended that lie once and for all.
I’ve yet to see a decent Windows PE instruction set (and I’ve wanted/needed them occasionally).
Ignoring that, it has the same potential problem that everything else I’ve seen has (and which I will be covering elsewhere):
Any time you set up a computer (of any type) and don’t do continuous/regular software updates, you risk having exploitable software on this computer.
Windows PE on a stick, which is used only once a month, will on average have 5-10 known exploits against it — before you could safely use it, you’d need to safely update it. That’s a risk (and if you forget, or if someone happens to deny you the updates by attacking your router and blocking access to the update servers…).
To be fair, the USB stick that Brian is mentioning here should, in theory, suffer from the same problem. By being read-only, it’ll always start off one step behind.
Hopefully the system has some kind of auto-update mechanism but there’s only so much you can do until you’ve got to update the kernel and other low-level components that can only be loaded at boot and not updated on-the-fly.
Personally I’ve never had much of a problem getting Ubuntu’s wireless stack up, but obviously with the massive array of PC hardware out there there’s bound to be a setup that isn’t supported or is tricky to get working. So far I guess I’ve been lucky.
So what do you do if this needs updating, because, nothing is secure forever.
How about banking with a Chromebook?
HP laptops provides such a function in-built where I can directly boot my laptop to a browser connecting to the internet based on a Linux kernel supporting wireless connection as well, rather than booting to a Windows OS.
The browser button above the keypad with a symbol resembling the shape of the earth is the one which helps us use this feature. Directly pressing this button before booting your PC redirects us to this secure browser.
As soon as I read this article, I order the pair of Zeusgard products. Less than 48 hrs later, I’ve got them; (yay, Amazon Prime.) Took about 20 min to get everything configured the first time. Next time will be much quicker.
Looks like great product – but the documentation is VERY sparse, essentially nonexistent for using the WiFi dongle in conjunction with the thumbdrive browser. Still, I’m WAY happy to have this solution. I had spent many hours previously, trying to get my laptop’s WiFi to work with a Live CD, but had given up. This rocks.
from the home site…
Low Cost – Only $19.95 shipped to USA
but the buy link links to Amazon
Price: $24.95 + $6.30 shipping
Note: Not eligible for Amazon Prime.
I thought $20 was a bit high for some public domain stuff but fair enough that I would order one…. guess not.
I think the advantage of this gizmo is the “write protect”, so running a general purpose bootable flash drive w/o that feature might not be as secure.
I was about to recommend using an SD card and adapter because they have write-protect switches, but those switches only set a flag to tell the OS, ” “please don’t write to this disk” – which or may not be respected.
On the other hand, you can buy USB flash drives with de facto write-protect switches in the same price range.
See an article here :
http://www.fencepost.net/2010/03/usb-flash-drives-with-hardware-write-protection/
Then you could use something like Sardu or RMPrepUSB to write any iso (s) of Linux, etc that you like to it.
I have used both programs, but not run anything write-protected, so I’m not sure if that would cause problems or not.
Sardu (fairly easy, although not for the total beginner)
http://www.sarducd.it
RMPrepUSB (requires more tech knowledge)
http://www.rmprepusb.com/
I’ve been rescuing computers by booting live Linux environments from USB for about a decade, and only ever had wifi issues with the more obscure devices, almost all of which could be easily fixed with a bit of Google-fu.
Nice product idea.
Just to note: there are a number of USB wifi adaptors that use drivers that will be found in most Linux kernels. For example, netgear WG111v2 and v3 use the rtl818. These adapters are available quite cheaply used. I keep one in the bag for demos of Linux live CDs.
Echoing what Thomas Spear said on July 16, 2014 at 5:50 pm; and thanks Thomas, it took me more time to download the .iso than it did to get it booted and tested (I used rufus-1.4.7 to put the iso on the usb).
Certified a secure environment and “…it runs from cd and usb, and using wireless is easy”
http://www.spi.dod.mil/lipose.htm
A standardized appliance with monitor, keyboard, mouse, and usb distro is appealing.
Keep the appliance in a central spot. Get an updated distro when available.
I could see paying for something like that. $25/month? Would be cheap insurance.
How do these liveCD type approaches work with password managers such as KeyPass? This is the only reason I haven’ switched to this mode of banking.
My bank credentials are 20+ character random strings (the full gamut of numbers/characters/special-characters) that I don’t wish to memorize.
Should I be booting off the LiveCD and then accessing my local disk for the password manager? That seems to somehow negate the idea of keeping the local disk out of the loop.
I don’t want to use an online service to store my passwords (Lastpass, while convenient, the fact that they store my passwords makes me uncomfortable)
I’ve used puppy linux on quite a few windows machines.. I’ve only once run into one that could not find wireless internet.
I’ll stick with it. It works well, and it is very light on the hardware. I got a place to get a bunch of small usb drives for next to nothing, so if one gets hit, I pitch it and start over. I am working on making them non-writeable after I write the image to them. Someday soon….
Me too! 🙂
Puppy Linux is positively bewildering compared to my favorite: ‘Instant WebKiosk’ . All you get to see is a browser. It uses persistent storage very sparingly, not much is stored apart from your Wifi settings and home page.