Adobe and Microsoft today each independently released security updates to fix critical problems with their products. Adobe issued patches for Adobe Reader/Acrobat, Flash Player and AIR, while Microsoft pushed nine security updates to address at least 37 security holes in Windows and related software.
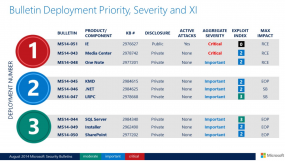
Two of the nine update bundles Microsoft released today earned the company’s most-dire “critical” label, meaning the vulnerabilities fixed in the updates can be exploited by bad guys or malware without any help from users. A critical update for Internet Explorer accounts for the bulk of flaws addressed this month, including one that was actively being exploited by attackers prior to today, and another that was already publicly disclosed, according to Microsoft.
Other Microsoft products fixed in today’s release include Windows Media Center, One Note, SQL Server and SharePoint. Check out the Technet roundup here and the Microsoft Bulletin Summary Web page at this link.
There are a couple other important changes from Microsoft this month: The company announced that it will soon begin blocking out-of-date ActiveX controls for Internet Explorer users, and that it will support only the most recent versions of the .NET Framework and IE for each supported operating system (.NET is a programming platform required by a great many third-party Windows applications and is therefore broadly installed).
These changes are both worth mentioning because this month’s patch batch also includes Flash fixes (an ActiveX plugin on IE) and another .NET update. I’ve had difficulties installing large Patch Tuesday packages along with .NET updates, so I try to update them separately. To avoid any complications, I would recommend that Windows users install all other available recommended patches except for the .NET bundle; after installing those updates, restart Windows and then install any pending .NET fixes).
Finally, I should note that Microsoft released a major new version (version 5) of its Enhanced Mitigation Experience Toolkit (EMET), a set of tools designed to protect Windows systems even before new and undiscovered threats against the operating system and third-party software are formally addressed by security updates and antimalware software. I’ll have more on EMET 5.0 in an upcoming blog post (my review of EMET 4 is here) but this is a great tool that can definitely help harden Windows systems from attacks. If you already have EMET installed, you’ll want to remove the previous version and reboot before upgrading to 5.0.
ADOBE
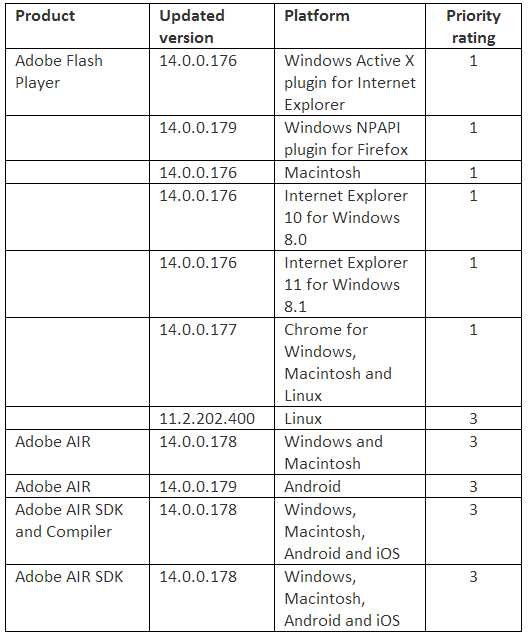
Adobe’s critical update for Flash Player fixes at least seven security holes in the program. Which version of Flash you should have on your system in order to get the protection from these latest fixes depends on which operating system and which browser you use, so consult the (admittedly complex) chart below for your appropriate version number.
 To see which version of Flash you have installed, check this link. IE10/IE11 on Windows 8.x and Chrome should auto-update their versions of Flash, although my installation of Chrome says it is up-to-date and yet is still running v. 14.0.0.145 (with no outstanding updates available, and no word yet from Chrome about when the fix might be available).
To see which version of Flash you have installed, check this link. IE10/IE11 on Windows 8.x and Chrome should auto-update their versions of Flash, although my installation of Chrome says it is up-to-date and yet is still running v. 14.0.0.145 (with no outstanding updates available, and no word yet from Chrome about when the fix might be available).
The most recent versions of Flash are available from the Flash home page, but beware potentially unwanted add-ons, like McAfee Security Scan. To avoid this, uncheck the pre-checked box before downloading, or grab your OS-specific Flash download from here.
Windows users who browse the Web with anything other than Internet Explorer may need to apply this patch twice, once with IE and again using the alternative browser (Firefox, Opera, e.g.). If you have Adobe AIR installed (required by some programs like Tweetdeck and Pandora Desktop), you’ll want to update this program. AIR ships with an auto-update function that should prompt users to update when they start an application that requires it; the newest, patched version is v. 14.0.0.137 for Windows, Mac, and Android.
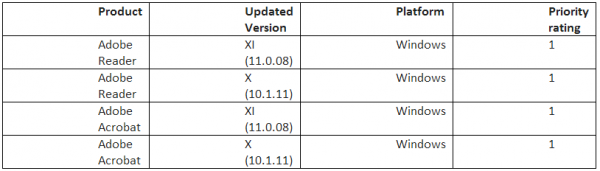
Adobe said it is not aware of any exploits in the wild that target any of the issues addressed in this month’s Flash update. However, the company says there are signs that attackers are are already targeting the lone bug fixed in an update released today for Windows versions of Adobe Reader and Acrobat (Adobe Reader and Acrobat for Apple’s OS X are not affected).
Experience technical issues during or after applying any of these updates, or with the instructions above? Please feel free to sound off in the comments below.
Update, 6:52 p.m. ET: In the second paragraph, corrected the number of updates Microsoft released today.




Google Chrome just pushed out its update.
Yep, my chrome just updated:
Version 36.0.1985.143 m
Google Chrome is up to date.
Is anyone else annoyed how Chrome updates itself automatically and setup.exe consumes all your free CPU time, even at below normal priority?
I’d rather not have that happen on its own — is there any way to get Chrome to ask for your go-ahead when an update is ready, as do most other software packages?
There was also a Java 7 update (version 67) about a week or two ago.
Tweetdeck desktop versions no longer use Adobe AIR
You recommend uninstalling EMET before upgrading, but Microsoft says this is not necessary in their User’s Guide, assuming you are going from v3 or v4. If you have a version older than EMET 3, then they do recommend an uninstall.
As always, it depends. I have two W7 computers. One wouldn’t install EMET 5 without uninstalling/re-booting, the other (newer) computer did. Don’t ask me why ….
Wasn’t impressed with MS14-051 (Cumulative Security Update for Internet Explorer (2976627) ) patching 26 more vulnerabilities with Internet Explorer. six to eleven When are people going to stop using the browser and move to a third party browser? It’s just not worth the risk anymore using the browser in your day to day tasks.
Its amazing how many updates Windows and IE seem to need. It just seems like a bottomless barrel that MS has to keeping pouring patches and updates into.
Maybe misperception on my part, but the rate and quantity and severity of holes to be plugged by MS never seems to slow up or diminish.
Can somebody explain to me why Apple doesn’t have similar need to patch as often or as extensively?
Apple pushes out updates on its own schedule, which is anything but predictable or transparent. That won’t fly with Microsoft’s customers — mainly businesses running hundreds if not thousands or tens of thousands of systems that need to be maintained and patched.
Those businesses have demanded some sort of regularity in the patching process, and so Microsoft made a business decision many years ago to switch to shipping security updates on the second Tuesday of every month (a.k.a. “patch Tuesday” or “black Tuesday”).
It is understandable why many people see a negative relationship between the security of a product and the frequency and number of updates that product receives from the software’s maker. But counting patched vulnerabilities in one product against another is a very poor way to compare the relative security of these products; what’s more one can just as easily argue that vendors who wait longer to patch problems (by doing so more infrequently) actually put their users at greater risk.
Indeed, I have conducted and published a ridiculous amount of research arguing the latter. Other researchers have come to similar conclusions, yet we still see headline-grabbing studies and stories comparing the number of patched vulnerabilities between and among vendors as if we should subtract points for patches.
See:
http://voices.washingtonpost.com/securityfix/2006/01/a_time_to_patch.html
http://voices.washingtonpost.com/securityfix/2006/02/a_time_to_patch_ii_mozilla.html
http://voices.washingtonpost.com/securityfix/2006/05/a_time_to_patch_iii_apple_2.html
Just installed EMET 5. So far it’s crashed adobe reader, Firefox and Chrome. Did not have this issue with 4.
Something is wrong with the page layout. The date of the article is for two days in the future. Had someone point this out to me and questioned the accuracy of the info based on that.
I think you’re confusing the publishing date (12th) with the year (14)
It clearly says “Aug 14” here
Because it is which month and which year?
The big number is the day.
Could be more specific? Define big.
This thread, often repeated, always makes me smile.
Bringing out Mr. Obvious.
Google: Date format by country. Start with the article from The Guardian which explains the Jonathan Swift reference, note the color map provided by The Guardian and then read the two Wikipedia entries. The United States has a chronic case of middle-endianness, that is to say MM/DD/YYYY. Many other countries use Little-endian DD/MM/YYYY. Brian uses Little-endian as does most of the world.
Don’t get me started on Big-endian.
The problem is with the fonts. The day number doesn’t look connected with the month and year in the way the date is displayed in this blog. It trips me up every time – and I grew up with the day-month-year ordering.
Also, using the actual year (all four digits) would eliminate all confusion, now and into the next century.
You can tell the programmers in the crowd, because they want things dated YYYY-MM-DD.
FYI – On one of my systems, a Lenovo, one of the updates has corrupted my network driver chain. Can’t connect via wireless or LAN. More troubleshooting in progress….
An update: I had to reboot the router. Go figure – I’ve not had to reboot that router in years. Other computers still connected wirelessly before the reboot. A test CAT5 cable connection didn’t show carrier sense. And it failed after the update.
But it all seems to be working now after the router reboot.
Your advice about breaking the update in two came home to me this time.
I had no trouble before, but this time, I got a blue screen of death and it took a lot of fiddling to where I could get to the system restore, about an hour’s worth.
So I am 100% with doing the NET updates separate.
Further on the update. I did them separately and the NET framework update is the cause of the BSOD and it is not an easy failure to recover from. Last known good configuration doesn’t work.
I have to go into recovery mode on my HP and use the Win7 disk to get to repair Windows7.
I might have a security problem without the updates installed, but I can’t use the computer at all with them installed.
Any word on which .net update is causing you trouble?
Mike and others that had a problem, I had no such problem, though I am running Win 7 pro – 64 bit (w/Service Pack 1) on an older core2 duo Lenovo (9088-BGU). Last evening, prior to any update, I ran a malware checker (Malwarebytes), de-fragged and optimized my hard disk (IObit Smart Defrag 3) . This morning I did the up-dates. I was able to download the entire series of MS updates in one session and installed in one session. No Blue Screen, no problems. I also did the Adobe up-grades with no difficulty. I use both IE and Mozilla Firefox as browsers.
I suspect the problems some have encountered have to do with corruptions on your hard drive, existing malware that has not been deleted, or viral problems. I also guess that it is possible that a portion of your download was either corrupted or truncated. Scan for Malware, Virus and defrag your hard drive. Then try and simply download one up-date item at a time and see if that does not solve your difficulty.
maybe use chkdsk /f
what does the blue screen say?
also i would use guru ddu program and then install updated video driver.
Do a memory test too as well as a hdd test.
CHKDSK /R i meant before not F.
Try to do a clean boot in windows and then update to rule out 3rd party software conflict.
wouldn’t be the first time an MS patch blue screens pc’s…
The blue screen says…..
Oh wait that was what does the fox say
if your systems start crashing after installing security updates, it could mean you were previously infected or compromised.
also I have to wonder how only supporting the latest .NET frameworks is going to play havoc with legacy intranet web / desktop apps. in the old days this would have prompted MS users to buy new systems and software.
nowadays they just move to a better platform – it’s less hassle and cost than enduring windows 8.1
The mscorsvw.exe sometimes uses very high cpu. It maxed out one of my cores heating up my cpu as much as when playing an intense video game like bf3, after this update. Ran for about 3 mins.
So unless you do other cpu intensive things on the pc, i t could be the cpu is overheating when booting after the .net update. Could also be the psu is not giving enough power. I would also check temps and voltages for the hell of it.
also see if you have latest bios for your mobo.
its probably a 3rd party conflict though…or overwhelmed cpu…. a clean boot should do it.
Looking forward to the EMET 5 post from Brian. Does anyone know if EMET 5 does better at protecting against Java exploitation? From this conference presentation, https://www.youtube.com/watch?v=EbHLeZ1VzDE, it looks like EMET 4.1 doesn’t provide effective protection for any? Java exploits.
EMET 5 is full of bugs. Be careful. There is a thread of user issues running on Microsoft. I have uninstalled it and dropped back to 4.
Thanks Brian, I find your notifications invaluable.
Multiple reports of BSOD resulting from this update:https://answers.microsoft.com/en-us/windows/forum/windows_7-windows_update/blue-screen-stop-0x50-after-applying-update/6da4d264-02d8-458e-89e2-a78fe68766fd
Brian can you comment on any of this:
http://www.chicagobusiness.com/article/20140815/NEWS07/140819895/jewel-osco-hit-by-computer-hack?r=3993H2334578J9B
https://www.securityweek.com/hackers-compromise-point-sale-systems-grocery-giants-supervalu-albertsons
It appears there are problems with some of the Microsoft patches this month causing a blue screen of death:
http://www.infoworld.com/t/microsoft-windows/blue-screen-stop-0x050-error-reported-systems-installing-kb2976897-kb2982791-and-kb2970228-248363
So far so good with Win 7 Starter 32bit with Office 2010 SP2 & Lenovo Power Edge 92 Win 7 Pro 64bit Office 2007 SP3 desktop
MS14-045 has been withdrawn.
___
MS14-045 – See “Known issues” …
– https://support.microsoft.com/kb/2982791
Last Review: August 16, 2014 – Revision: 4.0 – “… Status:
Microsoft has -removed- the download links to these updates while these issues are being investigated…
Mitigations: Open the Programs and Features item in Control Panel, and then click View installed updates. Find and then -uninstall- any of the following update that are currently installed:
KB2982791
KB2970228
KB2975719
KB2975331 …”
(More detail at the URL above.)
– https://technet.microsoft.com/library/security/ms14-045
V2.0 (August 15, 2014): Bulletin revised to -remove- Download Center links for Microsoft security update 2982791. Microsoft recommends that customers -uninstall- this update. See the Update FAQ for details.
.
AMAZINGLY POOR UPDATE QA — apparently, this time they managed to break something to do with Font handling(?!)
Microsoft Security Bulletin MS14-045 – Important https://technet.microsoft.com/library/security/ms14-045 — See Update FAQs
MS14-045: Description of the security update for kernel-mode drivers: August 12, 2014 http://support.microsoft.com/kb/2982791 — See Known issues with this security update
Steps 8, 9, 10, 11, 12:
8. After you save the reg file, find any registry values under the Fonts registry subkey for which the data field meets the following criteria:
– Contains a full file path (not just a file name)
– The full file path ends in an “.otf” extension. (This indicates an OpenType font file.)
9. Delete the fntcache.dat file again. (It will have been re-created.) To do this, type the following command at command prompt, and then press Enter:
del %windir%\system32\fntcache.dat
10. Open the Programs and Features item in Control Panel, and then click View installed updates. Find and then uninstall any of the following update that are currently installed:
KB2982791
KB2970228
KB2975719
KB2975331
11. Restart the computer.
12. Find the reg file that you saved earlier, right-click the file, and then click Merge to restore the font registry values that you previously removed.
Note It’s safe to re-add these registry values now that the offending updates have been removed.
~~~~~
End users forced to edit/merge the registry?? Not a good idea…
It’s Microsoft’s incompetence SNAFUs such as this that I *never* install patches on the first couple of days — I’m not their beta tester! 😉
It’s Official — Microsoft e-mail sent Friday night — only took 3 days to figure out the flawed patch…
———- Forwarded message ———-
From: Microsoft
Date: Fri, Aug 15, 2014 at 10:24 PM
Subject: Microsoft Security Bulletin Re-releases
********************************************************************
Title: Microsoft Security Bulletin Re-Releases
Issued: August 15, 2014
********************************************************************
Summary
=======
The following bulletins have undergone a major revision increment.
Please see the appropriate bulletin for more details.
* MS14-045 – Important
Bulletin Information:
=====================
MS14-045 – Important
– https://technet.microsoft.com/library/security/ms14-045
– Reason for Revision: V2.0 (August 15, 2014): Bulletin revised
to remove Download Center links for Microsoft security update
2982791. Microsoft recommends that customers uninstall this
update. See the Update FAQ for details.
– Originally posted: August 12, 2014
– Updated: August 15, 2014
– Bulletin Severity Rating: Important
Oops, I misspoke. This time it took *15* days to get the patch re-engineered (Version 3.0).
Allegedly, the 3rd time’s the charm — good luck, updaters! ;-)
———- Forwarded message ———-
From: Microsoft
Date: Wed, Aug 27, 2014 at 4:45 PM
Subject: Microsoft Security Bulletin Re-Releases
********************************************************************
Title: Microsoft Security Bulletin Re-Releases
Issued: August 27, 2014
********************************************************************
Summary
=======
The following bulletins have undergone a major revision increment.
Please see the appropriate bulletin for more details.
* MS14-045 – Important
Bulletin Information:
=====================
MS14-045 – Important
– https://technet.microsoft.com/library/security/ms14-045
– Reason for Revision: V3.0 (August 27, 2014): Bulletin rereleased to announce the replacement of the 2982791 update with the 2993651 update for all supported releases of Microsoft Windows. See the Update FAQ for details.
– Originally posted: August 12, 2014
– Updated: August 27, 2014
– Bulletin Severity Rating: Important
– Version: 3.0
I installed the four now-recalled updates and have had no problems. Do I need to uninstall them? Messing with the registry is not something I want to do.
Smug smiles from all those still on XP, well for a little while.
What a piece of garbage Windows is. It’s nothing but a breeding ground for viruses and malware. It is single handedly responsible for 99.9% of the viruses, malware and ransomware in existence. Do yourself a favour and rid yourself of this disgusting disease known as Microsoft Windows.
MS14-045 re-released
Vulnerabilities in Kernel-Mode Drivers Could Allow Elevation of Privilege (2984615)
– https://technet.microsoft.com/en-us/library/security/ms14-045.aspx
V3.0 (August 27, 2014): Bulletin rereleased to announce the replacement of the 2982791 update with the 2993651 update* for all supported releases of Microsoft Windows. See the Update FAQ for details.
* https://support.microsoft.com/kb/2993651
Last Review: Aug 27, 2014 – Rev: 2.0
.
… and THAT already has been “revised”:
> https://support.microsoft.com/kb/2993651
Last Review: Aug 28, 2014 – Rev: 3.0
.